Navigation
- Change Log
- Two common methods of getting certificates on NetScaler:
- Import the intermediate certificate and bind it.
- Export/Download certificate files from NetScaler
- Replace the management certificate, and then force SSL access for management.
- Update certificates before they expire.
💡 = Recently Updated
Change Log
- 2018 Oct 7 – Create Key File – 12.1 build 49 supports AES256 encoding
- Create CSR File – added info from CTX232305 How to create a SAN CSR in NetScaler 12.0 57.19
- 2018 Mar 13 – in Replace Management Certificate section, added link to CTP George Spiers How to secure management access to NetScaler and create unique certificates in a highly available setup
Convert .PFX Certificate to PEM Format
You can export a certificate (with private key) from Windows, and import it to NetScaler.
To export a Windows certificate in .pfx format
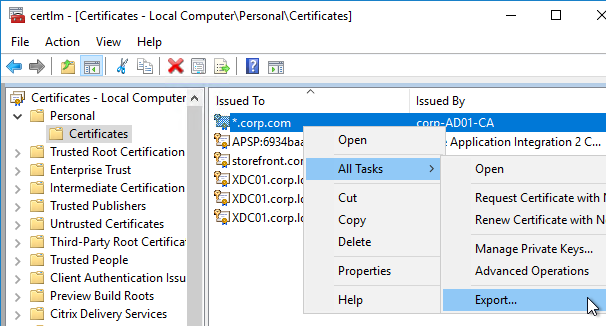
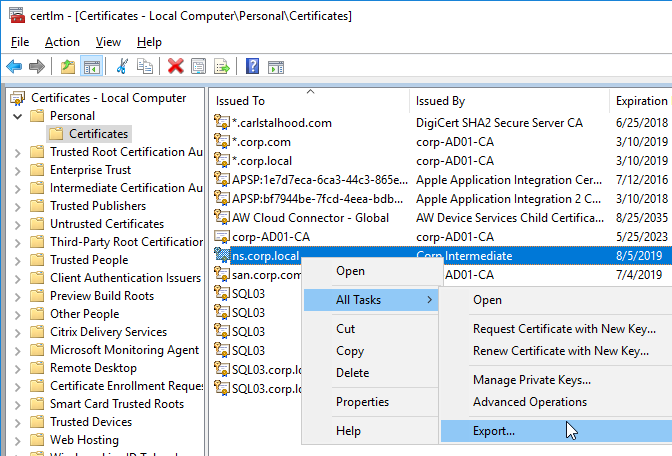
- If Windows Server 2012 or newer, on the Windows server that has the certificate, you can run certlm.msc to open the Certificates console pointing at Local Computer.
- Or, run mmc.exe, manually add the Certificates snap-in, and point it to Local Computer.
- Go to Personal > Certificates.
- Right-click the certificate, expand All Tasks, and click Export.
- On the Welcome to the Certificate Export Wizard page, click Next.
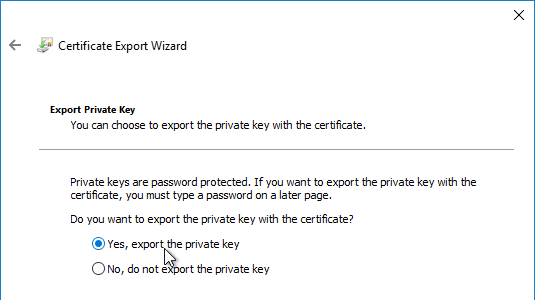
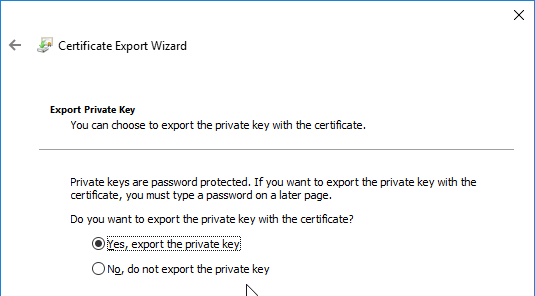
- On the Export Private Key page, select Yes, export the private key, and click Next.
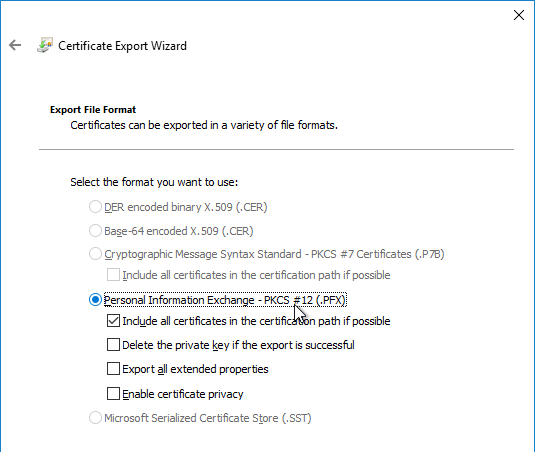
- On the Export File Format page, click Next.
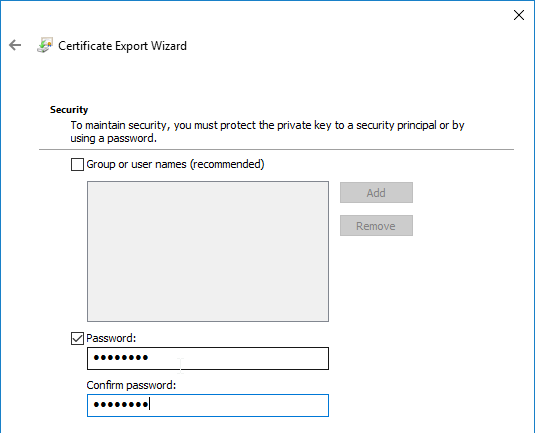
- On the Security page, check the box next to Password, and enter a new temporary password. Click Next.
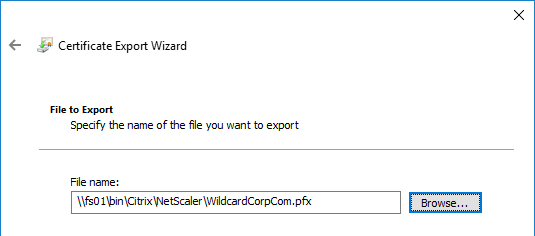
- On the File to Export page, specify a save location and name the .pfx file. Don’t put any spaces in the filename. Click Next.
- In the Completing the Certificate Export Wizard page, click Finish.
- Click OK when prompted that the export was successful.
To import a .pfx file
Newer builds of NetScaler ADC (e.g. 12.0 build 59 and 12.1 build 49) import .pfx files and use them in their native encrypted format.
- NetScaler ADC 12.0 build 58 and NetScaler ADC 12.1 build 48 had bugs preventing PFX files from importing correctly. Upgrade to a newer build.
Older builds of NetScaler ADC convert the .pfx file to an unencrypted .pem file that is named the same as the original .pfx file but with an additional .ns extension.
To import the .pfx file:
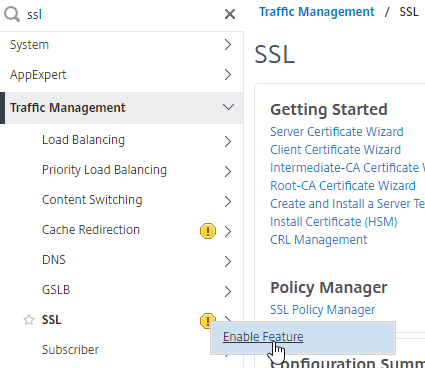
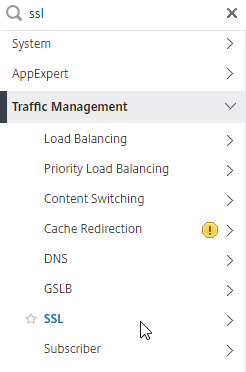
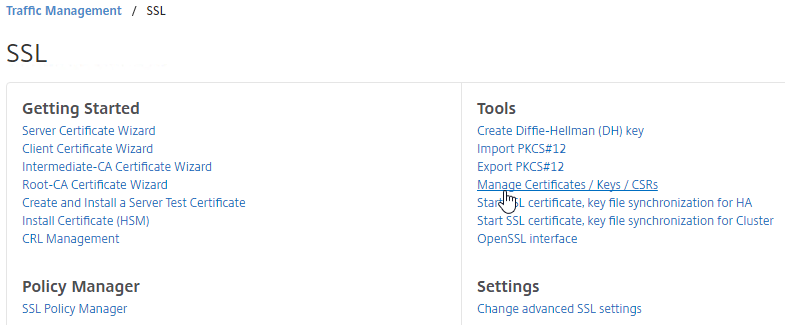
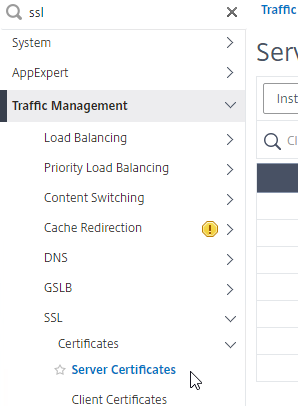
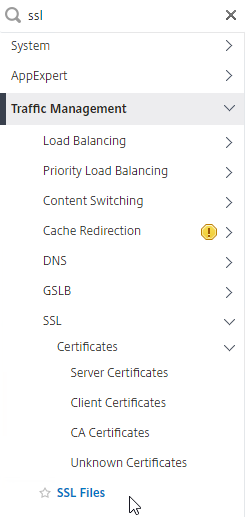
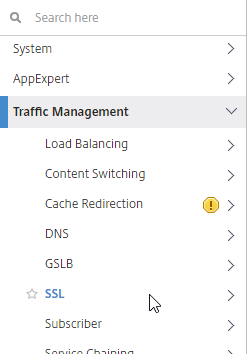
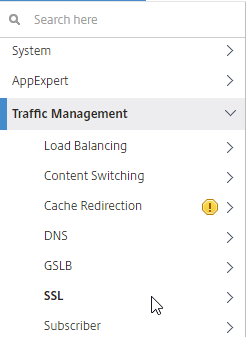
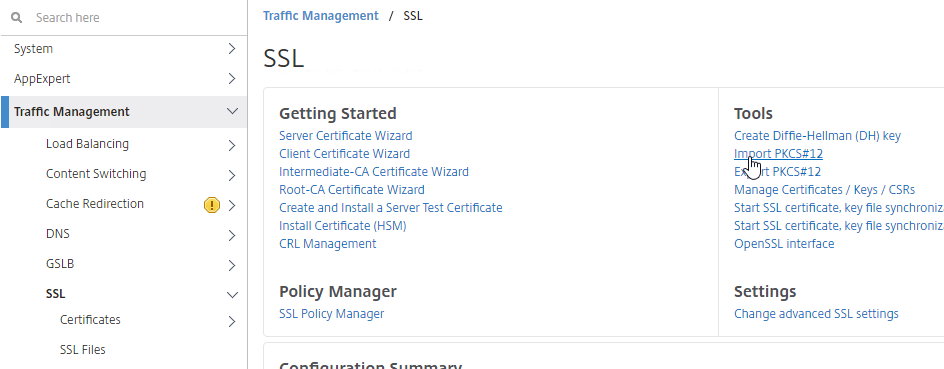
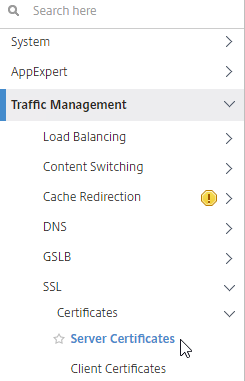
- On the NetScaler, expand Traffic Management, and click SSL.
