Navigation
- Change Log
- Overview
- PowerShell Deploy Script Method – both upgrade and new
- vSphere Client Deploy OVF method – Upgrade Existing, or Deploy New
- Web-based Admin Interface
- Add UAG to Horizon Console
- Monitor Sessions
- Logs and Troubleshooting
- Load Balancing
- UAG Authentication – SAML, RADIUS
- Other UAG Configurations – High Availability, Network Settings, System Settings
💡 = Recently Updated
Change Log
- 2025 July 29 – updated Import OVF section for UAG 2503
- 2024 Jan 31 – SHA-1 thumbprint no longer supported. Replace with SHA-256 thumbprint (fingerprint).
- 2021 Sep 30 – Horizon Edge configuration – added instructions to disable CORS to fix HTML Access in Horizon 2106 and newer.
Overview
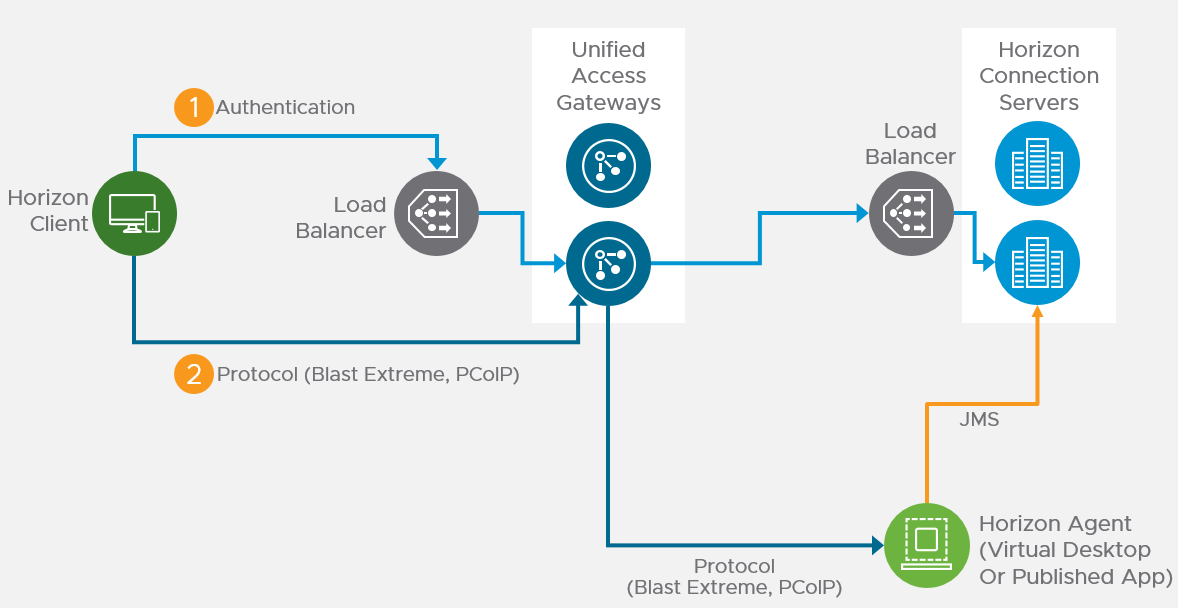
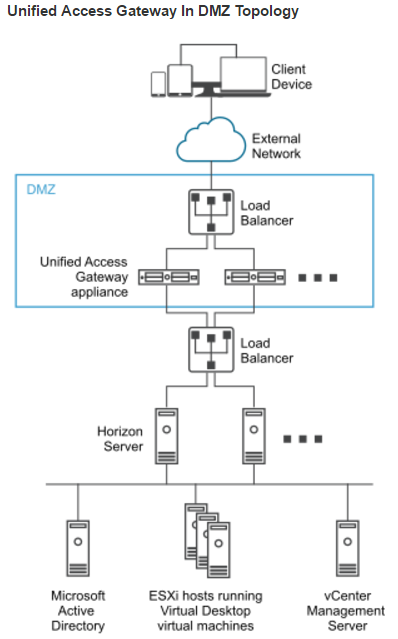
Unified Access Gateway provides remote connectivity to internal Horizon Agent machines. For an explanation of how this works (i.e., traffic flow), see Understand and Troubleshoot Horizon Connections at Omnissa Tech Zone.
Unified Access Gateway (formerly known as Access Point) is a replacement for Horizon Security Servers. Advantages include:
- You don’t need to build extra Connection Servers just for pairing. However, you might want extra Horizon Connection Servers so you can filter pools based on tags.
- Between Unified Access Gateway and Horizon Connection Servers you only need TCP 443. No need for IPSec or 4001 or the other ports. You still need 4172, 22443, etc. to the View Agents.
- No need to enable Gateway/Tunnel on the internal Horizon Connection Servers.
- Additional security with DMZ authentication. Some of the Authentication methods supported on Unified Access Gateway are RSA SecurID, RADIUS, CAC/certificates, etc.
However:
- It’s Linux. You can deploy and configure the appliance without any Linux skills. But you might need some Linux skills during troubleshooting.
Horizon View Security Server has been removed from Horizon 2006 (aka Horizon 8).
- Some of the newer Blast Extreme functionality only works in Unified Access Gateway. See Configure the Blast Secure Gateway at Omnissa Docs.
More information at VMware Blog Post Technical Introduction to VMware Unified Access Gateway for Horizon Secure Remote Access.
Horizon Compatibility – Refer to the interoperability matrix to determine which version of Unified Access Gateway is compatible with your version of Horizon.
- The latest version of UAG is 2503.
- You usually want the Non-FIPS version.
- Then download the PowerShell deployment scripts on the same UAG download page.
- You usually want the Non-FIPS version.
Firewall
Omnissa Tech Zone Omnissa Horizon Blast Extreme Display Protocol, and Firewall Rules for DMZ-Based Unified Access Gateway Appliances at Omnissa Docs.
Open these ports from any device on the Internet to the Unified Access Gateway Load Balancer VIP:
- TCP and UDP 443
- TCP and UDP 4172. UDP 4172 must be opened in both directions. (PCoIP)
- TCP and UDP 8443 (for HTML Blast)
Open these ports from the Unified Access Gateways to internal:
- TCP 443 to internal Connection Servers (through a load balancer)
- TCP and UDP 4172 (PCoIP) to all internal Horizon View Agents. UDP 4172 must be opened in both directions.
- TCP 32111 (USB Redirection) to all internal Horizon View Agents.
- TCP and UDP 22443 (Blast Extreme) to all internal Horizon View Agents.
- TCP 9427 (MMR and CDR) to all internal Horizon View Agents.
Open these ports from any internal administrator workstations to the Unified Access Gateway appliance IPs:
- TCP 9443 (REST API)
- TCP 80/443 (Edge Gateway)
PowerShell Deploy Script
Omnissa Docs Using PowerShell to Deploy VMware Unified Access Gateway. The script runs OVF Tool to deploy and configure Unified Access Gateway. The PowerShell script is updated as newer versions of Unified Access Gateways are released. This is the recommended method of deploying Unified Access Gateway.
If you prefer to use vSphere Client to Deploy the OVF file, skip ahead to Upgrade or Deploy.
The PowerShell deployment script is downloadable from the UAG download page.
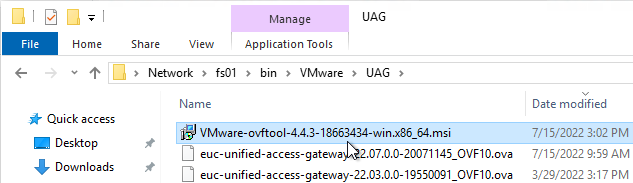
The PowerShell deploy script requires the OVF Tool:
- Download ovftool from Broadcom.
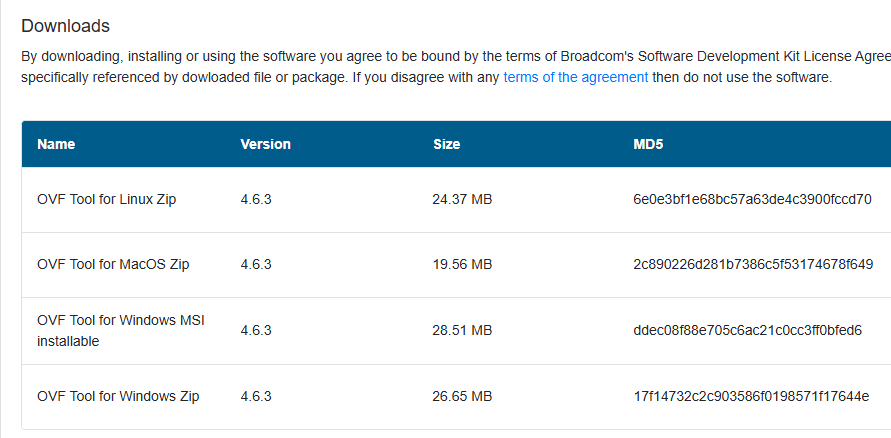
- On the machine where you will run the UAG Deploy script, install VMware-ovftool-…-win.x86_64.msi.
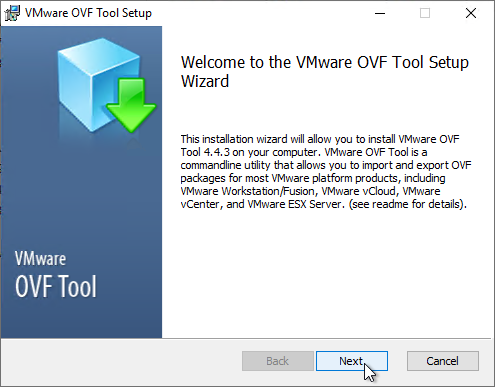
- In the Welcome to the VMware OVF Tool Setup Wizard page, click Next.
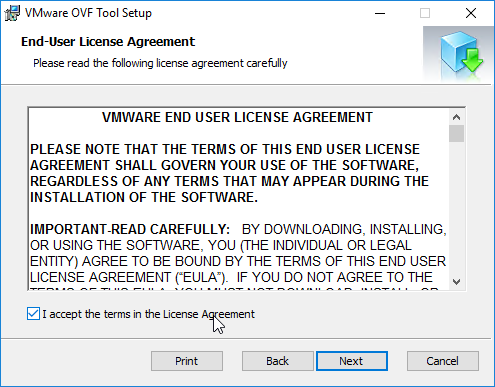
- In the End-User License Agreement page, check the box next to I accept the terms and click Next.
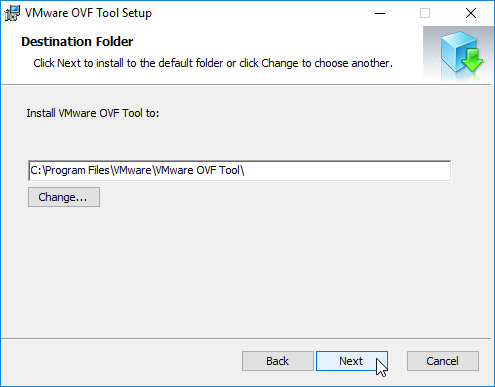
- In the Destination Folder page, click Next.
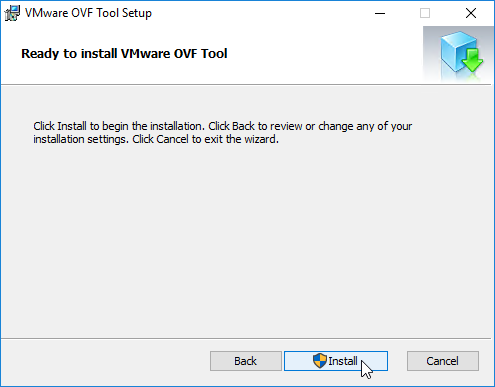
- In the Ready to install VMware OVF Tool page, click Install.
- In the Completed the VMware OVF Tool Setup Wizard page, click Finish.
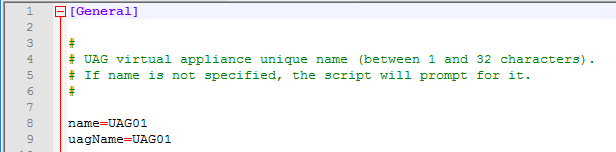
Create or Edit a UAG .ini configuration file:
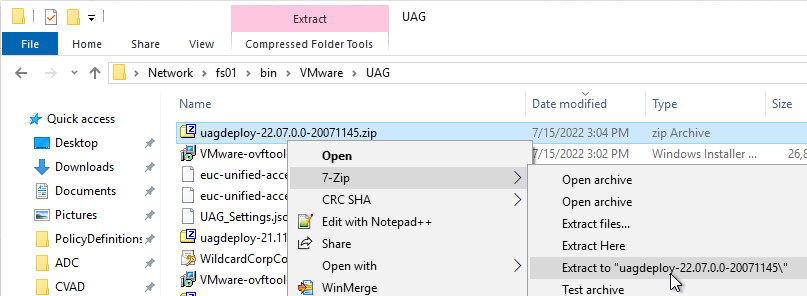
- Extract the downloaded uagdeploy PowerShell scripts for your version of Unified Access Gateway.
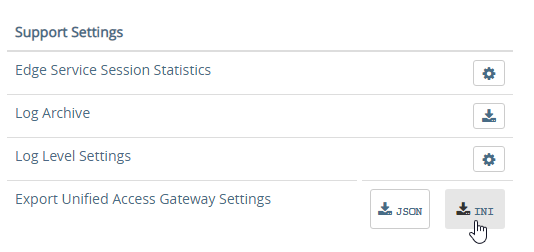
- If you have an existing UAG appliance, then you can download an INI of the configuration from the UAG Administrator page.
- Or copy and edit one of the downloaded .ini files, like uag2-advanced.ini.
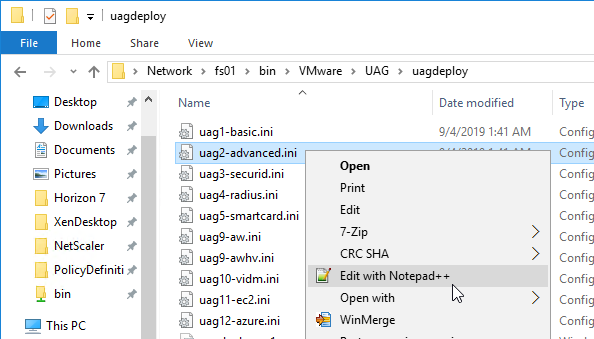
- Or copy and edit one of the downloaded .ini files, like uag2-advanced.ini.
