Navigation
In early 2024, NetScaler renamed Application Delivery Management (ADM) to NetScaler Console.
This post is for versions NetScaler Console 14.1 through Citrix ADM 13.1.
- Change Log
- Planning
- Import Appliance into vSphere
- Deployment Modes
- Add Instances
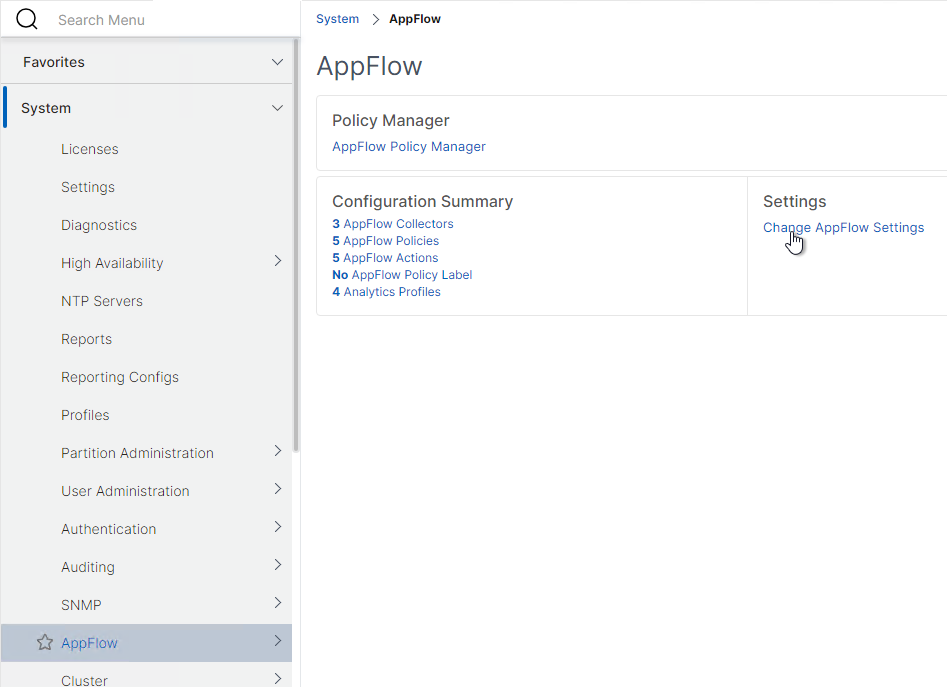
- Enable AppFlow / Insight / Analytics
- nsroot and nsrecover Password
- Management Certificate
- System Configuration
- Email Notification Server
- Authentication
- Analytics (Insight) Thresholds and Alerts
- SSL Certificate Expiration Notification (SSL Dashboard)
- Email Alerts (SNMP Traps)
- Director Integration
- Use NetScaler Console – HDX Insight, Gateway Insight, Security Insight
- Troubleshooting
- Upgrade NetScaler Console
💡 = Recently Updated
Change Log
- 2024 Dec 19 – updated some screenshots for new GUI in 14.1 build 38.53
- 2024 Feb 22 – renamed ADM to NetScaler Console
- 2023 Aug 25 – added info from CTX574664 ADM collector metric services port 5563 is down on VPXs
- 2023 Aug 18 – added info from CTX281388 Error Message “Network configuration change is not allowed in Citrix ADM HA setup” When Changing Network Settings in ADM.
- 2023 Mar 13 – Director Integration – changed user to only have HDX Insight permissions (h/t Artur Ogloza)
- 2022 Jun 9 – ADM Agents – 13.1 build 24 adds Agent Unreachable notifications
- 2021 Nov 27 – updated screenshots for version 13.1
Planning
Why NetScaler Console?
NetScaler Console 14.1 build 38.53 and newer have a new GUI.
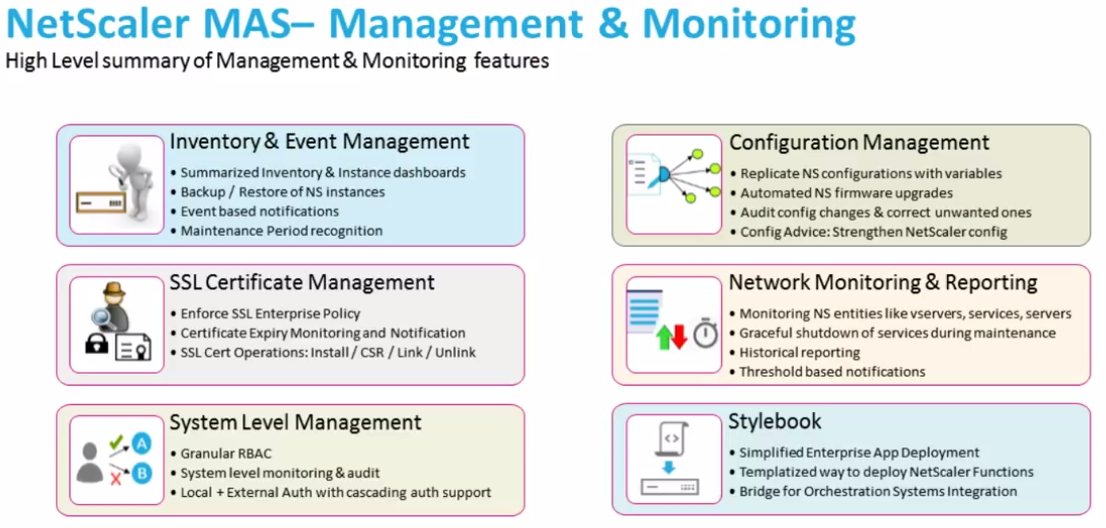
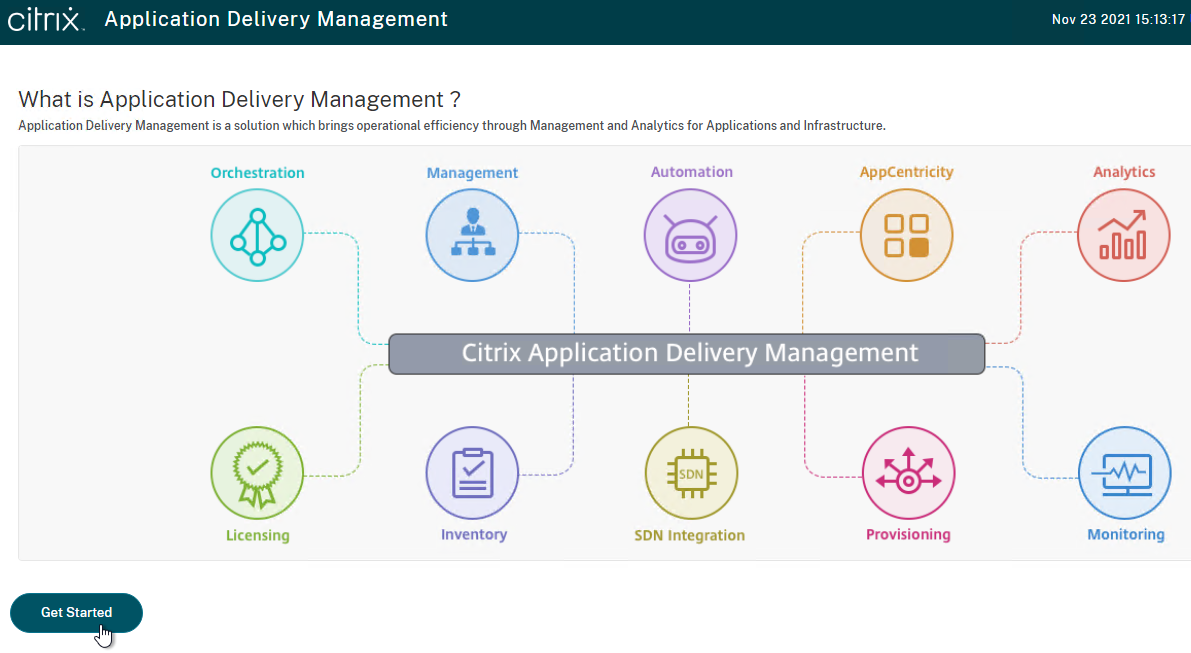
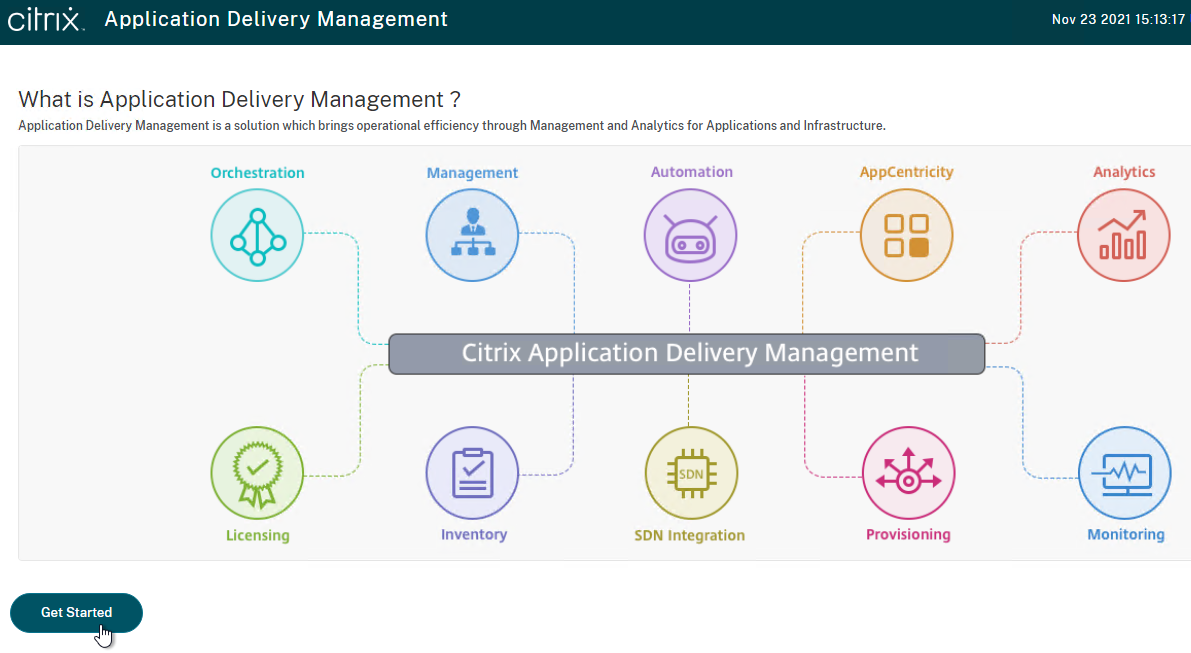
NetScaler Console (formerly ADM) enables every NetScaler administrator to achieve the following:
- Alert notifications – Receive email alerts whenever something goes down. For example, if a Load Balancing service goes down, you can receive an email alert.
- NetScaler Console can email you for any SNMP trap produced by any NetScaler ADC appliance.
- Automatically backup all NetScaler ADC instances.
- NetScaler Console can even transfer the backups to an external system, which is then backed up by a normal backup tool.
- SSL Certificate Expiration – Alert you when SSL certificates are about to expire.
- Show you all SSL certificates across all NetScaler ADC appliances.
- Configuration Record and Play – Use the Configuration Recorder to configure one NetScaler ADC appliance, and then push out the same configuration changes to additional appliances. This is the easiest method of managing NetScaler ADC appliances in multiple datacenters.
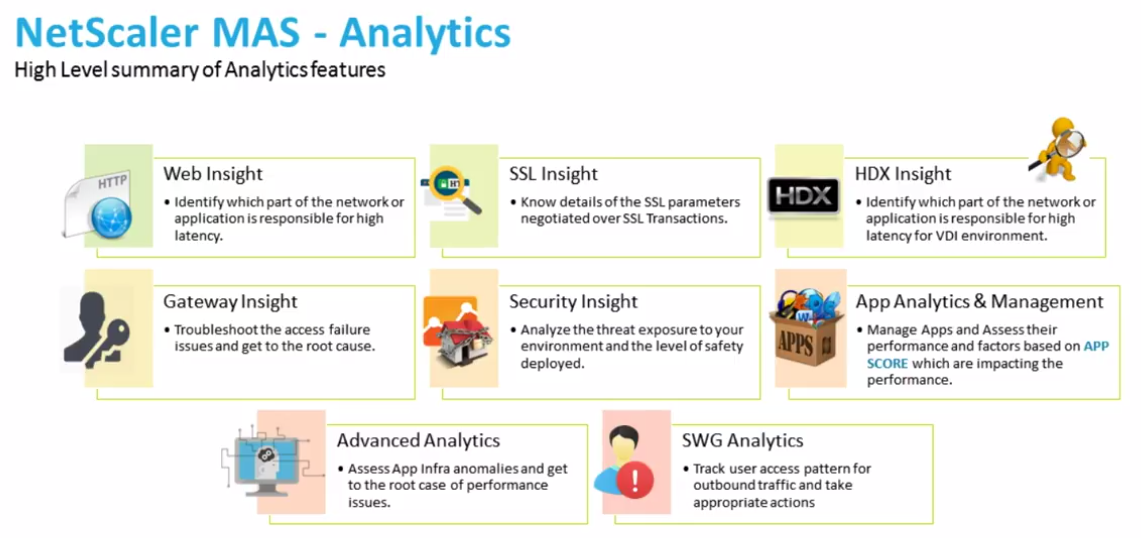
- AppFlow Reporting – Receive ICA AppFlow traffic from NetScaler Gateway and show it in graphs.
- Integrate NetScaler Console with Citrix Director so Help Desk can see the AppFlow data.
Everything listed above is completely free, so there’s no reason not to deploy NetScaler Console.
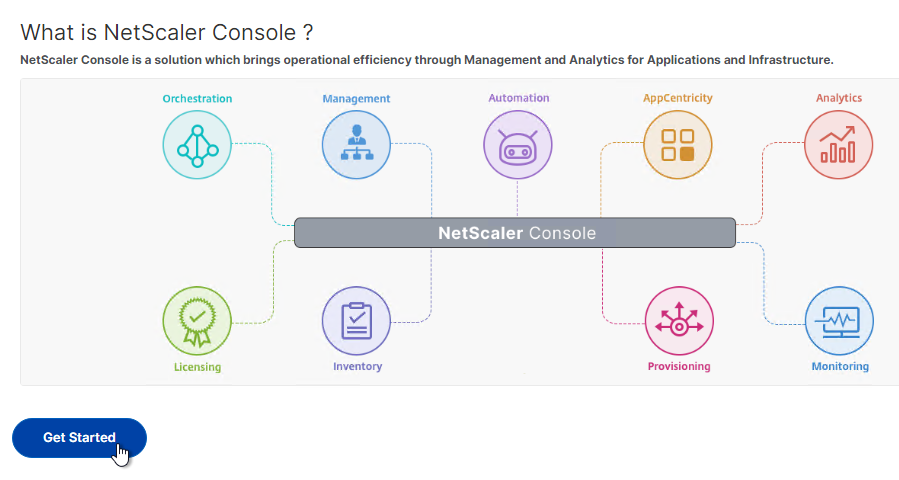
NetScaler Console Overview
For an overview of NetScaler Console, see Citrix’s YouTube video Citrix NetScaler MAS: Application visibility and control in the cloud.
