Navigation
- GSLB Planning
- GSLB Infrastructure – one time setup
- GSLB Configuration – Repeatable Steps
💡 = Recently Updated
GSLB Planning
GSLB is nothing more than DNS. GSLB is not in the data path. GSLB receives a DNS query, and GSLB sends back an IP address, which is exactly how a DNS server works. The user then connects to the returned IP, which doesn’t even need to be on a NetScaler.
GSLB can do some things that DNS servers can’t do:
- Don’t give out an IP address unless it is UP (monitoring)
- If the active IP address is down, then give out the passive IP address (active/passive)
- Give out the IP address that is closest to the user (proximity load balancing)
- Give out different IPs for internal users vs external users (DNS View)
GSLB is only useful if you have a single DNS name that could resolve to two or more IP addresses. If there’s only one IP address, then use normal DNS instead.
Citrix Blog Post Global Server Load Balancing: Part 1 explains how DNS queries work and how GSLB fits in.
Citrix has a good DNS and GSLB Primer.
When configuring GSLB, don’t forget to ask “where is the data?”. For XenApp/XenDesktop, DFS multi-master replication of user profiles is not supported, so configure “home” sites for users. More information at Citrix Blog Post XenDesktop, GSLB & DR – Everything you think you know is probably wrong!
GSLB Configuration Overview
GSLB Configuration can be split between one-time steps for GSLB infrastructure, and repeatable steps for each GSLB-enabled DNS name.
One-time GSLB Infrastructure configuration
- Create ADNS listener on each NetScaler pair – DNS clients send DNS queries to the ADNS listeners. GSLB resolves a DNS query into an IP address, and returns the IP address in the DNS response.
- Create GSLB Sites (aka MEP Listener) – GSLB Sites usually correspond to different datacenters. GSLB Sites are also the IP address endpoints for NetScaler’s proprietary Metric Exchange Protocol (MEP), which is used by GSLB to transmit proximity, persistence, and monitoring information.
- Import Static Proximity Database – NetScaler includes a database that can be used to determine the geographical location of an IP address. Or you can subscribe to a geolocation service, and import its database.
- Delegate DNS sub-zone to NetScaler ADNS – in the original DNS zone, create a new sub-zone (e.g. gslb.company.com), and delegate the sub-zone to all ADNS listeners.
Repeatable GSLB Configuration for each DNS name:
- Create one or more GSLB Services per DNS name, and per IP address response – each GSLB Service corresponds to a single IP address that can be returned in response to a DNS Query.
- Optionally, bind a Monitor to each GSLB Service. Monitors determine if the GSLB Service is up or not.
- Create a GSLB Virtual Server per DNS name
- Bind a DNS name to the GSLB Virtual Server.
- For active/active – bind multiple GSLB Services to the GSLB Virtual Server, configure a load balancing method (e.g. proximity), and configure site persistence.
- For active/passive – bind the active GSLB Service. Create another GSLB Virtual Server with passive GSLB Service, and configure as Backup Virtual Server.
- Create CNAME records for each delegated DNS name – in the main DNS zone, create a CNAME that maps the original DNS name to the delegated sub-zone. For example, CNAME citrix.company.com to citrix.gslb.company.com.
You will create separate GSLB Services, separate GSLB Virtual Servers, and separate CNAMEs for each DNS name. If you have a bunch of DNS names that you want to GSLB-enable, then you’ll repeat these steps for each GSLB-enabled DNS name.
Each datacenter has a separate ADNS listener IP address. DNS is delegated to all GSLB ADNS Listener IPs, and any one of them can respond to the DNS query. Thus, all NetScaler pairs participating in GSLB should have the same Per-DNS name configuration.
One NetScaler appliance for both public DNS/GSLB and internal DNS/GSLB?
GSLB can be enabled both publically and internally. For public GSLB, configure it on DMZ NetScaler appliances, and expose the DNS listener to the Internet. For internal GSLB, configure it on separate internal NetScaler appliances/instances, and create an internal DNS listener.
Each NetScaler appliance only has one DNS table, so if you try to use the same NetScaler for both public DNS and internal DNS, then be aware that external users can query for internal GSLB-enabled DNS names. As described by Phil Bossman in the comments, you can use a Responder policy to prevent external users from reading internal DNS names.
add policy patset GSLB_INTERNAL bind policy patset GSLB_INTERNAL internalHostname.gslb.domain.com -index 1 add responder action DNS_Empty_Response respondwith DNS.NEW_RESPONSE add responder policy GSLB_DNS_Empty_Response "(!(CLIENT.IP.SRC.IN_SUBNET(10.0.0.0/8)||CLIENT.IP.SRC.IN_SUBNET(192.0.0.0/16)||CLIENT.IP.SRC.IN_SUBNET(172.0.0.0/12)) && DNS.REQ.QUESTION.DOMAIN.CONTAINS_ANY(\"GSLB_INTERNAL\"))" DNS_Empty_Response bind responder global GSLB_DNS_Empty_Response 100 END -type DNS_REQ_DEFAULT
One appliance resolving a single DNS name differently for internal and public
Let’s say you have a single DNS name citrix.company.com. When somebody external resolves the name, it should resolve to a public IP. When somebody internal resolves the name, it should resolve to an internal IP.
For internal GSLB and external GSLB of the same DNS name on the same NetScaler appliance, you can use DNS Policies and DNS Views to return different IP addresses depending on where users are connecting from. See Citrix CTX130163 How to Configure a GSLB Setup for Internal and External Users Using the Same Host Name.
If the Internet circuit in the remote datacenter goes down, then this should affect public DNS, since you don’t want to give out a public IP that isn’t reachable. But do you also want an Internet outage to affect internal DNS? Probably not. In that case, you would need different GSLB monitoring configurations for internal DNS and external DNS. However, if you have only a single GSLB Virtual Server with DNS Views, then you can’t configure different monitoring configurations for each DNS View.
To work around this limitation, create two separate GSLB Virtual Servers with different monitoring configurations. Internal DNS uses a CNAME record to reach the GSLB Virtual Server configured for internal monitoring:
- External citrix.company.com:
- Configure NetScaler GSLB for citrix.company.com.
- On public DNS, delegate citrix.company.com to the NetScaler DMZ ADNS services.
- Internal citrix.company.com:
- Configure NetScaler GSLB for citrixinternal.company.com or something like that.
- On internal DNS, create CNAME for citrix.company.com to citrixinternal.company.com
- On internal DNS, delegate citrixinternal.company.com to NetScaler internal ADNS services.
Remote Internet Monitoring
For public DNS/GSLB, you don’t want to give out a remote public IP address if that remote public IP address is not reachable. That means the local NetScaler will need to somehow determine if the remote datacenter has Internet connectivity or not. Here are some methods of verifying the remote Internet connection:
- Route GSLB Metric Exchange Protocol (MEP) across the Internet. If MEP goes down, then all IP addresses associated with the remote GSLB Site are assumed to be down, and thus the local NetScaler will stop giving out those remote IP addresses.
- Bind explicit monitors to each GSLB Service, and ensure the monitoring is routed across the Internet.
GSLB IP Addresses
GSLB is separate from data traffic. The GSLB IP addresses are separate from the IP addresses needed for data.
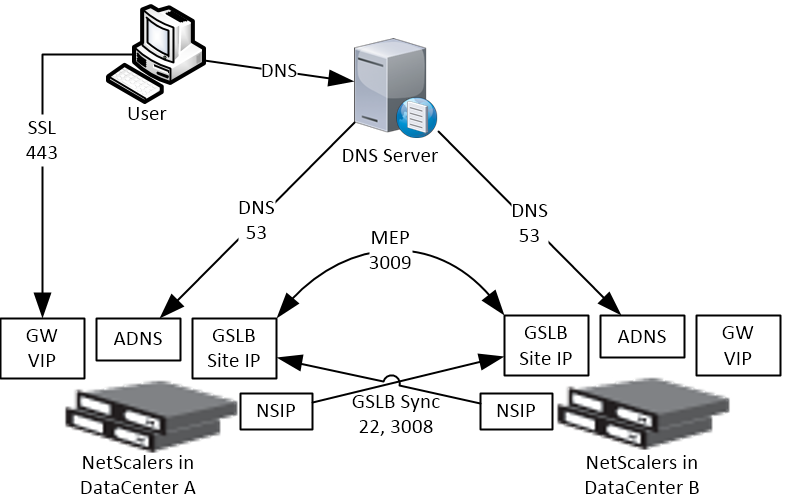
Some GSLB-specific IP Addresses are needed on each NetScaler pair:
- ADNS Listener IP: A NetScaler IP that listens for DNS queries.
- The ADNS listener IP is typically an existing SNIP on the appliance.
- For external DNS, create a public IP for the ADNS Listener IP, and open UDP 53, so Internet-based DNS servers can access it.
- A single NetScaler appliance can have multiple ADNS listeners – typically one ADNS listener for public, and another ADNS listener for internal.
- GSLB Site IP / MEP listener IP: A NetScaler IP that will be used for NetScaler-to-NetScaler GSLB communication. This communication is called MEP or Metric Exchange Protocol. MEP transmits the following between GSLB-enabled NetScaler pairs: load balancing metrics, proximity, persistence, and monitoring.
- GSLB Sites – On NetScaler, you create GSLB Sites. GSLB Sites are the endpoints for the MEP communication. Each NetScaler pair is configured with the MEP endpoints for the local appliance pair, and all remote appliance pairs.
- TCP Ports – MEP uses port TCP 3009 or TCP 3011 between the NetScaler pairs. TCP 3009 is encrypted.
- The ADNS IP address can be used as the MEP endpoint IP.
- MEP endpoint can be any IP – The MEP endpoint IP address can be any IP address and does not need to be a SNIP or ADNS.
- One MEP IP per appliance – there can only be one MEP endpoint IP address on each NetScaler pair.
- Route MEP across Internet? – If you route MEP across the Internet, and if the MEP connection is interrupted, then Internet at one of the locations is probably not working. This is an easy way to determine if remote Internet is up or not. If you don’t route MEP across the Internet, then you’ll need to configure every remote-site GSLB Service with a monitor to ensure that the remote Internet is up.
- Public IPs for MEP Enpoints – if you route MEP across the Internet, then you’ll need public IPs for each publically-accessible MEP endpoint IP address.
- Public Port for MEP: Open port TCP 3009 between the MEP Public IPs. Make sure only the MEP IPs can access this port on the other NetScaler. Do not allow any other device on the Internet to access this port. Port 3009 is encrypted.
- GSLB Sync Ports: To use GSLB Configuration Sync, open ports TCP 22 and TCP 3008 (secure) from the NSIP (management IP) to the remote public MEP IP. The GSLB Sync command runs a script in BSD shell and thus NSIP is always the Source IP.