- If the SSL feature is disabled, right-click the SSL node, and click Enable Feature.
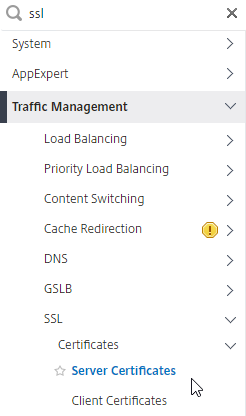
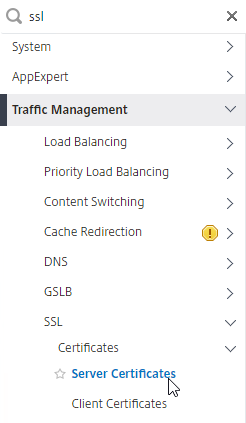
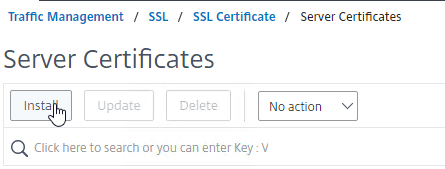
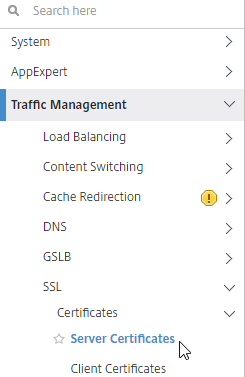
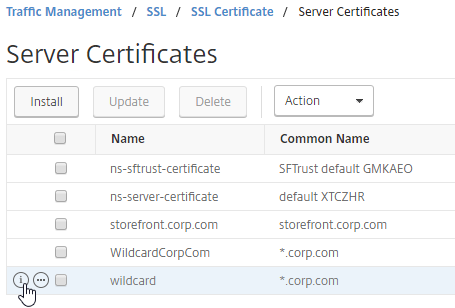
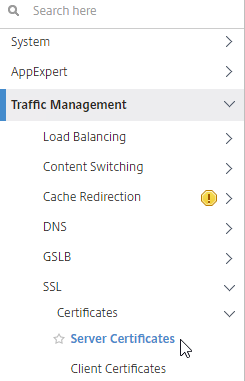
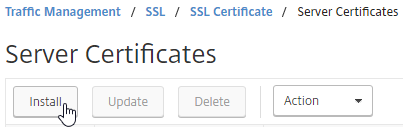
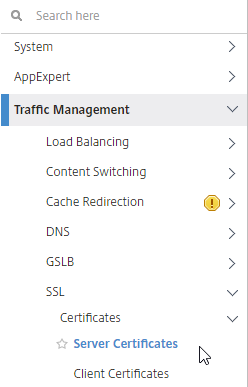
- Go to Traffic Management > SSL > Certificates > Server Certificates.
- There are four different certificate nodes:
- Server Certificates have private keys. These certificates are intended to be bound to SSL vServers.
- Client Certificates also have private keys, but they are intended to be bound to Services so NetScaler can perform client-certificate authentication against back-end web servers.
- CA Certificates don’t have private keys. The CA certificates node contains intermediate certificates that are linked to Server Certificates. CA certificates can also be used for SAML authentication, and to verify client certificates.
- Unknown Certificates list the certificates that don’t fall under the other categories. The Azure SAML certificate shows up here.
- On the left, click the Server Certificates node.
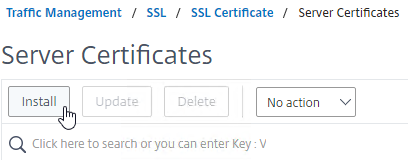
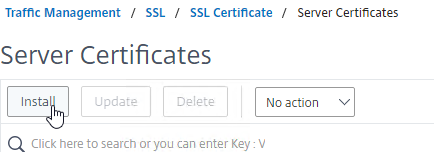
- On the right, click Install.
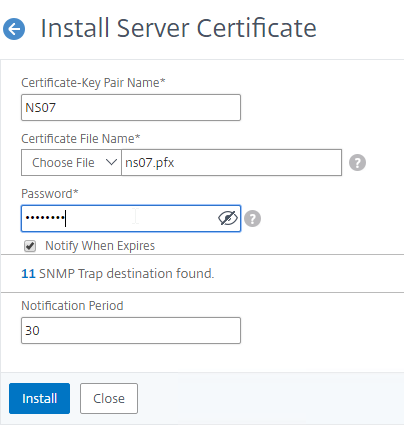
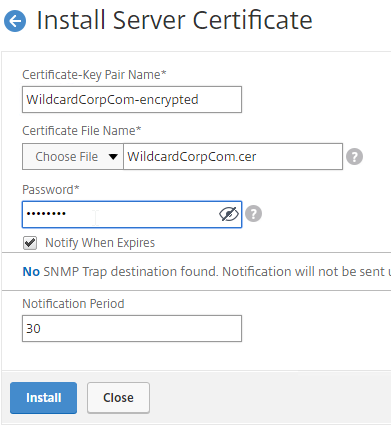
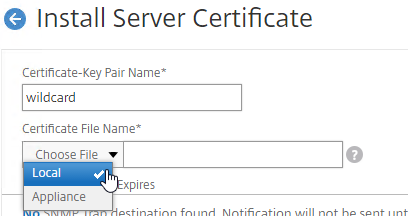
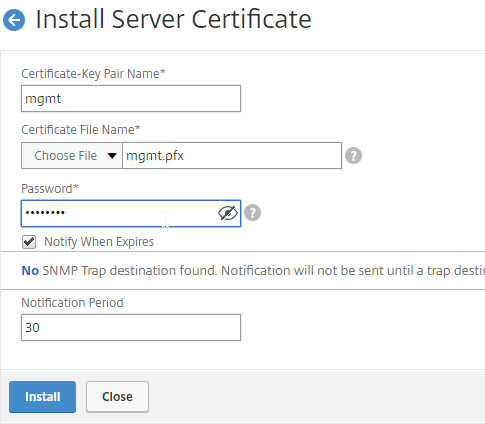
- Give the certificate (Certificate-Key Pair) a name.
- Click the drop-down next to Choose File, select Local, and browse to the .pfx file that you exported earlier.
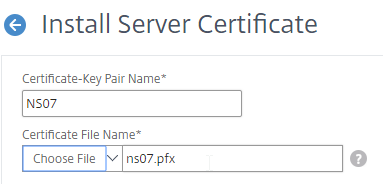
- After browsing to the .pfx file, NetScaler ADC will prompt you to enter the password for the .pfx file.
- Then click Install.
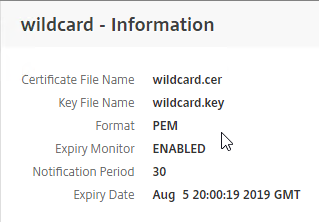
- If you click the information icon next to the new certificate…
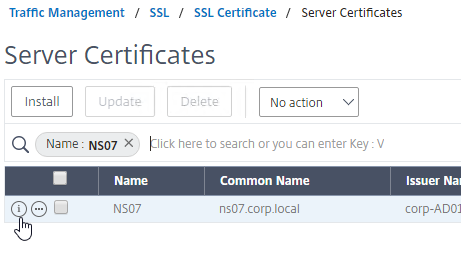
- You’ll see that NetScaler ADC uses the file in native .pfx format. No PEM conversion.
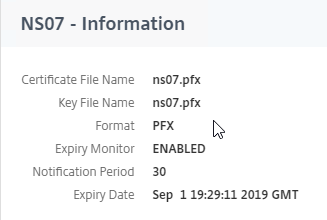
- You’ll see that NetScaler ADC uses the file in native .pfx format. No PEM conversion.
- You can now link an intermediate certificate to this SSL certificate, and then bind this SSL certificate to SSL and/or NetScaler Gateway Virtual Servers.
- To automatically backup SSL certificates and receive notification when the certificates are about the expire, deploy NetScaler Management and Analytics System. Also see Citrix CTX213342 How to handle certificate expiry on NetScaler.
To convert PFX to PEM (with Private Key encryption)
To convert PFX to PEM, do the following:
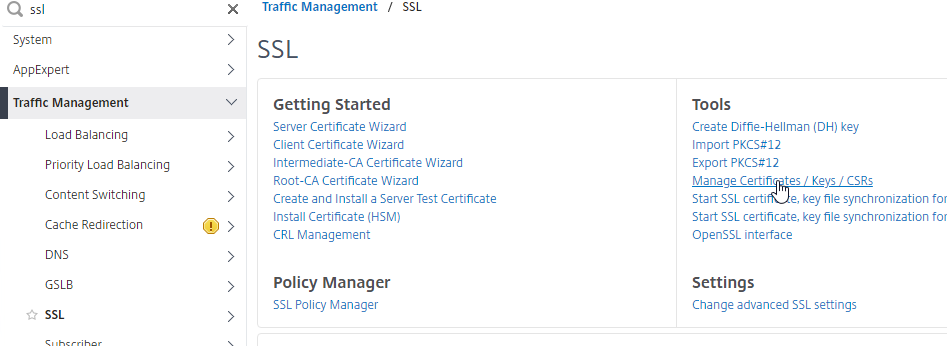
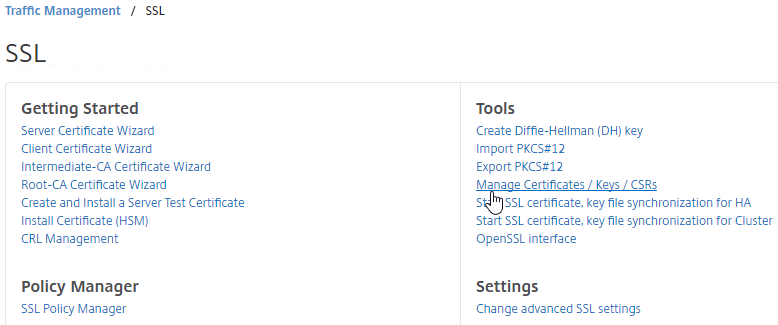
- In the NetScaler Configuration GUI, on the left, expand Traffic Management, and click SSL.