- A full explanation of all configuration settings can be found at Using PowerShell to Deploy Unified Access Gateway at Omnissa Docs.
- For any value that has spaces, do not include quotes in the .ini file. The script adds the quotes automatically.
- The name setting specifies the name of the virtual machine in vCenter. If this VM name already exists in vCenter, then OVF Tool will delete the existing VM and replace it.
- Add a uagName setting and specify a friendly name. You’ll later add this name to Horizon Console so you can view the health of the UAG appliance in Horizon Console.
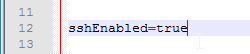
- You can optionally enable SSH on the appliance by adding sshEnabled=true.
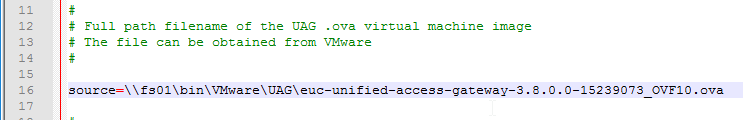
- For the source setting, enter the full path to the UAG .ova file.
- For the target setting, leave PASSWORD in upper case. Don’t enter an actual password. OVF Tool will instead prompt you for the password.
- For the target setting, specify a cluster name instead of a host. If spaces, there’s no need for quotes. For example:
target=vi://admin@corp.local:PASSWORD@vcenter02.corp.local/Datacenter/host/Cluster 1
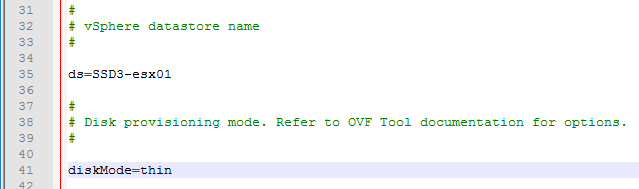
- Specify the exact datastore name for the UAG appliance.
- Optionally uncomment the diskMode setting.
- For a onenic configuration (recommended), set the netInternet, netManagementNetwork, and netBackendNetwork settings to the same port group name.
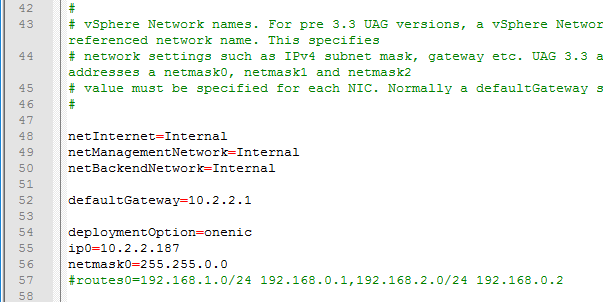
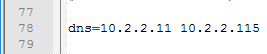
- Multiple dns servers are space delimited.
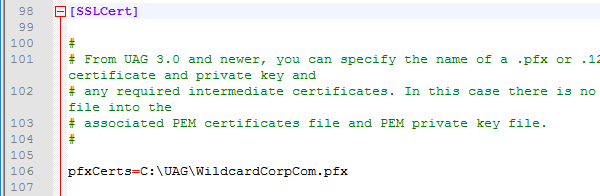
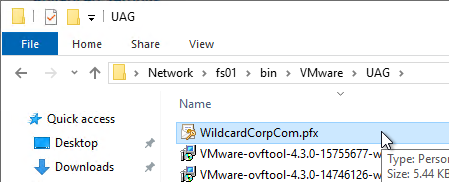
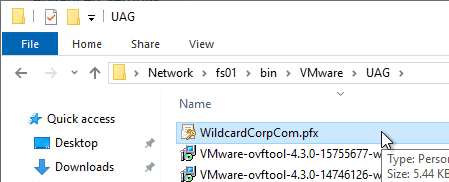
- For pfxCerts, UNC paths don’t work. Make sure you enter a local path (e.g. C:\). OVA Source File can be UNC, but the .pfx file must be local.
- There’s no need to enter the .pfx password in the .ini file since the uagdeploy.ps1 script will prompt you for the password.
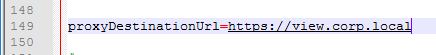
- proxyDestinationUrl should point to the internal load balancer for the Horizon Connection Servers.
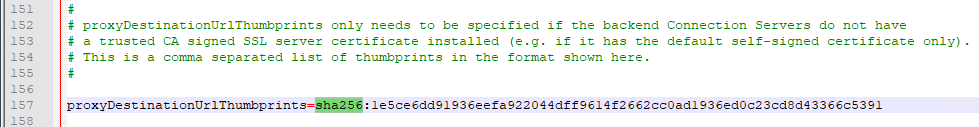
- For proxyDestinationUrlThumbprints, paste in the sha256 or higher thumbprint of the Horizon Connection Server certificate in the format shown.
- If your Horizon Connection Servers each have different certificates, then you can include multiple thumbprints (comma separated).
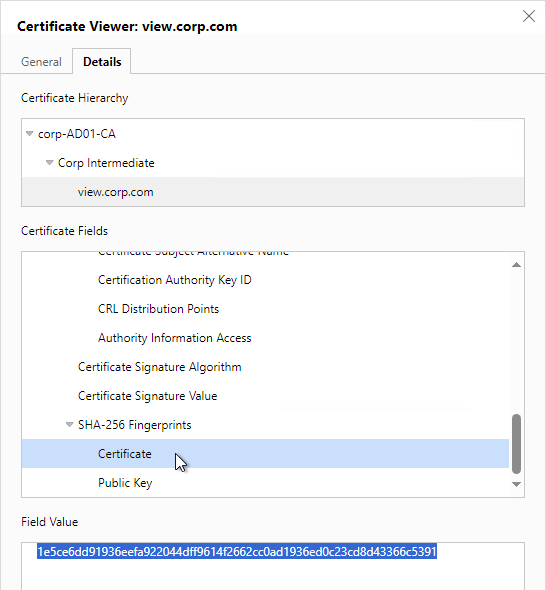
- Make sure there’s no hidden character between sha256 and the beginning of the thumbprint. Or you can just paste the thumbprint without specifying sha256. Note: sha1 is no longer supported. Edge and Chrome can show sha256 certificate fingerprint.
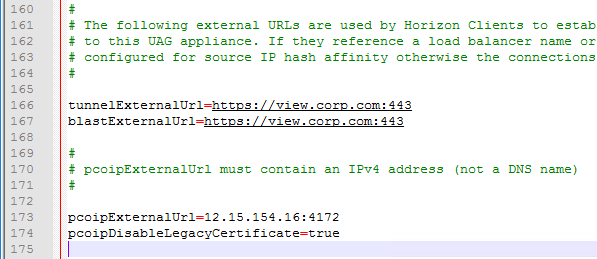
- Change the ExternalUrl entries to an externally-resolvable DNS name and a public IP address. For multiple UAGs, the FQDNs and public IP address should resolve to the load balancer. Note: your load balancer must support persistence across multiple port numbers (443, 8443, 4172).
When you run the PowerShell script, if the UAG appliance already exists, then the PowerShell script will replace the existing appliance. There’s no need to power off the old appliance since the OVF tool will do that for you.
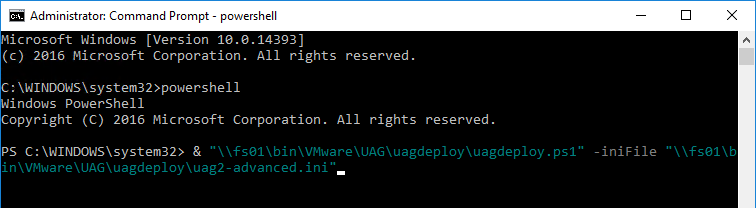
- Open an elevated PowerShell prompt.
- Paste in the path to the uagdeploy.ps1 file. If there are quotes around the path, then add a & to the beginning of the line so PowerShell executes the path instead of just echoing the string.
- Add the -iniFile argument and enter the path to the .ini file that you modified. Press <Enter> to run the script.
- You’ll be prompted to enter the root password for the UAG appliance. Make sure the password meets password complexity requirements.
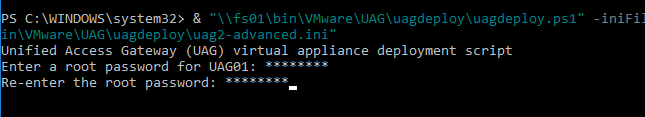
- You’ll be prompted to enter the admin password for the UAG appliance. Make sure the password meets password complexity requirements.
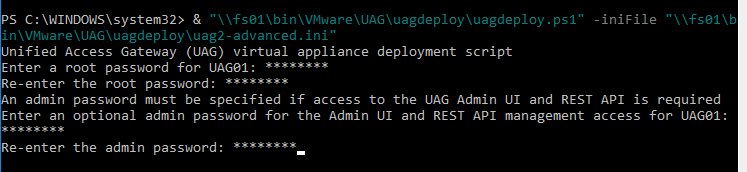
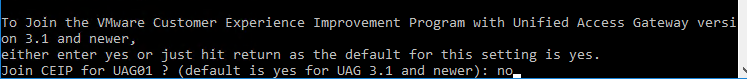
- For CEIP, enter yes or no.
- For .pfx files, you’ll be prompted to enter the password for the .pfx file. Note: the .pfx file must be local, not UNC.

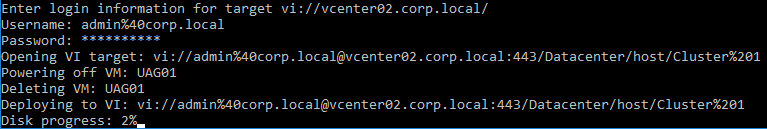
- OVF Tool will prompt you for the vCenter password. Special characters in the vCenter password must be encoded. Use a URL encoder tool (e.g., https://www.urlencoder.org/) to encode the password. Then paste the encoded password when prompted by the ovftool. The UAG passwords do not need encoding, but the vCenter password does.
- The deploy script will display the IP address of the powered on UAG appliance.
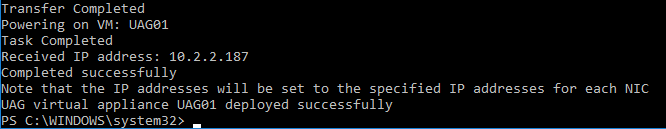
- Review settings in the UAG admin interface.
- Add the new UAG appliance to Horizon Console.
Upgrade
To upgrade from an older appliance, you delete the old appliance and import the new one. Before deleting the older appliance, export your settings:
- Login to the UAG at https://<Your_UAG_IP>:9443/admin/index.html.
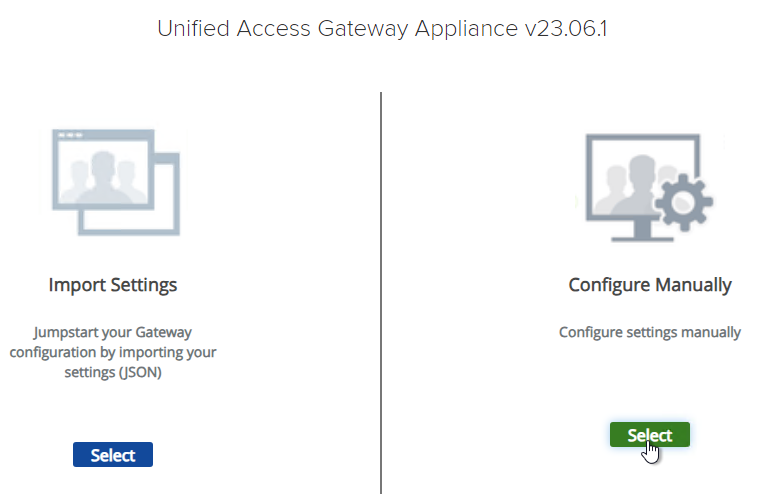
- In the Configure Manually section, click Select.
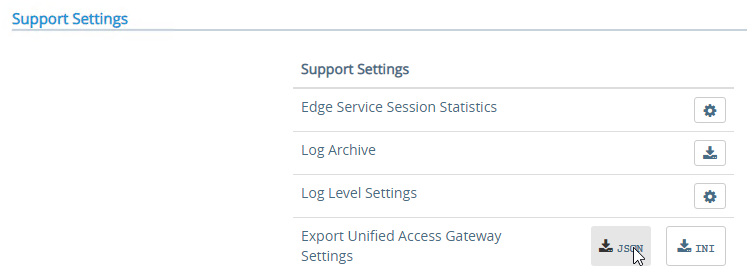
- Scroll down to the Support Settings section, and then click the JSON button next to Export Unified Access Gateway Settings.
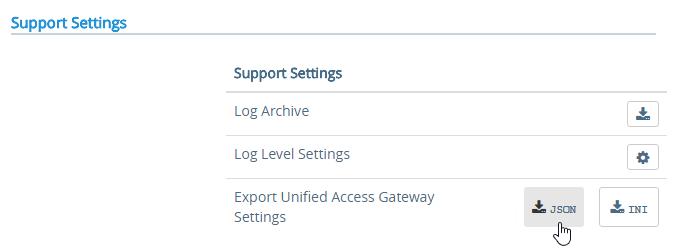
- Note: the exported JSON file does not include the UAG certificate, so you’ll also need the .pfx file. If RADIUS is configured, then during import you’ll be prompted to enter the RADIUS secret.
Deploy New
Horizon Compatibility – Refer to the interoperability matrix to determine which version of Unified Access Gateway is compatible with your version of Horizon.
- The latest version of UAG is 2503.
- You usually want the Non-FIPS version.
- You usually want the Non-FIPS version.