- Public IP Summary: In summary, for public GSLB, if MEP and ADNS are listening on the same IP, then you need one new public IP that is NAT’d to the DMZ IP that is used for ADNS and MEP (GSLB Site IP).
- Each datacenter has a separate public IP.
- DNS is delegated to all public ADNS IP listeners.
ADNS Listener
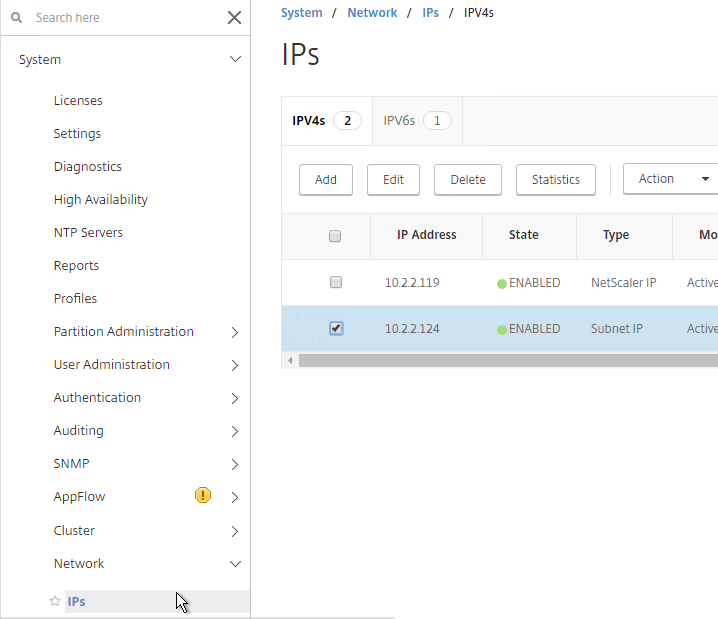
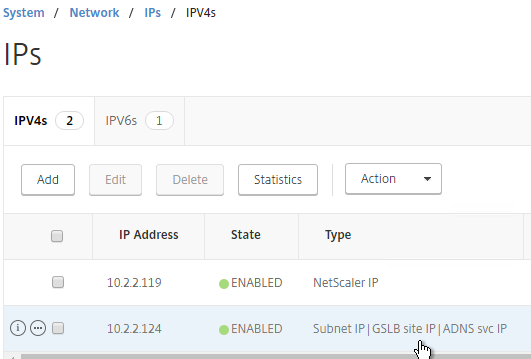
- At System > Network > IPs, identify a NetScaler-owned IP that you will use as the ADNS listener. This is typically a SNIP.
- Create a public IP for the ADNS Service IP, and configure firewall rules.
- On the left, expand Traffic Management > Load Balancing, and click Services.
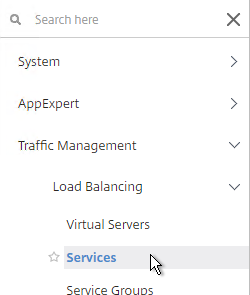
- On the right, click Add.
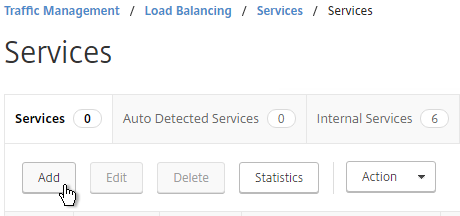
- In the Basic Settings section, do the following:
- Name the service ADNS or similar.
- In the IP Address field, enter an appliance SNIP.
- In the Protocol drop-down field, select ADNS.
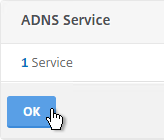
- Click OK.
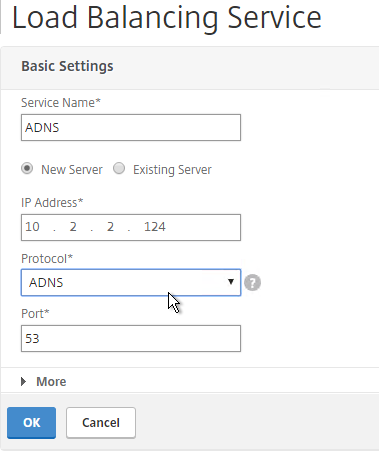
- Scroll down and click Done, to close the Load Balancing Service properties.
- On the left of the console, expand System, expand Network, and then click IPs.
- On the right, you’ll see the SNIP is now marked as the ADNS svc IP.
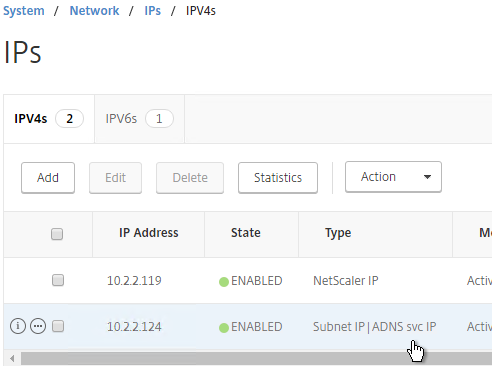
- Repeat ADNS configuration on the other appliance pair in the other datacenter.
- Your NetScaler appliances are now DNS servers.
DNS Security
- NetScaler 11.1 build 51 and newer includes DNS Security Options at Security > DNS Security, which can protect your ADNS service.

- To protect ADNS, set the Profile to All DNS Endpoints.

Metric Exchange Protocol
This section details MEP configuration between two GSLB Sites. See Citrix Docs for larger Parent-Child Topology Deployment using the MEP Protocol, including new features in NetScaler 11.1 build 51 and newer.
GSLB Sites
- The local GSLB Site IP can be any IP. Or you can use the same SNIP, and same public IP, used for ADNS.
- Open the firewall rules for Metric Exchange Protocol.
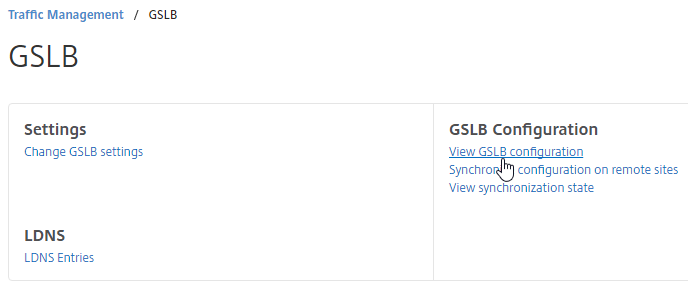
- On the left, expand Traffic Management, right-click GSLB, and enable the feature.
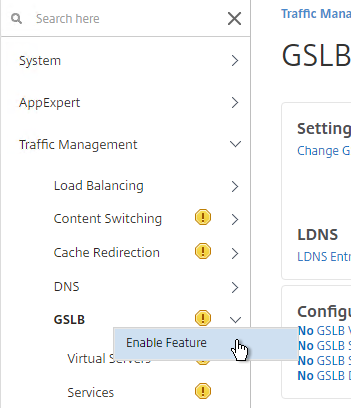
- Expand GSLB, and click Sites.
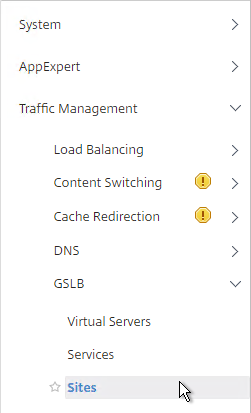
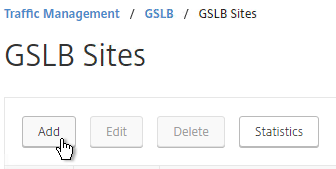
- On the right, click Add.
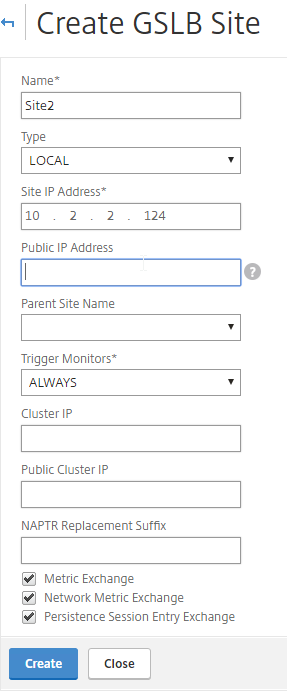
- In the Create GSLB Site page, do the following:
- We’re adding the local site first. Enter a descriptive name for the local site.
- In the Site Type drop-down, select LOCAL.
- In the Site IP Address field, enter an IP that this appliance will listen for MEP traffic. This is typically a DMZ SNIP.
- For Internet-routed GSLB MEP, in the Public IP Address field, enter the public IP that is NAT’d to the GSLB Site IP.
- For internal GSLB MEP, there is no need to enter anything in the Public IP field.
- Scroll down, and click Create, to close the Create GSLB Site page.
- Go back to System > Network > IPs, and verify that the IP is now marked as a GSLB site IP.
- If you want to use the GSLB Sync Config feature, then you’ll need to edit the GSLB site IP, and enable Management Access.
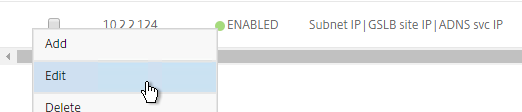
- Scroll down, and enable Management Access. SSH is all you need.
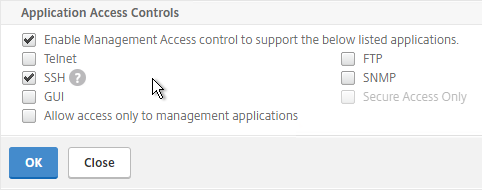
- Scroll down, and enable Management Access. SSH is all you need.
- Go to the other appliance pair,and also create the Local GSLB site using its GSLB site IP, and its public IP that is NAT’d to the GSLB site IP.
- In System > Network > IPs on the remote appliance, there should now be a GSLB site IP. This could be a SNIP. If GSLB Sync is desired, enable management access on that IP and ensure SSH is enabled.
- Now on each appliance add another GSLB Site, which will be the Remote GSLB site.
- In the Create GSLB Site page, do the following:
- Enter a descriptive name for the remote site.
- Select REMOTE as the Site Type.
- Enter the other appliance’s actual GSLB Site IP as configured on the appliance. This IP does not need to be reachable.
- In the Public IP Address field, enter the public IP that is NAT’d to the GSLB Site IP on the other appliance. For MEP, TCP 3009 must be open from the local GSLB Site IP, to the remote public Site IP. For GSLB sync, TCP 22, and TCP 3008, must be open from the local NSIP, to the remote public Site IP.
- Click Create.