Citrix Tech Zone Citrix Application Delivery Management (ADM) Overview Cheat Sheet
Cloud vs on-prem
NetScaler Console is available both on-premises and as a Cloud Service.
The Cloud version of NetScaler Console has new features that are not available in the on-premises version of NetScaler Console.
For the Cloud Service, you import a NetScaler Console Agent appliance to an on-prem hypervisor or deploy a NetScaler Console Agent to AWS or Azure. The NetScaler Console Agent is the proxy between the Cloud Service and the on-prem (or cloud hosted) NetScaler ADC appliances. For more info on the NetScaler Console Cloud Service, see the following:
- Demo: Citrix NetScaler Management and Analytics Service – YouTube video
- Many NetScaler Console features are supported in the Cloud Service.
- The Cloud Service uses subscription licensing.
- Citrix Application Delivery Management Service at NetScaler Docs
- George Spiers NetScaler Management and Analytics Service
The rest of this article focuses on the on-premises version, but much of it also applies to the Cloud Service.
On-premises NetScaler Console Licensing:
- Instance management is free (unlimited). This includes Configuration Jobs, Instance Backups, Network Functions/Reporting. Basically everything in the Infrastructure node is free.
- Analytics and Application monitoring are free in NetScaler Console build 21 and newer.
NetScaler Console version – The version/build of NetScaler Console must be the same or newer than the version/build of the NetScaler ADC appliances being monitored. NetScaler Console 14.1 can monitor many NetScaler ADC appliance versions including version 11.1, version 12.1, version 13.0, version 13.1, and version 14.1.
HDX Insight
See CTX239748 for a list of HDX Insight Quality Improvements in Citrix Gateway 12.1 and newer. These include:
- NSAP protocol for reduced performance impact on NetScaler ADC
- EDT support
HDX Insight Requirements (aka AppFlow Analytics for Citrix ICA traffic):
- Your NetScaler ADC appliance must be running Advanced Edition or Premium Edition.
- For EDT (UDP-based ICA), NetScaler ADC must be 12.1 build 49 or newer.
- AppFlow statistics are only generated when ICA traffic flows through a Citrix Gateway. Internally, when a user clicks an icon from StoreFront, an ICA connection is established directly from Workspace app to the VDA, thus bypassing the internal NetScaler Gateway. Here are some methods of getting ICA traffic to flow through an internal NetScaler ADC:
- Implement NetScaler Gateway ICA Proxy (SSL) internally.
- However, Single Sign-on (pass-through authentication) has special considerations for Citrix Gateway:
- In the newest Workspace app, you can set the client-side GPO setting to enable Single Sign-on through Gateway.
- Or, use SSL ICA Proxy without authenticating at Citrix Gateway, see CTX200129 – How to Force Connections through NetScaler Gateway Using Optimal Gateways Feature of StoreFront.
- However, Single Sign-on (pass-through authentication) has special considerations for Citrix Gateway:
- Route ICA traffic (TCP/UDP 1494 and TCP/UDP 2598) through a NetScaler ADC SNIP, and NetScaler ADC routes it to the VDAs.
- NetScaler ADC can proxy ICA traffic through a SOCKS protocol Cache Redirection Virtual Server.
- Advantages: no need to authenticate at Citrix Gateway, and no routing changes. See Citrix Blog Post Gathering HDX Insight Analytics for LAN Users with NetScaler Using SOCKS for more information.
- NetScaler Docs Enabling HDX Insight Data Collection details additional ICA routing/proxy considerations – Transparent Mode, Citrix Gateway Single-Hop and Double-Hop, LAN User Mode (NetScaler ADC as SOCKS Proxy), Multi-Hop (NetScaler ADC connection chaining)
- Implement NetScaler Gateway ICA Proxy (SSL) internally.
- A new Workspace app Virtual Channel named NetScaler App Experience or NSAP can dramatically reduce the CPU needed on the NetScaler ADC to process AppFlow. Details at Citrix Blog Post HDX Insight 2.0.
- For ICA round trip time calculations, in a Citrix Policy, enable the following settings:
- ICA > End User Monitoring > ICA Round Trip Calculation
- ICA > End User Monitoring > ICA Round Trip Calculation Interval
- ICA > End User Monitoring > ICA Round Trip Calculation for Idle Connections
- Citrix CTX215130 HDX Insight Diagnostics and Troubleshooting Guide contains the following contents:
- Introduction
- Prerequisites for Configuring HDX Insight
- Troubleshooting
- Issues Related to ICA parsing
- Error Counter details
- Checklist before Contacting Citrix Technical Support
- Information to collect before Contacting Citrix Technical support
- Known Issues
Citrix CTX204274 How ICA RTT is calculated on NetScaler Insight: ICA RTT constitutes the actual application delay. ICA_RTT = 1 + 2 + 3 + 4 +5 +6:
- Client OS introduced delay
- Client to NS introduced network delay (Wan Latency)
- NS introduced delay in processing client to NS traffic (Client Side Device Latency)
- NS introduced delay in processing NS to Server (XA/XD) traffic (Server Side Device Latency)
- NS to Server network delay (DC Latency)
- Server (XA/XD) OS introduced delay (Host Delay)
Multi-Datacenter Deployment Architecture
In a main datacenter, import two NetScaler Console appliances into the same subnet and configure them as an HA pair with a Floating IP address.
- Documentation at Configure high availability deployment at NetScaler Docs and will be detailed later in this article.
In a DR datacenter, import a DR node NetScaler Console appliance and configure it to replicate with the main datacenter.
- Note: DR node requires a Floating IP, which requires NetScaler Console HA to be configured in the main datacenter.
- Documentation at Configure disaster recovery for high availability at NetScaler Docs and will be detailed later in this article.
For NetScaler ADC appliances in additional datacenters, import two NetScaler Console Agent appliances into each datacenter. Remote NetScaler ADC instances are discovered and managed through remote NetScaler Console agents.
- The virtual appliance for NetScaler Console Agent is different than the normal NetScaler Console appliance.
- Documentation at Configure on-prem agents for multisite deployment at NetScaler Docs and will be detailed later in this post.
Import NetScaler Console Appliance
If you are upgrading an existing NetScaler Console or ADM, skip to the Upgrade section.
There are two different NetScaler Console appliances:
- ADM appliance for the main datacenter, including High Availability, and for the DR node.
- ADM Agent appliance for remote datacenters
To import a NetScaler Console Appliance into vSphere, do the following:
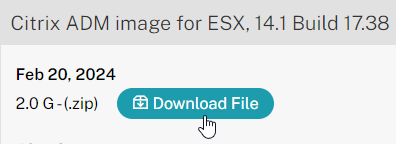
- Download Citrix ADM Image for ESX.
- The download page for NetScaler Console has two different images: one called ADM Image, and one called ADM Agent Image. The first image should be the non-agent image.
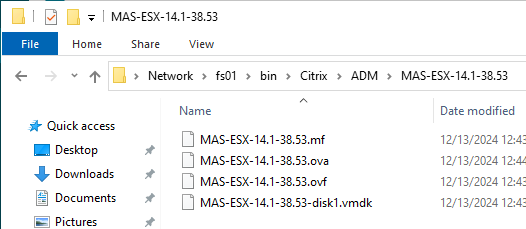
- Extract the downloaded .zip file for the non-agent image (MAS-ESX-14.1).
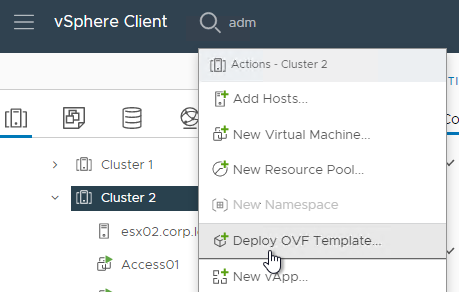
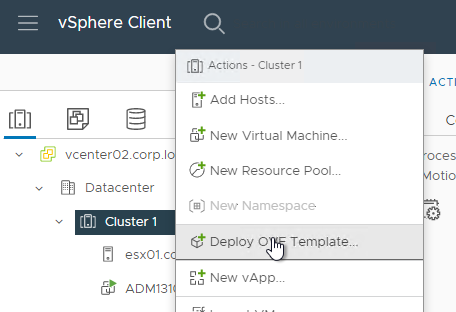
- In vSphere Web Client, right-click a cluster, and click Deploy OVF Template.
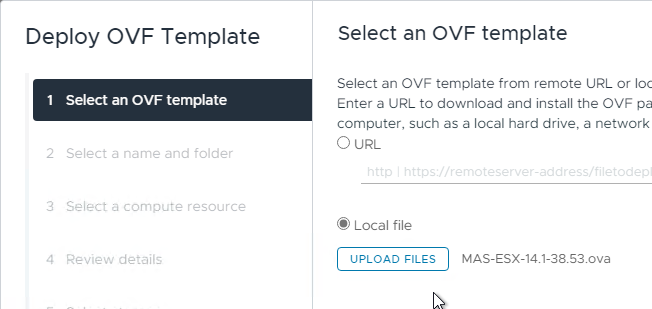
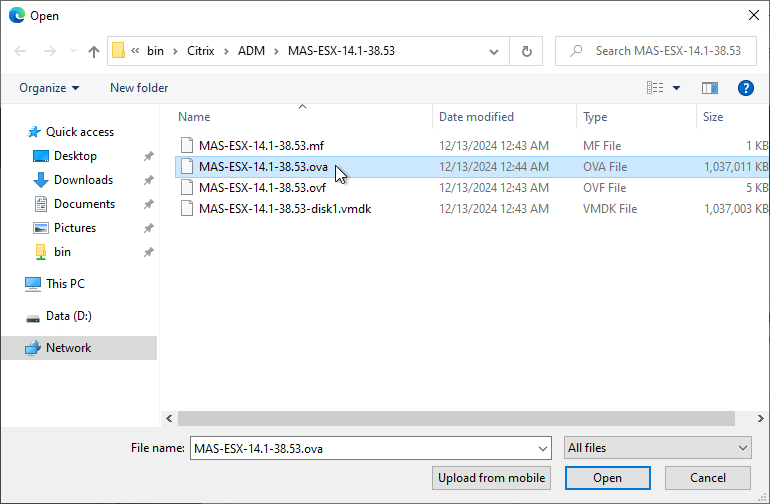
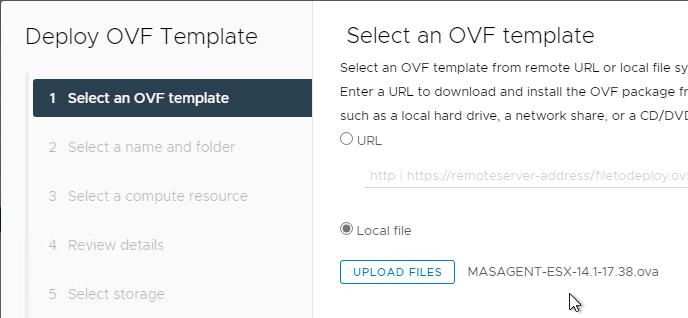
- In the Select an OVF Template page, select Local file and browse to the NetScaler Console .ovf files. If .ova file is available, then only select the one .ova file. Otherwise, select all three files (.ovf, .mf, and .vmdk). Click Next.
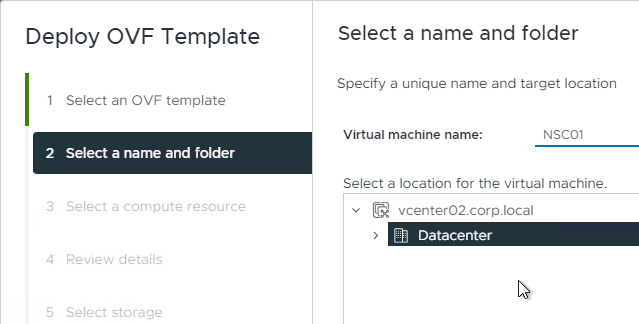
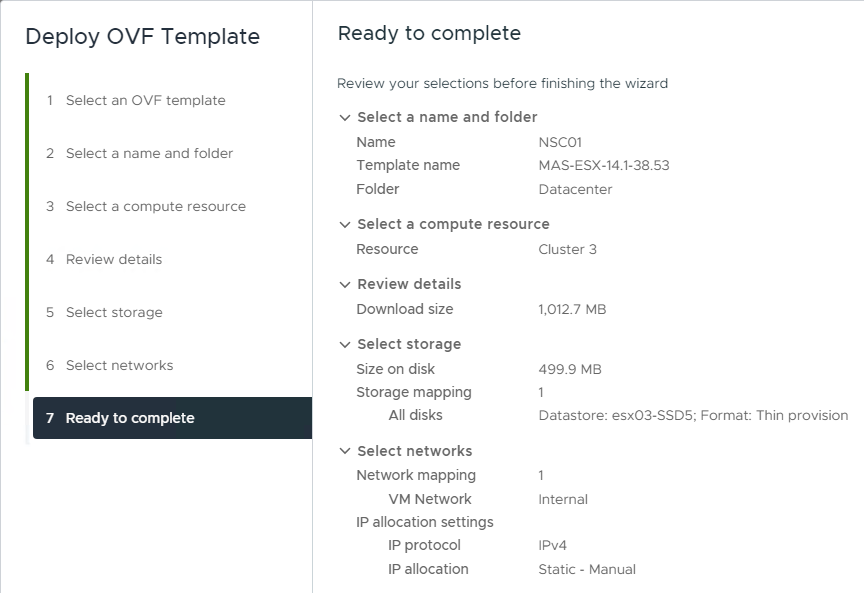
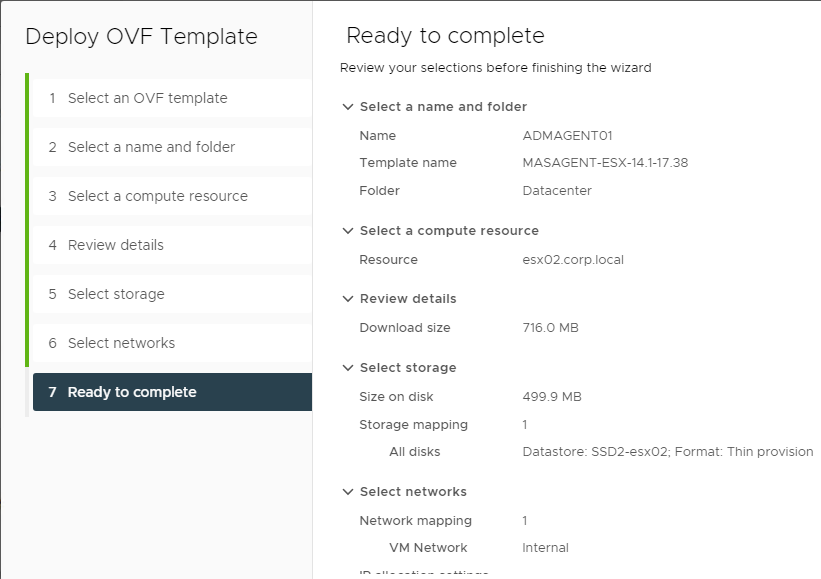
- In the Select name and folder page, enter a name for the virtual machine, and select an inventory folder. Then click Next.