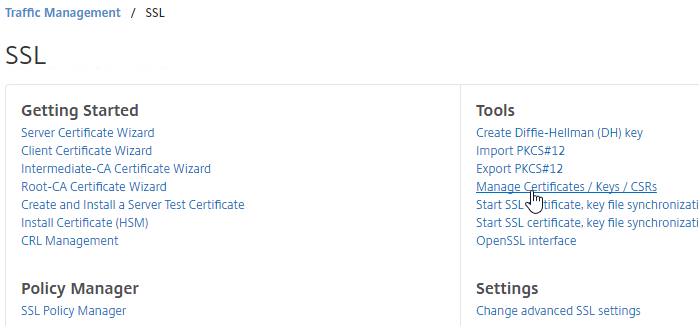
- In the right column of the right pane, in the Tools section, click Import PKCS#12.
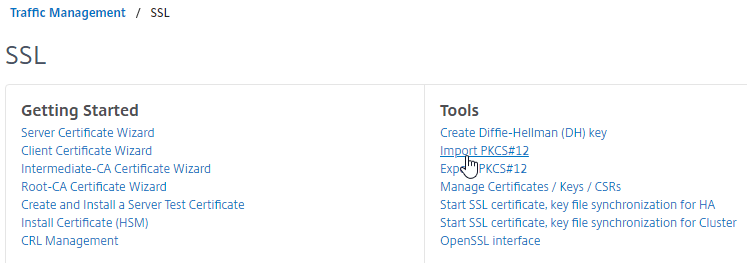
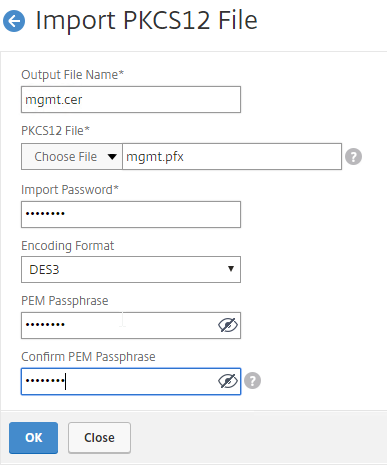
- In the Import PKCS12 File dialog box:
- In the Output File Name field, enter a name for a new file where the converted PEM certificate and private key will be placed. This new file is created under /nsconfig/ssl on the NetScaler appliance.
- In the PKCS12 File field, click Choose File, and select the previously exported .pfx file.
- In the Import Password field, enter the password you specified when you previously exported the .pfx file.
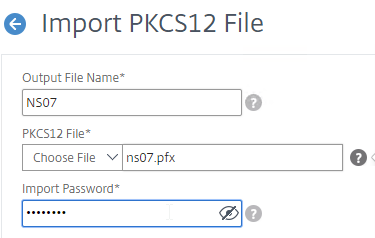
- By default, the private key in the new PEM file is unencrypted. To encrypt the private key, change the Encoding Format selection to AES256 (if NetScaler 12.1 build 49 or newer) or DES3. This causes the new PEM file to be password protected, and encrypted.
- Enter a permanent password for the new PEM file, and click OK.
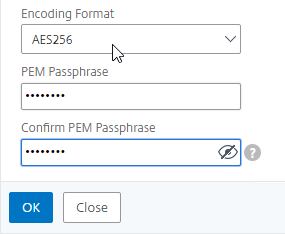
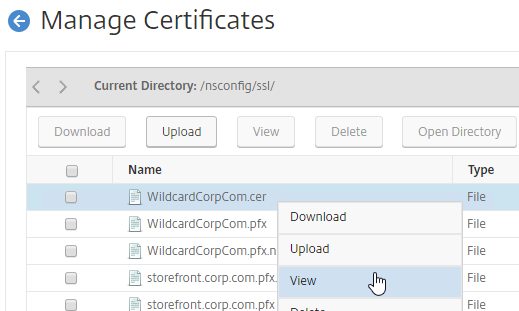
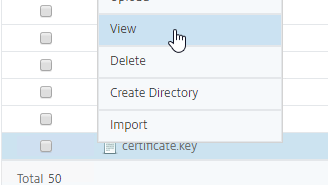
- You can use the Manage Certificates / Keys / CSRs link to view the new PEM file.
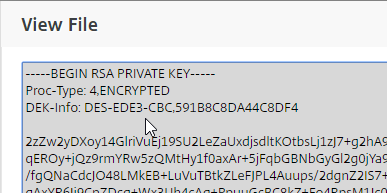
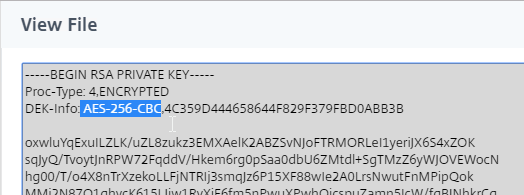
- Right-click the new file, and click View.
- Notice that the Private Key is encrypted.
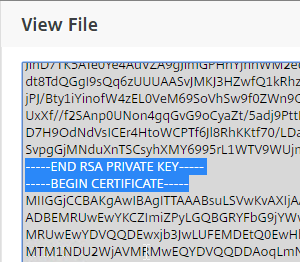
- If you scroll down, notice that the file contains both the certificate, and the RSA Private key.
- Right-click the new file, and click View.
- Now that the PFX file has been converted to a PEM file, the PEM certificate file must be installed before it can be used.
- On the left side of the NetScaler Configuration GUI, go to Traffic Management > SSL > Certificates > Server Certificates.
- On the right, click Install.
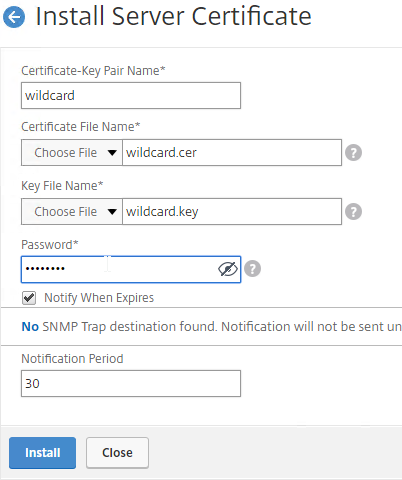
- In the Certificate-Key Pair Name field, enter a friendly name for this certificate.
- In the Certificate File Name field, click the drop-down next to Choose File, and select Appliance.
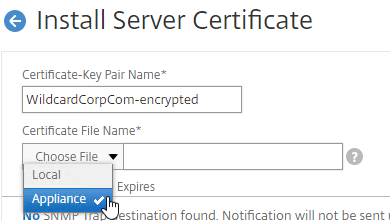
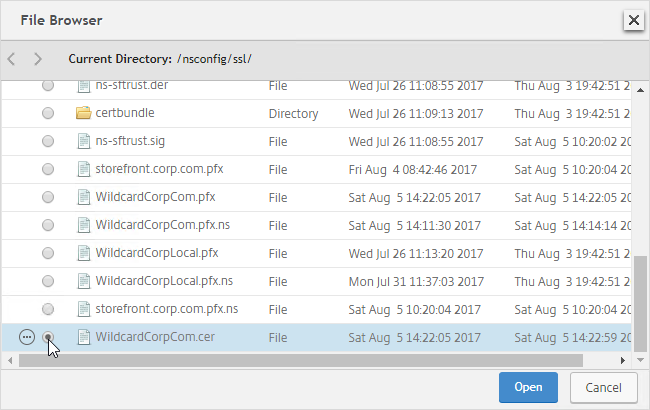
- Click the radio button next to the .cer file you just created, and click Open. The new file is probably at the bottom of the list.
- NetScaler will ask you to enter the password for the encrypted private key.
- Click Install.
- On the left side of the NetScaler Configuration GUI, go to Traffic Management > SSL > Certificates > Server Certificates.
- You can now link an intermediate certificate to this SSL certificate, and then bind this SSL certificate to SSL and/or NetScaler Gateway Virtual Servers.
- To automatically backup SSL certificates and receive notification when the certificates are about the expire, deploy NetScaler Management and Analytics System. Also see Citrix CTX213342 How to handle certificate expiry on NetScaler.
- You can also export the certificate files and use them on a different NetScaler.
Create Key and Certificate Request
If you want to create free Let’s Encrypt certificates, see John Billekens’ PowerShell script detailed at Let’s Encrypt Certificates on a NetScaler.
You can create a key pair and Certificate Signing Request (CSR) directly on the NetScaler appliance. The CSR can then be signed by an internal, or public, Certificate Authority.
Most Certificate Authorities let you add Subject Alternative Names when creating (or purchasing) a signed certificate, and thus there’s no reason to include Subject Alternative Names in the CSR created on NetScaler. You typically create a CSR with a single DNS name. Then when submitting the CSR to the Certificate Authority, you type in additional DNS names.
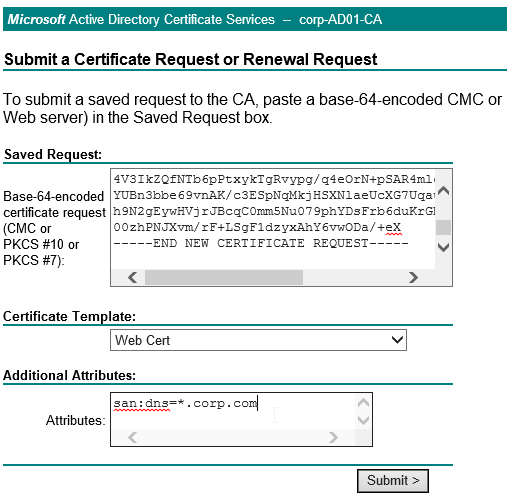
- For a Microsoft Certificate Authority, you can enter Subject Alternative Names in the Attributes box of the Web Enrollment wizard.
- For public Certificate Authorities, you purchase a UCC certificate or purchase a certificate option, that lets you type in additional names.
To create a key pair on NetScaler
- On the left, expand Traffic Management, expand SSL, and click SSL Files.
- On the right, switch to the Keys tab.
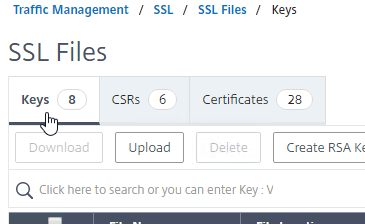
- Click Create RSA Key.
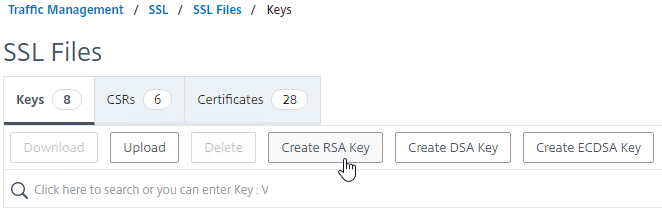
- In the Key Filename box, enter a new filename (e.g. wildcard.key). Key pair files typically have a .key extension.