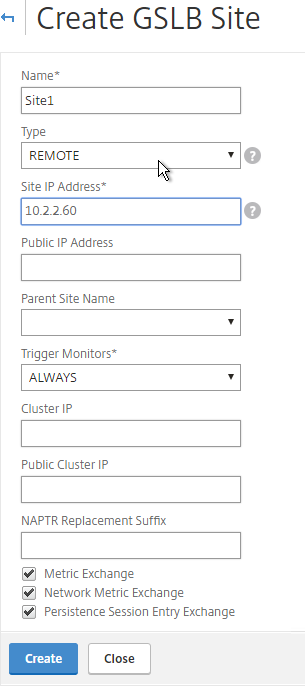
- Repeat on the other appliance.
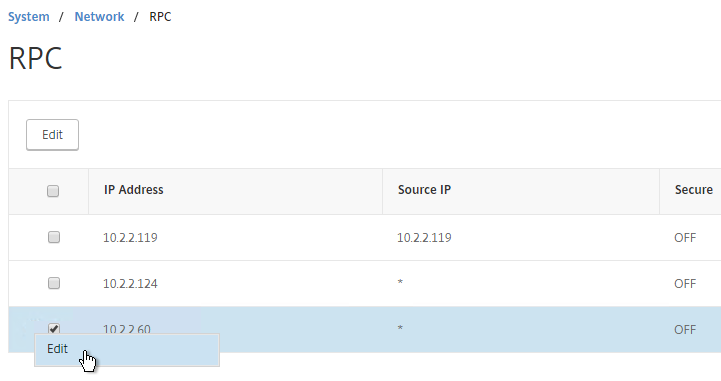
RPC
MEP defaults to unencrypted on TCP 3011. To fix that:
- On the left, expand System, expand Network, and click RPC.
- On the right, right-click the new RPC address (the other site’s GSLB Site IP), and click Edit.
- On the bottom, check the box next to Secure.
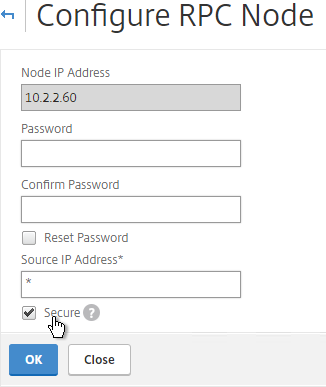
- If your local GSLB Site IP is not a SNIP, then you’ll need to change the RPC Node to use the local GSLB Site IP as the source IP. In the Source IP Address field, enter the local GSLB Site IP.
- Click OK when done.
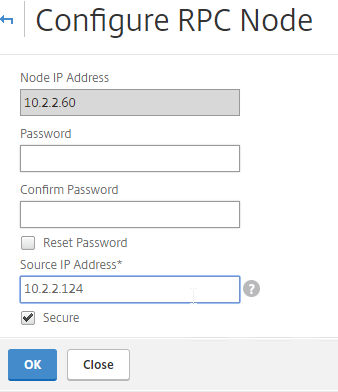
- Do the same thing on the other appliance.
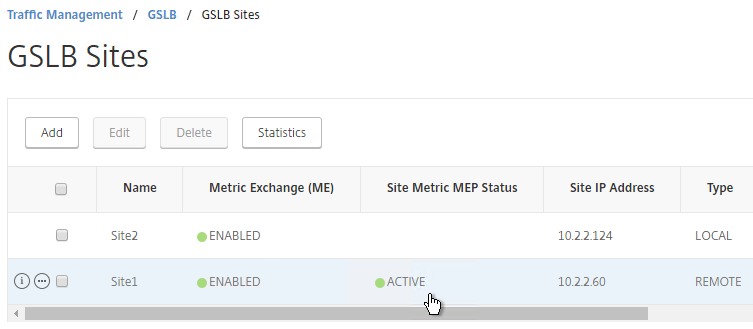
- If you go back to GSLB > Sites, you should see it as active.
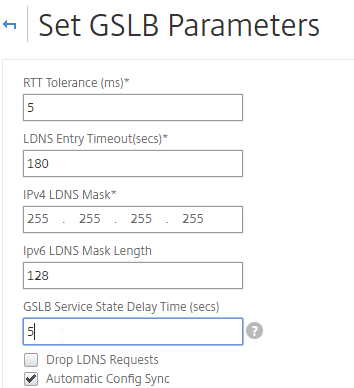
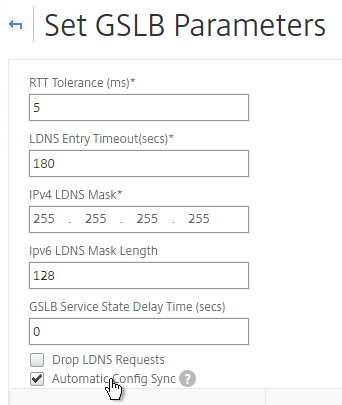
If your MEP connection between GSLB Sites flaps, it might be useful to introduce a delay before remote GSLB Services are marked as Down. In NetScaler 11.1 build 51 and newer:
- you can do this at Traffic Management > GSLB, on the right, in the left column, click Change GSLB settings.
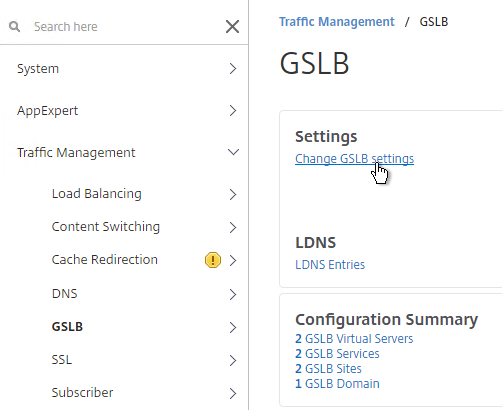
- In the GSLB Service State Delay Time (secs) field, enter a delay before the GSLB Services are marked as down when MEP goes down.
set gslb parameter -GSLBSvcStateDelayTime 15
Static Proximity Geo Location Database
If you want to use DNS Policies or Static Proximity GSLB Load Balancing or Responders based on user’s location, import a geo location database.
NetScaler has a built-in database at /var/netscaler/inbuilt_db/ that you can use. Or you can download a database. Common free databases are:
- GeoLite Legacy – http://dev.maxmind.com/geoip/legacy/geolite/
- IP2Location Lite – http://lite.ip2location.com/
For IP2Location, see the blog post Add IP2Location Database as NetScaler’s Location File for instructions on how to import.
Import Built-in Geo database
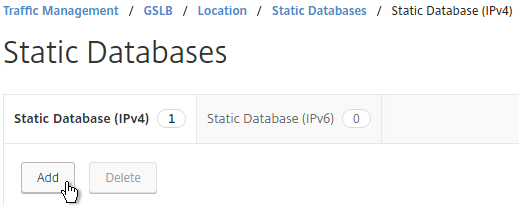
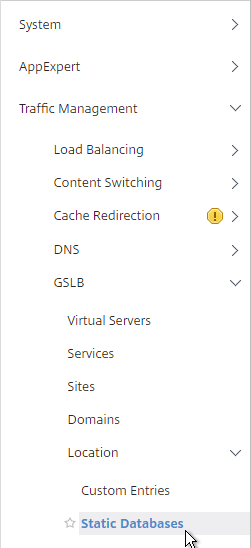
- In the NetScaler GUI, on the left, expand Traffic Management, expand GSLB, expand Location, and click Static Databases.
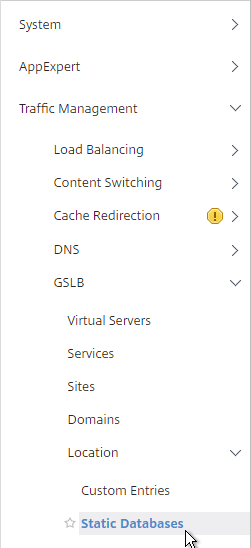
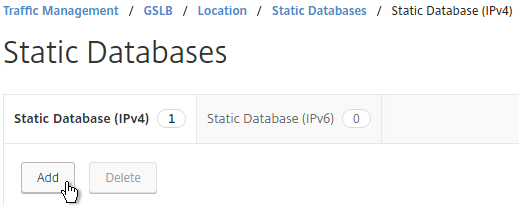
- On the right, click Add.
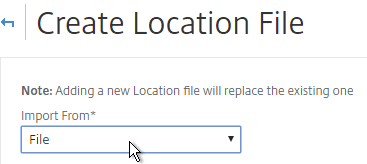
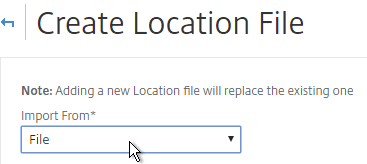
- Change the Import From selection to File.
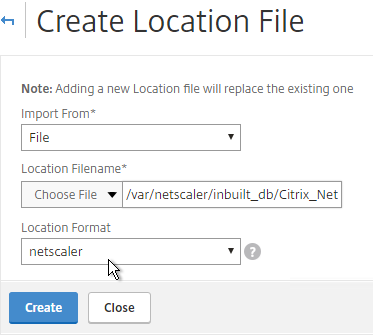
- Click Choose File.
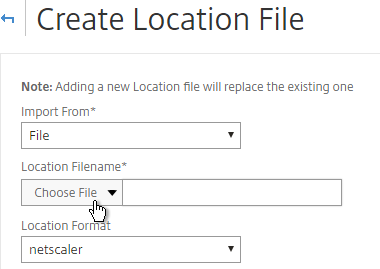
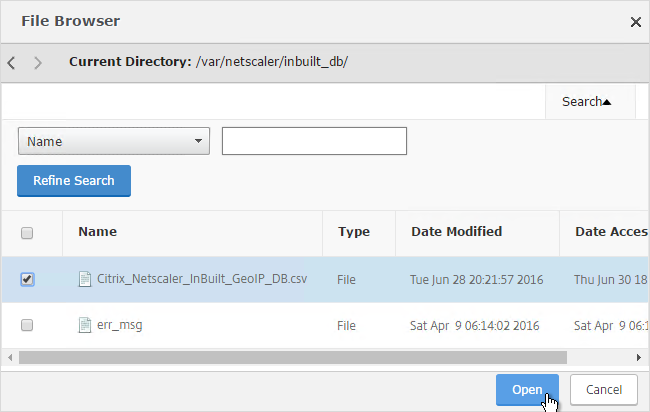
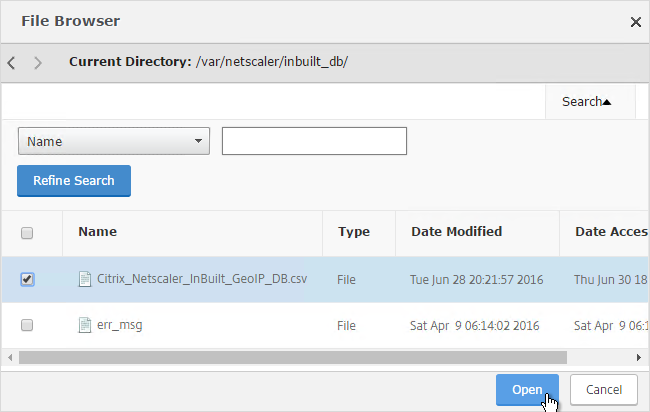
- Browse to /var/netscaler/inbuilt_db/, and open Citrix_NetScaler_InBuilt_GeoIP_DB.csv. To browse to the directory, select var, and then click Open. Repeat for each directory until you reach /var/netscaler/inbuilt_db.