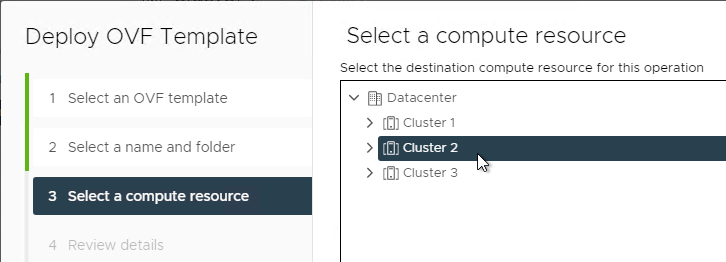
- In the Select a resource page, select a cluster or resource pool, and click Next.
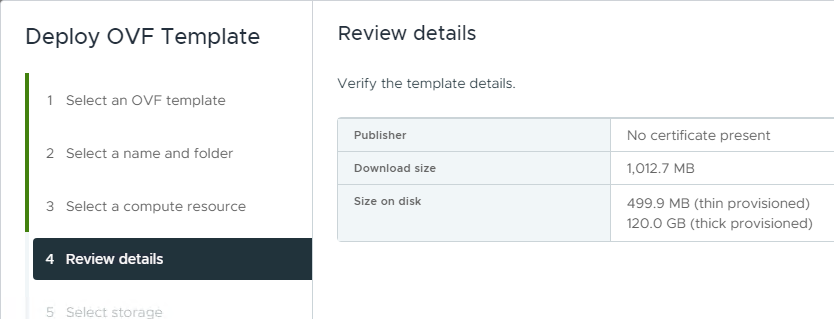
- In the Review details page, click Next.
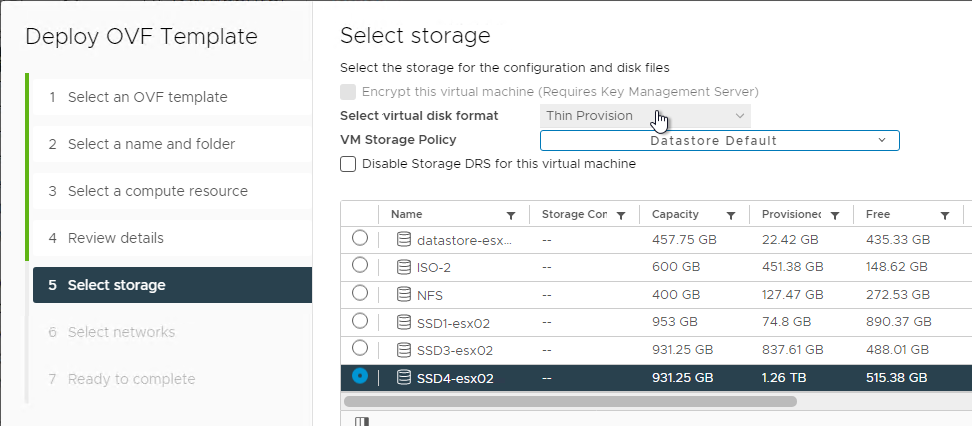
- In the Select storage page, select a datastore. Due to high IOPS requirement, SSD is recommended.
- Change the virtual disk format to Thin Provision. Click Next.
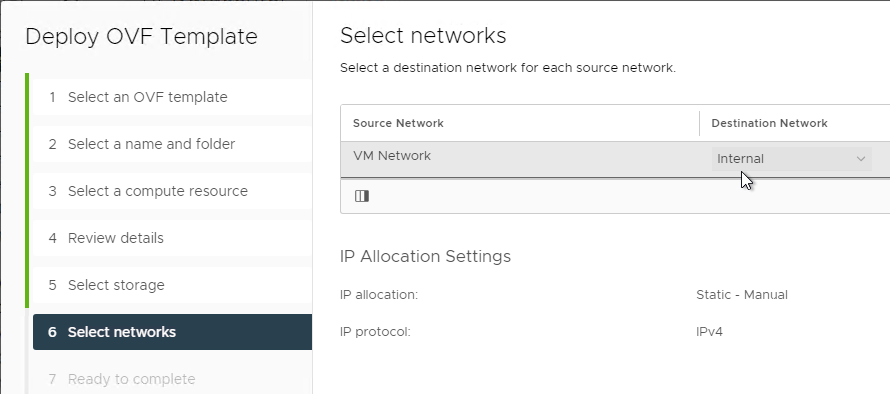
- In the Select networks page, choose a valid port group, and click Finish.
- In the Ready to Complete page, click Finish.
Appliance Hardware Configuration
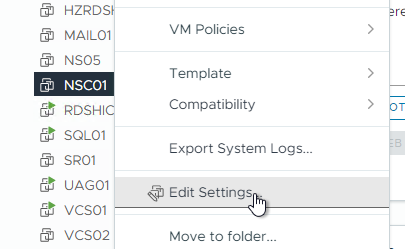
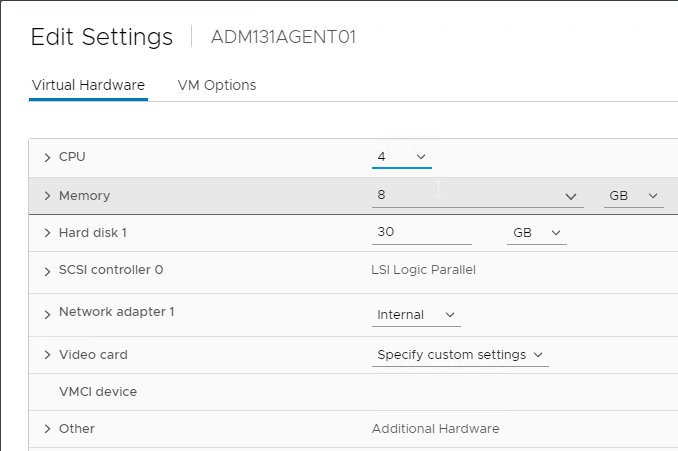
- Before powering on the appliance, you can review its hardware specs. Right-click the NetScaler Console virtual machine and click Edit Settings.
- Review the specs. NetScaler Docs NetScaler Console on VMware ESXi recommends 8 vCPUs and 32 GB RAM.
- You can add a second hard disk at this time.
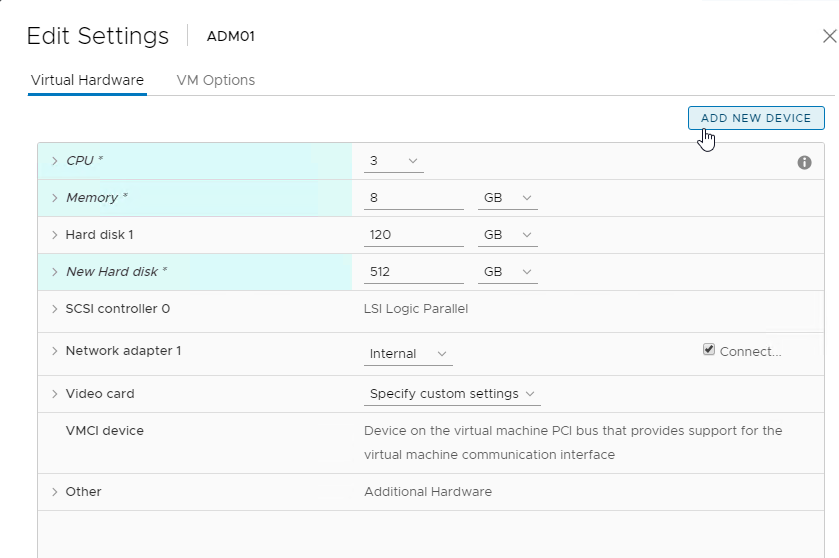
- NetScaler Docs Attach an additional disk to NetScaler Console says that an additional disk must be added before initial deployment.
- Use the NetScaler Console storage calculator to determine the recommended size of the disk. Ask your Citrix Partner for the tool.
- The new disk must be larger than 120 GB.
- The new disk can be larger than 2 TB.
- The new disk can be grown later, and
/mps/DiskPartitionTool.pycan resize the partition, but only up to 2 TB. If you need more than 2 TB, the initial disk should be larger than 2 TB.
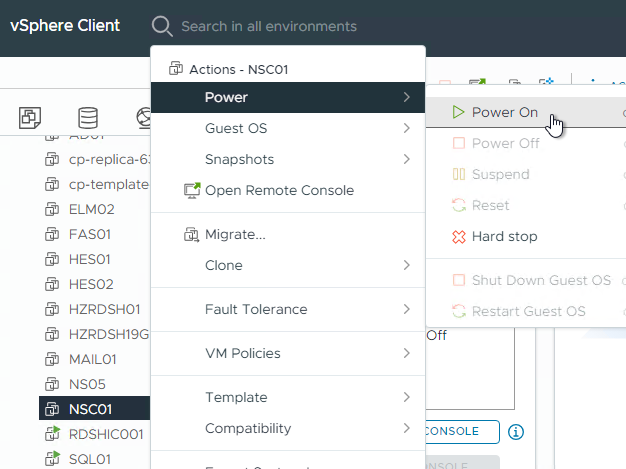
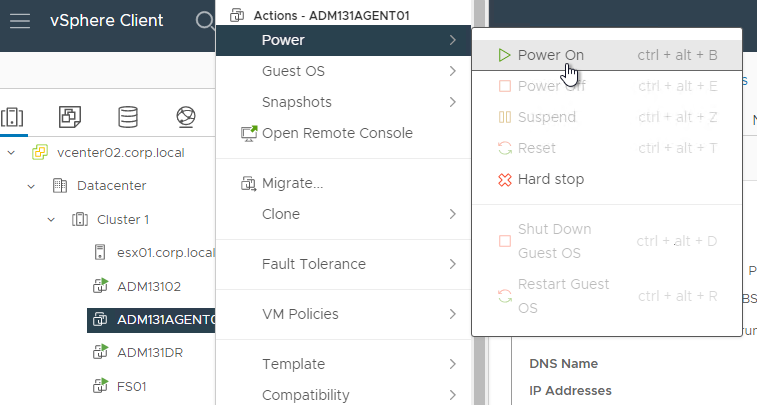
- Power on the Virtual Machine.
Appliance IP Address Configuration
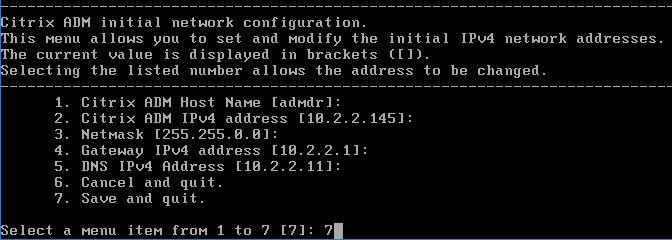
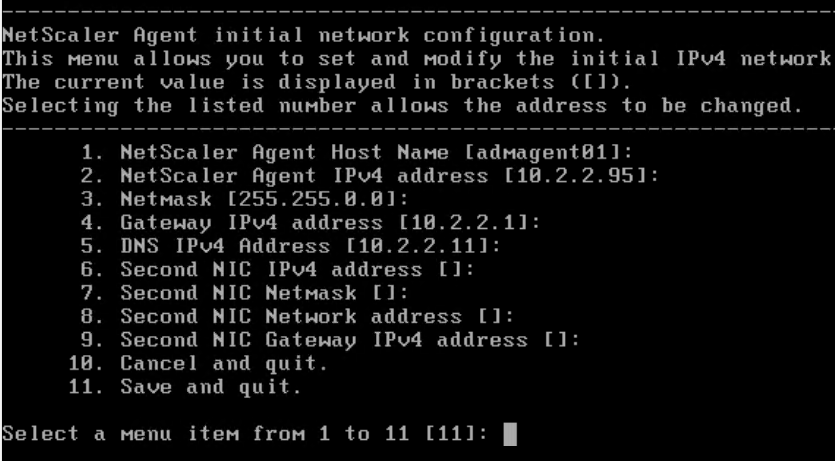
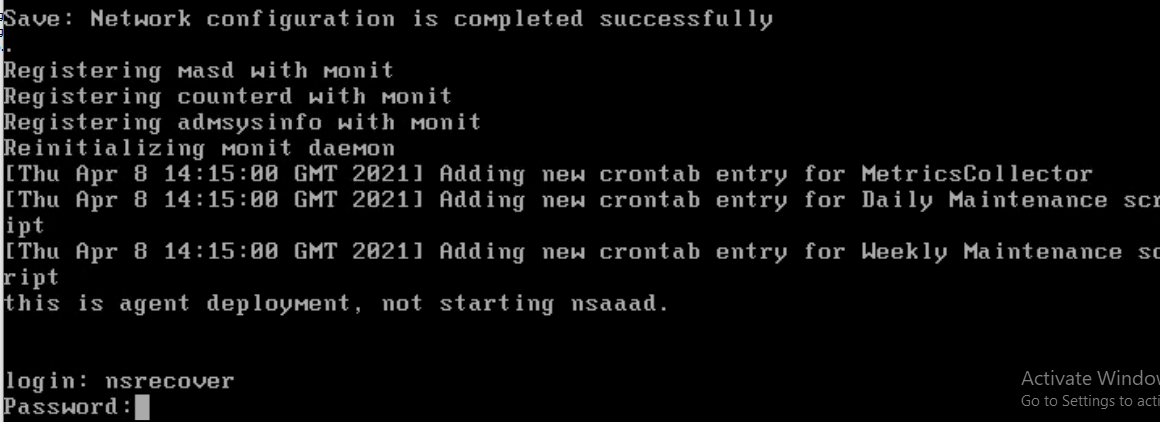
- Open the console of the virtual machine.