- In the Key Size field, enter 2048 bits.
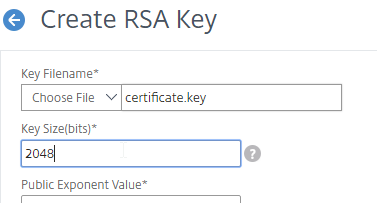
- By default, the private key is unencrypted. To encrypt it, set the PEM Encoding Algorithm drop-down to AES256 (if NetScaler 12.1 build 49 or newer) or DES3.
- Enter a password to encrypt the private key.
- Click Create.
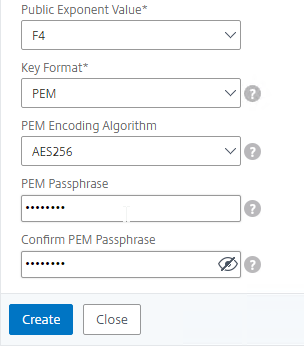
- To view the new file:
- Go to Traffic Management > SSL.
- On the right, in the right column, click Manage Certificates / Keys / CSRs.
- Scroll down to the new file, right-click it, and click View.
- The Private Key should be encrypted with your chosen encoding algorithm.
To create CSR file
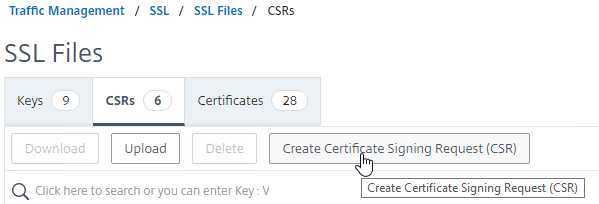
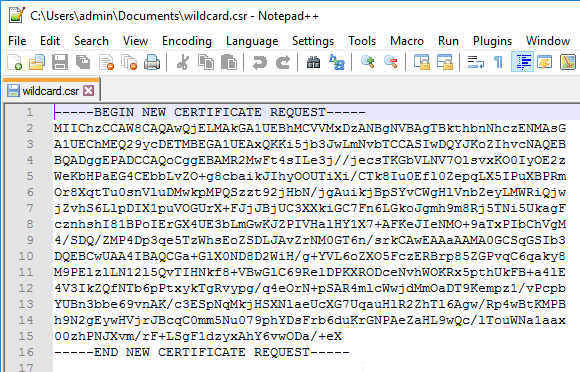
- Back in the SSL Files page, on the right, switch to the CSRs tab.
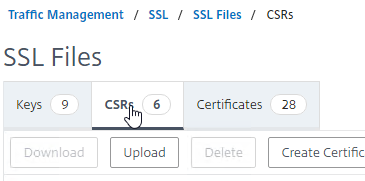
- Click Create Certificate Signing Request (CSR).
- In the Request File Name field, enter the name of a new CSR file. CSR files typically have .csr or .txt extension.
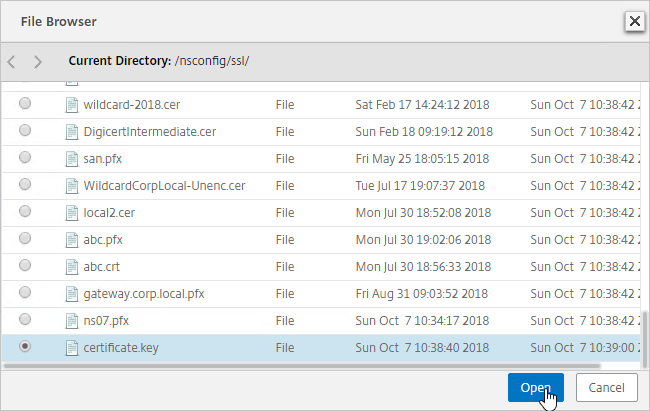
- In the Key Filename field, click Choose File and select the previously created .key file. It’s probably at the bottom of the list.
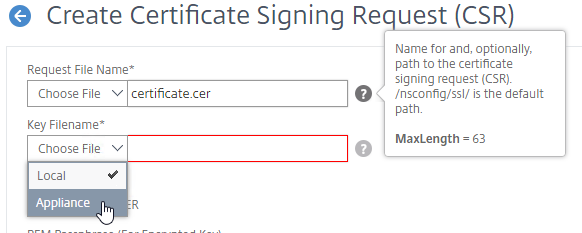
- If the key file is encrypted, enter the password.
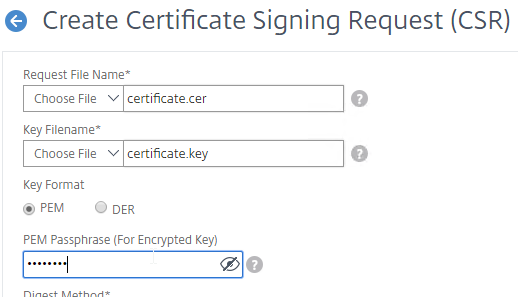
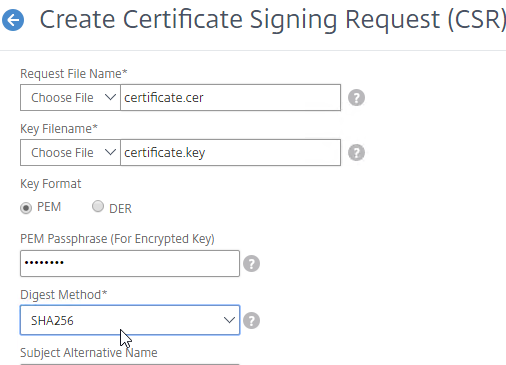
- You can optionally change the CSR Digest Method to SHA256. This only applies to the CSR and does not affect the CA-signed certificate.
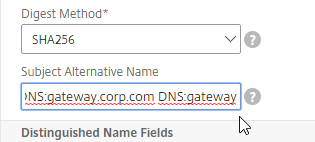
- Newer builds of NetScaler let you specify up to three Subject Alternative Names in the CSR. Some Certificate Authorities ignore this field and instead require you to specify the Subject Alternative Names when purchasing the signed certificate. See CTX232305 How to create a SAN CSR in NetScaler 12.0 57.19.
- In the Common Name field, enter the FQDN of the SSL enabled-website. If this is a wildcard certificate, enter * for the left part of the FQDN. This is the field that normally must match what users enter into their browser address bars.
- In the Organization Name field, enter your official Organization Name.
- Enter IT, or similar, as the Organization Unit.
- Enter the City name.
- In the State field, enter your state name without abbreviating.
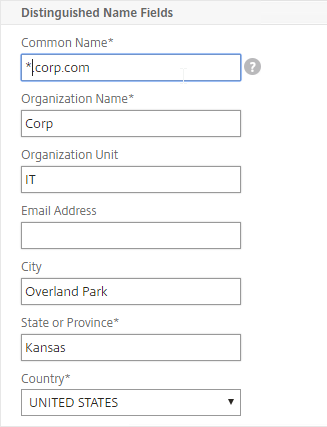
- Scroll down and click Create.
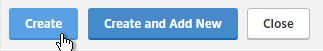
- Right-click the new .csr file, and click Download.
Get CSR signed by CA, and install certificate on NetScaler
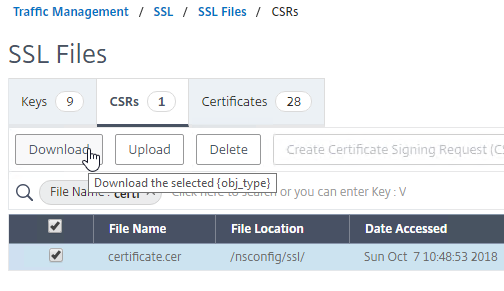
- Open the downloaded .csr file with Notepad, and send the contents to your Certificate Authority.
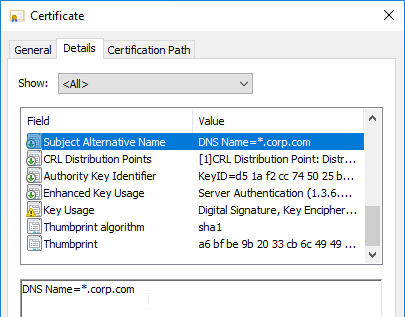
- Chrome requires every certificate to have at least one Subject Alternative Name that matches the FQDN entered in Chrome’s address bar. Public CAs will handle this automatically. But for Internal CAs, you typically must specify the Subject Alternative Names manually when signing the certificate.
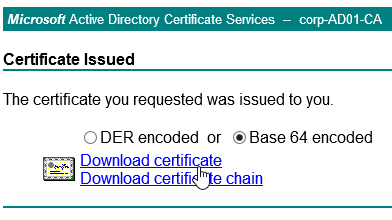
- If the CA asks you for the type of web server, select Apache, or save the CA response as a Base 64 file.
- Chrome requires every certificate to have at least one Subject Alternative Name that matches the FQDN entered in Chrome’s address bar. Public CAs will handle this automatically. But for Internal CAs, you typically must specify the Subject Alternative Names manually when signing the certificate.
- After you get the signed certificate, on the left side of the NetScaler Configuration GUI, expand Traffic Management > SSL > Certificates, and click Server Certificates.
- On the right, click Install.
- In the Certificate-Key Pair Name field, enter a friendly name for this certificate.
- In the Certificate File Name field, click the drop-down next to Choose File, and select Local.
- Browse to the Base64 (Apache) .cer file you received from the Certificate Authority.
- In the Key File Name field, click the drop-down next to Choose File, and select Appliance.
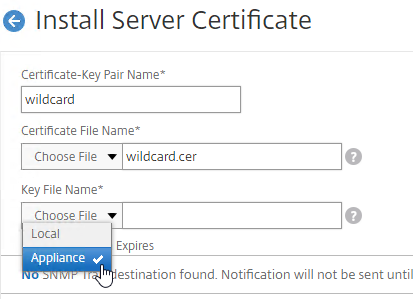
- Select the key file you created earlier, and click Open. It’s probably at the bottom of the list.
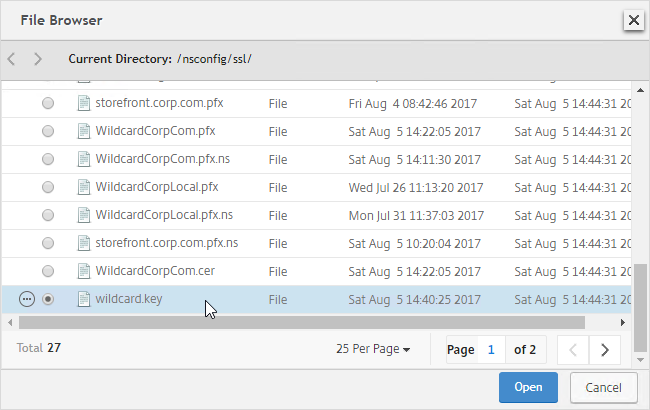
- If the key file is encrypted, enter the password.