- In the Location Format field, if using the built-in database, select netscaler, and click Create.
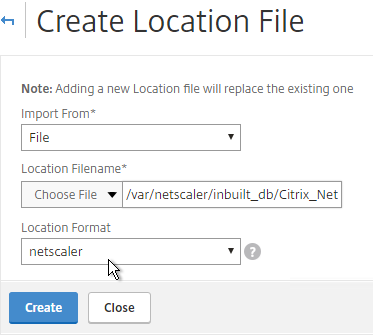
- When you open a GSLB Service, the public IP will be translated to a location.

Private IP Blocks
Geo Location databases only contain entries for Public IPs. For Private IPs, do the following:
- On the left, expand Traffic Management, expand GSLB, expand Location, and click Custom Entries.
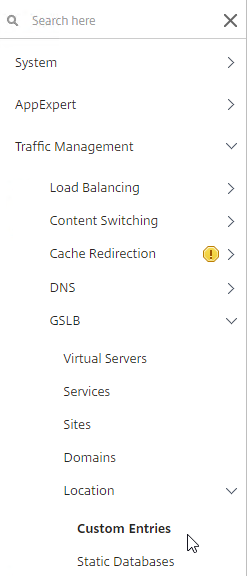
- On the right, click Add.

- Enter a range of IP addresses for a particular location.
- Enter a Location Name in Geo Location format, which is typically six location words separated by periods. You can look in the static proximity database for examples.
- Click Create.

- Continue creating Custom Entries for other private IP blocks.

Use Geo Locations
You can use the Geo locations in a DNS Policy, static proximity GSLB Load Balancing, or Responders:
- Citrix Knowledgebase article CTX130701 – How to Block Access to a Website Using a Location Database Based on User’s Country
- Neil Spellings blog post – Using Netscaler HTTP callouts for real-time GeoIP and anonymous proxy detection
- Citrix Docs – Overriding Static Proximity Behavior by Configuring Preferred Locations
GSLB Services
GSLB Services represent the IP addresses that are returned in DNS Responses. The IP addresses represented by GSLB Services do not need to be on a NetScaler, but NetScaler-owned IP addresses (e.g. load balancing VIPs) have additional GSLB Site Persistence options (e.g. cookie-based persistence).
- Each potential IP address in a DNS response is a separate GSLB Service.
- GSLB Services are associated with GSLB Sites.
- GSLB Service configuration is identical for active/active and active/passive. GSLB Virtual Server define active/active or active/passive, not GSLB Services.
GSLB should be configured identically on all NetScaler pairs that are responding to DNS queries. Since you have no control over which NetScaler will receive the DNS query, you must ensure that both NetScaler pairs are giving out the same DNS responses.
To create a GSLB Service:
- On the left, expand Traffic Management > GSLB, and click Services.
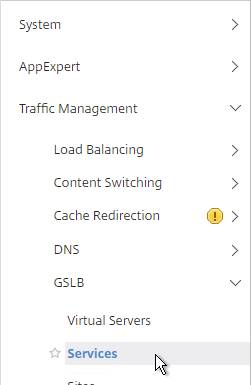
- On the right, click Add.
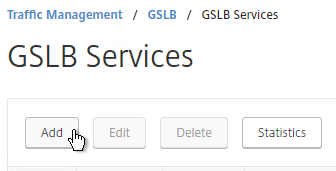
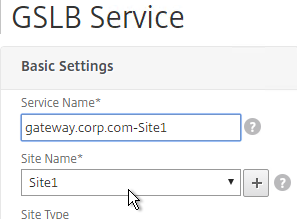
- The service name should be similar to the DNS name that you are trying to GSLB. Include the site name in the service name.
- Select one of the GSLB Sites. The IP address you’re configuring in this GSLB Service should be geographically located in the selected GSLB Site.
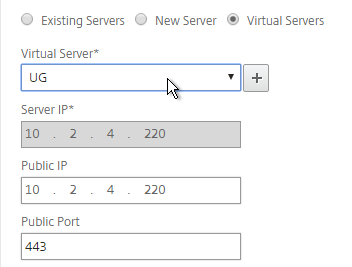
- On the bottom part, if the IP address is owned by this NetScaler (Local Site), then select Virtual Servers, and select a Virtual Server that is already defined on this appliance. It should automatically fill in the other fields. If you see a message asking if you wish to create a service object, click Yes. This option is only available when creating a GSLB Service in the Local GSLB Site.
-
- If the IP address is not owned by this NetScaler, then change the selection to New Server, and enter the remote IP address in the Server IP field.
- The Server IP field is the IP address that NetScaler will monitor for reachability.
- If the remote IP is owned by a different NetScaler that is reachable by MEP, then enter the actual VIP configured on that remote NetScaler. The Server IP does not need to match what is returned to the DNS Query.

-
- In the Public IP field, enter the IP address that will be returned to the DNS Query. If you leave Public IP blank, then NetScaler will copy the Server IP to the Public IP field. For Public GSLB, the Public IP field is usually a Public IP address. For internal GSLB, the Public IP field is usually an internal IP, and probably matches the Server IP.

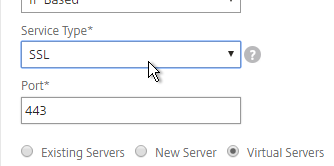
- Scroll up and make sure the Service Type is SSL. It’s annoying that NetScaler doesn’t set this drop-down correctly.
- Scroll down and click OK to close the Basic Settings section.
- GSLB Service Monitoring – on the right, in the Advanced Settings column, you can click Monitors to bind a monitor to this GSLB Service. Review the following notes before you bind a monitor.

- Local NetScaler VIP – If the GSLB Service IP is a VIP on the local appliance, then GSLB will simply use the state of the local traffic Virtual Server (Load Balancing, Content Switching, or Gateway). There’s no need to bind a monitor to the GSLB Service.
- Remote NetScaler VIP – If the GSLB Service IP is a VIP on a remote appliance, then GSLB will use MEP to ask the other appliance for the state of the remote traffic Virtual Server. In both cases. There’s no need to bind a monitor to the GSLB Service.
- GSLB Monitor overrides other Monitoring methods – If you bind a monitor to the GSLB Service, then MEP and local Virtual Server state are ignored (overridden).
- Here are some reasons for binding a monitor to the GSLB Service:
- IP is not on a NetScaler – If the GSLB Service IP is not hosted on a NetScaler, then only GSLB Service monitors can determine if the Service IP is up or not.
- Monitor remote Internet – For Public DNS, if MEP is not routed through the Internet, then you need some method of determining if the remote Internet circuit is up or not. In that case, you’ll need to bind monitors directly to the GSLB Service. The route of the Monitor should go across the Internet. Or you can ping the Internet router in the remote datacenter to make sure it’s reachable.
- Traffic Domains – If the GSLB Service IP is in a non-default Traffic Domain, then you will need to attach a monitor, since GSLB cannot determine the state of Virtual Servers in non-default Traffic Domains.
- Active/Active Site Persistence – If you intend to do GSLB active/active, and if you need site persistence, then you can configure your GSLB Services to use Connection Proxy or HTTP Redirect. See Citrix Blog Post Troubleshooting GSLB Persistence with Fiddler for more details. This only works with GSLB Service IPs that match Virtual Server VIPs on NetScaler appliances reachable through MEP.

- Scroll down, and click Done, to finish creating the GSLB Service.
- Create additional GSLB Services for each IP address that will be returned to a DNS query.

Manually Synchronize GSLB Configuration
Copy the GSLB Service Configuration to the remote NetScaler pair. You can either repeat the GUI steps listed above. Or you can do the following:
- On the left, expand Traffic Management, and click GSLB.
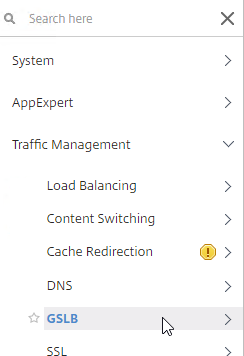
- On the right, click View GSLB Configuration.
- This shows you all of the CLI commands for GSLB. Look for add gslb service commands. You can copy them, and run them (SSH) on other NetScaler pairs that are participating in GSLB.

GSLB Virtual Server
The GSLB Virtual Server is the entity that the DNS name is bound to. GSLB Virtual Server then gives out the IP address of one of the GSLB Services that is bound to it.
For Active/Passive GSLB:
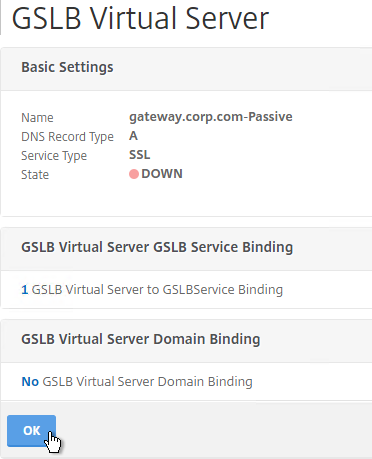
- Create a GSLB Virtual Server for the Passive IP address.
- Bind the Passive GSLB Service to the Passive GSLB Virtual Server.
- Create another GSLB Virtual Server for the Active IP address.
- Bind the Active GSLB Service to the Active GSLB Virtual Server.
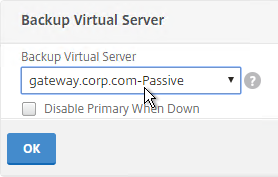
- Configure Backup Virtual Server pointing to the Passive GSLB Virtual Server.
- Bind a DNS name to the Active GSLB Virtual Server.
- Repeat the GSLB Virtual Server configuration on other NetScaler pairs participating in GSLB.
- Delegate the DNS name to NetScaler ADNS.
For Active/Active GSLB:
- Create one GSLB Virtual Server.
- Bind two or more GSLB Services to the Virtual Server.
- Configure the GSLB Virtual Server Load Balancing Method – e.g. Proximity
- Configure Site Persistence:
- Source IP persistence is configured on the GSLB Virtual Server.