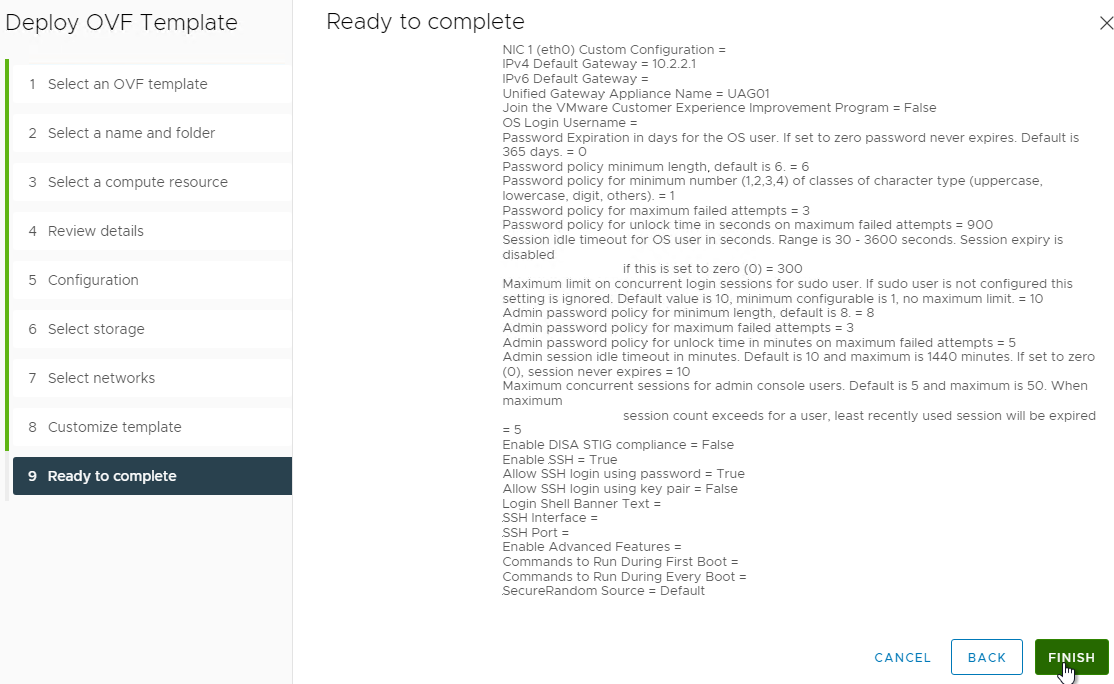
To deploy the Unified Access Gateway using VMware vSphere Client:
- If vSphere Client, right-click a cluster, and click Deploy OVF Template.
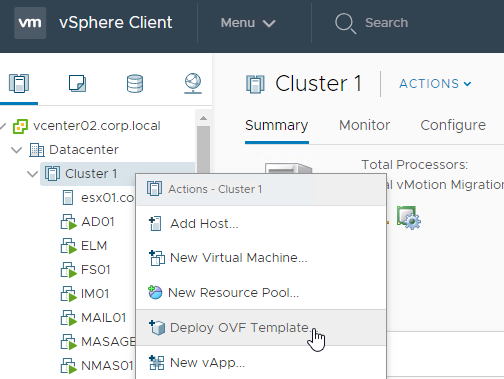
- Select Local File and click Upload Files. In the Open window, browse to the downloaded euc-unified-access-gateway.ova file, and click Next.
- In the Select a name and folder page, give the machine a name, and click Next.
- In the Review Details page, click Next.
- In the Select configuration page, select a Deployment Configuration. See Network Segments at Unified Access Gateway Architecture at Omnissa Tech Zone. Click Next.
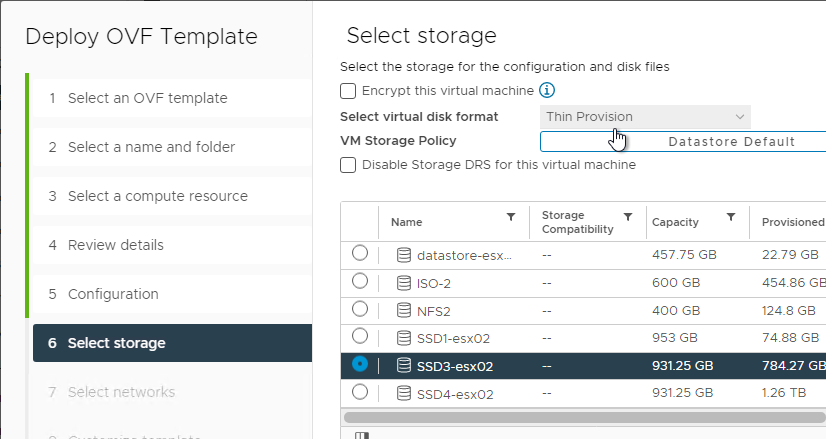
- In the Select storage page, select a datastore, select a disk format, and click Next.
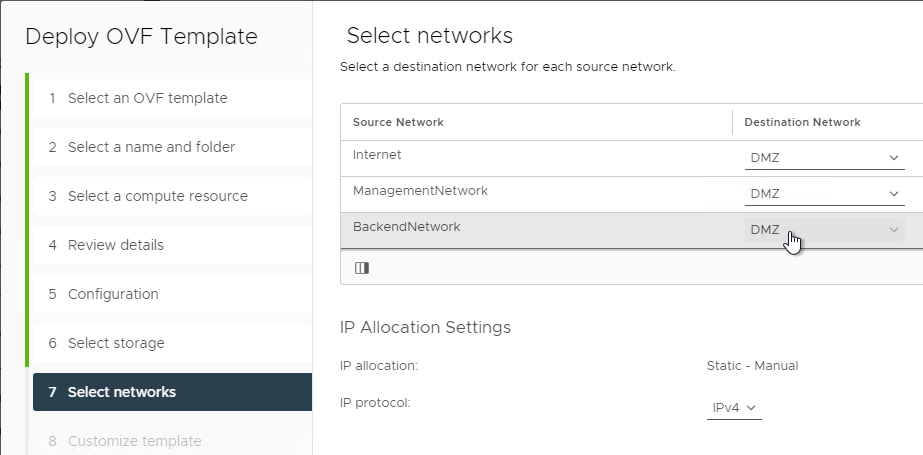
- In the Select networks page, even if you select Single NIC, the OVF deployment wizard asks you for multiple NICs. UAG typically goes in the DMZ.
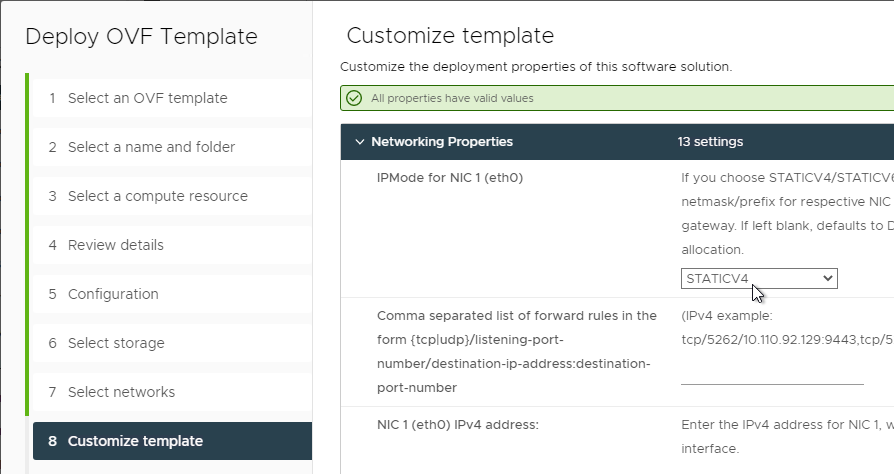
- In the Customize template page, select STATICV4, and scroll down.
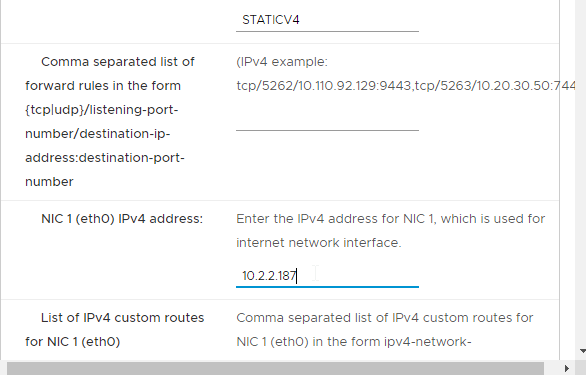
- In the NIC1 (eth0) IPv4 address field, enter the NIC1 (eth0) IPv4 address. Scroll down.
- Enter DNS addresses, Gateway, and Subnet Mask. Scroll down.
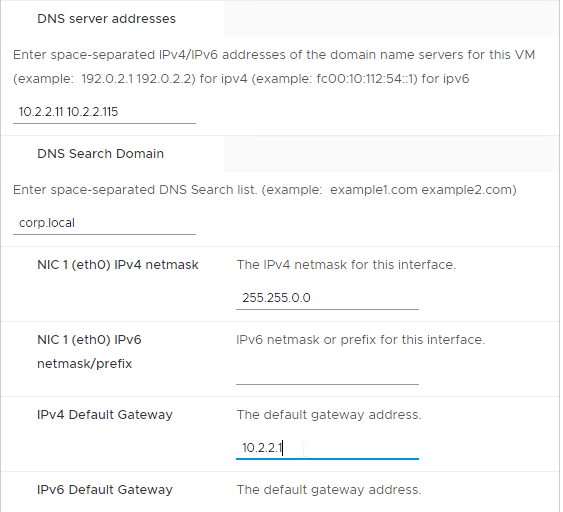
- Scroll down and enter more IP info.
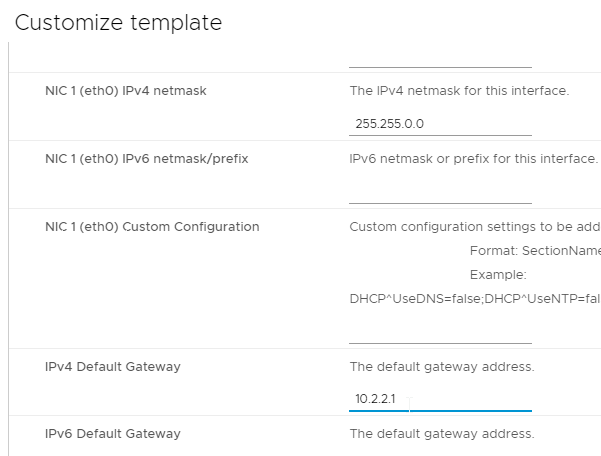
- Scroll down.
- Enter a Unified Gateway Appliance Name.
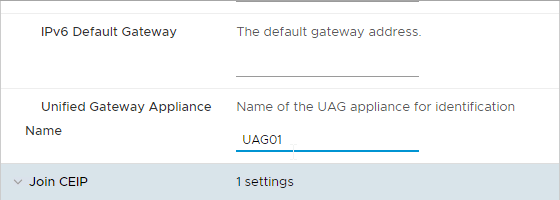
- Scroll down.
- UAG 2207 and newer let you specify the local root username.
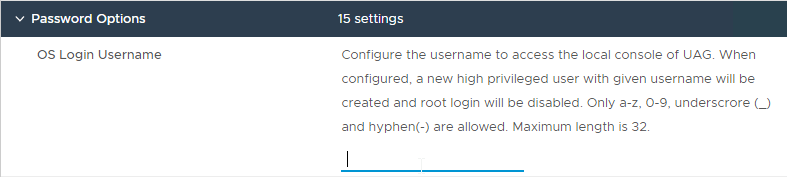
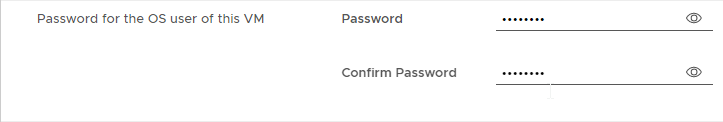
- Enter passwords.
- UAG 20.12 (2012) and newer let you specify Password Policy settings when deploying the OVF.
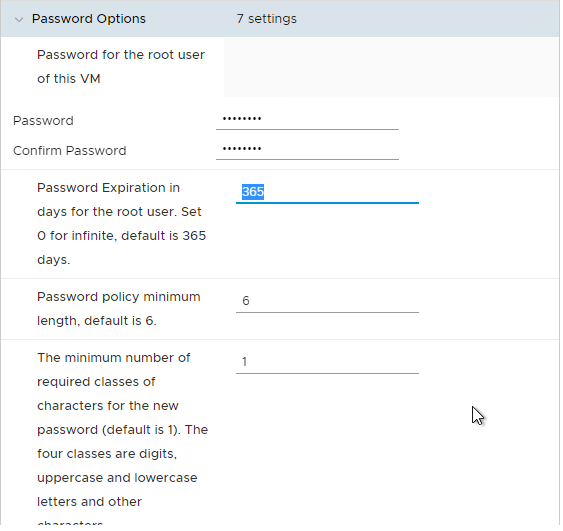
- UAG 20.12 (2012) and newer let you specify Password Policy settings when deploying the OVF.
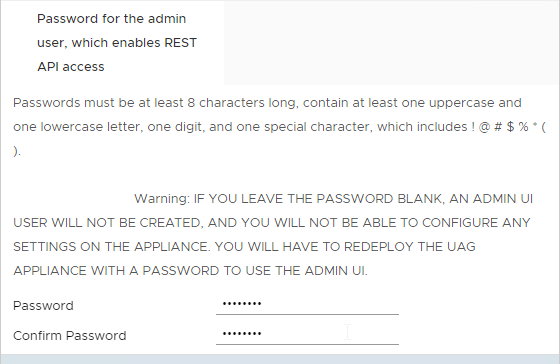
- Scroll down and enter the password for the admin user.
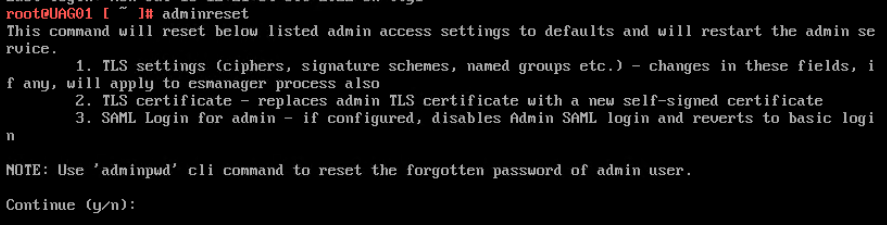
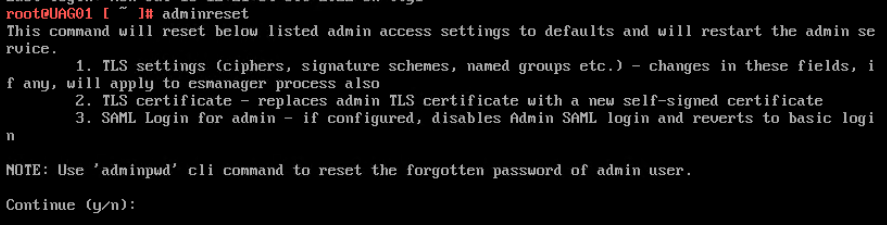
- UAG 2207 and newer have an adminreset command if you mess up the admin interface login. There’s also an adminpwd command to reset the password.