- Click Install.
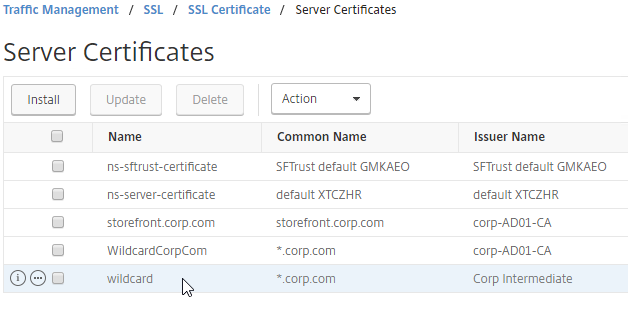
- The certificate is now added to the list.
- You can now link an intermediate certificate to this SSL certificate, and then bind this SSL certificate to SSL and/or NetScaler Gateway Virtual Servers.
- To automatically backup SSL certificates and receive notification when the certificates are about the expire, deploy Citrix NetScaler Management and Analytics. Also see Citrix CTX213342 How to handle certificate expiry on NetScaler.
- You can also export the certificate files and use them on a different NetScaler.
Intermediate Certificate
If your Server Certificate is signed by an intermediate Certificate Authority, then you must install the intermediate Certificate Authority’s certificate on the NetScaler. This Intermediate Certificate then must be linked to the Server Certificate.
To get the correct intermediate certificate
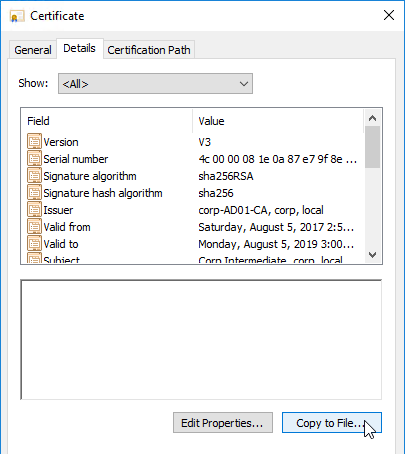
- Log into Windows, and double-click the signed certificate file.
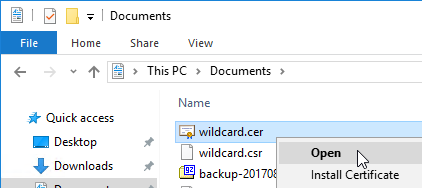
- On the Certification Path tab, double-click the intermediate certificate (e.g. Go Daddy Secure Certificate Authority. It’s the one in the middle).
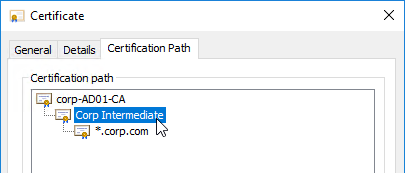
- On the Details tab, click Copy to File.
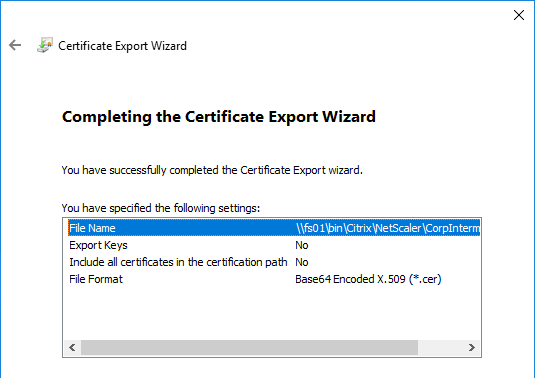
- In the Welcome to the Certificate Export Wizard page, click Next.
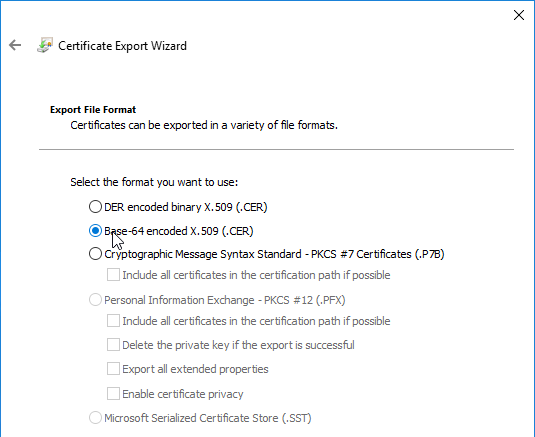
- In the Export File Format page, select Base-64 encoded, and click Next.
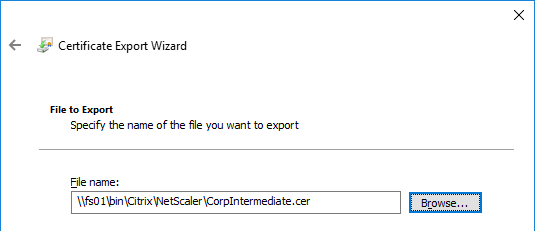
- Give it a file name, and click Next.
- In the Completing the Certificate Export Wizard page, click Finish.
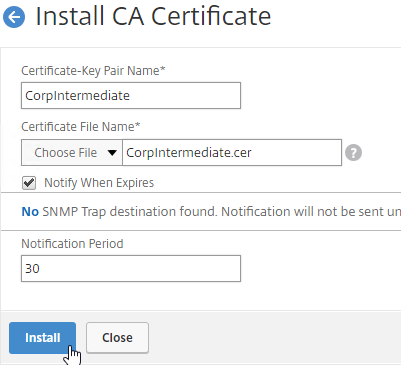
To import the intermediate certificate
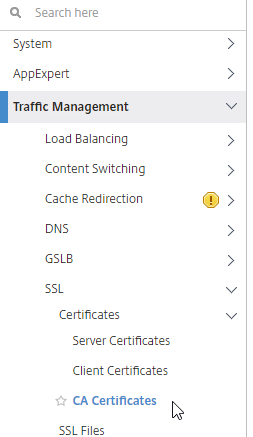
- In the NetScaler configuration GUI, expand Traffic Management, expand SSL, expand Certificates, and click CA Certificates.
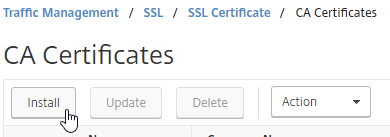
- On the right, click Install.
- Name it Intermediate or similar.
- Click the arrow next to Choose File, select Local, and browse the Intermediate certificate file.
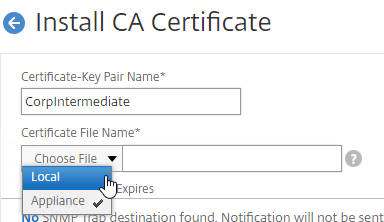
- Click Install.
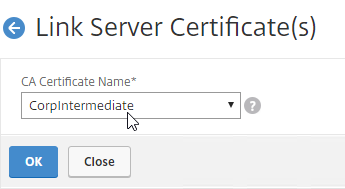
Link Intermediate Certificate to Server Certificate
- Go back to Traffic Management > SSL > Certificates >Server Certificates.
- Right-click the server certificate, and click Link.
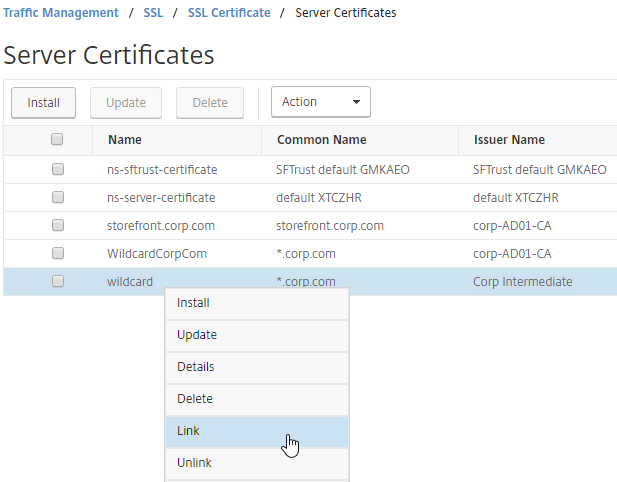
- The previously imported Intermediate certificate should already be selected. Click OK.
- You might be tempted to link the Intermediate certificate to a Root certificate. Don’t do this. Root certificates are installed on client machines, not on NetScaler. NetScaler must never send the root certificate to the client device.
Export Certificate Files from NetScaler
You can easily export certificate files from the NetScaler, and import them to a different NetScaler.
- Go to Traffic Management > SSL > Certificates > Server Certificates.
- Move your mouse over the certificate you want to export, and then click the information icon on the far left.
- Note the file names. There could be one or two file names.
- On the left, go to Traffic Management > SSL.
- On the right, in the right column, click Manage Certificates / Keys / CSRs.
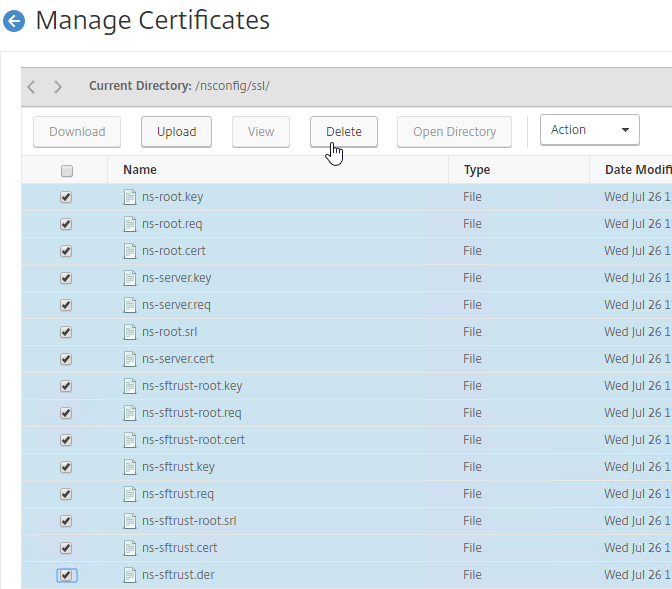
- Find the file(s) in the list, right-click it, and click Download.
- While it seems like you can download multiple files, actually, it only downloads one at a time.
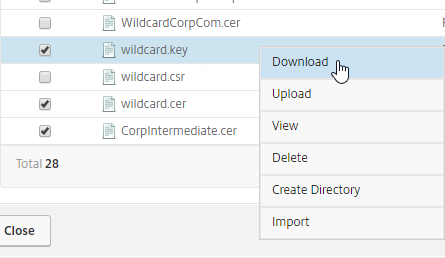
- You might have to increase the number of files shown per page, or go to a different page.
- While it seems like you can download multiple files, actually, it only downloads one at a time.
- Also download the files for any linked intermediate certificate.
- You can now use the downloaded files to install certificates on a different NetScaler.