- Cookie Persistence is configured on the GSLB Services.
- Bind a DNS name to the GSLB Virtual Server.
- Repeat the GSLB Virtual Server configuration on other NetScaler pairs participating in GSLB.
- Delegate the DNS name to NetScaler ADNS.
Configure the GSLB vServer identically on both appliances:
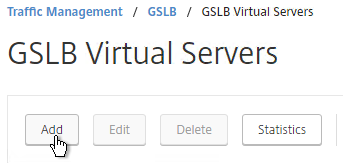
- On the left, expand Traffic Management > GLSB, and click Virtual Servers.
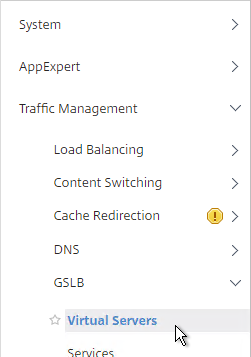
- On the right, click Add.
- Give the GSLB vServer a descriptive name. For active/active, you can name it the same as your DNS name. For active/passive, you will create two GSLB Virtual Servers, one for each datacenter, so include Active or Passive in the Virtual Server name.
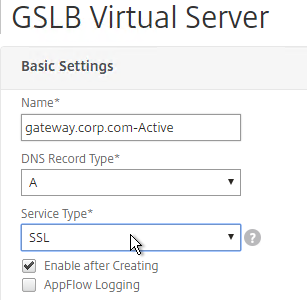
- If you intend to bind multiple GSLB Services to this GSLB vServer, then you can optionally check the box for Send all “active” service IPs. By default, GSLB only gives out one IP per DNS query. This checkbox always returns all IPs, but the IPs are ordered based on the GSLB Load Balancing Method and/or GSLB Persistence.
- If you configure GSLB to use Static Proximity Load Balancing Method, a new DNS feature called ECS will contain the actual DNS client IP. This dramatically improves the accuracy of determining a user’s location. Without this setting, GSLB can only see the IP address of the user’s configured DNS server instead of the real client IP.
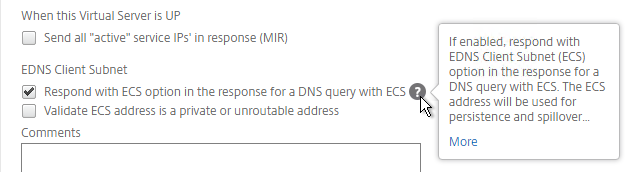
set gslb vserver <gslb_vserver> -ECS ENABLED -ecsAddrValidation ENABLED
- Click OK.
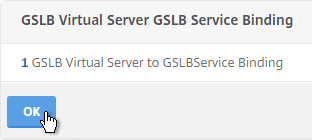
- On the left, click where it says No GSLB Virtual Server to GSLBService Binding.
- Click the arrow next to Click to select.
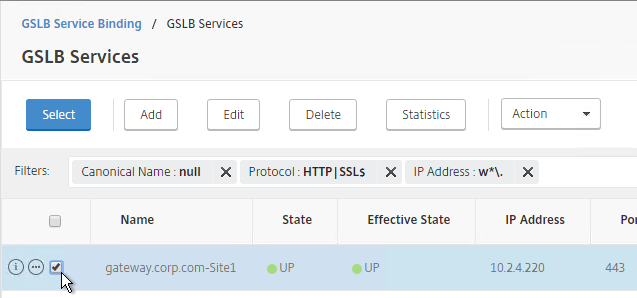
- Check the box next to an existing GSLB Service and click Select. If your GSLB is active/passive then only bind one service.
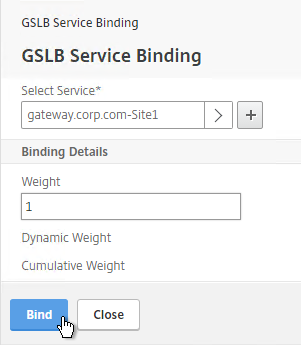
- If your GSLB is active/active then bind multiple GSLB Services. Also, you’d probably need to configure GSLB persistence (Source IP or cookies).
- Click Bind.
- Click OK.
- On the left, click where it says No GSLB Virtual Server Domain Binding.
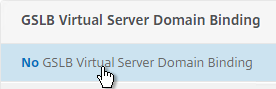
- Enter the FQDN that GSLB will resolve.
- If this GSLB is active/passive, there are two options:
- Use the Backup IP field to specify the IP address that will be handed out if the primary NetScaler is inaccessible or if the VIP on the primary appliance is marked down for any reason.
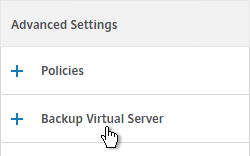
- Or, create a second GSLB Virtual Server that has the passive GSLB service bound to it. Don’t bind a Domain to the second GSLB Virtual Server. Then edit the Active GSLB Virtual Server and use the Backup Virtual Server section to select the second GSLB Virtual Server.
- Click Bind.
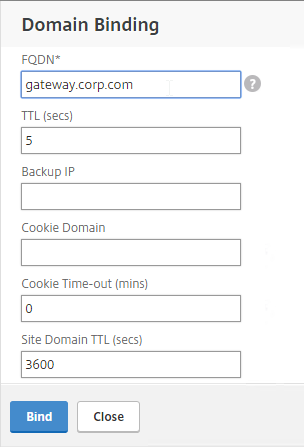
- Click OK.
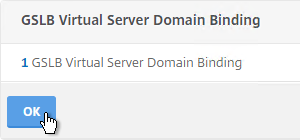
- In the ADNS Service section, click OK.
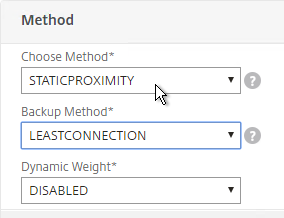
- If this is active/active GSLB, you can edit the Method section to enable Static Proximity. This assumes the Geo Location database has already been installed on the appliance.
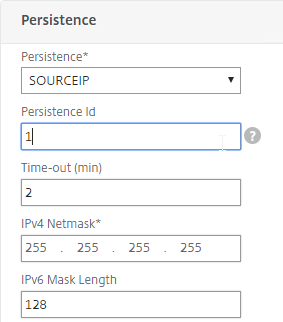
- Also for active/active, if you don’t want to use Cookie-based persistence, then you can use the Persistence section to configure Source IP persistence.
- Click Done when done.
- If you are configuring active/passive using the backup GSLB Virtual Server method, create a second GSLB Virtual Server that has the passive GSLB service bound to it. Don’t bind a Domain to the second GSLB Virtual Server.
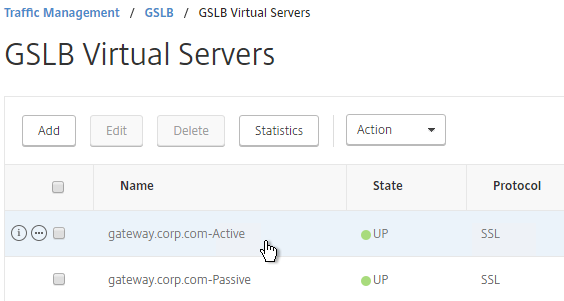
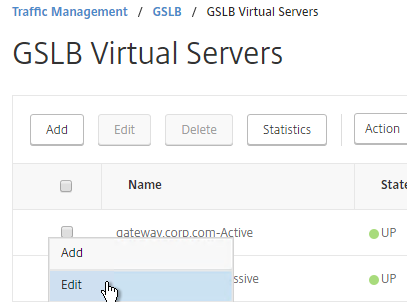
- Then edit the Active GSLB Virtual Server and use the Backup Virtual Server section to select the second GSLB Virtual Server.
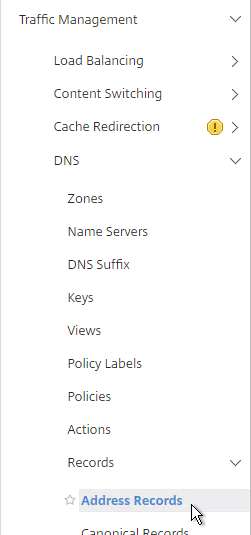
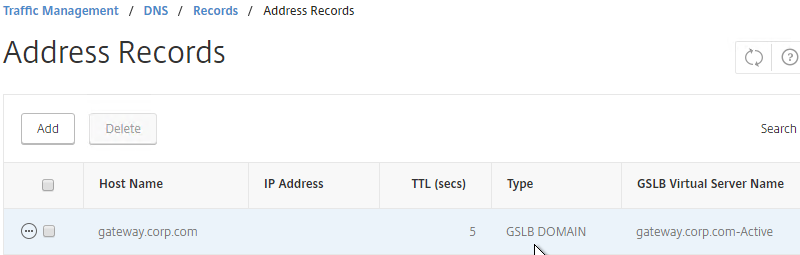
- On the left, if you expand Traffic Management > DNS, expand Records, and click Address Records, you’ll see a new DNS record for the GSLB domain you just configured. Notice it is marked as GSLB DOMAIN.
- Configure identical GSLB Virtual Servers on the other NetScaler appliance. Both NetScalers must be configured identically. You can also synchronize the GSLB configuration with the remote appliance as detailed in the next section.
GSLB Configuration Synchronization
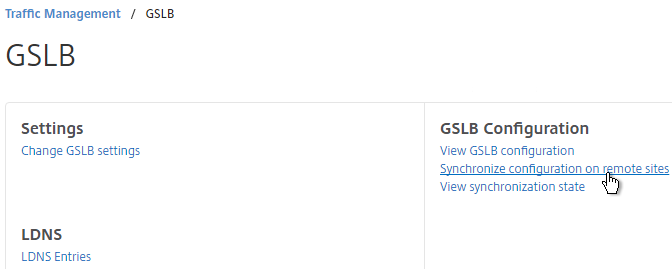
- To manually sync the GSLB configuration from one GSLB Site to another, go to Traffic Management > GSLB.
- On the right, in the right column, click Synchronize configuration on remote sites.