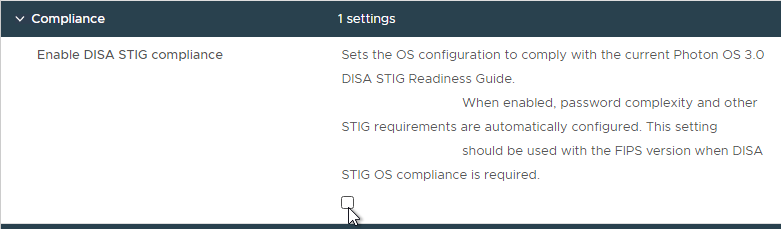
- UAG 2207 and newer have an option to enable DISA STIG compliance, usually on the FIPS version of UAG.
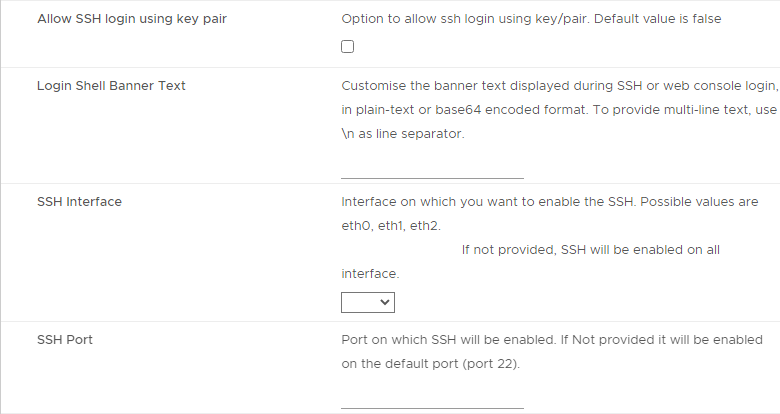
- There’s a checkbox for Enable SSH.
- In UAG 3.9 and newer, there’s an option to login using a SSH key/pair instead of a password.
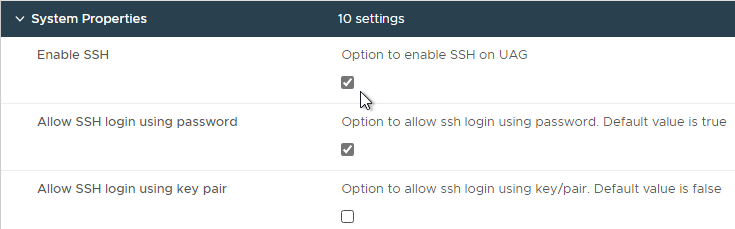
- Newer versions of UAG have more SSH options.
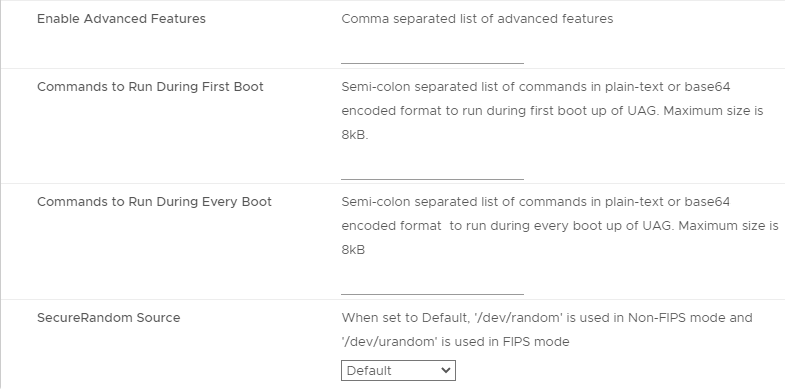
- UAG 2207 adds Commands to Run on First Boot or Every Boot.
- Click Next.
- In the Ready to complete page, click Finish.
UAG Admin Interface
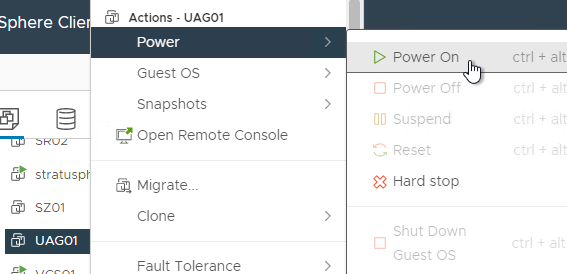
- Power on the Unified Access Gateway appliance.
- Point your browser to https://My_UAG_IP:9443/admin/index.html and login as admin. It might take a few minutes before the admin page is accessible.
- UAG 2207 and newer have an adminreset command if you mess up the admin interface login. There’s also an adminpwd command to reset the password.
Import Settings
- If you have previously exported settings, you can import it now by clicking Select in the Import Settings section.
- Browse to the previously exported UAG_Settings.json file and then click Import. Note that this json file might have old settings, like old ciphers. Review the file to ensure you’re not importing legacy configurations. If the .json file has a SHA-1 thumbprint, then edit the file and replace it with SHA-256 thumbprint (fingerprint).
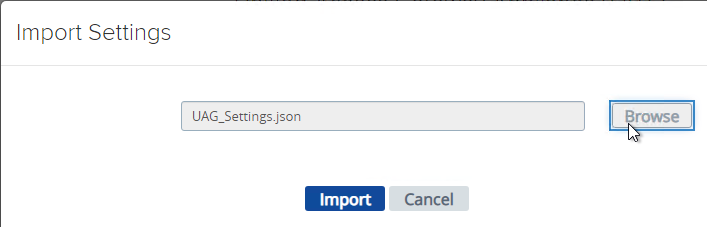
- It should say UAG settings imported successfully. If you don’t see this, then your .json file probably has a SHA-1 thumbprint.
- Press <F5> on your keyboard to refresh the browser.
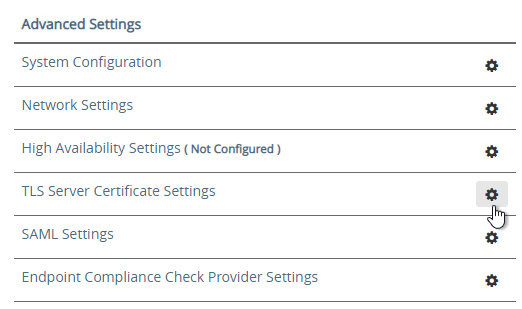
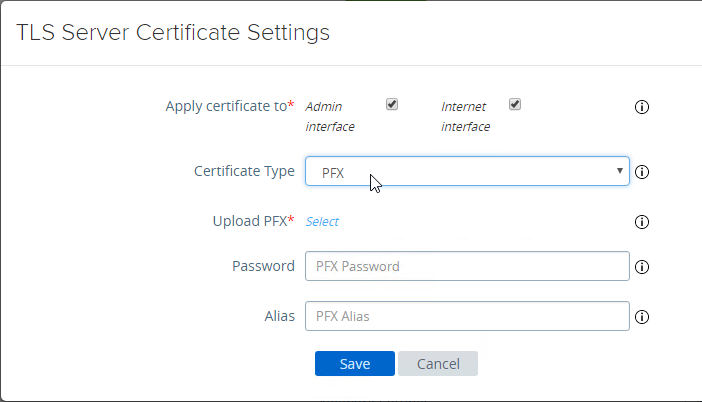
- The .json file does not include the certificate so you’ll have to do that separately. In the Admin console, in the Advanced Settings section, click TLS Server Certificate Settings.
- Check the box next to Internet Interface. Optionally uncheck the box next to Admin Interface.
- Change the drop-down for Certificate Type to PFX.
- In the row Upload PFX, click Select and browse to your PFX file.
- In the Password field, enter the PFX password and then click Save.
Configure Horizon Settings
- To manually configure the appliance, under Configure Manually, click Select.
- Click the slider for Edge Service Settings.
- Click the gear icon for Horizon Settings.
- Click the slider for Enable Horizon.
- As you fill in these fields, hover over the information icon to see the syntax.
- The Connection Server URL should point to the internal load balanced DNS name (URL) for your internal Connection Servers.
- For the Connection Server URL Thumbprint, get the thumbprint from the internal Horizon certificate. Point your browser to the internal Horizon Connection Server FQDN (load balanced) and click the padlock icon to open the certificate.
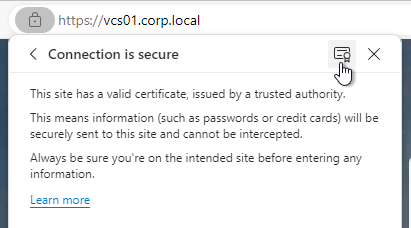
- On the Details tab, copy the SHA-256 Fingerprint. Note that SHA-1 thumbprint is no longer supported.
- For the Connection Server URL Thumbprint, get the thumbprint from the internal Horizon certificate. Point your browser to the internal Horizon Connection Server FQDN (load balanced) and click the padlock icon to open the certificate.
- In the Proxy Destination URL Thumb Prints field, type in
sha256=and paste the certificate thumbprint. - At the beginning of the Thumbprint field, immediately after the equals sign, there might be a hidden character. Press the arrow keys on the keyboard to find it. Then delete the hidden character.
- Enable the three PCOIP, Blast, and Tunnel Gateways and perform the following configurations:
- For PCOIP External URL, enter the external IP and
:4172. The IP should point to your external load balancer that’s load balancing UDP 4172 and TCP 4172 to multiple Unified Access Gateways. - For Blast External URL, enter https://<FQDN>:8443 (e.g. https://view.corp.com:8443). This FQDN should resolve to your external load balancer that’s load balancing UDP 8443 and TCP 8443 to multiple Unified Access Gateways.
- You could change the Blast port to 443 but this would increase CPU utilization on UAG. See Omnissa 78419 Unified Access Gateway (UAG) high CPU utilization.
- Link: Troubleshooting Blast at Omnissa Discussions
- For Enable UDP Tunnel Server, enable the setting.
- For Tunnel External URL, enter https://<FQDN>:443 (e.g., https://view.corp.com:443). This FQDN should resolve to your external load balancer that’s load balancing TCP 443 to multiple Unified Access Gateways.
- The external load balancer must be capable of using the same persistence across multiple port numbers. On NetScaler, this feature is called Persistency Group. On F5, the feature is called Match Across.
- For PCOIP External URL, enter the external IP and
- Then click More.
- Unified Access Gateway has a default list of paths it will forward to the Horizon Connection Server. You can edit the Proxy Pattern and add
|/downloads(.*)to the list so that users can also download Horizon Clients that are stored on your Horizon Connection Servers as detailed elsewhere at carlstalhood.com. Make sure you click Save at least once so it saves the default Proxy Pattern. Then go back in and add|/downloads(.*)to the end of the Proxy Pattern but inside the last parentheses. In UAG 2406, the default Proxy Pattern looks something like below:
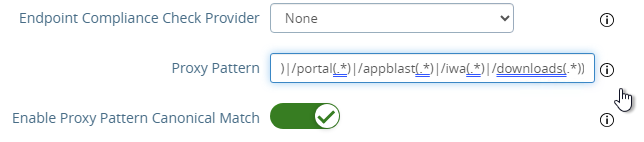
(/|/view-client(.*)|/portal(.*)|/appblast(.*)|/iwa(.*)|/downloads(.*))
- Scroll down and click Save when done.
- If you click the arrow next to Horizon Settings, then it shows you the status of the Edge services. It might take a minute or two to start working.
- In your Horizon Connection Servers, the Secure Gateways (e.g. PCoIP Gateway) should be disabled.
- Go to Horizon Console.
- Expand Settings and click Servers. On the right, switch to the tab named Connection Servers. Highlight your Connection Servers and click Edit.
- Then uncheck or disable all three Tunnels/Gateways.
- HTML Access probably won’t work through Unified Access Gateway. You’ll probably see the message Failed to connect to the Connection Server.
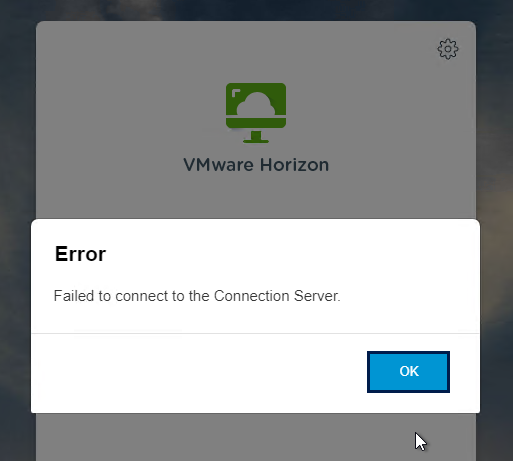
- To fix this, configure on each Connection Server the file C:\Program Files\Omnissa\Horizon\Server\sslgateway\conf\locked.properties (or C:\Program Files\VMware\VMware View\Server\sslgateway\conf\locked.properties) to disable Origin Check (checkOrigin=false) or configure the Connection Server’s locked.properties with the UAG addresses. Also see 2144768 Accessing the Horizon View Administrator page displays a blank error window in Horizon 7.
- Horizon 2106 and newer enable CORS by default so you’ll need to either disable CORS by adding enableCORS=false to C:\Program Files\Omnissa\Horizon\Server\sslgateway\conf\locked.properties (0r C:\Program Files\VMware\VMware View\Server\sslgateway\conf\locked.properties) or configure the portalHost entries in locked.properties as detailed at 85801 Cross-Origin Resource Sharing (CORS) with Horizon 8 and loadbalanced HTML5 access.
- After modifying the locked.properties file, restart the Omnissa Horizon Secure Gateway (or VMware Horizon View Security Gateway Component) service.
Add UAG to Horizon Console
In Horizon 7.7 and newer, you can add UAG 3.4 and newer to Horizon Console so you can check its status in the Dashboard.
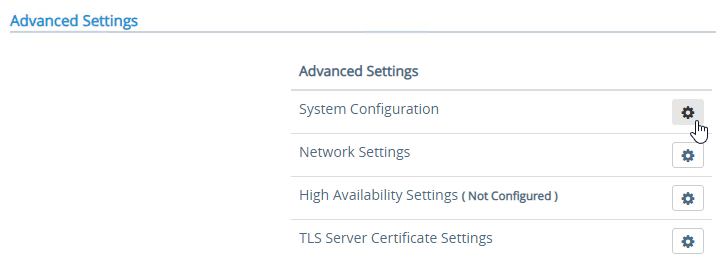
- In UAG Admin console, under Advanced Settings, click the gear icon next to System Configuration.