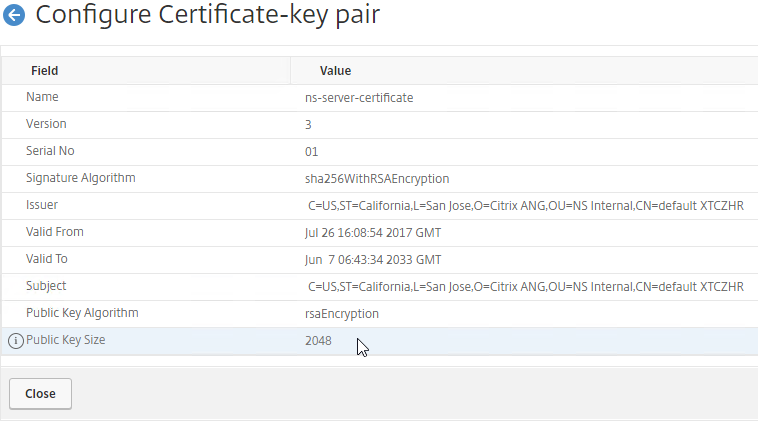
Default Management Certificate Key Length
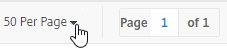
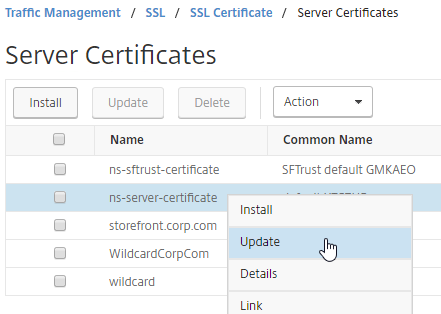
To see the key size for the management certificate, right-click the ns-server-certificate (Server Certificate), and then click Details.
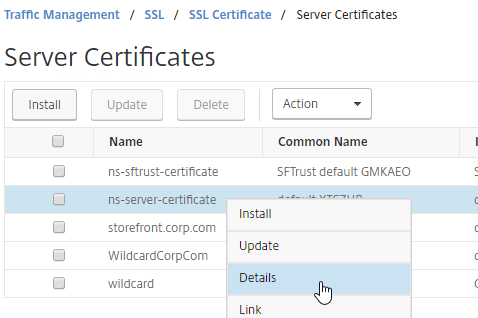
If the management certificate key size is less than 2048 bits, simply delete the existing ns-server-certificate certificate files, and reboot. NetScaler will create a new management certificate with 2048-bit keys.
- Go to Traffic Management > SSL.
- On the right, in the right column, click Manage Certificates / Keys / CSRs.
- Highlight any file named ns-* and delete them. This takes several seconds.
- Then go to the System node, and reboot.
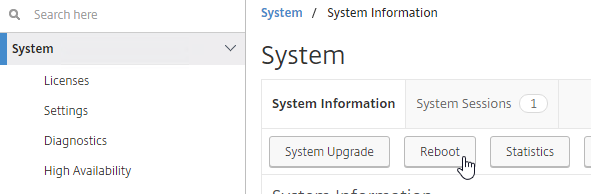
- After a reboot, if you view the Details on the ns-server-certificate, it will be recreated as self-signed, with 2048-bit key size.
Replace Management Certificate
You can replace the default management certificate with a new trusted management certificate.
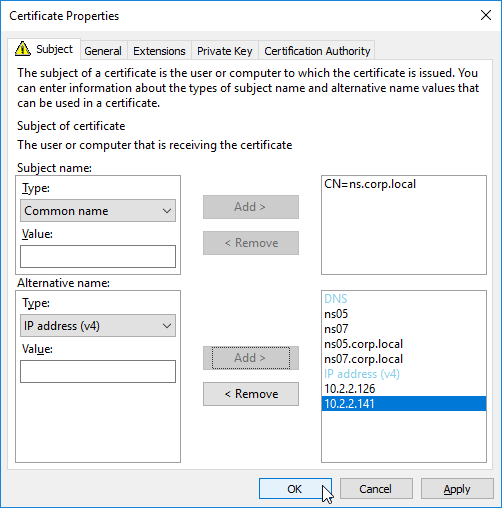
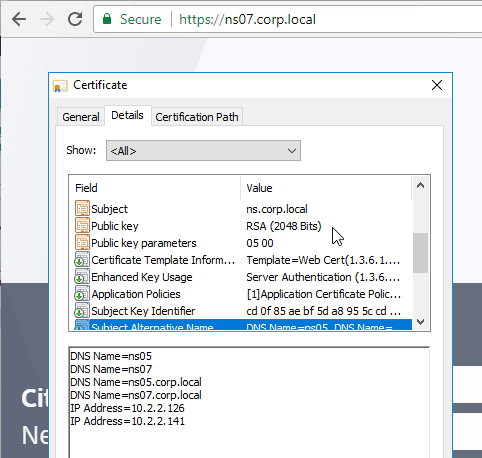
High Availability – When a management certificate is installed on one node of a High Availability pair, the certificate is synchronized to the other node, and used for the other node’s NSIP. So make sure the management certificate matches the DNS names of both nodes. This is easily doable using a Subject Alternative Name certificate. Here are some names the management certificate should match (note: a wildcard certificate won’t match all of these names):
- The FQDN for each node’s NSIP. Example: ns01.corp.local and ns02.corp.local
- The shortnames (left label) for each node’s NSIP. Example: ns01 and ns02
- The NSIP IP address of each node. Example: 192.168.123.14 and 192.168.123.29
- If you enabled management access on your SNIPs, add names for the SNIPs:
- FQDN for the SNIP. Example: ns.corp.local
- Shortname for the SNIP. Example: ns
- SNIP IP address. Example: 192.168.123.30
If you prefer to create a separate management certificate for each HA node, then see CTP George Spiers How to secure management access to NetScaler and create unique certificates in a highly available setup. 💡
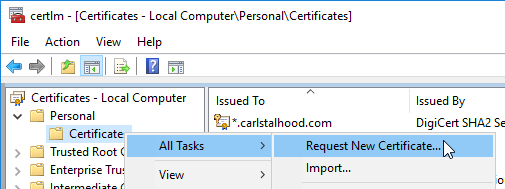
Request Management Certificate
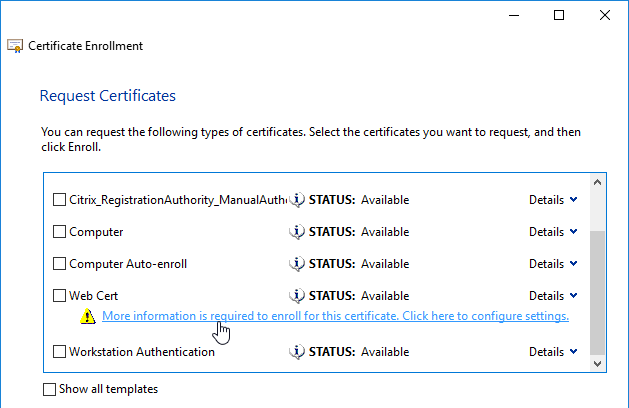
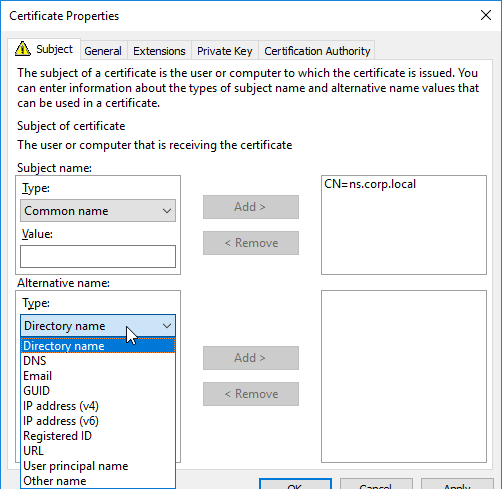
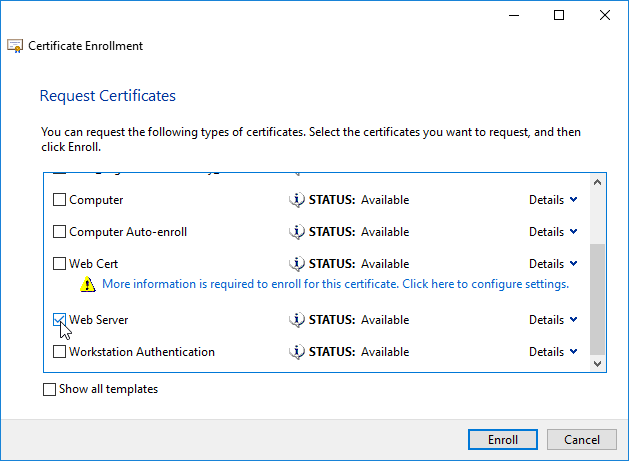
If you are creating a Subject Alternative Name certificate, it’s probably easiest to request a SAN certificate from an internal CA using the MMC Certificates snap-in on a Windows box.:
- Open the MMC certificates snap-in by running certlm.msc on a Windows 2012 or newer machine.
- Go to Personal, right-click Certificate, expand All Tasks, and click Request New Certificate.
- A web server certificate template should let you specify subject information.
- In the top half, change the Subject name > Type drop-down to Common Name. Enter a DNS name, and click Add to move it to the right.
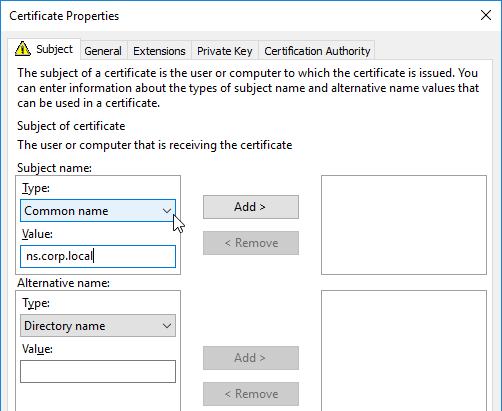
- In the bottom half, change the Alternative Name > Type drop-down to either DNS or IP address (v4). Type in different names or IPs as detailed earlier, and click Add to move them to the right.
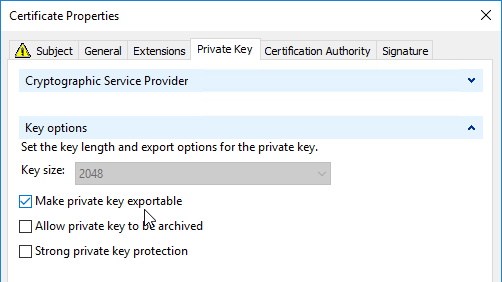
- On the Private Key tab, expand Key Options, and make sure Mark private key as exportable is checked.
- Then finish Enrolling the certificate.
- Export the certificate and Private Key to a .pfx file.