- Configure IP address information.
- Enter 7 when done.
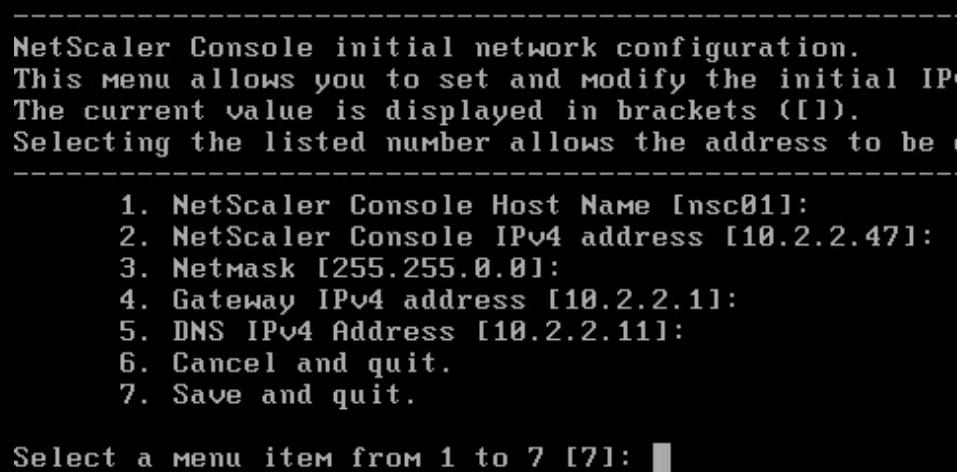
- It takes several minutes for the GUI login to start working.
Second Disk
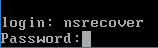
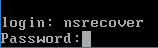
- SSH to the appliance and login as nsrecover/nsroot.
- Enter
/mps/DiskPartitionTool.py
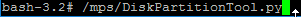
- The Disk Partition Tool is documented at Attach an additional disk to NetScaler Console at NetScaler Docs.
- Enter
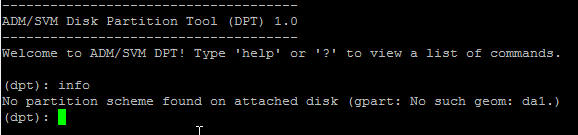
infoto see that there are no existing partitions on the second disk.
- Enter
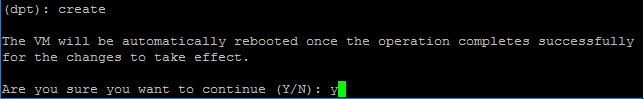
createto create partitions on the second disk. A reboot is required.
- During the reboot, the database is moved to the second disk.
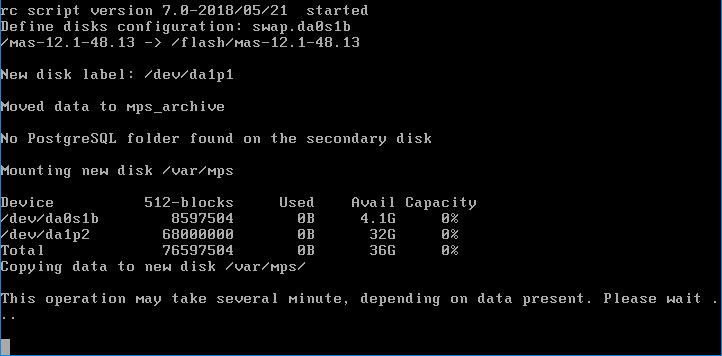
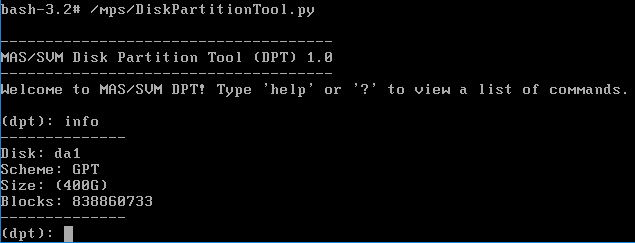
- After the reboot, the Disk Partition Tool info command shows the partition on the second disk.
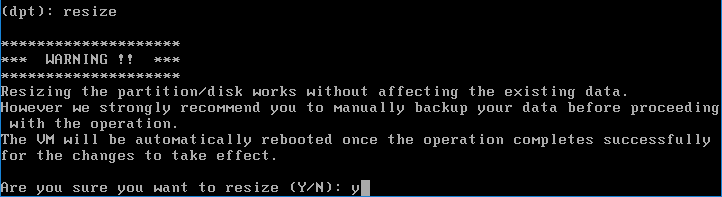
- If you need to increase the size of the disk, reboot the NetScaler Console appliance so it detects the larger size. Then use the Disk Partition Tool
resizecommand.
Deployment Modes
HA Pair in the Main Datacenter
If NetScaler Console 14.1 build 17 or newer, HA is no longer configured from the CLI. Instead, use the GUI.
- Latency to the HA node must not exceed 10 ms.
- The HA nodes must be on the same subnet.
- Import a second NetScaler Console appliance.
- If you added a second disk to the first NetScaler Console appliance, then you must add the same size second disk to the second NetScaler Console appliance.
- Configure the new node’s IP address.
- SSH to the second appliance, login as nsrecover/nsroot, and run the Disk Partition tool.
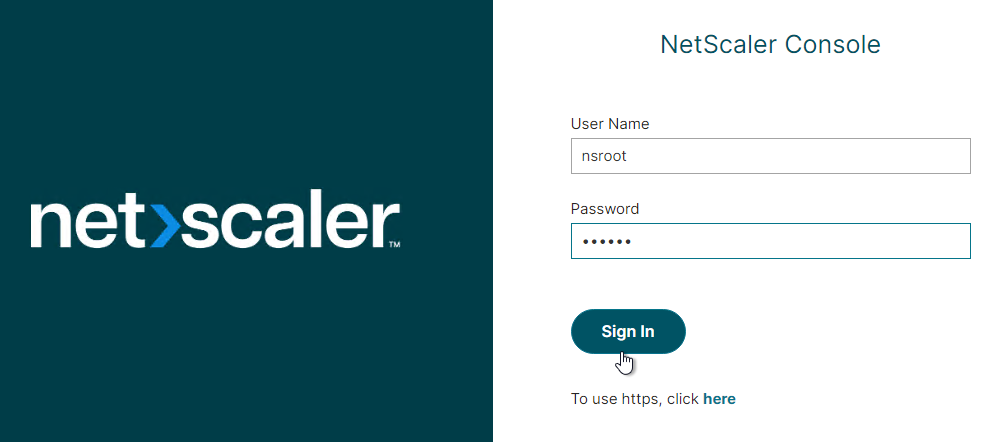
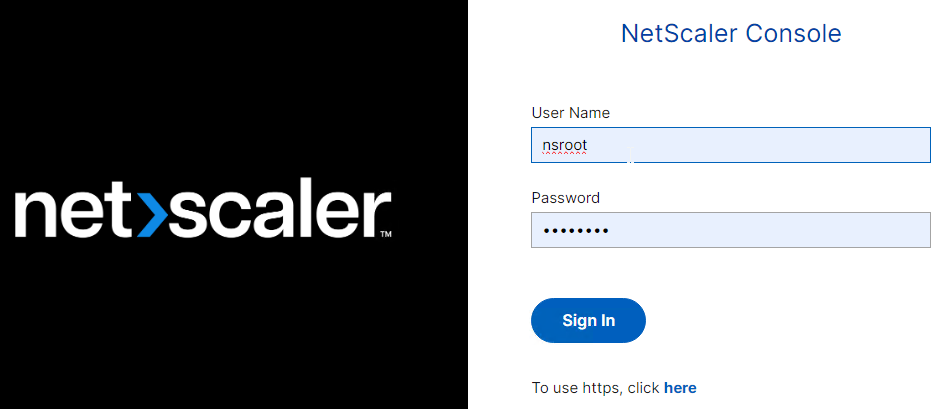
- Point your browser using https to the first NetScaler Console IP address. Note: After configuring the appliance IP, it takes several minutes for the GUI login to start working.
- Login using nsroot/nsroot credentials.
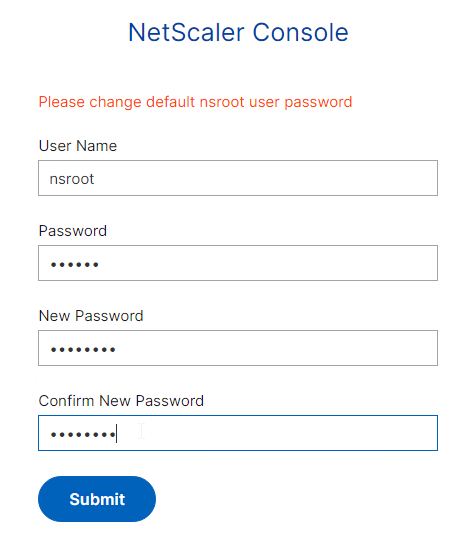
- Change the nsroot password when prompted. Login to the second node and also change its password.
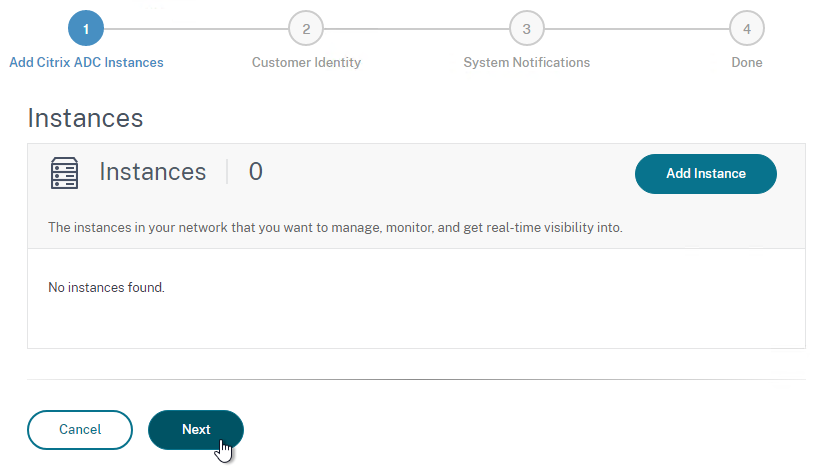
- Click Get Started.
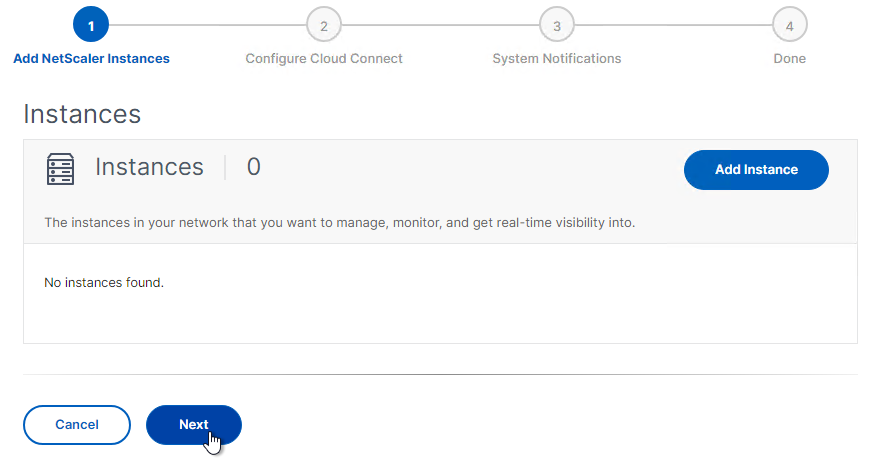
- In the Instances page, click Next.
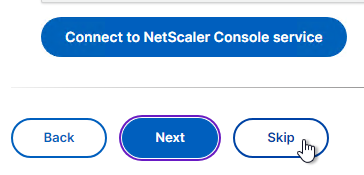
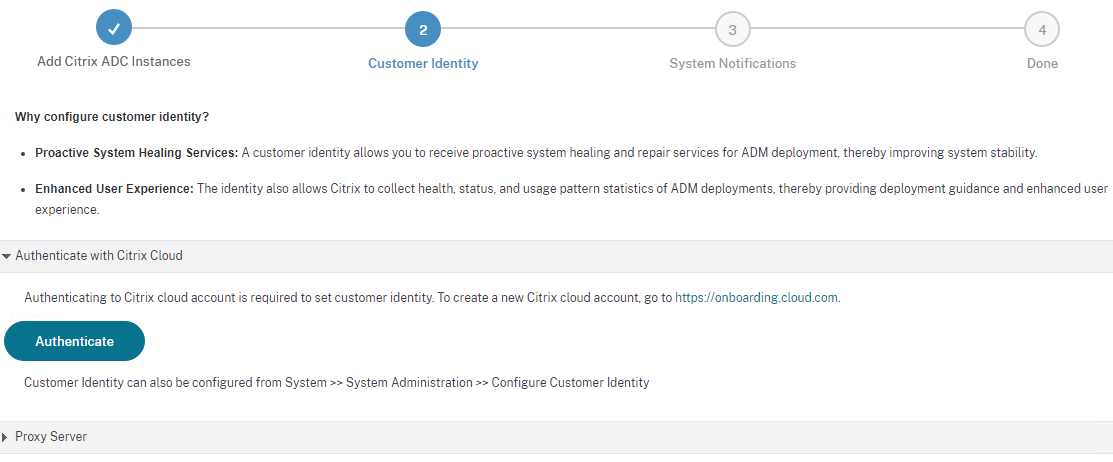
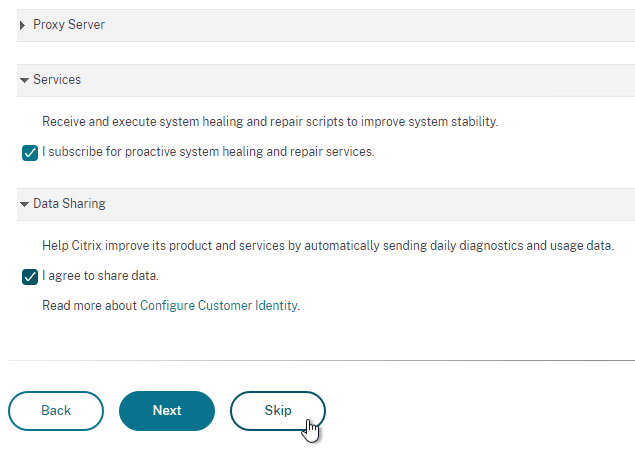
- In the Connect to NetScaler Console Service page, click Skip.