- At the top of the page, change the UAG Name to a friendly name. You’ll use this case-sensitive name later.
- Click Save at the bottom of the page.
- In Horizon Administrator Console, on the left, expand Settings and click Servers. On the right, switch to the tab named Gateways. Click the Register button.
- In the Gateway Name field, enter the case-sensitive friendly name you specified earlier, and then click OK.
See status of UAG appliances:
- Use a Horizon Client to connect through a Unified Access Gateway. Horizon Console only detects the UAG status for active sessions.
- In Horizon Console 7.10 and newer, to see the status of the UAG appliances, on the top left, expand Monitor and click Dashboard.
- In the top-left block named System Health, click VIEW.
- With Components highlighted on the left, on the right, switch to the tab named Gateway Servers.
- This tab shows the status of the UAG appliances, including its version. If you don’t see this info, then make sure you launch a session through the UAG.
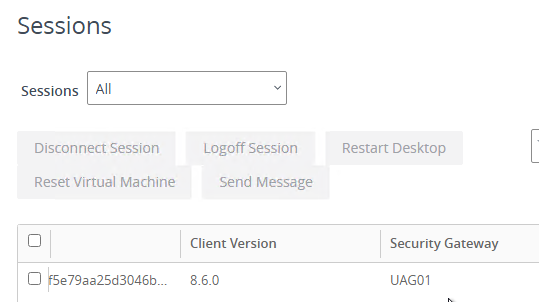
To see the Gateway that users are connected to:
- In Horizon Console 7.10 or newer, go to Monitor > Sessions.
- Search for a session and notice the Security Gateway column. It might take a few minutes for it to fill in.
UAG Authentication
SAML is configured in UAG 3.8 and newer in the Identity Bridging Settings section.
- Upload Identity Provider Metadata.
- Then in UAG Admin > Edge Service Settings > Horizon Settings > More (bottom of page), you can set Auth Methods (near top of page) to SAML only, which requires True SSO implementation, or SAML and Passthrough, which requires two logins: one to IdP, and one to Horizon.
- For complete True SSO instructions, see https://www.carlstalhood.com/vmware-horizon-true-sso-uag-saml/.
- For Okta and True SSO, see Enabling SAML 2.0 Authentication for Horizon with Unified Access Gateway and Okta: VMware Horizon Operational Tutorial at Omnissa Tech Zone.
- For Azure MFA, see Sean Massey Integrating Microsoft Azure MFA with VMware Unified Access Gateway 3.8.
For RADIUS authentication:
- Enable the Authentication Settings section and configure the settings as appropriate for your requirements. See Configuring Authentication in DMZ at VMware Docs.
- When configuring RADIUS, if you click More, there’s a field for Login page passphrase hint.
- When configuring RADIUS, if you click More, there’s a field for Login page passphrase hint.
- Then in Edge Service Settings > Horizon Settings > More (bottom of page), you can set Auth Methods (near top of page) to RADIUS.
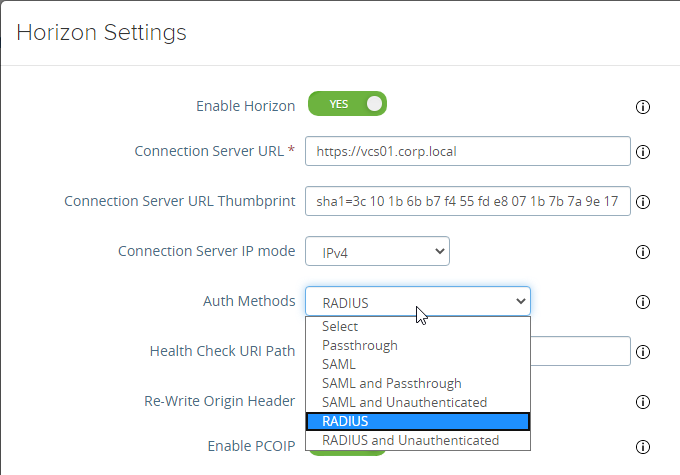
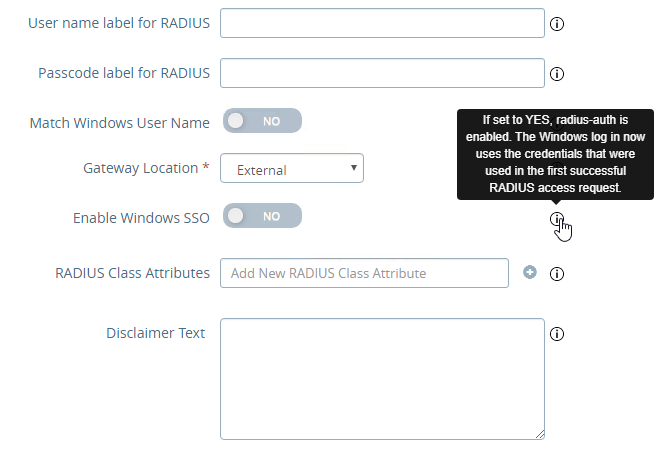
- If you scroll down the Horizon Settings page, you’ll see additional fields for RADIUS.
- In UAG 3.8 and newer, Passcode label field can be customized for MFA providers like Duo.
- If your RADIUS is doing Active Directory authentication (e.g. Microsoft Network Policy Server with Azure MFA), then Enable Windows SSO so the user isn’t prompted twice for the password.
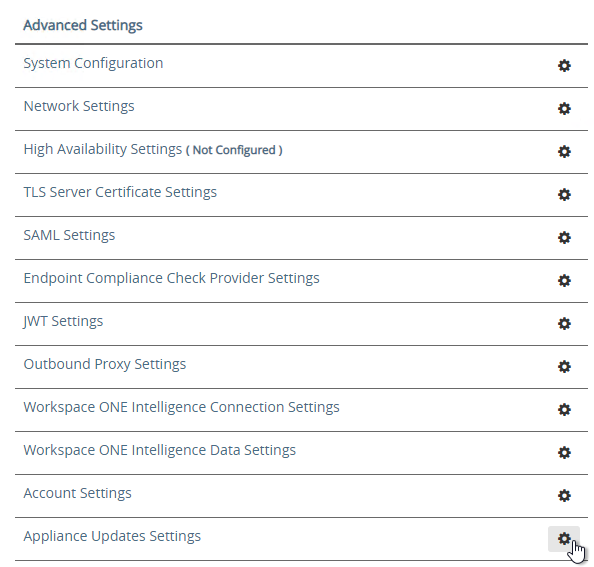
Other UAG Configurations
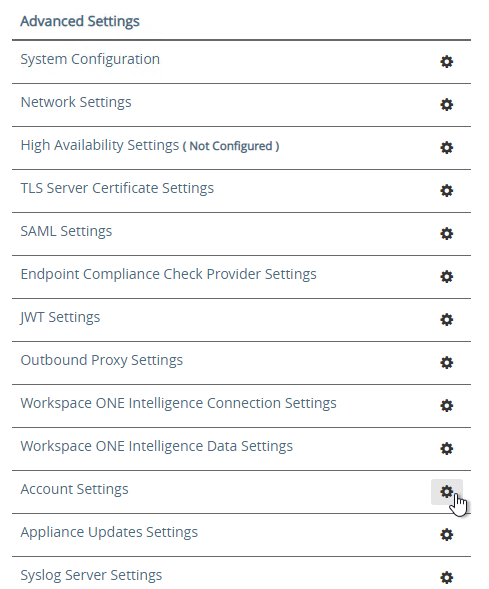
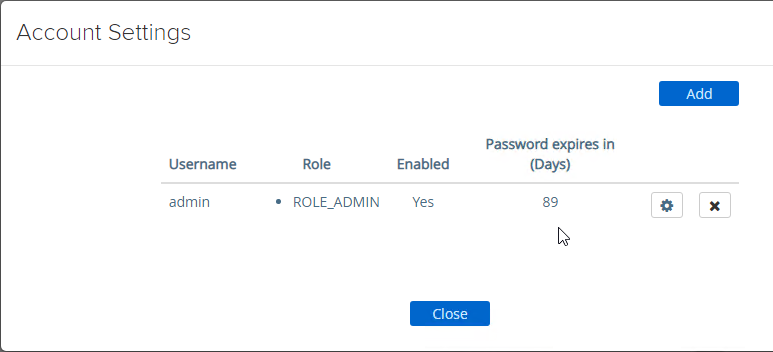
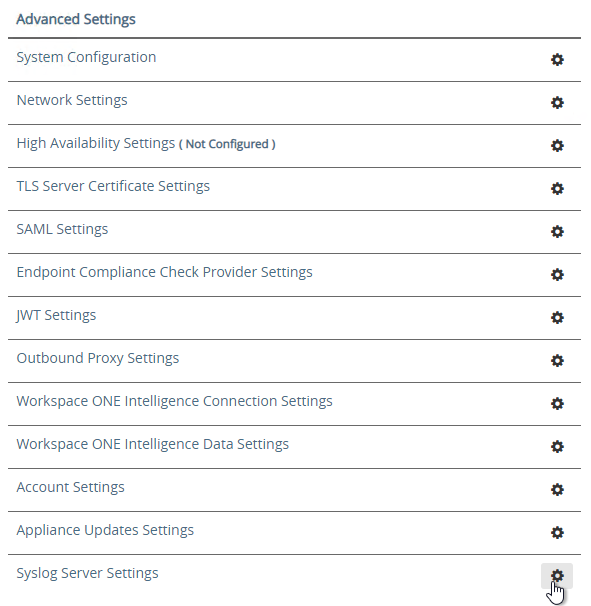
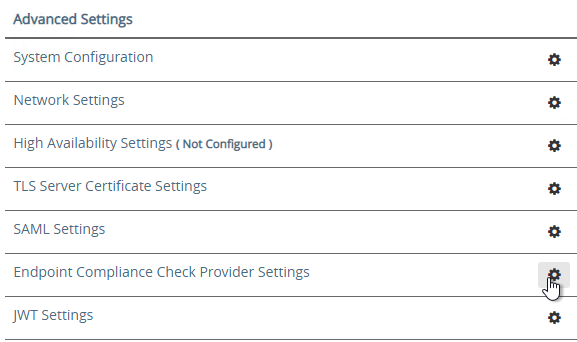
- UAG 3.8 and newer shows when the admin password expires in Account Settings in the Advanced Settings section.
- Ciphers are configured under Advanced Settings > System Configuration.
- The default ciphers in UAG 2412 are the following and include support for TLS 1.3.
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256,TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256,TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256,TLS_AES_128_GCM_SHA256,TLS_AES_256_GCM_SHA384,TLS_CHACHA20_POLY1305_SHA256
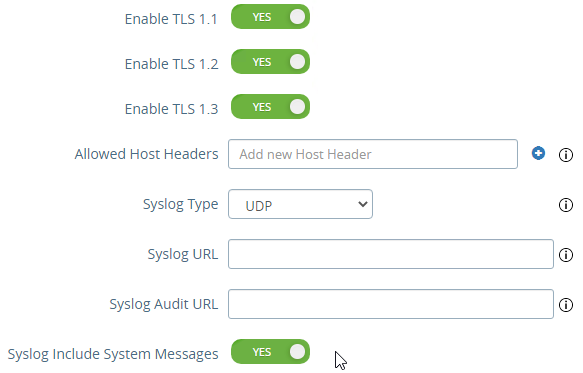
- In UAG older than 2103, Syslog is also configured here. In UAG 2103 and newer, Syslog is in a different menu as described below.
- At the bottom of the System Configuration page are several settings for SNMP, DNS, and NTP.
- UAG 20.12 (2012) and newer support SNMPv3.
- UAG 3.10 and newer have Admin Disclaimer Text.
- You can add NTP Servers.
- The default ciphers in UAG 2412 are the following and include support for TLS 1.3.
- Session Timeout is configured in System Configuration. It defaults to 10 hours.
- UAG 3.6 and newer let you add static routes to each NIC.
- Click Network Settings.
- Click the gear icon next to a NIC.
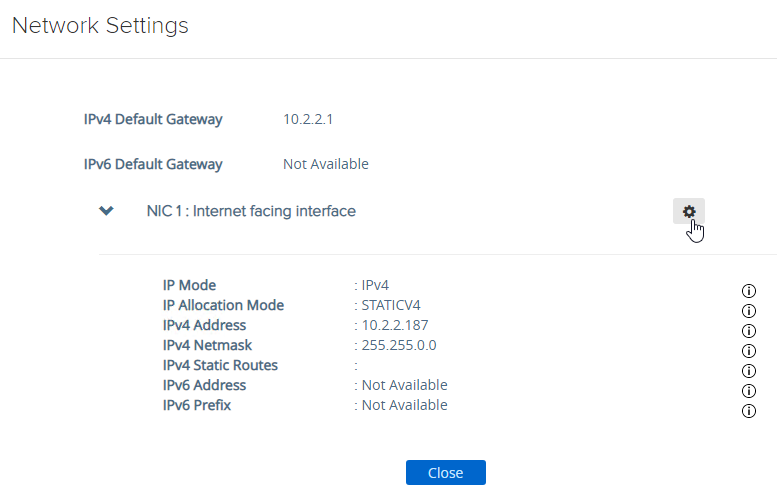
- Click IPv4 Configuration to expand it and then configure IPv4 Static Routes.
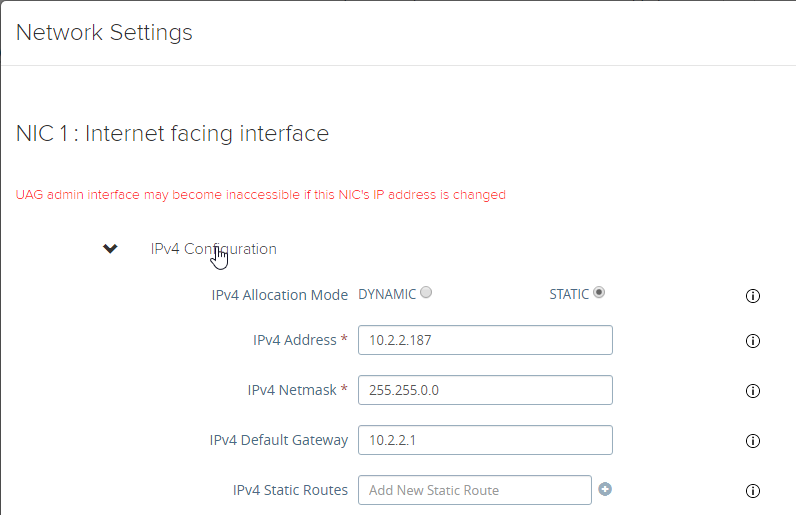
- Click Network Settings.