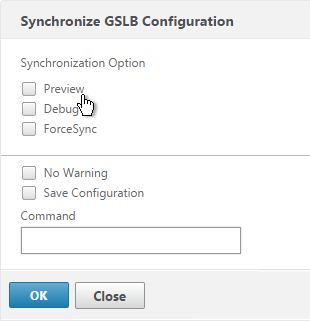
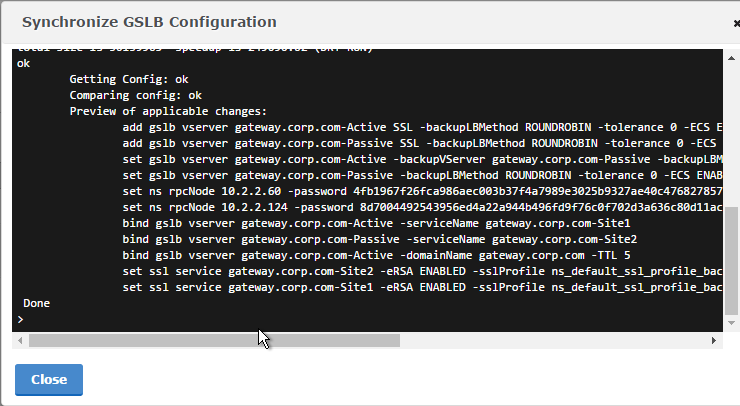
- Use the check boxes on the top, if desired. It’s usually a good idea to Preview the changes before applying them. Then click OK to begin synchronization.
- NetScaler 11.1 build 51 and newer has an automatic GSLB Configuration Sync feature, which automatically syncs the GSLB config every 15 seconds. To enable it on the master appliance, go to Traffic Management > GSLB. On the right, in the left column, click Change GSLB settings.
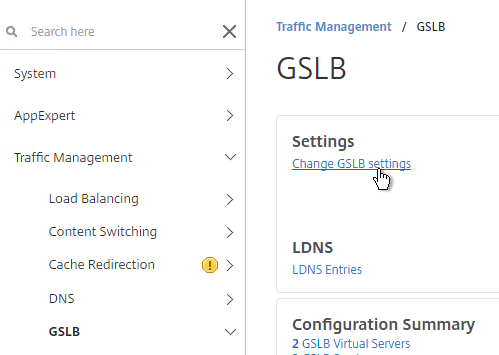
- Check the box next to Automatic Config Sync. Only enable this on the one appliance where you are configuring GSLB and want that GSLB config synced to other appliance.
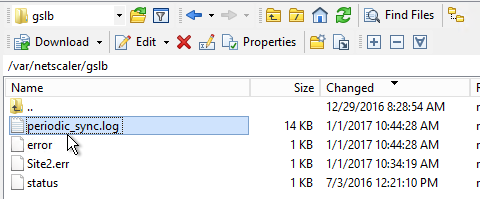
- The automatic sync log can be found at /var/netscaler/gslb/periodic_sync.log.
Some notes regarding GSLB Sync:
- When syncing GSLB Services, it tries to create LB Server objects on the remote appliance. If the GSLB Service IP matches an existing LB Server object, then the GSLB sync will fail. Check the Sync logs for details. You’ll have to delete the conflicting LB Server object before GSLB Sync works correctly.
- GSLB Sync runs as a script on the BSD shell and thus always uses the NSIP as the source IP.
- GSLB Sync connects to the remote GSLB Site IP on TCP 3008 (if RPC is Secure) and TCP 22.
Test GSLB
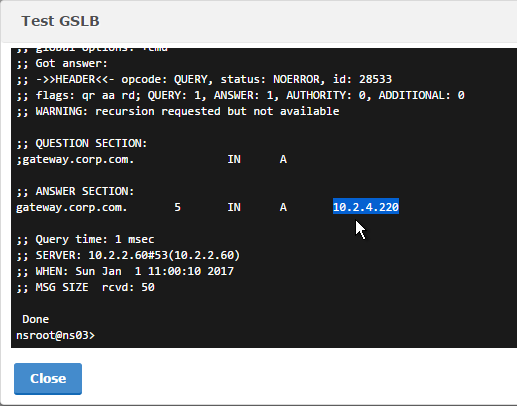
- In NetScaler 11.1 build 51 and newer, you can test GSLB DNS name resolution from the GUI by going to Traffic Management > GSLB, and on the right, in the left column, click Test GSLB.
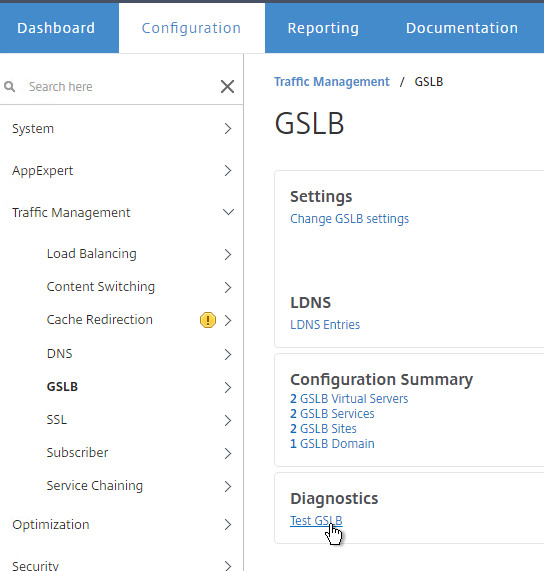
- Select a GSLB Domain Name.
- Select an ADNS Service IP, and click Test.
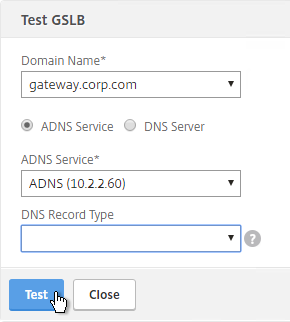
- The test performs a dig against the ADNS IP. Verify that the response contains the IP address you expected.
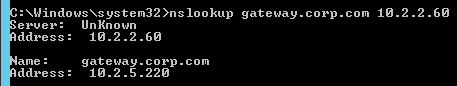
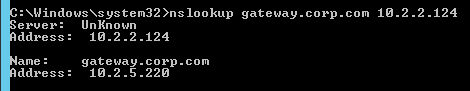
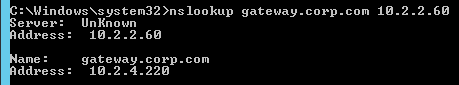
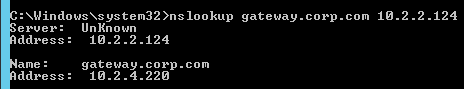
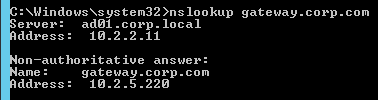
- Another method of testing GSLB is to simply point nslookup to the ADNS services, and submit a DNS query for one of the DNS names bound to a GSLB vServer. Run the query multiple times to make sure you’re getting the response you expect.
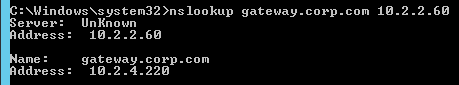
- The NetScaler ADNS services at both GSLB sites should be giving the same response.
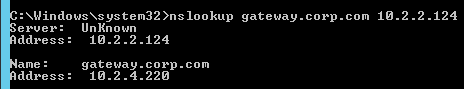
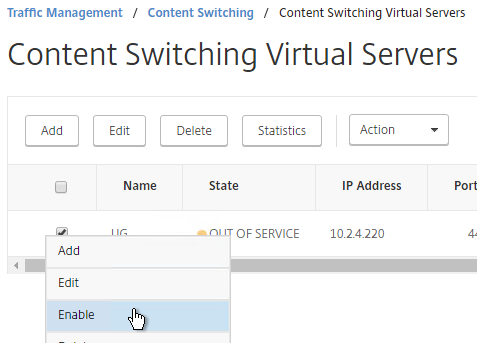
- To simulate a failure, disable the traffic Virtual Server.
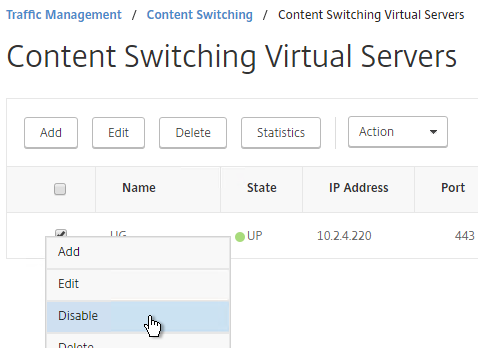
- Then the responses should change. Verify on both ADNS services.
- Re-enable the traffic Virtual Server, and the responses should return to normal.
DNS Delegation
If you are enabling GSLB for the domain gateway.corp.com, you’ll need to create a delegation at the server that is hosting the corp.com DNS zone. For public GSLB, you need to edit the public DNS zone for corp.com.
DNS Delegation instructions will vary depending on what product host’s the public DNS zone. This section details Microsoft DNS, but it should be similar in BIND or web-based DNS products.
There are two ways to delegate GSLB-enabled DNS names to NetScaler ADNS:
- Delegate the individual record. For example, delegate gateway.corp.com to the two NetScaler ADNS services (gslb1.corp.com and gslb2.corp.com).
- Delegate an entire subzone. For example, delegate the subzone gslb.corp.com to the two NetScaler ADNS services. Then create a CNAME record in the parent DNS zone for gateway.corp.com that is aliased to gateway.gslb.corp.com. When DNS queries make it to NetScaler, they will be for gateway.gslb.corp.com and thus gateway.gslb.corp.com needs to be bound to the GSLB Virtual Server instead of gateway.corp.com. For additional delegations, simply create more CNAME records.
This section covers the first method – delegating an individual DNS record:
- Run DNS Manager.
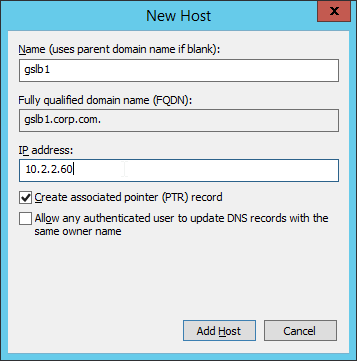
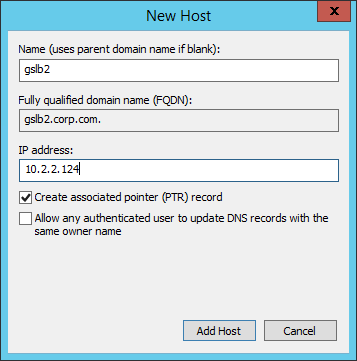
- First, create Host Records pointing to the ADNS services running on the NetScalers in each data center. These host records for ADNS are used for all GSLB delegations no matter how many GSLB delegations you need to create.
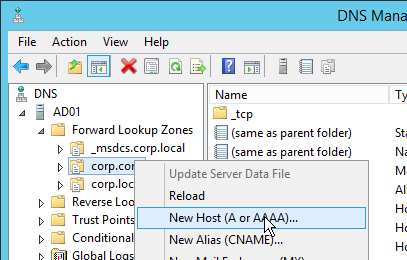
- The first Host record is gslb1 (or similar) and should point to the ADNS service (Public IP) on one of the NetScaler appliances.