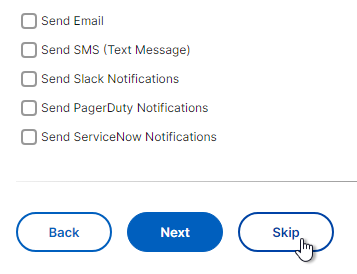
- In the Notifications page, click Skip.
- Click Finish.
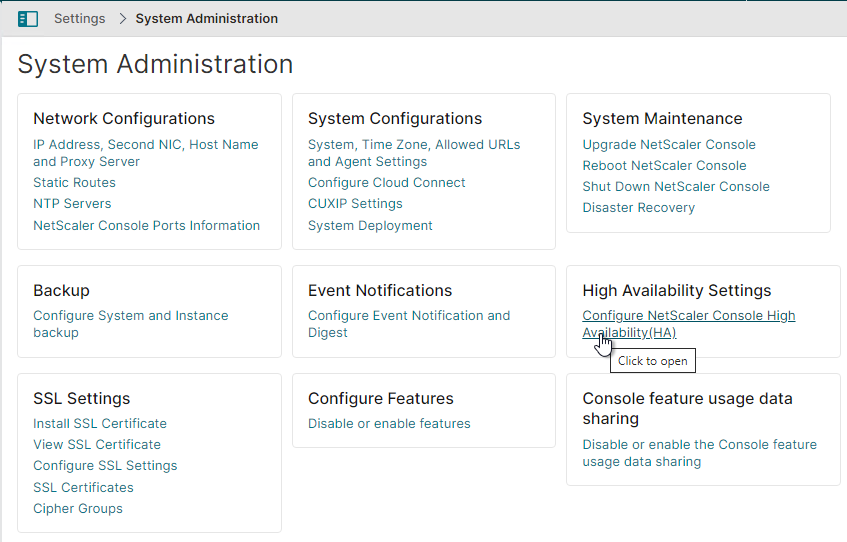
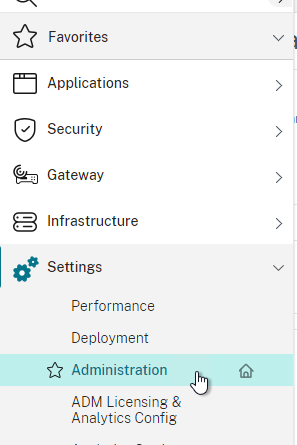
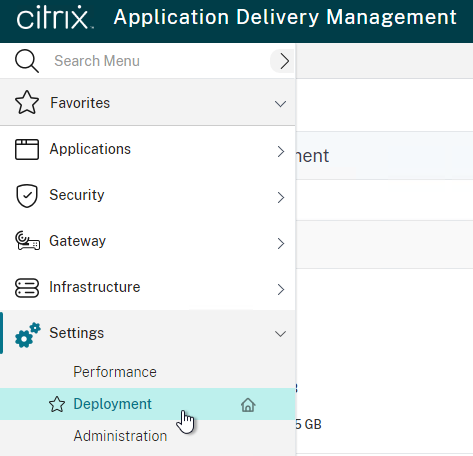
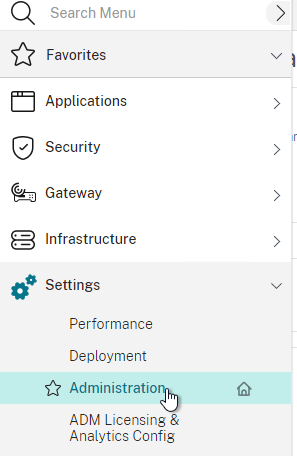
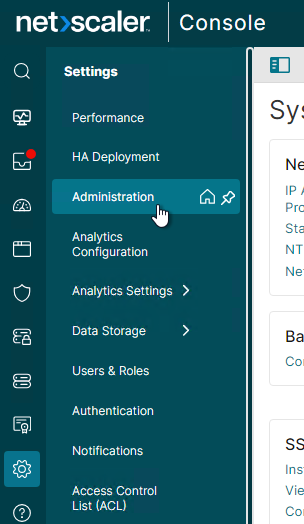
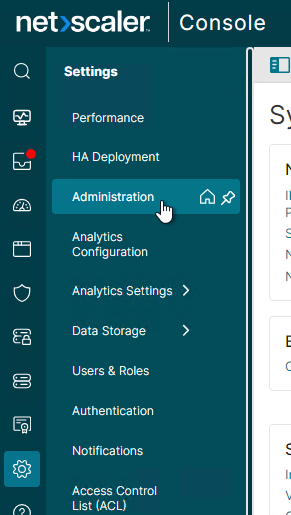
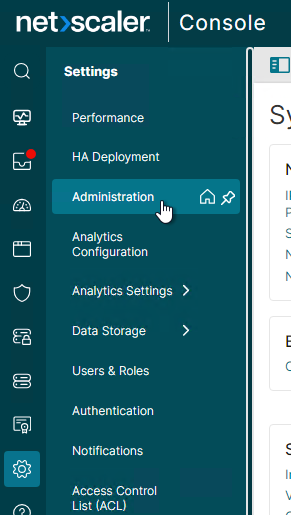
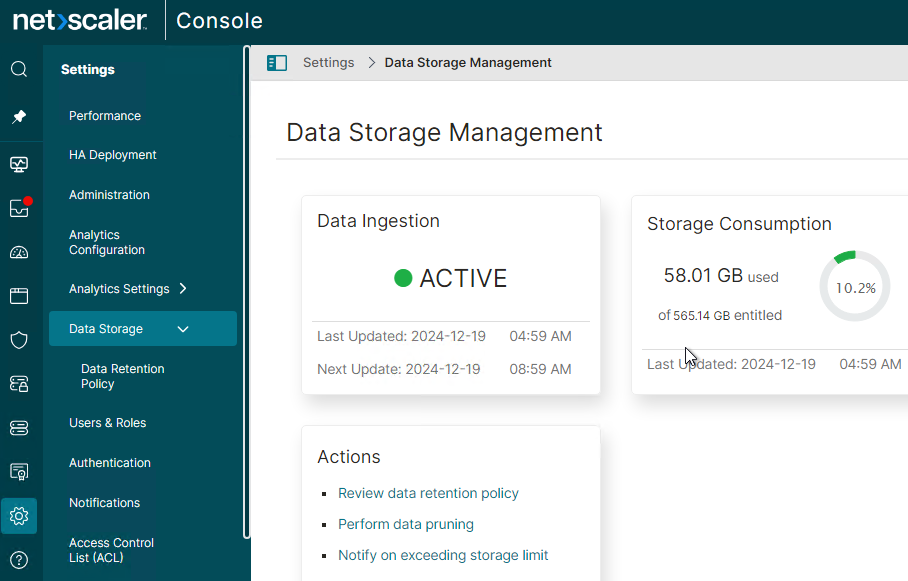
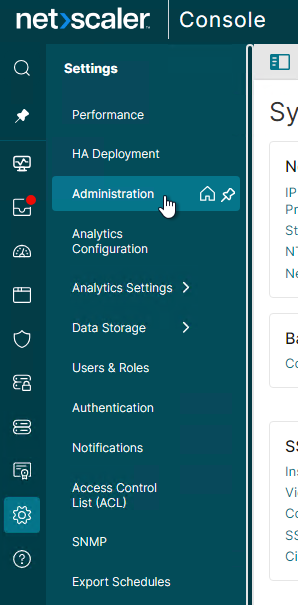
- In the left menu, expand Settings and click Administration.
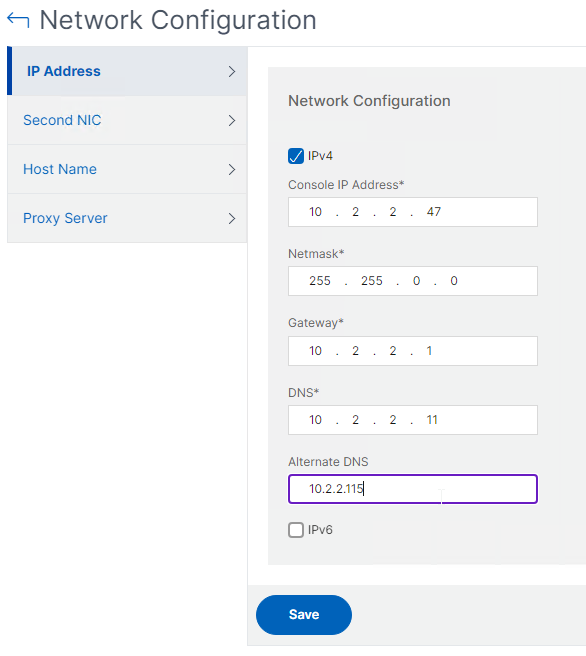
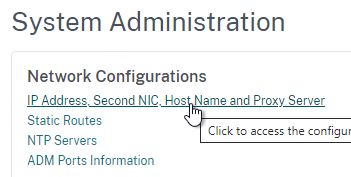
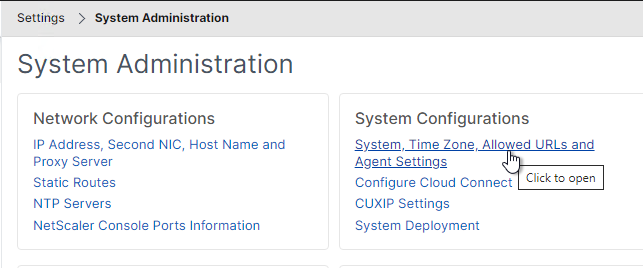
- On the right, click IP Address, Second NIC, Host Name and Proxy Server.
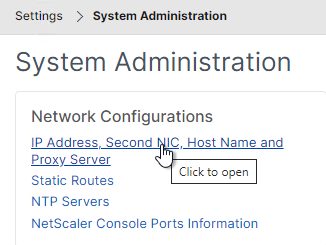
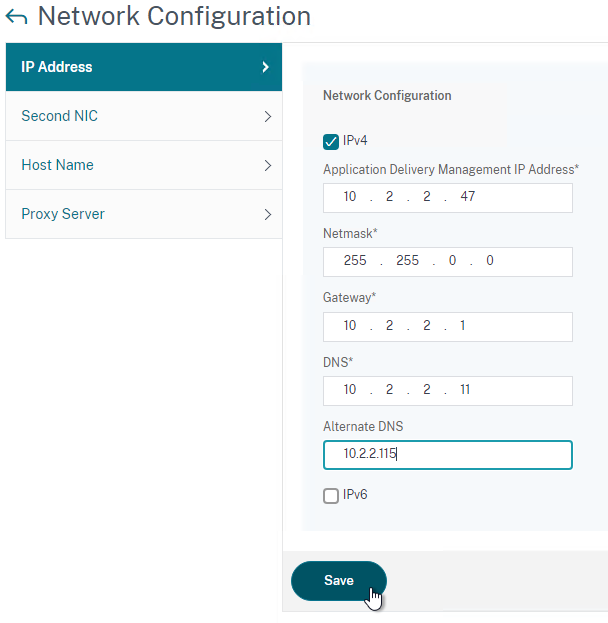
- Configure the Alternate DNS and click Save. You can only configure this before you create the HA pair. Repeat on both nodes.
- On the right, click Configure NetScaler Console High Availability (HA).
- Enter the IP of the second NetScaler Console appliance.
- Enter a new IP that will float between the two nodes. Click Configure.
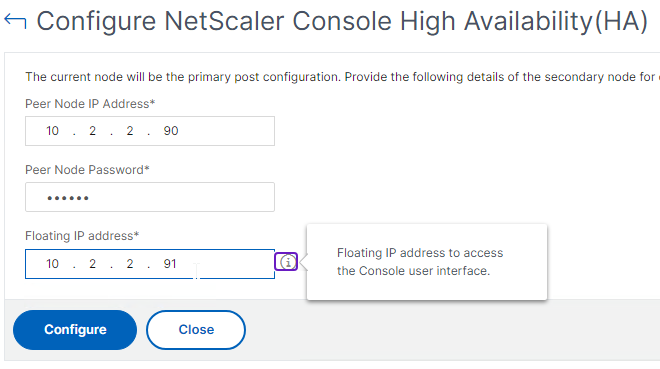
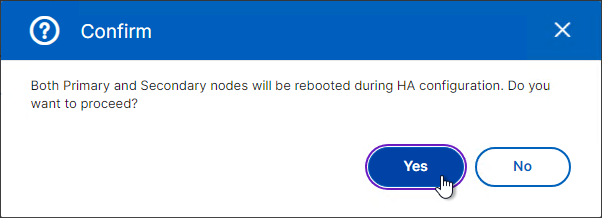
- Click Yes to reboot.
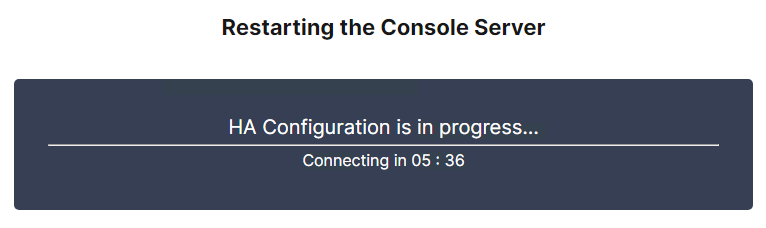
- It will take several minutes to configure HA.
- After the reboot, log into the floating IP.