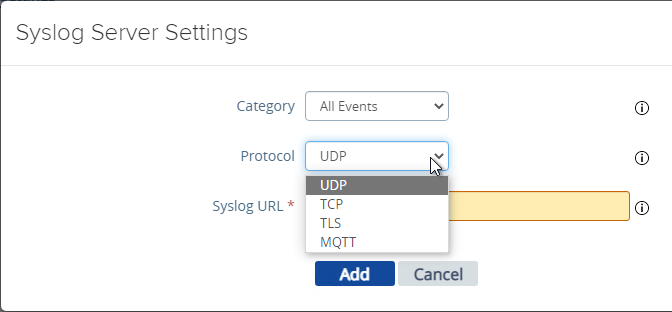
- UAG 2103 and newer have a different menu item for Syslog Server Settings.
- You can specify up to two Syslog servers.
- You can include System Messages.
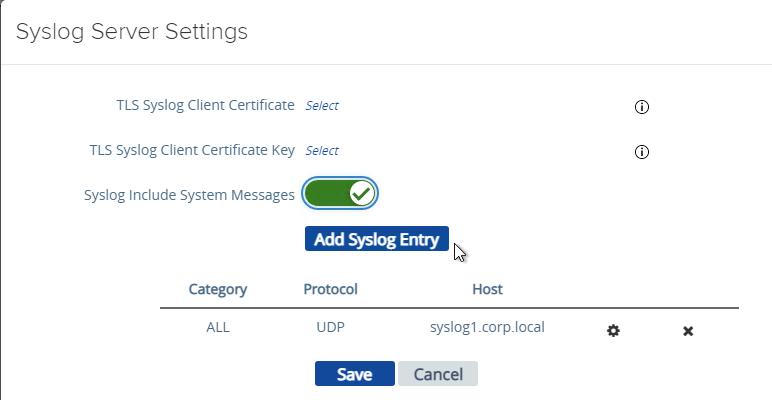
- UAG 2207 supports MQTT when adding Syslog servers.
- UAG 20.09 (2009) and newer can automatically install patches/updates when the appliance reboots.
- In the Advanced Settings section, click Appliance Updates Settings.
- For Apply Updates Scheme, select an option. Click Save.
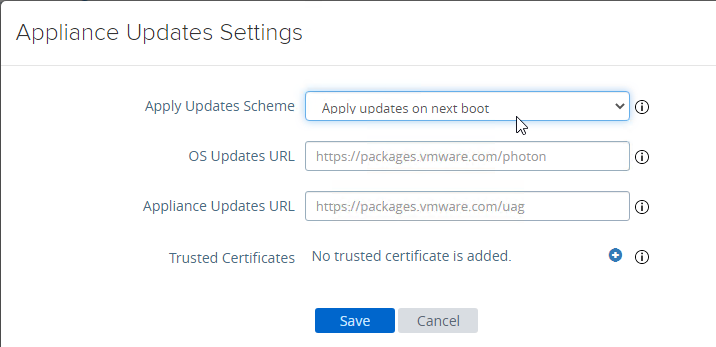
- In the Advanced Settings section, click Appliance Updates Settings.
- UAG supports High Availability Settings.
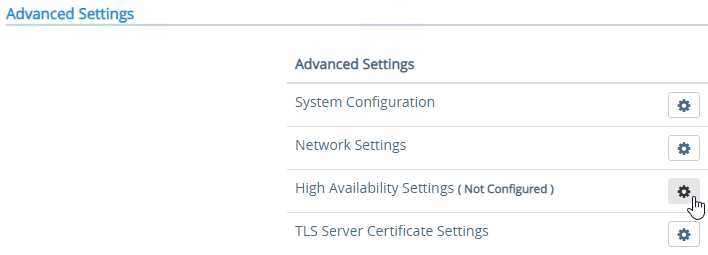
- With the High Availability Virtual IP address, you might not need load balancing of the UAG appliances. See Unified Access Gateway High Availability at Omnissa Docs.
- The High Availability feature requires three IP addresses and three DNS names:
- One IP/FQDN for the High Availability Virtual IP.
- And one IP/FQDN for each appliance/node.
- The Horizon Edge Gateways should be set to node-specific IP addresses and node-specific DNS names. Each appliance is set to a different IP/FQDN.
- The Virtual IP (and its DNS name) is only used for the High Availability configuration.
- The YouTube video High Availability on VMware Unified Access Gateway Feature Walk-through explains the High Availability architecture.
- The High Availability feature requires three IP addresses and three DNS names:
- Set the Mode to ENABLED.
- Enter a new Virtual IP Address which is active on both appliances.
- Enter a unique Group ID between 1 and 255 for the subnet.
- Click Save.
- On the second appliance, configure the exact same High Availability Settings.
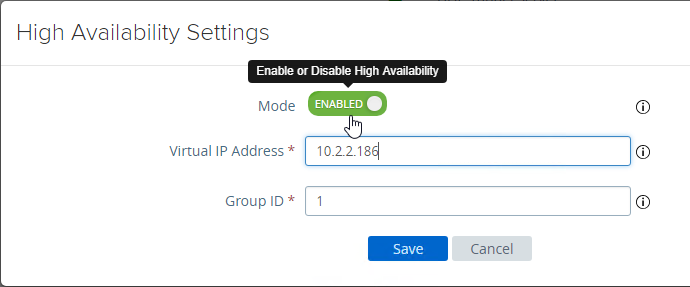
- With the High Availability Virtual IP address, you might not need load balancing of the UAG appliances. See Unified Access Gateway High Availability at Omnissa Docs.
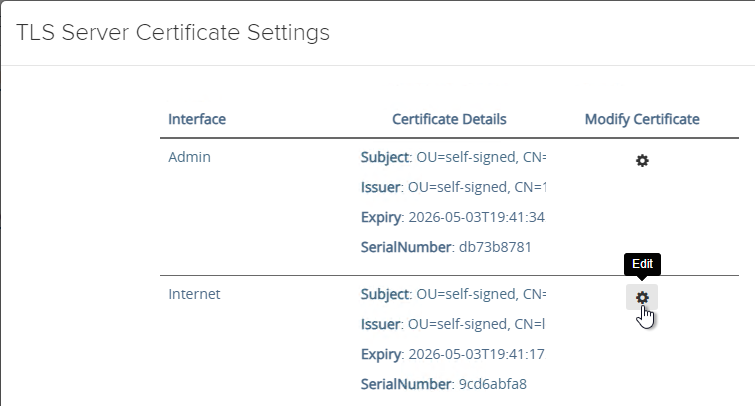
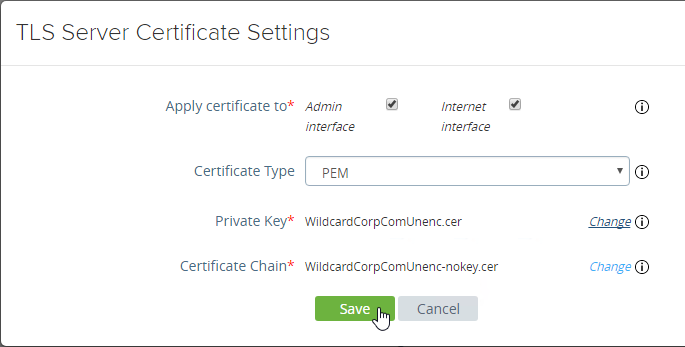
- To upload a valid certificate, scroll down to the Advanced Settings section, and next to TLS Server Certificate Settings, click the gear icon.
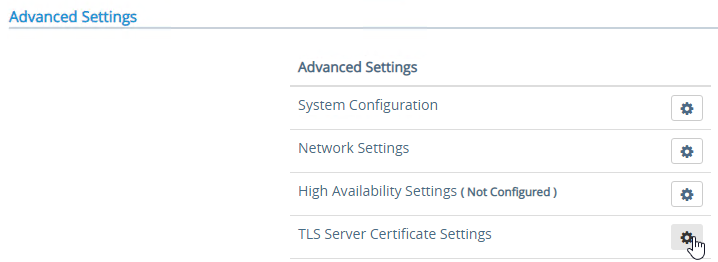
- In Unified Access Gateway 2312 and newer, click Edit in the Internet section.
- In Unified Access Gateway 3.2 and newer, you can apply the uploaded certificate to Internet Interface, Admin Interface, or both.
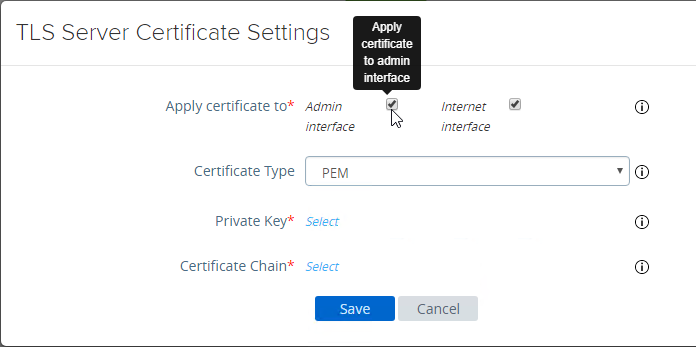
- In Unified Access Gateway 3.0 and newer, change the Certificate Type to PFX, browse to a PFX file, and then enter the password. This PFX file certificate must match the Public FQDN (load balanced) for Unified Access Gateway. If your load balancer is terminating SSL, then the certificate on the UAG must be identical to the certificate on the load balancer.
- Leave the Alias field blank.
- Click Save.
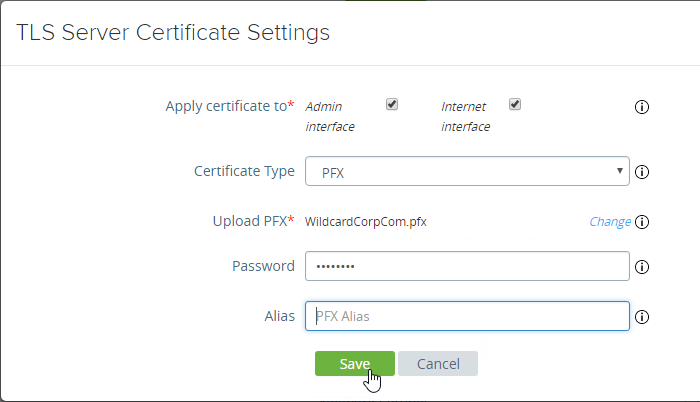
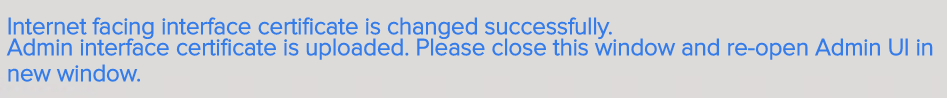
- If you changed the Admin Interface certificate, then you will be prompted to close the browser window and re-open it.
- In Unified Access Gateway 2312 and newer, click Edit in the Internet section.
- Or, you can upload a PEM certificate/key (this is the only option in older UAG). Next to Private Key, click the Select link.
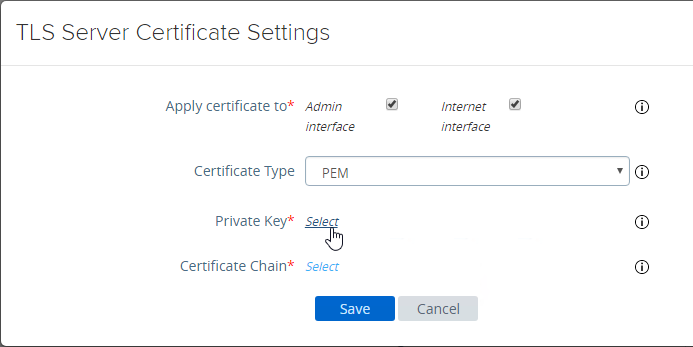
- Browse to a PEM keyfile. If not running Unified Access Gateway 3.0 or newer, then certificates created on Windows (PFX files) must be converted to PEM before they can be used with Unified Access Gateway. You can use openssl commands to perform this conversion. The private key should be unencrypted.
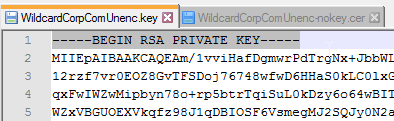
- Browse to a PEM certificate file (Base-64) that contains the server certificate, and any intermediate certificates. The server certificate is on top, the intermediate certificates are below it. The server certificate must match the public FQDN (load balanced) for the Unified Access Gateway.
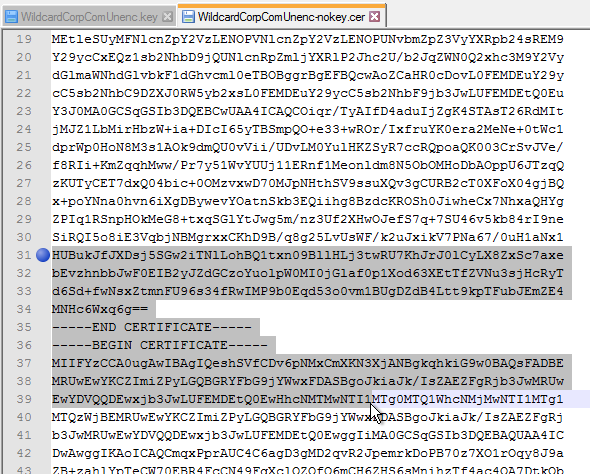
- Click Save when done.
- Browse to a PEM keyfile. If not running Unified Access Gateway 3.0 or newer, then certificates created on Windows (PFX files) must be converted to PEM before they can be used with Unified Access Gateway. You can use openssl commands to perform this conversion. The private key should be unencrypted.
- UAG 3.1 and newer have an Endpoint Compliance Check feature. The feature requires an OPSWAT subscription. Newer versions of UAG can deploy the OPSWAT agent. It’s pass/fail. See Configure OPSWAT as the Endpoint Compliance Check Provider for Horizon at VMware Docs.