- The second Host record is gslb2 and should point to the ADNS Service (public IP) on the other NetScaler appliance.
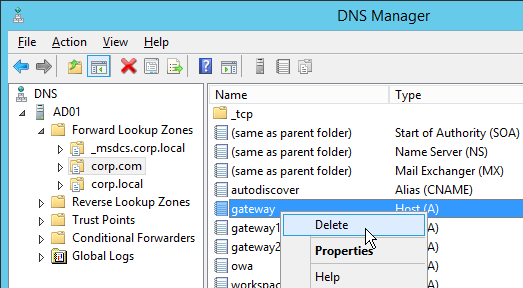
- If you currently have a host record for the service that you are delegating to GSLB (gateway.corp.com), delete it.
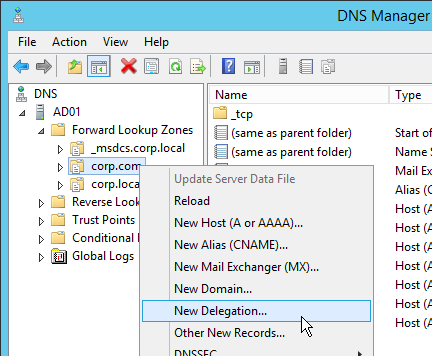
- Right-click the parent DNS zone and click New Delegation.
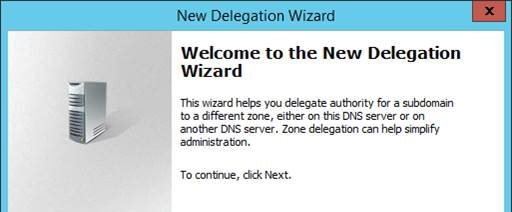
- In the Welcome to the New Delegation Wizard page, click Next.
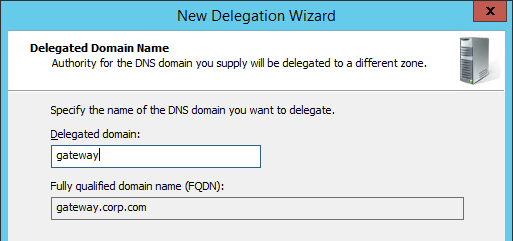
- In the Delegated Domain Name page, enter the left part of the DNS record that you are delegating (e.g. gateway). Click Next.
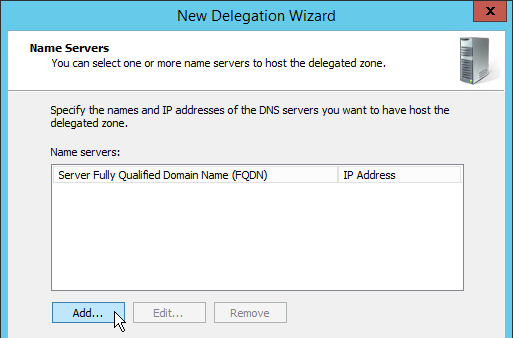
- In the Name Servers page, click Add.
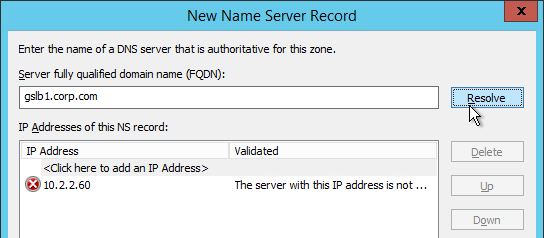
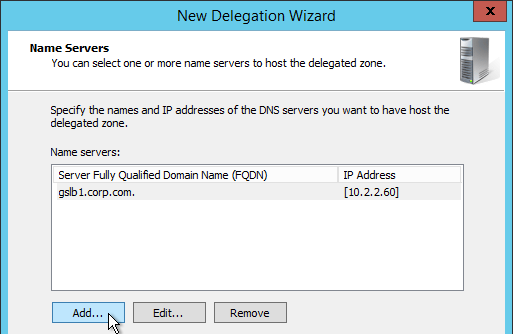
- This is where you specify gslb1.corp.com and gslb2.corp.com. Enter gslb1.corp.com and click Resolve. Then click OK. If you see a message about the server not being authoritative for the zone, ignore the message.
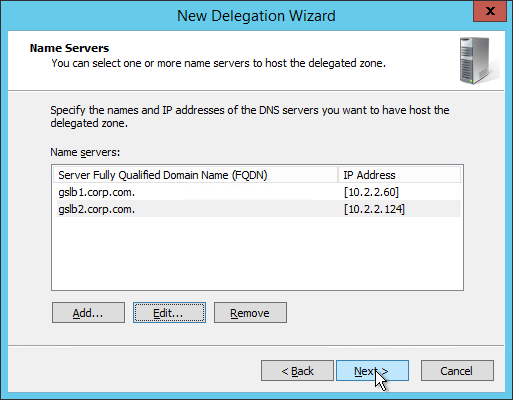
- Then click Add to add the other GSLB ADNS server.
- Once both ADNS servers are added to the list, click Next.
- In the Completing the New Delegation Wizard page, click Finish.
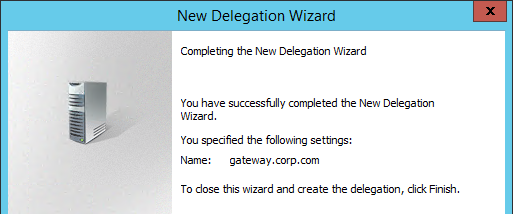
- If you run nslookup against your Microsoft DNS server, it will respond with Non-authoritative answer. That’s because it got the response from NetScaler and not from itself.
That’s all there is to it. Your NetScalers are now DNS servers. For active/passive, the NetScalers will hand out the public IP address of the primary data center. When the primary data center is not accessible, GSLB will hand out the GSLB Service IP bound to the Backup GSLB vServer.
Geo Location Database
If you want to use DNS Policies or Static Proximity GSLB Load Balancing or Responders based on user’s location, import a geo location database.
NetScaler has a built-in database at /var/netscaler/inbuilt_db/ that you can use. Or you can download a database. Common free databases are:
- GeoLite Legacy – http://dev.maxmind.com/geoip/legacy/geolite/
- IP2Location Lite – http://lite.ip2location.com/
For IP2Location, see the blog post Add IP2Location Database as NetScaler’s Location File for instructions on how to import.
To Download GeoLite Legacy:
- Download the GeoLite Country database CSV from http://dev.maxmind.com/geoip/legacy/geolite/.
- Note: GeoLite City is actually two files that must be merged as detailed at Citrix Blog Post GeoLite City as NetScaler location database. GeoLite Country doesn’t need any preparation.
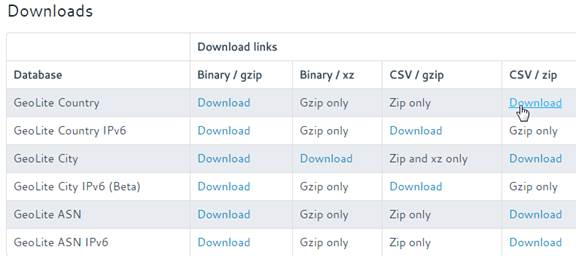
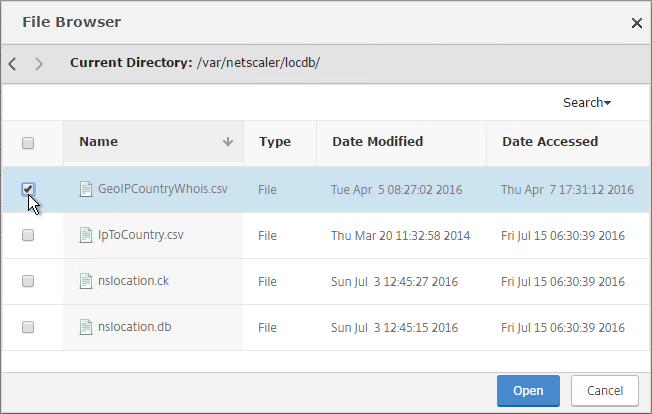
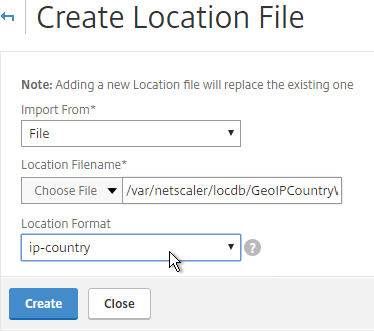
- Upload the extracted database (.csv file) to the NetScaler appliance at /var/netscaler/locdb.
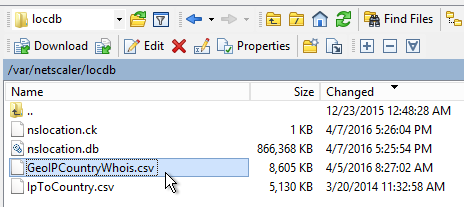
To import the Geo database (including the built-in database):
- In the NetScaler GUI, on the left, expand Traffic Management, expand GSLB, expand Location, and click Static Databases.
- On the right, click Add.
- Change the Import From selection to File.
- Click Choose File.
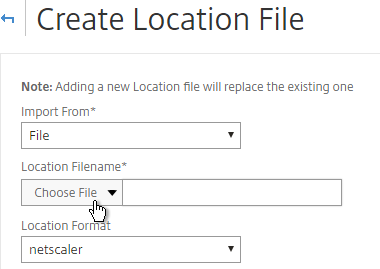
- For the built-in database, browse to /var/netscaler/inbuilt_db/ and open Citrix_NetScaler_InBuilt_GeoIP_DB.csv. To browse to the directory, select var and then click Open. Repeat for each directory until you reach /var/netscaler/inbuilt_db.
- Or browse to the Geo Location database file you uploaded and open it.
- In the Location Format field, if using the built-in database, select netscaler, and click Create.
- If using GeoLite Country, select geoip-country and click Create.
- When you open a GSLB Service, the public IP will be translated to a location.

You can use the Geo locations in a DNS Policy, static proximity GSLB Load Balancing, or Responders:
- Citrix Knowledgebase article CTX130701 – How to Block Access to a Website Using a Location Database Based on User’s Country
- Neil Spellings blog post – Using Netscaler HTTP callouts for real-time GeoIP and anonymous proxy detection
- Citrix Docs – Overriding Static Proximity Behavior by Configuring Preferred Locations
Hi Carl:
I have LLB on TD 0, SLB on TD 1
there are two ISP on my local site, meanings two different public ip for the same private VIP
and the dr site only have one ISP
now I want to add the GSLB, what should I do?
I feel confuse
thx
You can add two GSLB Services on the same GSLB Site. Then create GSLB Virtual Server to load balance the two GSLB Services.