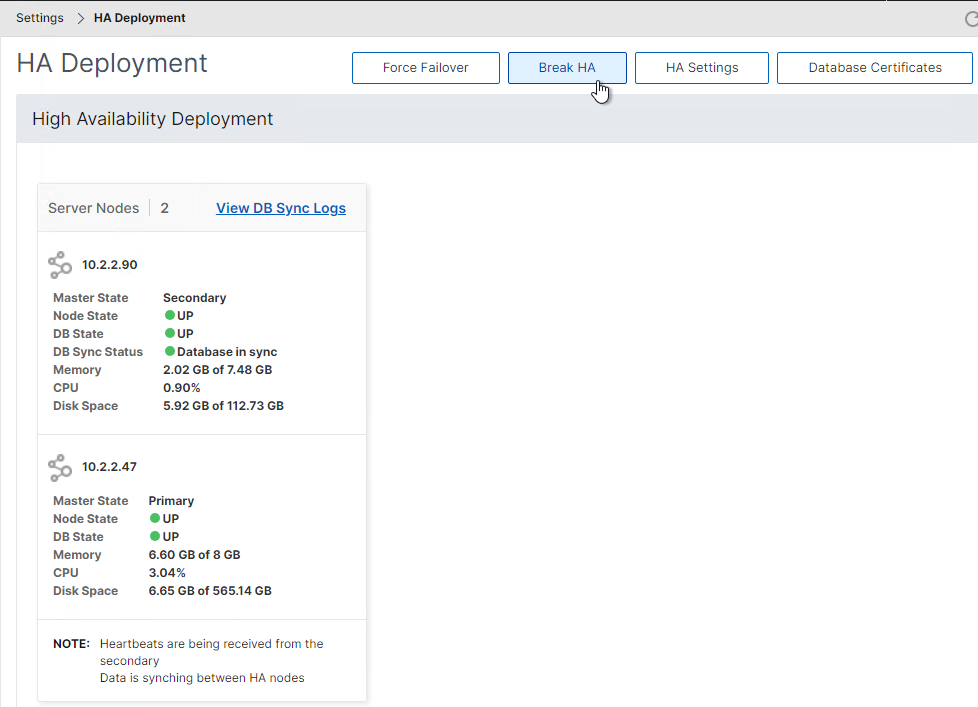
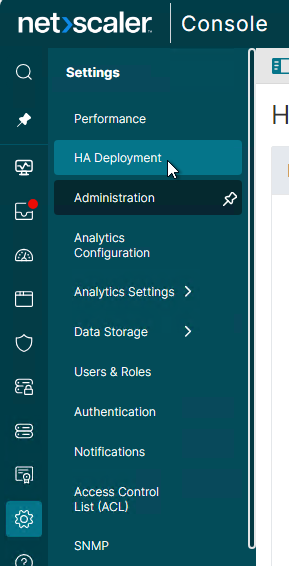
- In the left menu, expand Settings and click HA Deployment.
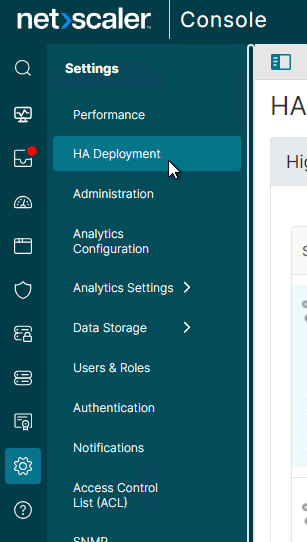
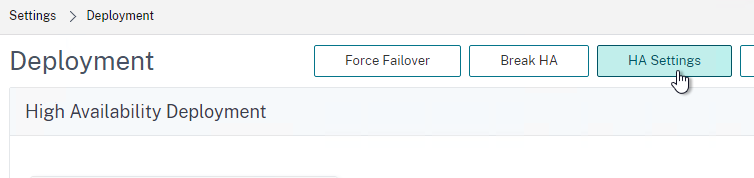
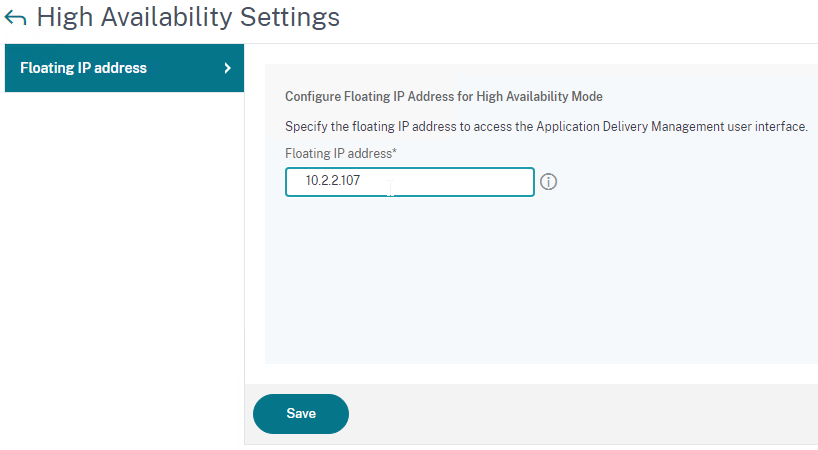
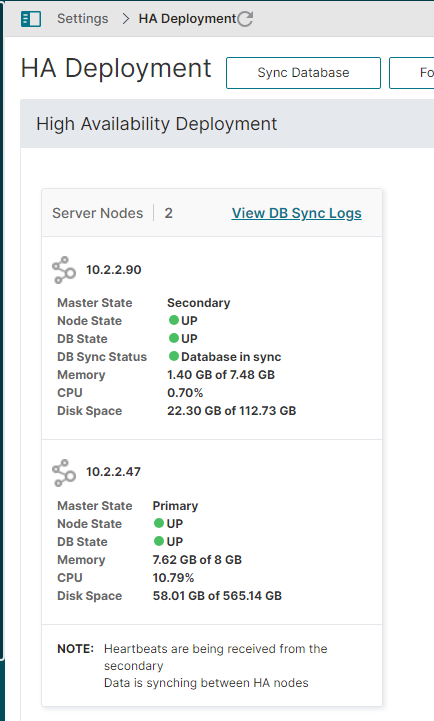
- You can view the status of the HA pair and fix the database sync if it is broken. You can Break HA, Force Failover, or change the Floating IP (in HA Settings).
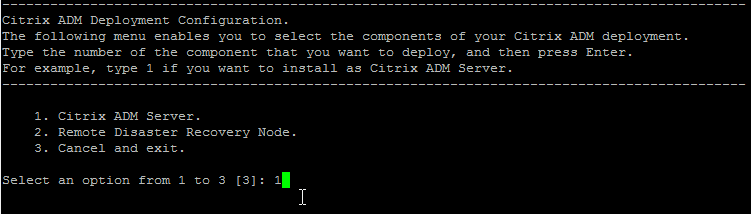
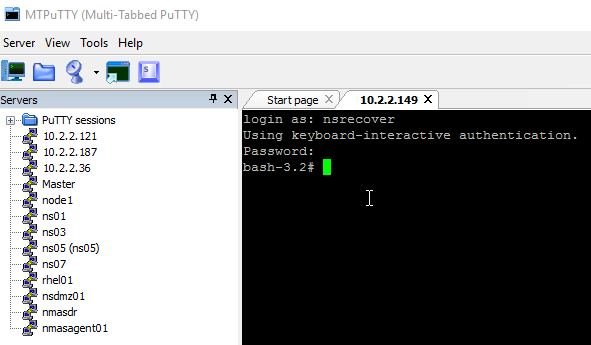
If this is older Citrix ADM, on the First Node, do the following:
- SSH to the first node and login as nsrecover/nsroot.
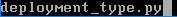
- Enter deployment_type.py.
- Enter 1 for NetScaler Console Server.
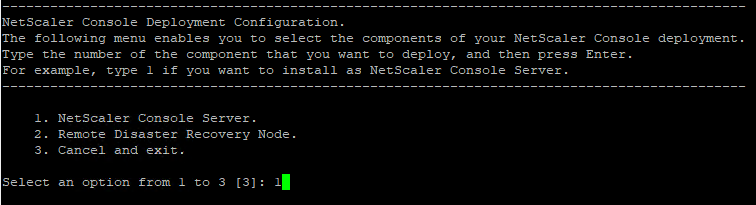
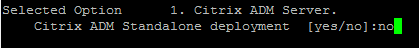
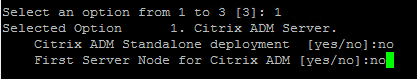
- Enter no when prompted for NetScaler Console Standalone deployment.
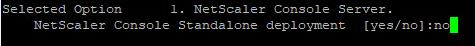
- For the First Server Node prompt, enter yes.
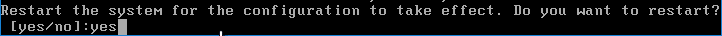
- Enter yes to Restart the system.
Older Citrix ADM Second Node:
- Import another ADM appliance to the same subnet and configure an IP address.
- Latency to the HA node must not exceed 10 ms.
- The HA nodes must be on the same subnet.
- If you added a second disk to the first ADM appliance, then you must add the same size second disk to the second ADM appliance.
- Configure the new node’s IP address.
- SSH to the second appliance, login as nsrecover/nsroot, and run the Disk Partition tool.
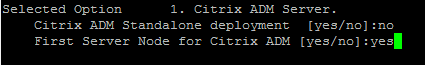
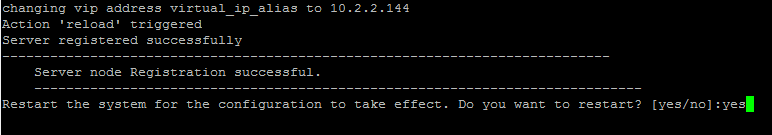
- SSH to the second appliance, login as nsrecover/nsroot, and run deployment_type.py.
- Enter 1 for Citrix ADM Server.
- Enter no when prompted for Citrix ADM Standalone deployment.
- Enter no when prompted is this is First Server Node.
- Enter the IP address of the first ADM node.
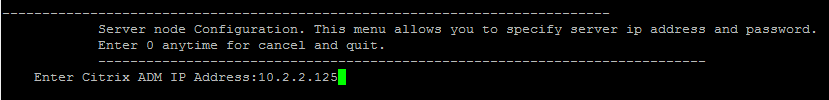
- Enter the nsroot password of the first node. The default password is nsroot.
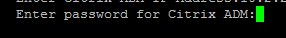
- Enter a new Floating IP address.
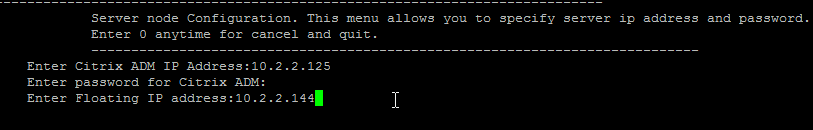
- Enter yes to restart the system.
Older Citrix ADM Get Started:
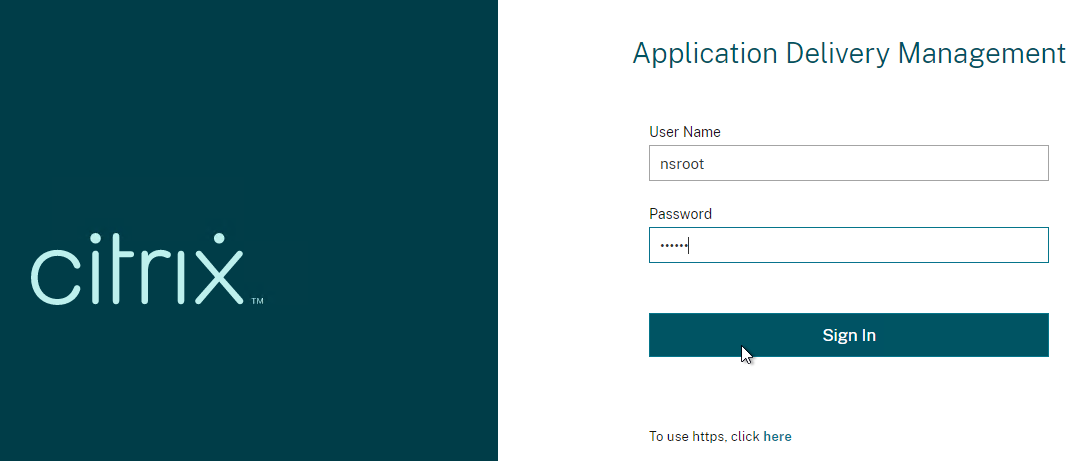
- Use a browser to log into the first ADM appliance as nsroot/nsroot.
- Logging in to NetScaler ADM might show you the Get Started wizard. If you don’t see this wizard, then skip to the next section.
- In the Add NetScaler Instances page, you can Add Instance now, or just click Next and add instances later.
- In the Customer Identity page, you can login to Citrix Cloud, configure data sharing, or click Skip to do it later.
- In the System Notifications page, you can configure Email notifications now, or click Skip and do it later.
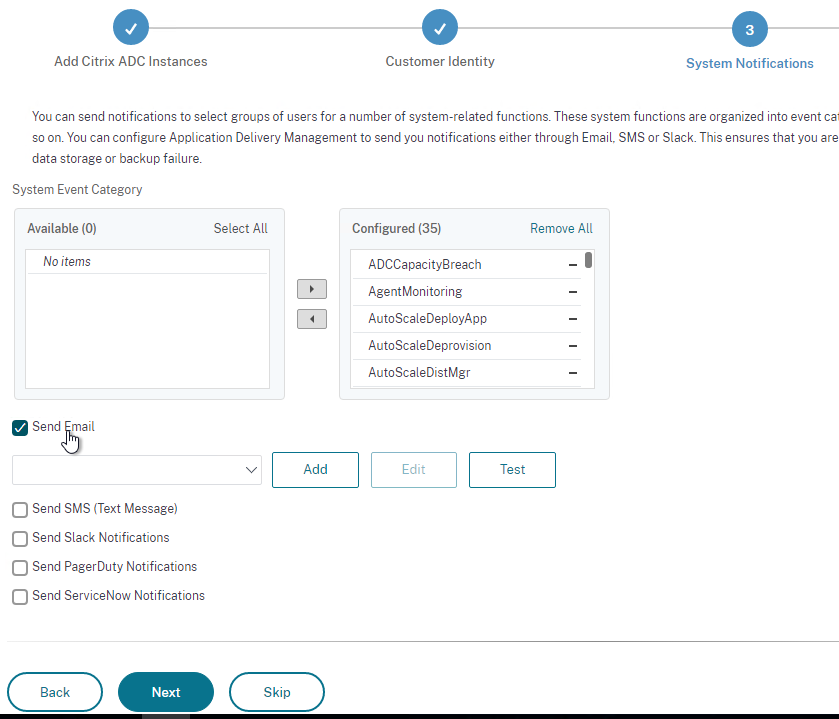
- In the Done page, click Finish.
Older Citrix ADM Deploy HA Configuration:
- After both appliances are fully booted, point your browser to the first appliance’s IP address and login as nsroot/nsroot. It will take several minutes after booting before the ADM appliance is ready.
- The top of the screen has some banners.
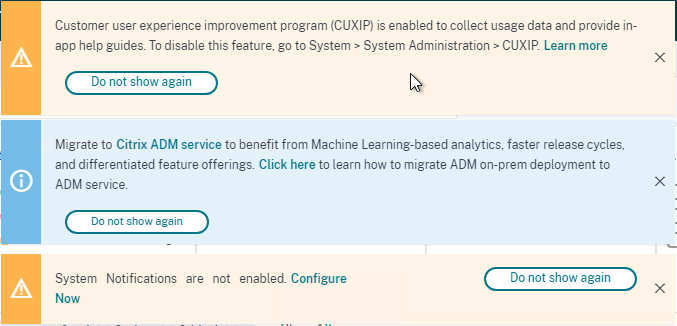
- If you want to make any network changes (e.g., DNS servers) to either node, then you must make those changes before you deploy the HA pair. Move your mouse over the left menu, expand Settings and click Administration.