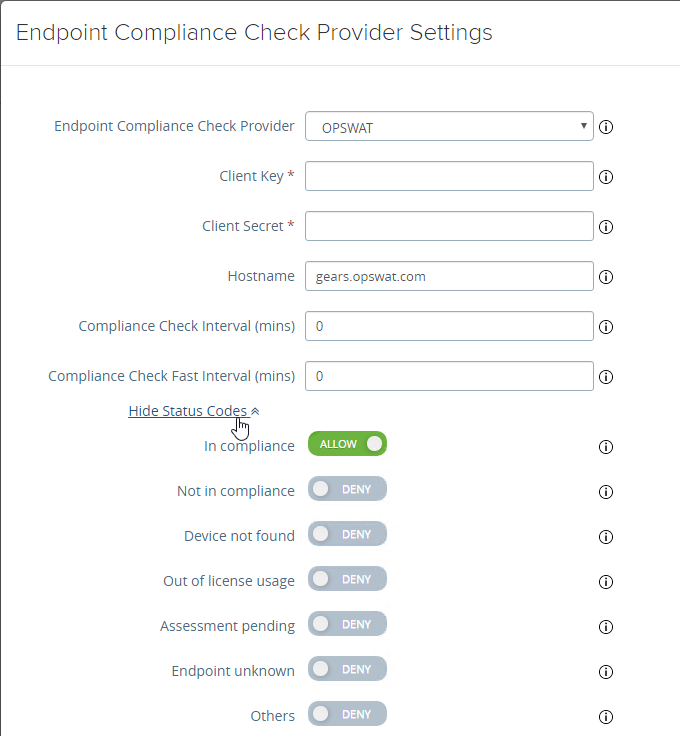
- UAG 3.9 and newer let you upload the Opswat Endpoint Compliance on-demand agent executables. Horizon Client downloads the executables from UAG and runs them. See Upload OPSWAT MetaAccess on-demand agent Software on Unified Access Gateway at VMware Docs.
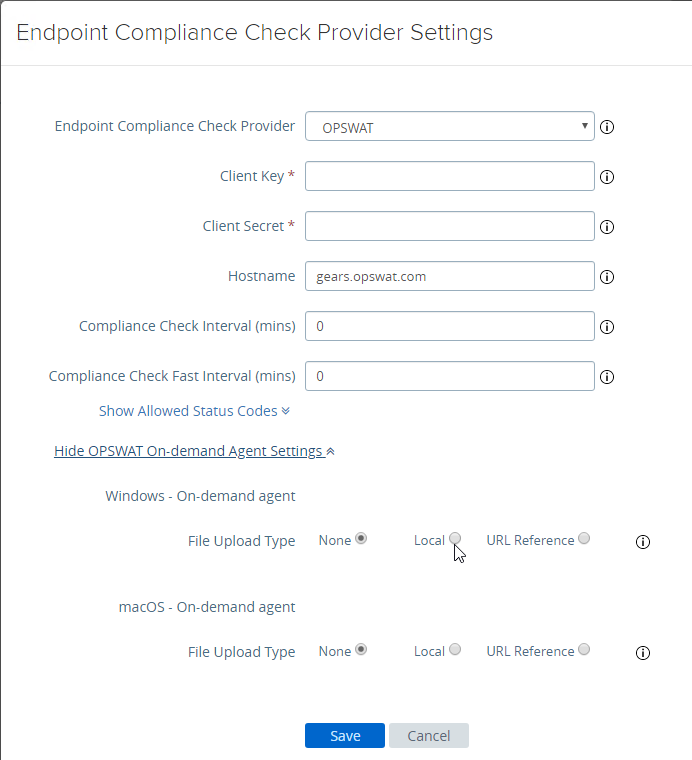
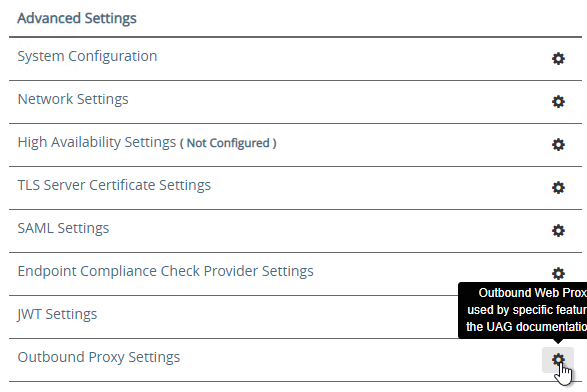
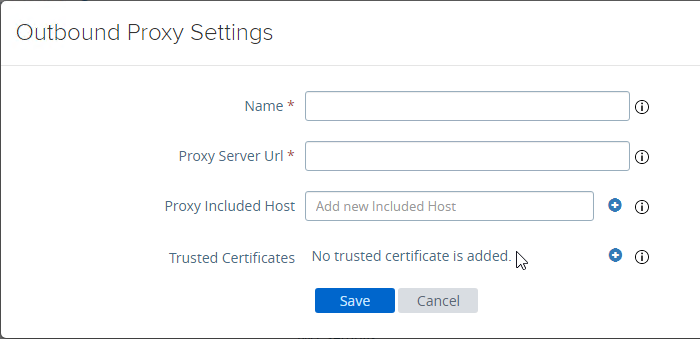
- In UAG 20.09 and newer, Outbound Proxy Settings can be configured to allow UAG to contact the Opswat servers when checking for device compliance.
- UAG 3.9 and newer let you upload the Opswat Endpoint Compliance on-demand agent executables. Horizon Client downloads the executables from UAG and runs them. See Upload OPSWAT MetaAccess on-demand agent Software on Unified Access Gateway at VMware Docs.
- Scroll down to Support Settings and click the icon next to Export Unified Access Gateway Settings to save the settings to a JSON file. If you need to rebuild your Unified Access Gateway, simply import the the JSON file.
- The exported JSON file does not include the UAG certificate, so you’ll also need the .pfx file.
- The exported JSON file does not include the UAG certificate, so you’ll also need the .pfx file.
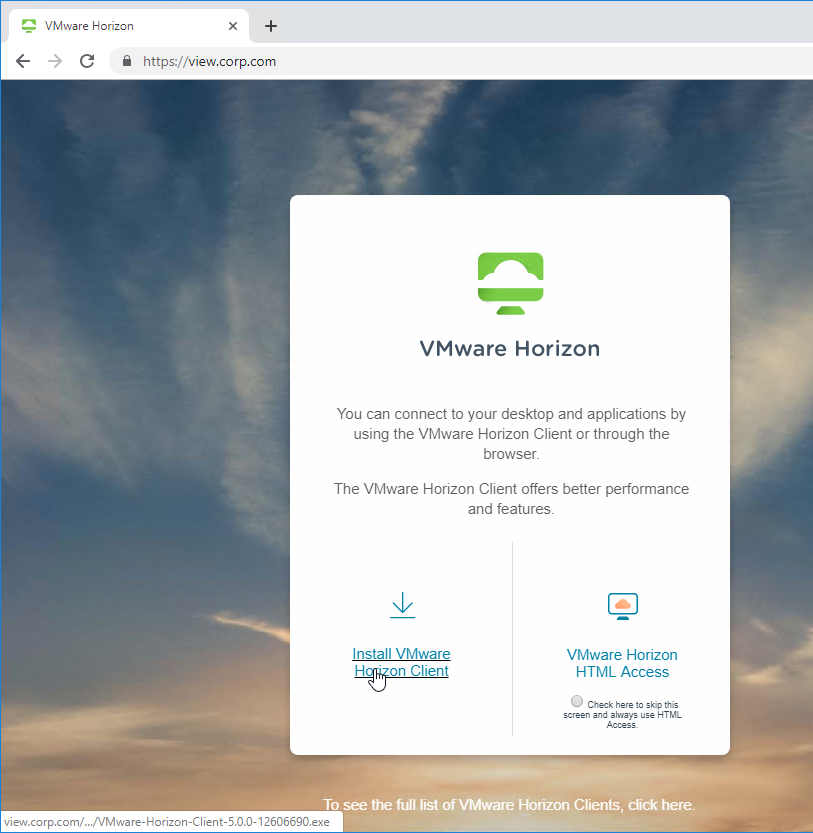
- If you point your browser to the Unified Access Gateway external URL, you should see the Horizon Connection Server portal page. Horizon Clients should also work to the Unified Access Gateway URL.
Monitor Sessions
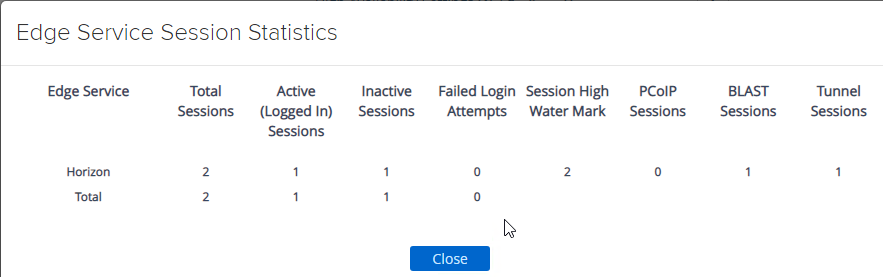
In UAG 3.4 and newer, in the UAG Admin interface,
- At the top of the page, next to Edge Service Settings, you can see the number of Active Sessions on this appliance.
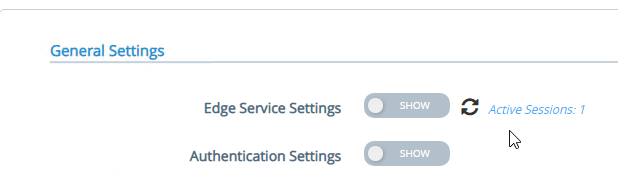
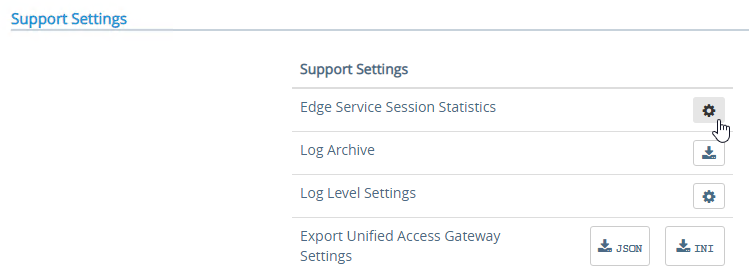
- At the bottom of the page, under Support Settings, click Edge Service Session Statistics to see more details.
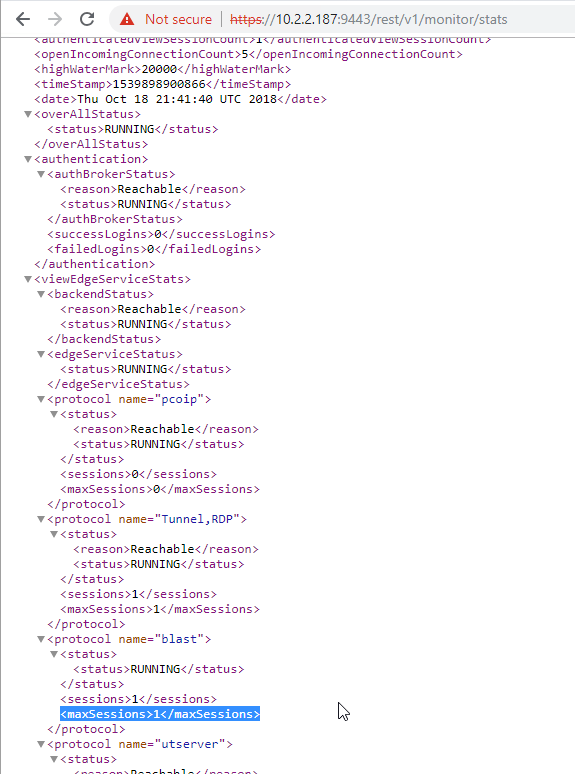
In older versions of UAG, to see existing Horizon connections going through UAG, point your browser to https://uag-hostname-or-ip-addr:9443/rest/v1/monitor/stats.
Logs and Troubleshooting
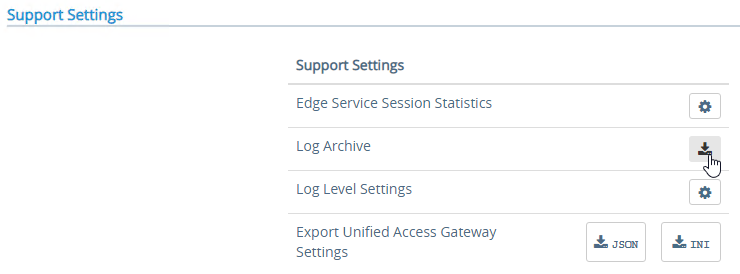
You can download logs from the Admin Interface by clicking the icon next to Log Archive.
You can also review the logs at /opt/vmware/gateway/logs. You can less these logs from the appliance console.
Or you can point your browser to https://MyApplianceIP:9443/rest/v1/monitor/support-archive. This will download a .zip file with all of the logfiles. Much easier to read in a GUI text editor.
For initial configuration problems, check out admin.log.
For Horizon View brokering problems, check out esmanager.log.
By default, tcpdump is not installed on UAG. To install it, login to the console and run /etc/vmware/gss-support/install.sh
- More info at Justin Johnson Troubleshooting Port Connectivity For Horizon’s Unified Access Gateway 3.2 Using Curl And Tcpdump
Load Balancing
If NetScaler, see https://www.carlstalhood.com/vmware-horizon-unified-access-gateway-load-balancing-citrix-adc/ load balance Unified Access Gateways.
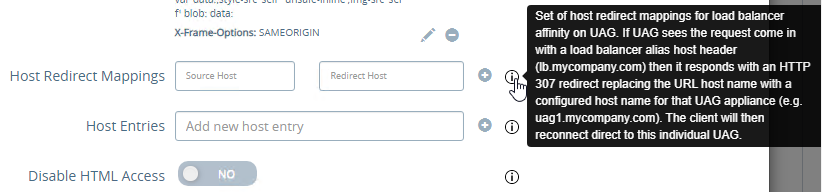
To help with load balancing affinity, UAG 3.8 and newer can redirect the load balanced DNS name to a node-specific DNS name. This is configured in Edge Service Settings > Horizon Settings > More (bottom of page).
Related Pages
- Back to Omnissa Horizon 8
Hi, great articles as always Thank you.