- On the NetScaler, if you want to encrypt the private key, then use the Traffic Management > SSL > Import PKCS#12 tool to convert the .pfx to PEM format.
- Then follow one of the procedures below to replace the management certificate.
Methods of replacing the Management Certificate
There are two methods of replacing the management certificate:
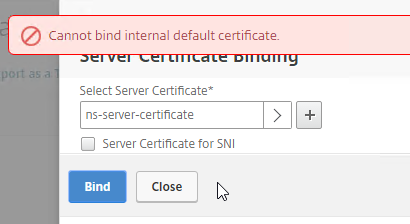
- In the NetScaler GUI, right-click ns-server-certificate, and click Update. This automatically updates all of the Internal Services bindings too. This method is intended for dedicated management certificates, not wildcard certificates. Notes:
- You cannot rename the ns-server-certificate in the NetScaler GUI. It remains as ns-server-certificate.
- ns-server-certificate cannot be bound to Virtual Servers. So make sure you are replacing it with a dedicated management certificate.
- Or manually Bind a new management certificate to each of the Internal Services.
Update Certificate Method
The Update Certificate button method is detailed below:
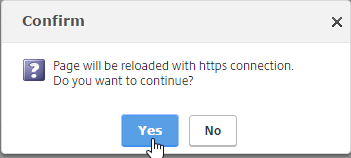
- You can’t update the certificate while connected to the NetScaler using https, so make sure you connect using http.
- On the left, expand Traffic Management, expand SSL, expand Certificates, and click Server Certificates.
- On the right, right-click ns-server-certificate, and click Update.
- Check the box next to Click to update the certificate and key.
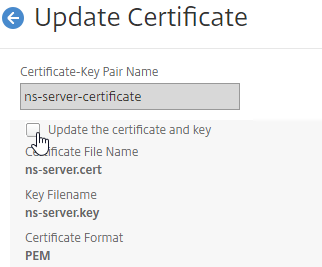
- Click Choose File, and browse to the new management certificate. It could be on the appliance, or it could be on your local machine.
- If the PEM private key is encrypted, enter the password.
- Check the box next to No Domain Check. Click OK.
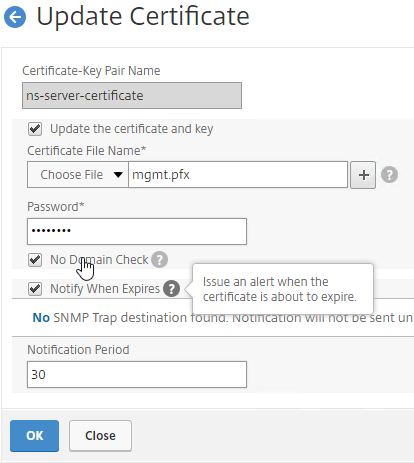
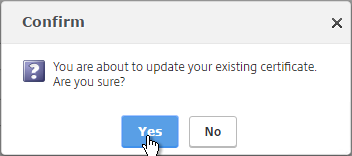
- Click Yes to update the certificate.
- You can now connect to the NetScaler using https protocol. The certificate should be valid, and it should have a 2048 bit key.
Manual Binding Method
The manual Binding to Internal Services method is detailed below:
- You can’t update the certificate while connected to the NetScaler using https, so make sure you connect using http.
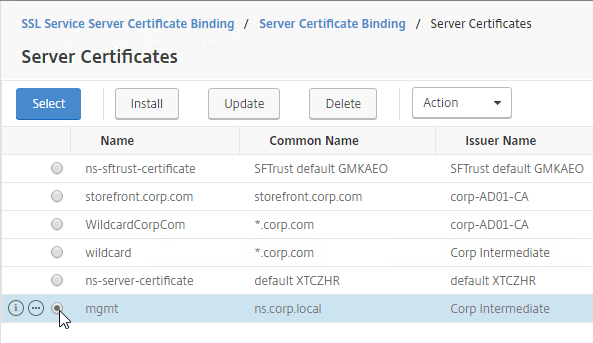
- On the left, expand Traffic Management, expand SSL, expand Certificates, and click Server Certificates.
- On the right, use the Install button to install the new management certificate.
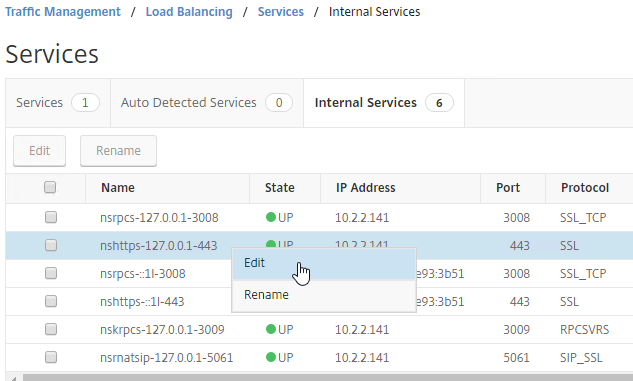
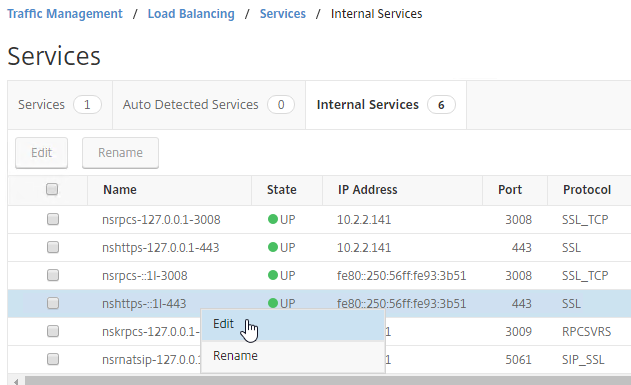
- Go to Traffic Management > Load Balancing > Services.
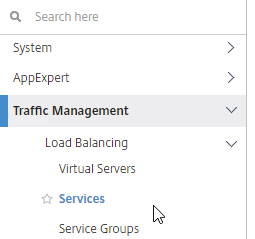
- On the right, switch to the Internal Services tab.
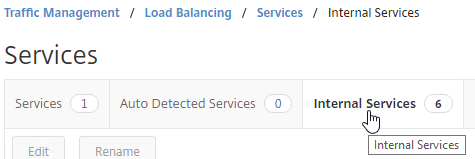
- Right-click one of the services, and click Edit.
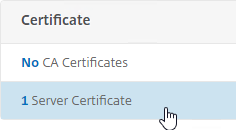
- Scroll down, and click where it says 1 Server Certificate.
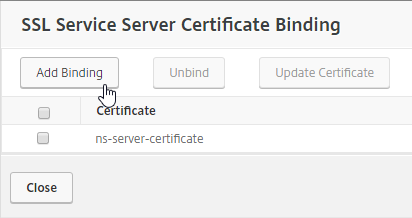
- Click Add Binding.
- Click where it says Click to select.
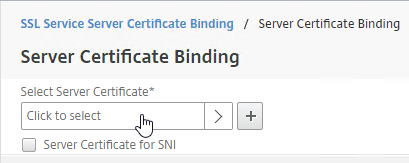
- Click the radio button next to the new management certificate, and click Select.
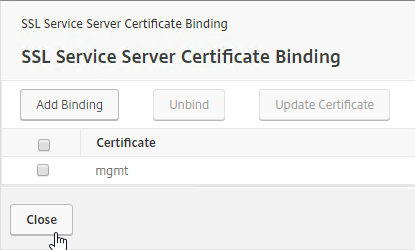
- Click Bind, and click Close.
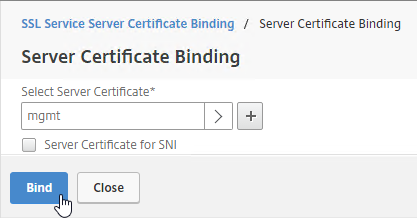
- Click Close.
- If Default SSL Profile is not enabled, then you can modify the SSL Parameters and/or Ciphers on each of these Internal Services.
- Repeat for the rest of the internal services. There should be at least 6 services. Additional Internal Services are created for SNIPs with management access enabled, and High Availability.
Force Management SSL
By default, administrators can connect to the NSIP using HTTP or SSL. This section details how to disable HTTP.
- Connect to the NSIP using https.
- On the left, expand System, expand Network, and click IPs.
- On the right, right-click your NetScaler IP, and click Edit.
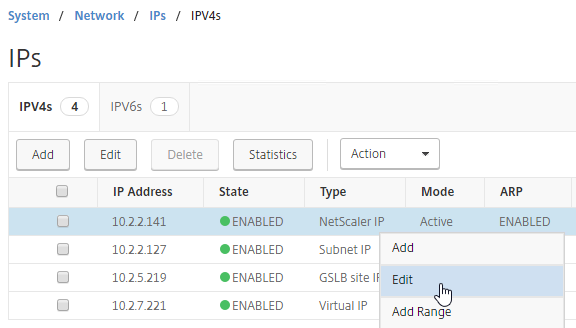
- Near the bottom, check the box next to Secure access only, and then click OK.
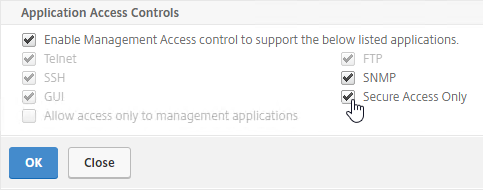
- If you are connected using http, the page will reload using https.
set ns ip 10.2.2.126 -gui SECUREONLY
- Repeat this procedure on the secondary appliance.
- Repeat for any SNIPs that have management access enabled.
Also see:
- Citrix CTX204217 How to redirect users from HTTP to HTTPS while accessing NSIP/Management IP. Requires a Responder policy, and a nsapimgr command.
SSL Certificate – Update
There are two options for updating a certificate:
- Create or Import a new certificate to NetScaler > Traffic Management > SSL > Certificates > Server Certificates. Then find all of the places the original certificate is bound, and manually replace the original certificate binding with the new certificate. This method is obviously prone to errors.
- On NetScaler, simply right-click the existing certificate, and click Update. This automatically updates all of the bindings. Much faster and easier.
To update a certificate using the Update method:
- Create an updated certificate, and export it as .pfx file (with private key). Don’t install the certificate onto NetScaler yet, but instead, simply have access to the .pfx file.
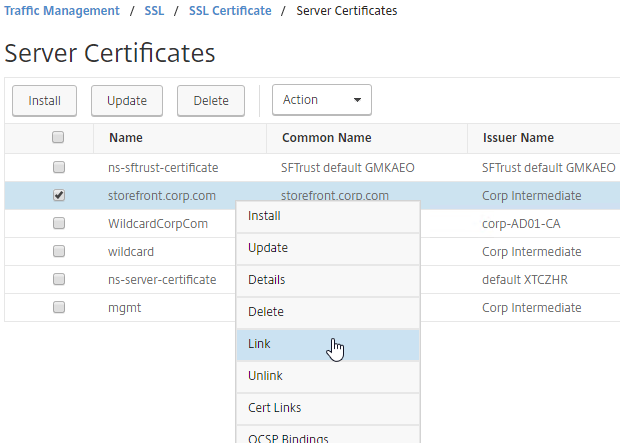
- In NetScaler, navigate to Traffic Management > SSL > Certificates > Server Certificates.