- On the right, click IP Address, Second NIC, Host Name and Proxy Server.
- Enter an Alternate DNS and then click Save.
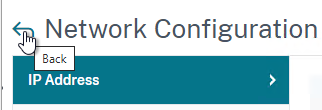
- Click the back arrow to go back.
- If you already created the HA pair, then the only way to add a second DNS server is through the command line on both nodes. See CTX281388 Error Message “Network configuration change is not allowed in Citrix ADM HA setup” When Changing Network Settings in ADM.
echo "echo \"nameserver DNS_IP\" >> /etc/resolv.conf" >> /mpsconfig/svm.conf
- Enter an Alternate DNS and then click Save.
- Move your mouse to the left side of the screen, expand Settings, and then click Deployment.
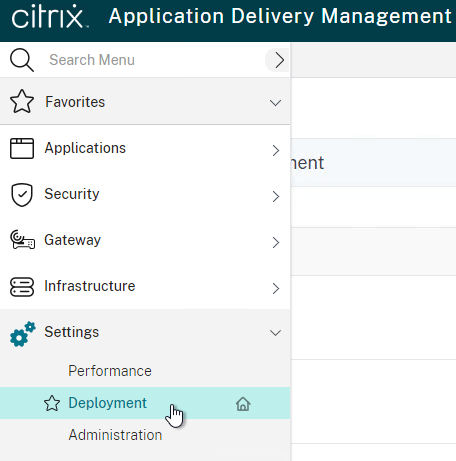
- In the top right, click Deploy.
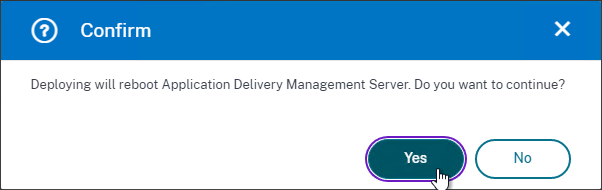
- Click Yes to reboot.
- It takes around 10 minutes to restart.
- After deployment, you can now use the Floating IP to manage the appliance pair.
- Logging in might show you the Get Started wizard. Proceed through the wizard as described in the previous section.
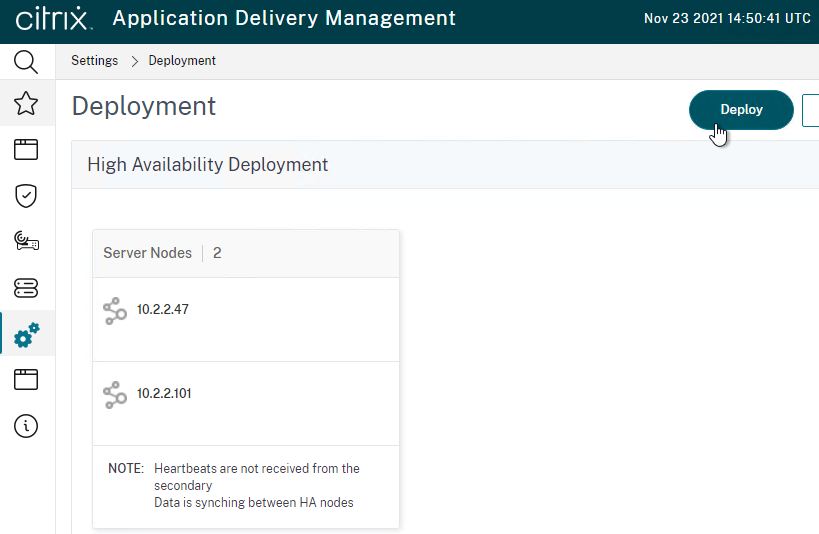
- Move your mouse to the left menu, expand Settings, and click Deployment.
- The Settings > Deployment page should show both nodes as UP and syncing.
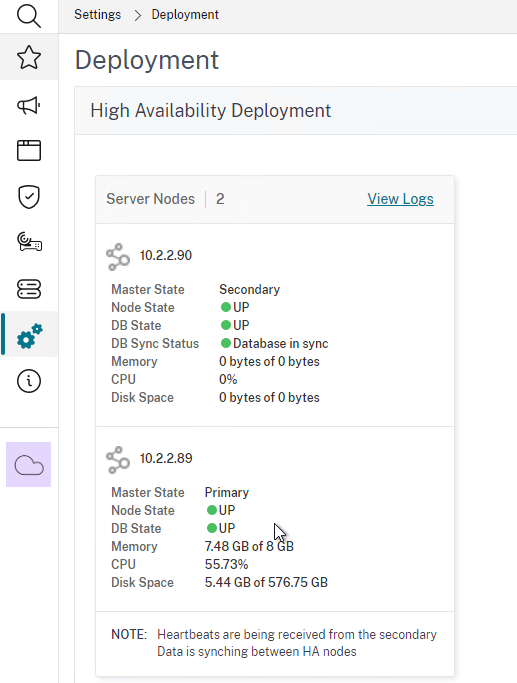
Afterwards, you can manage High Availability.
- Settings> Deployment lets you see the HA nodes.
- You can Force Failover from here. Note: HA failover only occurs after three minutes of no heartbeats.
- On the top right is a HA Settings button that lets you change the Floating IP.
DR Node
Requirements for the DR node:
- The main datacenter must have an HA pair of NetScaler Console appliances. Standalone in the main datacenter is not supported.
- Latency from the main datacenter HA pair to the DR node must not exceed 200 ms.
- Ports 5454 and 22 open between the NetScaler Console nodes.
To configure a DR node:
- Import another NetScaler Console appliance into a remote datacenter and configure an IP address.
- If you added a second disk to the main datacenter NetScaler Console appliances, then you must add the same size second disk to the DR NetScaler Console appliance.
- After configuring the new nodes’ IP address, SSH to the DR appliance and login as nsrecover/nsroot.
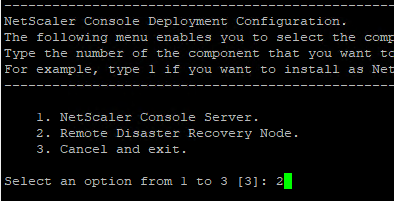
- Enter deployment_type.py.
- Enter 2 for Remote Disaster Recovery Node.
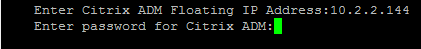
- Enter the Floating IP address of the HA pair in the main datacenter.
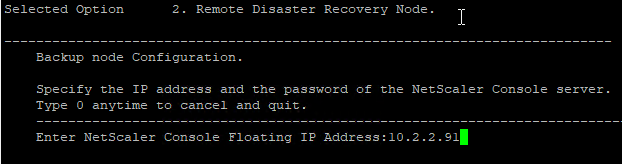
- Enter the nsroot password, which is nsroot by default.
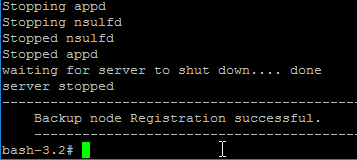
- The DR node registers with the NetScaler Console HA Pair.
- You can change the password of the DR node by running the following command:
./mps/change_freebsd_password.sh <username> <password>
- Point your browser to the Floating IP Address and login.
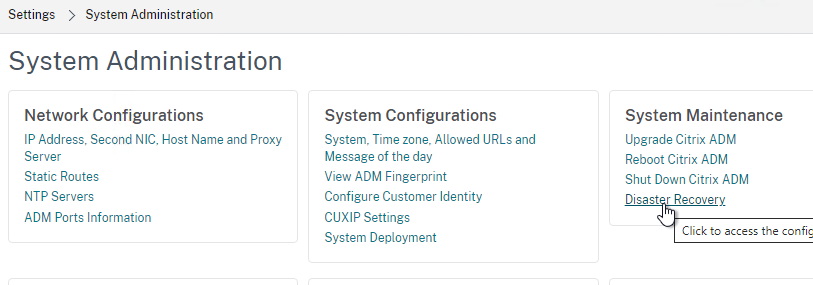
- Go to Settings > Administration.
- On the right, in the right column, click Disaster Recovery Settings.
- The Registered Recovery Node should already be filled in. Click Deploy DR Node.
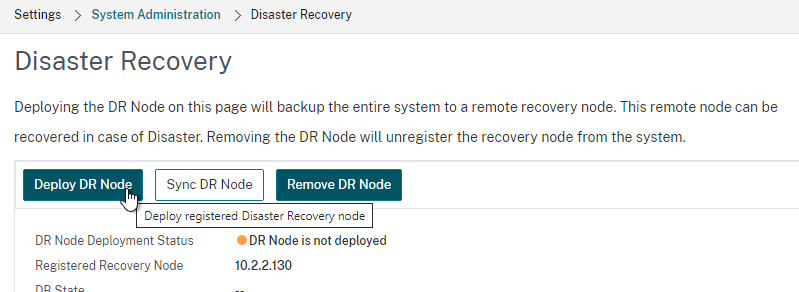
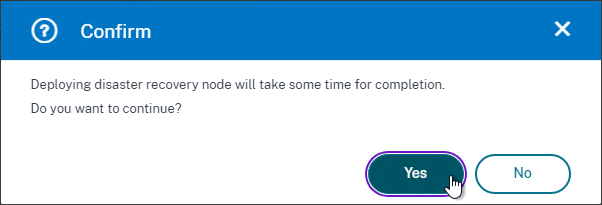
- Click Yes to enable DR.
- A System Backup is performed and replicated to the DR appliance. Click Close when done.
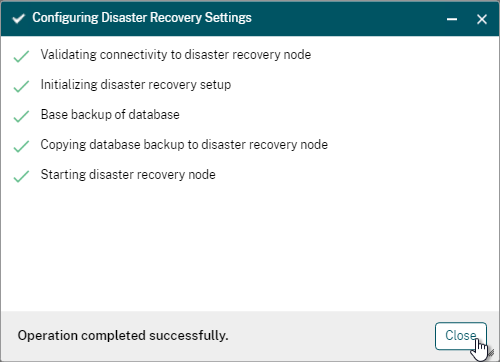
- The status of the DR node is displayed. You can click the Refresh icon on the top right to update the display.
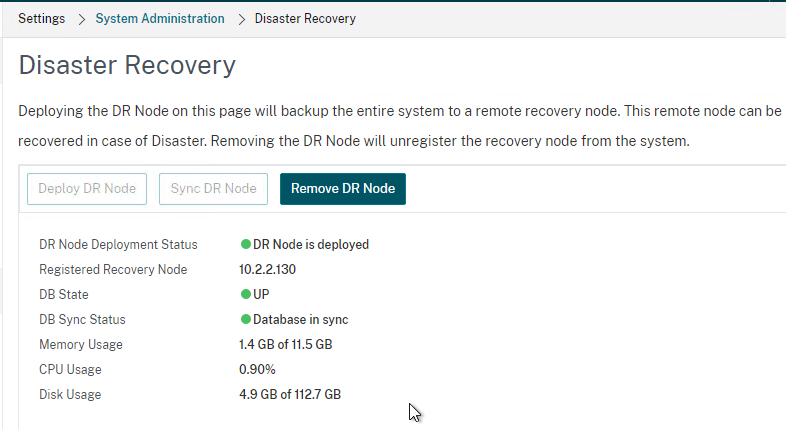
- There’s a Sync DR Node button in case it gets out of sync.
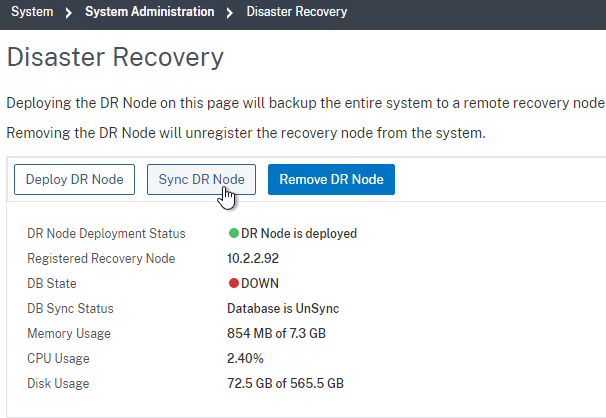
- Disaster Recovery is not automatic. See the manual DR procedure at NetScaler Docs. Docs also shows how to fail back.
/mps/scripts/pgsql/pgsql_restore_remote_backup.sh
NetScaler Console Agents
NetScaler Console Agents help NetScaler Console discover and manage instances on the other side of a high latency WAN link.
The virtual appliance for NetScaler Console Agent is different than the normal NetScaler Console appliance.
- Download the NetScaler Console Agent from the main NetScaler Console download page. On the NetScaler Console download page for a particular build, scroll down the page to find the ADM Agent images.
- Extract the downloaded .zip file.
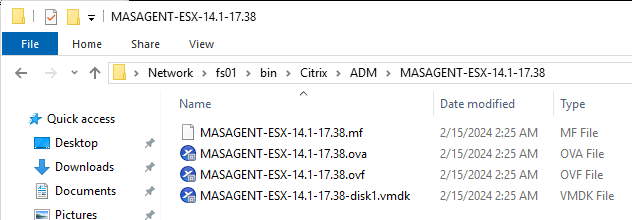
- Import the MASAGENT .ova to vSphere. You can import the single .ova file, or you can import the .ovf file plus the .mf file and the .vmdk file.
- Edit the settings of the virtual machine to see the allocated CPU and Memory.
- There’s no need to add a disk to the Agent.
- Power on the NetScaler Console Agent virtual machine.
- At the virtual machine’s console, configure an IP address.
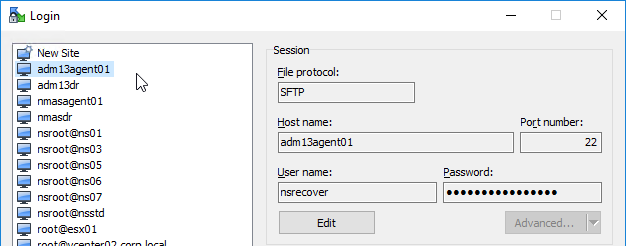
- Login as nsrecover/nsroot.
- Run
/mps/register_agent_onprem.py
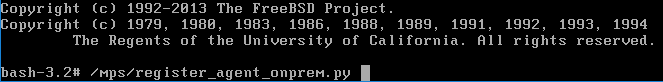
- Enter the floating IP address of the main NetScaler Console HA Pair. Enter nsroot credentials for NetScaler Console. Enter a new password for NetScaler Console Agent.