We have Horizon 8 consisting of UAG’s, TrueSSO and ADFS SAML auth. Our ADFS token signing and token encryption certs are due to expire so I was hoping you could give guidance on the steps please. We are adding the new certs as secondary in ADFS for a week before promoting the new cert to primary so I was planning to download the new ADFS metadata, upload to the UAG’s and import into the Connection Servers as normal.
Thanks
How to add another user with role admin on the UAG? I have tried different methods and only did an account with monitoring role.
Here is a note that I hope saves someone time. If you deploy your UAG via the OVA through the GUI (maybe this happens via other deployment methods too) and you put in a password for the API (which you have to do in order for the Admin GUI to work), but it doesn’t meet the requirements, then the OVA will deploy successfully, but the Admin GUI will not work. And there is no warning or anything telling you that your password is crap. It won’t stop you from entering a password that is not good enough.
As this may be helpful to others:
If, for some reason, you see an error message ERR_TUNNEL_CONNECTION_FAILED when trying to open up the admin interface via :9443 even if the VM is pingable, generally responding and behaving correctly try this:
http:/// → Enter
This should forward you to the correct login page. Don’t ask me why, I deployed this freaggin’ thing at least three times and couldn’t reach it via https, so http instead with IP address only and that worked.
Also *do NOT use* a password with a ‘+’ character for the admin user in the UAG .ova enrollment wizard; the deployment will proceed successfully and will not show an error message, but it will fail to setup the admin account properly.
Maybe a portable browser also comes in handy. This thing’s as unstable as an IKEA nightstand until fully set up.
Hello Carl,
I replaced the certificate on my (external) connection servers with an external certificate issued by an external party. I also installed this certificate on the external UAG by means of an import of the PFX. However, after this the connection server can no longer communicate with the UAG, unless I specify the thumbprint of the certificate on the UAG. This has always worked this way. Can you point me in the right direction and indicate why this no longer works? The UAG version is 25.03
Thanks in avance!!
In former versions I used command “tail -f /opt/vmware/gateway/logs/authbroker.log | grep -i user” for monitoring / troubleshooting logons.
It seems this log does not longer exist or has been moved.
Recommondation or hard line?
“If you are running an ESB version of Horizon, then make sure you run the ESB version of Unified Access Gateway.”
Interoperability matrix says Horizon 2312.x is ok with UAG 2412.
You’re probably right. It looks like UAG is not covered by ESB. https://kb.omnissa.com/s/article/86477
Hi Carl,
thx for your awesome webpage.
We have an issue that pops up from time to time.
Suddenly the UAG is no longer accessiable and runs into a timeout.
We exported the logs and Omnissa states its a SSL Handshake issue.
We have 2 ENVs running and 1 of them runs always fine. Its only the 2nd one that is the problem.
They are setup the same way (besides the URLs)
Each ENV has 2 UAGs, 2 INT Conn Servers and 2 EXT Conn Servers
After a Reboot of the UAGs it works again.
Do you have any idea how to debug this?
What is your load balancer? What probe/monitor is configured?
we use Kemp Loadbalancer with 443 and (one udo one tcp) 8443 source IP affinity
Real Server check Methode is TCP connection only and then the port (8443 or 443)
We also have set
Subnet Originating Request
Persistence options Source IP (1h timeout)
Port folowing on the UAG IP
Add HTTP Headers is set to Legaxy Operation X-Forward-For)
Those were all according to the KEMP KB
Hi,
We have setup F5 external LB with 2 UAGs and 2 Connection Servers. UAG 1 points to CS1, and UAG2 to CS2. If I reboot for example CS1 then I get http error to the F5 VIP address, probably because CS1 is not available and UAG1 tried to contact it. Do we need to have an internal loadbalancer aswell that points to both Connection Servers? e.g. horizon.view.internal?
I normally point UAGs to the load balanced Connection Servers instead of single. Or make sure your F5 has good probes/monitors for the UAGs.
Thank you. So this would be the recommended setup then instead of pointing UAGs directly to Connection Servers (UAG1 -> CS1, UAG2 -> CS2)
Example:
F5: horizon.external.com points to UAG1&2
UAGs: Points to horizon.connect.com (Connection Servers 1 & 2) instead of UAG1 pointing to CS1 and UAG2 pointing to UAG2?
Back when Horizon (or View if you go back far enough) had “Security Servers” instead of UAGs, those had to point to a specific Connection Servers (ss1 > cs1, ss2 > cs2). One of the benefits of UAGs was that pairing was no longer required, which allowed you to further load balance between connection servers.
Our environment points users to connect to a load balancer URL, which splits between two UAGs. The UAGs themselves point to another load balancer URL, which splits between Connection Servers.
public.your.domain > uag1/uag2 > internal.your.domain > cs1/cs2
Hello,
We are trying to upgrade our UAG from 3.10 to current. I have exported the json and we we have brought up the upgraded UAG on a VM. When I try to import the json it prompts for the api server password and gives an error json mapping exception while processing request. I am at an impass. Any thoughts or suggestions?
Current UAG requires SHA256 thumbprints instead of SHA1.
You can also download the logs from UAG to see what the issue is.
Hi Carls,
We have a Horizon setup with **four connection servers** behind an **internal F5 load balancer**. Recently, we deployed **two UAGs** and configured **SAML authentication**.
Here’s our current certificate setup:
– **UAGs & Connection Servers:** Using an **internal CA certificate**.
– **F5 Load Balancer:** Using a **public certificate**.
### **Issue:**
We are encountering a **tunnel certificate mismatch error**. To resolve this, we have a few questions:
1️⃣ Should we use the **same public certificate** for both UAGs and F5 to ensure consistency?
2️⃣ What **SANs (Subject Alternative Names)** should be included in the certificate to avoid authentication issues?
3️⃣ Do we need to create **DNS records for the UAGs**, given that they are deployed in the **DMZ network**?
Would appreciate your guidance on the best approach to resolve this. Thanks!
The cert on the F5 and the cert on the UAGs must be identical (same thumbprint) to avoid issues in the Horizon Client.
Thank you Carl.
Since the F5 cert is public cert. We would like to know what SANs we suppose to use. We will use SSL cert not the wild card cert.
We do have two load balancer URLs (one is internal and one is external). Two UAGs and 4 connection servers. So what SANs we suppose to use in public cert that is going to use for F5 and UAGs. Appreciated your kind response.
The SAN should match whatever FQDN that users are using and any SSL Tunnel or Blast Gateway FQDN.
Thanks for a great blog.
Exactly which connections need to have identical thumbprints?
Is it the UDP tunnel, or Blast Extreme (8443)? Or both?
Does F5 know how to terminate SSL offload for Blast and the UDP tunnel (instead of just NAT). So that you can get the same cert on F5 instead of having to copy same certificates to uag?
If Secure Tunnel is enabled in UAG, then Horizon Client first connects to the load balancer and then creates a second connection to the Secure Tunnel URL, which is on the UAG. However, Horizon Client uses the thumbprint of the first connection to verify the cert for the second connection. Thus, the load balancer cert and the UAG cert must be identical.
Yeah, thats why I wonder if its possible to terminate the secure tunnel on the load balancer aswell, so that from the client perspective, it always is shown the right certificate.
Hello Carl,
Thanks for your wonderful website and precious advices.
I’m using UAG 2406 and My Horizon View Connection Server 2406 too. My problem is that I’m not able to deactivate HTML access for Horizon View. With “Disable HTML access” ON or OFF in Edge/Horizon settings of my UAG, HTML sessions are still going thru?
(I have also restarted the UAG after each change just in case this would apply only at startup)
Any idea?
Bests
Laurent
You can also disable it at the paired Connection Server – https://docs.omnissa.com/bundle/HorizonHTMLAccessGuideV2406/page/ConfiguringHTMLAccessforEndUsers.html#:~:text=Set%20the%20Disable%20HTML%20Access,a%20Folder%20for%20Branding%20section.
We just upgraded UAG from 2212 to 2406. Load Balancer access is giving us HTTP 400 error. Any idea? We can connect directly to the UAG IPs with no issues.
I’m sure you’ve likely solved your own issue by now, but if someone else comes looking, what worked for us when getting this HTTP 400 error was to make sure the Tunnel External URL is the FQDN or IP of the load balancer, not the UAG itself.
Hello Carl,
I need to implement UAGs in a very unconventional way. They need to support both external and internal users, end users cannot go directly to the connection servers, they need to go through the UAGs first. I need to implement SAML authentication integrated with Microsoft Azure MFA for external users, but for internal users this doesn’t make sense, they must authenticate only in Horizon. Is it possible to implement this with just one group of UAGs, or do I need one UAGs group for external users and another UAGs group for internal users?
Thank you very much!
UAGs don’t have conditional authentication so you would need separate UAGs for internal vs external. Or you can deploy Omnissa Access, which does have conditional authentication.
Hi Carl,
Just wanted to drop a humungous thank you for all the information, support, and detail you provide to this community. Following your guides this past weekend, I was able to update both my UAG and Connection Server without any major hiccups. Can’t say it would have gone so well without your thorough guidance. Much appreciated!
Hello,
I just installed UAG 2406.1. It works perfectly with the Horizon View Client and Connections Servers (same version).
HTML access is disabled so when I connect to the UAG with a web browser (Chrome), I get the the “You must use Horizon Client for Windows to access this Server.” message, The only thing that is boring me is that logo in the upper left corner of this message webpage is missing (ref: /styles/clientlaunch-default/343x62_vmware_banner.png). How can I fix that?
Thanks, regards,
What Proxy Pattern do you have configured?
Hi, Carl
is it any way to use to use a different certificate on the load balancer and Unified Access Gateway ?
As i see in documentanion
It is possible to use a different certificate on the load balancer and Unified Access Gateway in which case you can configure the public load balancer certificate for the Tunnel and Blast sessions so that the thumbprint mismatch will not occur.
This means that I need to configure (upload) a Blast Proxy certificate and a Tunnel Proxy certificate, right?
Hi, we are deploying the UAG to AWS using Terraform but for some reason it’s not taking the ‘threenic’ deployment type from the userdata, although it’s taking all the other configs from there (admin and root pwd, SSH, SSH interface, etc)
Is there a way to change the UAG to three NIC type after it’s deployed, using SSH console?
Btw, the actual NICs are there, I can see them from the SSH console.
Thanks.
Hi Carl,
I came across this blog while searching for an issue that I am facing after upgrading horizon environment from 2111.1 to 2312.1.
Our setup is having one UAG and 2 connection servers behind a NetScaler VIP. Internal access is working fine with out any issues.
Problem is with external access. I am able to login both via web browser and horizon client and see the assigned pools. Once I click the pool it shows loading desktop and then disconnects with VDP_CONNECT FAILURE the connection to remote desktop ended. There are no changes to existing rules for VDI in firewall.
I know its a generic error. What would be the best way to troubleshoot this issue?
If you download the logs from UAG, look in esmanager log and bsg.log for issues.
Is this all the time? We get it also, but it appears for us it is related to reconnecting to an existing session from a client that has been left open at the pool screen. We have a setting “Discard SSO Credentials” set at 2 minutes. This forces a credential check so if you disconnect from the existing session or create a new one it will require creds again. We had to restart the blast service for users constantly, maybe 3+ times a day for random people. It was getting really frustrating and then we change that setting to never and it went away. We stopped getting the VDP Connect Failures completely once we changed that setting. I have a ticket with Omnissa on this issue, but noting here in case this happens to be related to your issue (or if Carl has any idea why that would be happening)
Hello,
I’m really struggling with our UAG/Horizon/Avi setup.
Our environment differs from the one shown in your diagram at the beginning of this write-up. We have external connections coming into our load balancer, that is then directing traffic to services. However there is only one load balancer and no DMZ. None of our connections go out to the internet so there’s no need for a DMZ.
so its external network -> AVI -> 2x UAG -> 2x Horizon connection servers.
my confusion is this: if we only have one load balancer that’s intending to point to our two connection servers, do we really even need UAG? It almost seems like an extra step for nothing. Is it possible to just configure the AVI loadbalancer to point straight to our connection servers?
UAG adds SAML since Connection Server can’t do it on its own.
UAG adds Proxy for Blast to handle NAT’d connections.
If you don’t need those features then you probably don’t need UAG.
Hello Carl,
We have 2 UAG in the DMZ (for external access) and 2 internal CS (for internal access). The connections through the UAG are tunneled (not through the connection servers) and 2FA is mandatory.
Now, some of our customers want to enable 2FA for internal access as well. We were thinking of enabling 2FA on one of the internal CS, but I wonder it can works event it’s paired to the UAG servers.
Best Regards
Hello !
We need to enable 2FA (RADIUS) on one of our 2 internal CS.
We also have 2 UAG in the DMZ and these 2 UAG are paired with our 2 internal CS. 2FA is already enabled for external access through the 2 UAG
Is it possible to enable RADIUS on the internal CS even if a UAG is paired ?
Thank you for your help
Yes. Have you tried it?
Hi Carl,
We tried, but never got it to work. Is there a special configuration ? As soon as 2FA is activated on the CS, connections via UAG no longer work.
Hi Carl,
By any chance, do you have any ideas?
Thank you very much
Hello Carl,
I’ve been following for years, this is my first comment. So, I upgraded my UAGs to 2406 and am now getting an “Internal Server Error” after selecting the desktop pool . The solution works fine when I power up the older 2303 UAGs. We are using a netscaler and single sign on which it seem to get through just fine. Any ideas?
Doug
Using HTML5 instead of full Horizon Client? Have you edited the locked.properties file on the Connection Server? https://www.carlstalhood.com/vmware-horizon-8-configuration/#horizonconsoles
Hey Carl, I have a question about UAG 2111.2
Can I just turn off TLS 1.0 and 1.1 live on the UAG? Will that cause any issues or disruptions?
Thanks
If nobody’s using those protocols then I assume it won’t cause any disconnects. But I would do it during a change window.
Hi Carl,
Man! been following you for many years and thank you for all your help!
I have question concerning AWS setup for UAG.
we have the UAG setup in GCP working by following your instructions without any problems. but on AWS, we are having some problems.
all seems to be well but when I try to access the published app via UAG, I get “internal Server error” I have created security groups for UAG server to have port 8443 and 443 open both TCP and UDP. The UAG is in pub and workspace is in priv and also the horizon server is also in priv. any suggestion? Lost to where to look
Hi,
in HA configuration can we decide which UAG will be the primary and which will be the backup?
we want the UAG in DR site to be the backup UAG