- On the right, right-click the certificate you intend to update, and click Update.
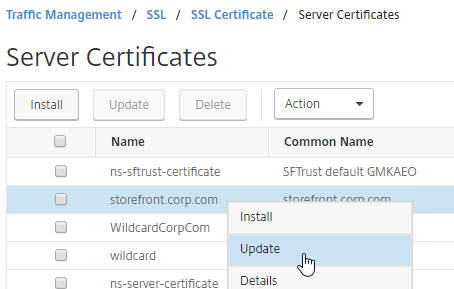
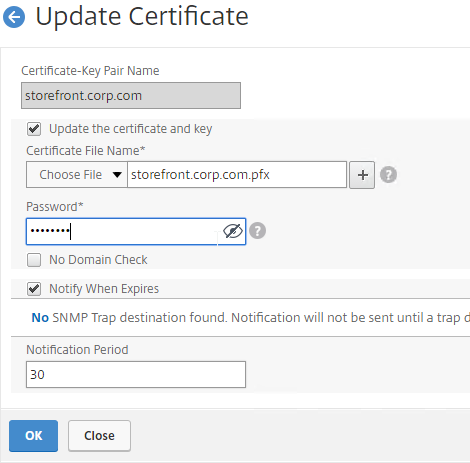
- Check the box next to Update the certificate and key.
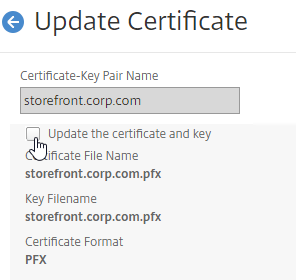
- Click Choose File > Local, and browse to the updated .pfx file.
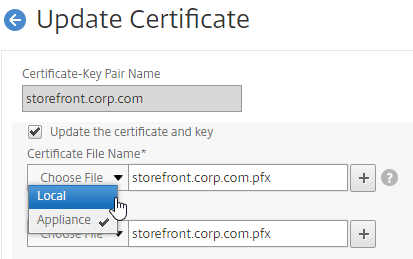
- NetScaler will prompt you to specify the .pfx file password.
- Click OK. This will automatically update every Virtual Server on which this certificate is bound.
- Intermediate certificate – After replacing the certificate, you might have to update the cert link to a new Intermediate certificate.
- Right-click the updated certificate, and click Cert Links, to see if it is currently linked to an intermediate certificate.
- If not, right-click the updated certificate, and click Link, to link it to an intermediate certificate. If it doesn’t give you an option to link it to, then you’ll first have to install the new intermediate certificate on the NetScaler.
Certificates can also be updated in NetScaler Management and Analytics System.
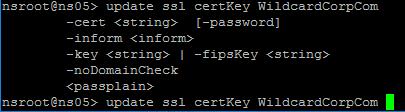
Certificates can be updated from the CLI by running update ssl certKey MyCert. However, the certificate files must be stored somewhere on the appliance, and already be in PEM format.
Hi Carl, when i create the key with password. Then i create the csr with 3 SAN in it to the send it to the public CA(entrut) to receive the cert. when i try to import and put the password of the private through the GUI, the system keeps telling me that I have an ‘invalid password’ which is note the case when I created the csr with it. Do you have any idea what could cause that behaviour? Thanks
Does the password have special characters? Try using the CLI to run the “add ssl certkey” command.
I also had the same issue. But mine was solved after I downloaded the certificate as base64 from the windows CA. Each time I used the DER encorded, it gave the error invalid password during installing the certificate in the netscaler.
Hi Carl,
I’m seeing a potential issue when I generate a CSR for a wildcard on the appliance itself.
When I check the CSR using a decoder the common name has a backslash at the beginning of it:
\*.domain.com
Not sure if you have seen this before on version 12.
This is a known issue and has been fixed in 13.0.83+ or 12.1 63+
So, we would request you to upgrade the ADC to get this issue fixed.
Hi Karl, when I try to install the .pem or .cer certificate it keeps on circling in the Netscaler ADC with no further movement. What could be the reason ?
I tried reboot the ADC and tried multiple times but no luck. No error message, the install wizard page just circling after provide all details and when click on Install button. Please help me to fix the issue.
There have been bugs in various builds of ADC. I usually upload the certificate file to /nsconfig/ssl and then run the “add ssl certkey” command from CLI.
Great article!! I’m using this in my certificate renewal process for my Storefront servers which are in a load balanced service group on my Netscaler. The only thing I’m missing is a rollback plan.
When you update the certificate and it is rebound on all the servers, is the original certificate removed from the system? If I have to roll back, I’d like the original cert to be there to rebind.
I apologize if this is a repeat question.
On NetScaler, the old files are still there but the GUI configuration object points to new files instead of the old files. You’d have to change it back to the old files. You can go to System > Diagnostics > Running Configuration, search for the certificate name and see the old files.
Is there any disturbance in connection , if we renewed certificate with using manual method binding.
When you go to the SSL vServer and open the Server Certificate section, you’ll see the existing binding. You might be tempted to unbind it before binding the new one. However, if you click Add and select the new cert, it will replace the existing binding. If you do it this way, then I don’t think it will drop.
Hello Carl,
This is an excellent article. I would like to ask you a question. If current ssl certificate that is binded to virtual server is a pem file can I update it with pfx file? What i need to do? Thank you for your interest. Have a healthy days.
You should be able to. When updating the cert, browse to the PFX file. If you might see it asking you for the key file then just ignore it. Enter the PFX password.
I’m updating an existing pfx file, but it still has the field for the key. It’s filled in with the old pfx file name. If I change it to the new one it tells me it’s an invalid format. Do I just leave it alone, put in the new file location in the cert field, and put in my password?
I believe that’s correct. I sometimes have to try different combinations to get it to work. CLI is also an option.
Hello Carl,
I wonder if you came across this error upon removing a certificate from Traffic ManagementSeparatorSSLSeparatorSSL CertificateSeparatorServer Certificates
file or installing it even if its a different certificate.
ERROR: Problem in input PKCS12 file
even from SSH command line it gives the same error upon removing or adding a new certificate, graphically and thru commandline.
And I dont want to reboot as its production.
NetScaler NS12.1: Build 55.18.nc
Hi Carl
Are we able to use Microsoft CNG/ECDH certs? Struggling to import a PFX with a CNG key, issued by a MS CA, exported from Windows. (Goal is replacing the mgmt cert). RSA keys have always worked fine.
Carl,
First off I want to thank you for this amazing How to document you have provided. I was successful in a little over a year ago to step through the entire process to get up and running.
However what leads me to my post today is surrounding the Local Wildcard certificate I installed last year that has now expired. I have stepped through the steps to create a new local wildcard cert and updated the expired cert on the netscaler–>Traffic Management–>SSL–>Certificates–>Server Certificates . I add the cert to the IIS and bind it to the Default Website and restarted services. But when I try to access the storefront via a web browser internally on the network I receive a message that the cert is not trusted. Also when I try to open up the Director web page it too has a trust issue with the certificate and can not retrieve any data. I think I am missing something very simple possibly. Thanks for any help you can shed on the issue.
What CA signed the certificate? Is the CA root certificate installed on the client machines?
What browser? Firefox has different root certificates than the other browsers.
Carl,
My apologizes for not replying much sooner. I was monitoring a different thread and didn’t see this update for some time. Turned out my issue got resolved when I recreated the self signed wildcard cert using sha256. The other problem I discovered was I forgot to place the “.” after the wildcard character. *.xxxx.local Once I added that along with making the cert sha256 all worked great. Thanks so much for the fast response and sorry for my late reply.
Hi Carl, great work as always!
I’m using NetScaler ADC (NS12.1 54.13.nc)
I’m trying to use Client authentication certificates to verify the an external client identity when connecting to the Gateway interface. but keep getting “SSL error 47 peer sent a handshake failure alert”
– The Gateway Server certificate works fine using various cipher groups and TLS 1.1 > TLS1.3 using our own internal CA cert
– The Gateway has the correct CA specified (exported from our CA, imported and installed on the ADC)
– Enabling ‘Client Authentication’ on the gateway causes the Clients to select the correct certificate in their browser.
– LDAP auth work on the Gateway fine
– Users can logon to Storefront ok.
But i always get the “SSL error 47 peer sent a handshake failure alert” on the client Reciever and Workspace app
Any ideas what i might be missing in my config ?
Thanks in advance 🙂
I don’t think Receiver supports client certificates unless they are on a smart card. You might have to create a second Gateway for ICA Proxy that doesn’t have client certificates enabled.
Thanks Carl. Great detailed information that really helped me with this process.
I am configuring the NetScaler as Load Balance. But I don’t understand Convert .PFX Certificate to PEM Format. How to get the *.corp.com certificate? Certificate name with the NetScaler Name the same?
https://www.carlstalhood.com/storefront-3-5-basic-configuration/#sslcert has some info on how to use Windows to create a certificate. After the certificate is created, export it to a .pfx file.
Or you can skip Windows and instead use NetScaler to create the certificate. https://www.carlstalhood.com/certificates-citrix-adc-13/#csr
That’s my understanding:
When I configure StoreFront certificate need add load balance FQDN to Alternative Names of Certificate Properties.
Then export StoreFront certificate and add to load balance.
Am I right?
Yes.
don’t know why citrix had to make ssl certificate use such a rocket science. No wonder why they’re loosing their business.
amazing doco carl
Hello,
I installed a server cert with your method (To auto-convert a .pfx file (without private key encryption) but it does not appear in server cert section on NetScaler 12.
And when I tried to add it again I got this message -> already exist etc.
Do you have any idea?
Thank you in advance!
There have been various bugs in the UI for displaying certs. You can probably see it from the CLI at “show ssl certKey”
I’ll check it, and of course I’ll give you a feedback… and share the results… additional info->these certs were created by vmware and it works on NS11.1. But not on 12.
Thx Carl!
I could manage these certs with CLI… not else. Strane.
Thx for your help!
Hello Carl!
Thank you for great articles!
I have one question about SSL. One of imprted CA certificates shown in NS as expired. In details I can see as follow:
Valid From
Jan 14 08:41:47 2009 GMT
Valid To
Jan 14 08:42:2108 GMT
There is no “sec” value. “year” value has been moved to “sec”. So strange issue. Windows console shows it as 14 Jan 2108 11:42:12 and valid. Could you give me some advice to solve it please?
There have been several issues with how certificates are read in 11.1 and newer. You might have to open a support case so they can fix it.
Unfortunately I have a trial license only and no way to open a support case for. BTW thank you for your answer.