Hi Carl
I have a situation just like this. And I’m in some trouble.
Building a GSLB site where one of my GSLB service is in TD 1.
Also got an SNIP in TD 1.
But when I try to bind a monitor to this TD 1 GSLB service, it shows DOWN.
Nstrace shows probe is sending with SNIP in TD 0 as source IP, and probe sends to default gateway..
Then I’ve tried netprofile to use SNIP in TD 1, it still sending probes to default GW.
What should I do to fix that?
Thanks!
I think that’s a limitation of GSLB and I haven’t seen any changes in recent builds. See https://support.citrix.com/article/CTX202277
Carl, I’ve been approached by my security team about our GSLB site running some weak ciphers. I’ve noticed that SSL options aren’t the same in GSLB as it is when setting up regular load balanced virtual servers and services. Is there a way to change ciphers and TLS versions that port 3009 responds with?
Go to Traffic Management > Load Balancing > Services, and there’s a tab called Internal Services.
Hi Carl,
I have a question about built-in Geo database on NetScaler VPX. We are using VPX 12.1 48.13.nc on our LAB and Production environment. We want to setup GSLB for global wide and I am thinking to use StaticProximity. Followed your instruction and there is no items under the location var/netscaler/inbuilt_db. Is there any wrong with this version of NetScaler?
Thanks,
Xiaoming
Try doing an in-place upgrade to a newer build. I’ve heard that the files are created during an upgrade but not during a new deployment.
Hey Carl, great post. I wanted to know could one use the same process for a 3rd GSLB site for dynamic proximity i.e. each datacentre will be a GSLB site providing location based routing for Citrix resources keeping the connections optimal depending on where the user is accessing resources from. Each datacentre is also a dedicated site.
Of course. You can use GSLB to load balance a DNS name across as many IPs as you want. And multiple NetScaler appliances can participate in GSLB MEP.
Hi Carl,
First time looking at a request to do GSLB for a AAA server which is used for SAML auth, it’s not bound to an LB vServer. In the GSLB services section the AAA vServer doesn’t show up in the list of vServers I can choose.
I could put the AAA server behind a CS server, would this work? Or is there a better way?
Regards,
Dan
On the bottom of the GSLB Service, you could simply enter the VIP address as a new Server. The Virtual Servers option is for monitoring. You’ll probably have to bind a monitor to the GSLB Service.
Thanks Carl, that’s what I ended up doing – just wasn’t sure if there was a better way for NetScaler owned IPs.
Carl,
I’ve got a service that I would like to put behind GSLB but I think I’m overthinking what the DNS should look like. All of my GSLB domains to-date have been specific subdomains – ie: app1.domain.com, app2.domain.com, etc. In those cases, app1 and app2 are actually CNAME records in DNS going to app1.gslb.domain.com, etc.
My next service is domain.com itself. I feel like I’m overthinking this, am I just replacing this process at a higher level? Turning domain.com into a CNAME for gslb.domain.com and delegating that as I normally do?
So you want to delegate all of domain.com to NetScaler GSLB? In that case, you go to the domain registrar and change the Name Servers hosting the domain.
Or you can create a CNAME for domain.com to point to gslb.domain.com.
Hi Carl, for public GSLB do I am using the GSLB Site and ADNS IP to be the same. So from System / Network / IPs – i see the type set as GSLB site IP | ADNS svc IP. My question is do i need to also set IP as a SNIP type for it to work on the outside?
In newer versions of NetScaler, GSLB site IP definitely doesn’t need to be a SNIP. But I’m not sure about ADNS.
Thanks Carl, I will communicate my findings. Another question do NetScaler’s need to be same firmware version for all GSLB sides?
Nope. It should work if they are different versions, except for new features (e.g. ECS), of course.
Hi Carl and thank you again for the useful job that you made for all of Citrix technical specialists.
I have an easy question: if I put under GSLB two couple of StoreFront, when primary site goes down and the client re-connect to the secondary one, does the current cookie permit to access to the new StoreFront or the client have to authenticate again?
Thank you very much and congrats.
Each StoreFront Server Group has its own Authentication Service so I expect users would have to login again. And maybe have to close browser and reopen it.
Hello Carl,
Thanks for the post.
Please, I would like to get some support for the following matter.
I have configured a GSLB Active-StandBy scenario having two Internet links ISP1 and ISP2 in the Active Data Center. Therefore, the users will ever receive one IP belonging to ISP1 or ISP2 whenever they make a DNS request to the GSLB system. Yesterday, the Internet of ISP1 was down and the router and all its interfaces were UP. In other words, there were no Internet connectivity in ISP1. Unfortunately, the NetScaler GSLB system continued responding the DNS requests with IPs of the ISP1 which had no Internet access. As a result, the users could not access the services whenever the NetScaler answered with an IP belonging to ISP1, so I need to manually disable (it is supossed to be automatic) the GSLB services related to this ISP1. I need to know if there is an option to monitor the Internet across the router no matter if it and its interfaces are UP. Maybe, by creating a PING monitor to check an ALWAS-UP site in the Internet across the routers. I see that MEP cannot be able to help me to monitor the links, can it? The NetScaler MEP cannot detect that a link or the Internet is down and make the GSLB system to stop responding the DNS requests using IPs of the down link.
Thanks in advance.
Jorge
I believe that is correct. You would have to bind monitors to each GSLB Service.
Hello Carl,
Thanks for this outstanding post.
Please, I would like to get some recommendations to achieve a deployment that my boss wants.
I am deploying a GSLB system by using two NetScaler 8005 appliances NS 11.1, both located in different locations away from each other. My boss wants the system to act as an active-“passive” GSLB, so a SIte A will always respond DNS queries and if it fails, a Site B will take over. So far, it would be easy to deploy; but, my boss wants that Site B not to be as “passive” as expected. He wants that Site B redirects all the DNS queries to Site A (in a manner of forwarding DNS). In other words, the Site B’s NetScaler will be acting as forwarding DNS to the NetScaler in Site A and only if the Site A goes down, Site B’s NetScaler will take over. Does the NS system support such configuration? Hope I could have explained myself clearly.
Any comment will be very very appreciated.
Thanks Sir.
Omar
Are you referring to DNS? Or HTTP?
In either case, you can create a Load Balancing vServer on Site B that has a service that points to the listener on Site A. Create a second LB vServer that uses services on Site B and bind this second load balancer as “backup vServer” for the first vServer.
Hello Sir,
Thanks for your answer. I have many services behind the Site A NetScaler (i.e. SSL, HTTP, RDP, FTP, SFTP, SSH) and those are located only in the Site A. That is the reason why I need that the NetScaler in Site B acts like a forwarding DNS, so the clients will ever reach the Site A even though they send their DNS queries to SIte B (Site B NetScaler is supposed to redirect DNS queries to site A NetScaler). I have tried to configure the vServer on Site B, but i did not succeded because the IP I must use as VIP is already acting as SNIP | ADNS svc IP in the appliance; indeed, this IP is the Site B Listener and it must be represented by the SNIP and the VIP in the same time. I guess I cannot re-use a SNIP in order to configure it as a VIP. How could I address this?
Thanks in advance Sir.
any comment or suggestion is very appreciated.
Best regards
Omar.
If you do DNS Load Balancing instead of ADNS, when NetScaler receives a DNS request on the LB VIP, NetScaler will return local ADNS records and anything not on the local appliance will be forwarded to the remote DNS server (ADNS in Site A). If your Site B is publicly accessible, you can simply change the NAT to point to the DNS LB VIP instead of the ADNS IP. Or update the DNS delegation to point to the DNS LB VIP in Site B instead of the ADNS IP in Site B.
Hello Sir,
really, your help is very very appreciated.
You say: “when NetScaler receives a DNS request on the LB VIP, NetScaler will return local ADNS records and anything not on the local appliance will be forwarded to the remote DNS server”, but in my case, I think that the NetScaler in Site B will find everything in its own site and will respond everything. There won’t be “anything not on the local appliance which could be forwarded to the remote DNS server”. Site B NetScaler will answer everything due to it will be authoritative for its GSLB domains which are the same as the domains in Site A.
On the other hand, I have just one public IP for DNS listening in the Site B. So I must use the same as SNIP and ADNS IP or VIP. I think this might be more addressable if the SNIP could be re-used as VIP.
Thanks.
And sorry for keeping making questions.
Best regards,
Omar
Regarding NAT, you can forward different port numbers to different DMZ IP addresses. This is called Port Address Translation.
If Site B is authoritative for the same DNS names as Site A, then you need to configure Site B identically to Site A. Meaning you configure GSLB vServer to return the Site A GSLB Service when it’s up. And return Site B GSLB Service when Site A is down. This is a standard Active/Passive configuration. You have two GSLB vServers configured. One GSLB vServer returns the Site A IP address (Site A GSLB Service). The other GSLB vServer returns the Site B IP address (Site B GSLB Service). The DNS name is bound to the GSLB vServer that returns the Site A IP. Then edit the GSLB vServer that returns Site A IP and go to Protection > Backup vServer, and specify the GSLB vServer that returns Site B IP.
Hi Carl,
Have you done anything on powered zone mappings with GSLB?, I have tried to set it up think i might be missing something.
http://docs.citrix.com/en-us/netscaler/11-1/solutions/global-server-load-balancing–gslb–powered-zone-preference.html
Thanks
Brenton.
I try to avoid stretched farms (and zones) if I can. Otherwise, it’s just a matter of injecting the zone into the HTTP header sent to StoreFront.
Hello Carl,
Hope you could support me with this matter.
I am configuring GSLB in ONE box with NS11.1. The NS must answer DNS queries by using one IP of three different Internet Public IP segments. The answering must obviously depend on the availability of the ISP link as well as the service (http and ftp) itself. As a GSLB IP, I have configured an internal one. In order to check the health of the GSLB services I am configuring a monitor of type PING and Transparent which check the IP 208.67.222.222 (an always-UP address in the Internet) going across a router. The monitor does not work when I add it to a GSLB Service even I have ping reply in the NS. I receive “Failure – Internal Error: resource unavailable to send probe” when I add the monitor to a GSLB Service. I have tested by adding the monitor to a LB service and it works fine. Why could be the explanation of this behaviour? Am I missing something in my configuration? I remember to have configured a platform in the past by using this way and it worked fine woth the monitors pointing to an always-UP IP address in the Internet.
Thanks
A bug? Might have to call Citrix Support.
Hey Luis, the problem here is GSLB does not support transparent monitors. Just uncheck that and will work.
This is great Article and easy to explain steps
does anything need to be done on the XenDesktop side for this to work properly? If so, what? thx
You mean StoreFront? See https://www.carlstalhood.com/storefront-3-5-configuration-for-netscaler-gateway/#multisite