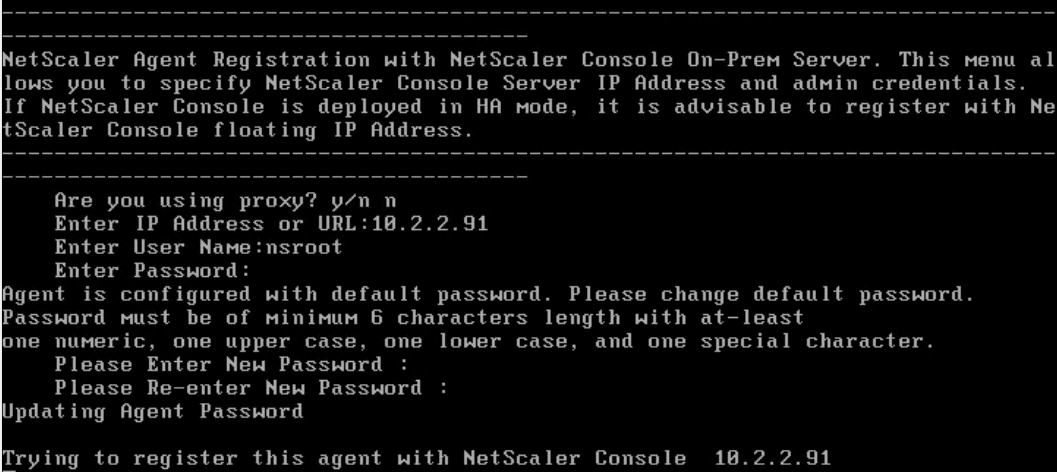
- The Agent will be registered, and services restarted.
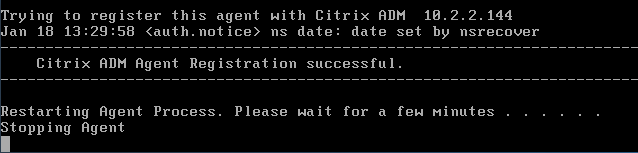
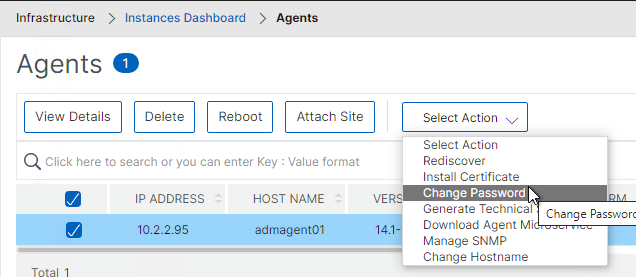
- To change the nsrecover password on NetScaler Console Agents, putty (SSH) to the NetScaler Console Agent appliance, login as nsrecover and then run the script at /mps/change_agent_system_password.py. Or you can change the password in the NetScaler Console interface at Infrastructure > Agents.
- Login to the NetScaler Console Floating IP.
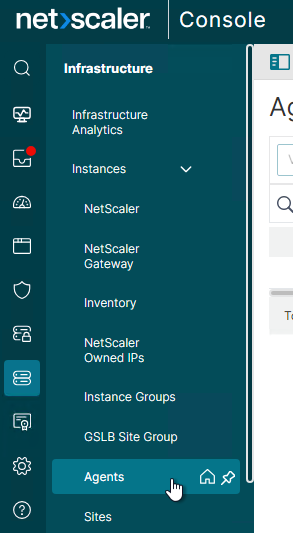
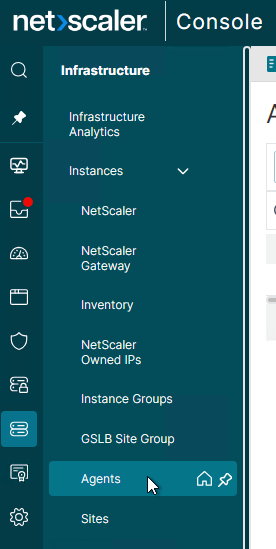
- Go to Infrastructure > Instances > Agents.
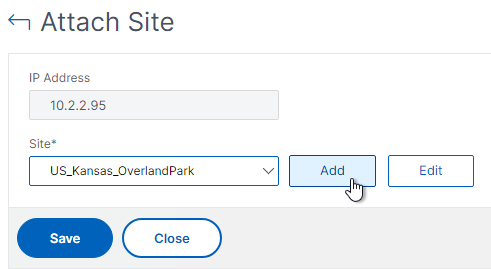
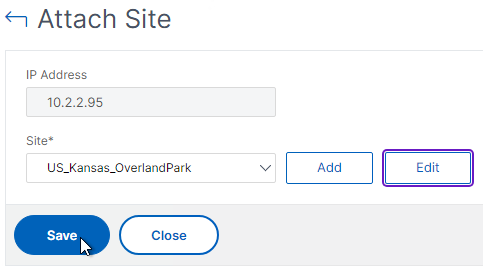
- On the right, select the NetScaler Console Agent, and then click Attach Site.
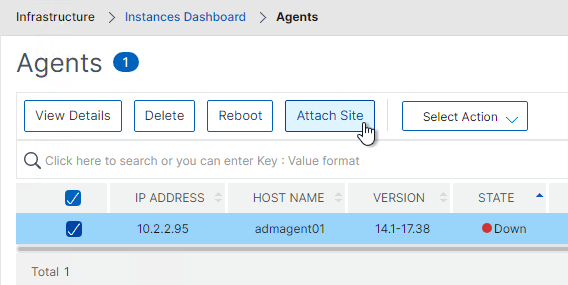
- In the Site drop-down, if you don’t see your site, then you can click the Add button to create a new site.
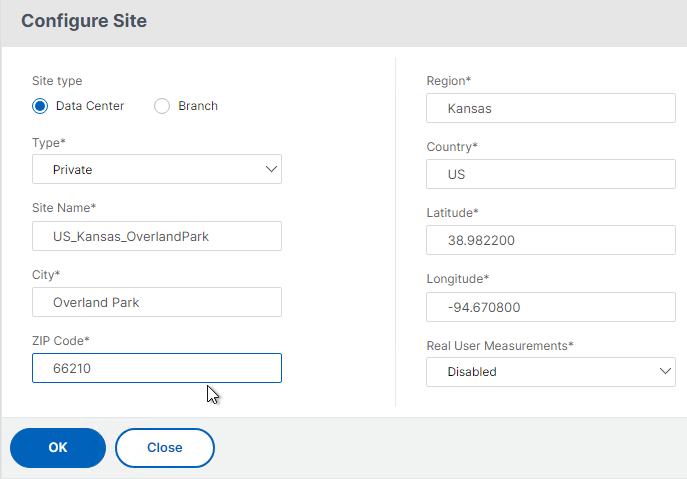
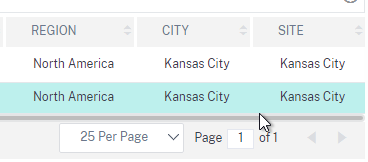
- Enter a name and other location information.
- Make sure you enter the coordinates. Google can find coordinates for various locations. If Longitude is West, then the value is negative.
- Click Create when done.
- Click Save to attach the Site to the Agent. Any NetScaler instance discovered through this Agent will be attached to the configured Site.
- For Agent HA, import two NetScaler Console Agents into your hypervisor and attach both Agents to the same Site.
- You can change the Agent’s nsrecover password from the NetScaler Console GUI.
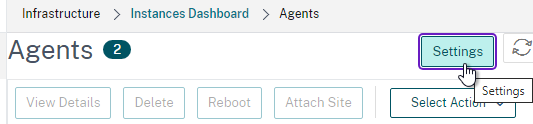
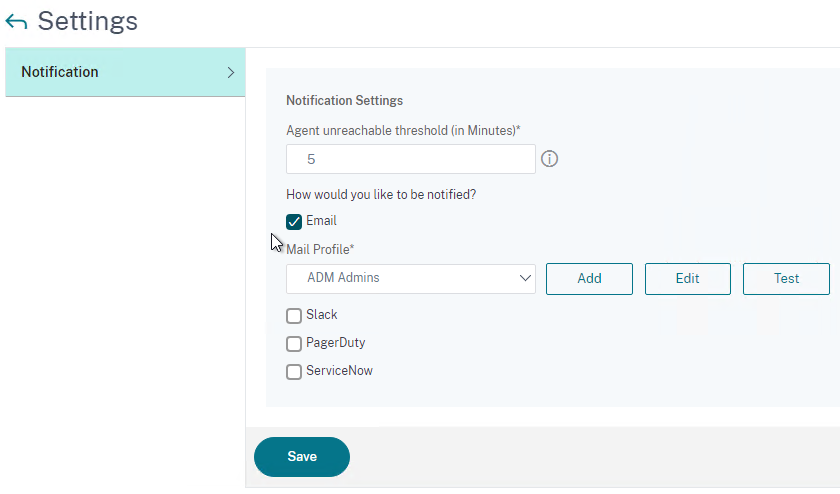
- ADM 13.1 build 24 and newer have a Settings button on the top-right of the Agents page where you can enable Notifications when a NetScaler Console Agent is unreachable.
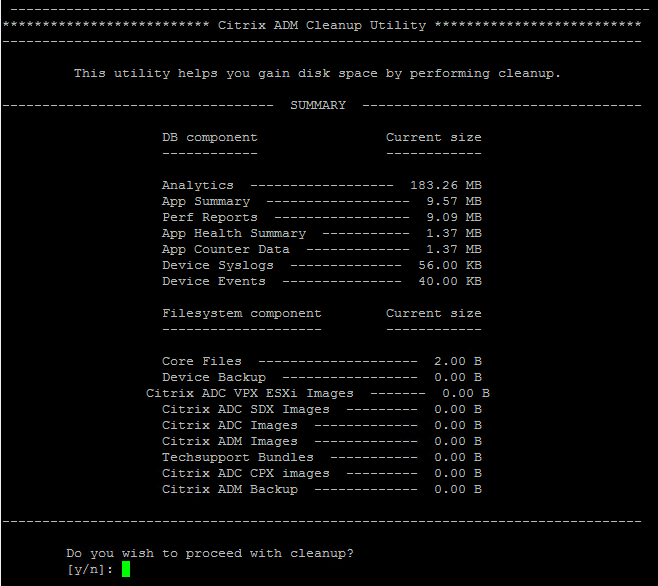
NetScaler Console Appliance Maintenance
- Shutdown or Reboot – From CTX220000 How to reboot or shutdown NetScaler MAS using CLI: when using the NetScaler Console CLI, do not use the reboot command since it will cause data corruption. Instead, run shutdown -r now.

- Static Route – If you need to add a static route to NetScaler Console, then see CTX223282 How to Add a Static Route on NetScaler MAS.

- NetScaler Console Database Cleanup Tool – Run
/mps/mas_recovery/mas_recovery.py. For details, see Recover inaccessible NetScaler Console servers at NetScaler Docs.
Add NetScaler Instances
NetScaler Console must discover NetScaler instances before they can be managed. NetScaler Docs How NetScaler Console discovers instances.
- Point your browser to the NetScaler Console Floating IP address and login as nsroot/nsroot.
Before adding instances, NetScaler Console needs to know the nsroot password for the instances. You create Admin Profiles to specify the nsroot passwords.
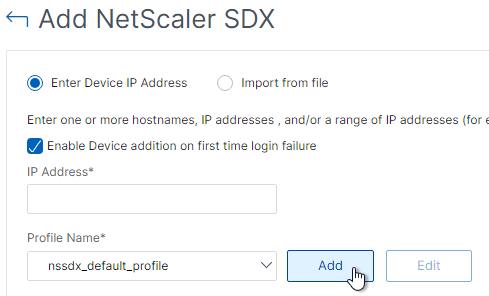
- When adding instances during the initial Welcome wizard, next to Profile Name, click Add to create an Admin Profile.
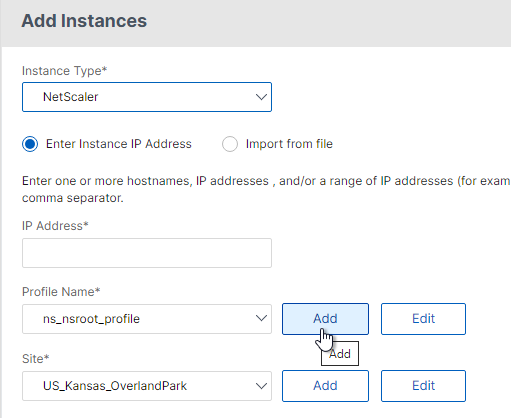
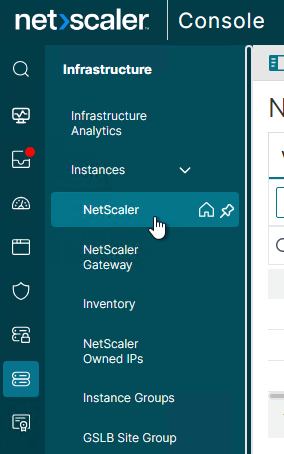
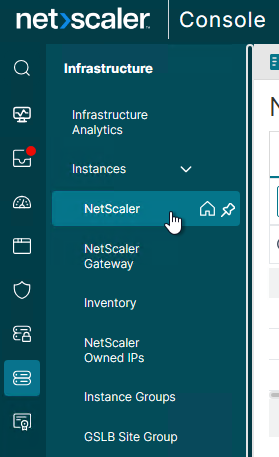
- Or in the main interface, to edit or create new Admin Profiles, move your mouse to the left menu, then go to Infrastructure > Instances > NetScaler.
- On the right, open the menu named Select Action, and click Profiles.
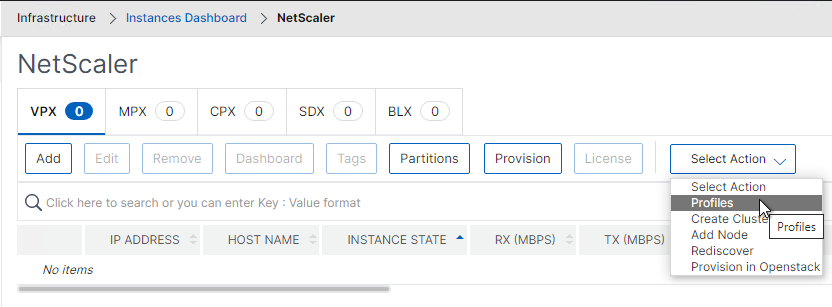
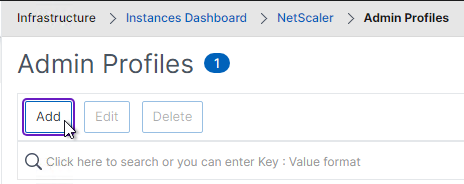
- Click the Add button to create an Admin Profile.
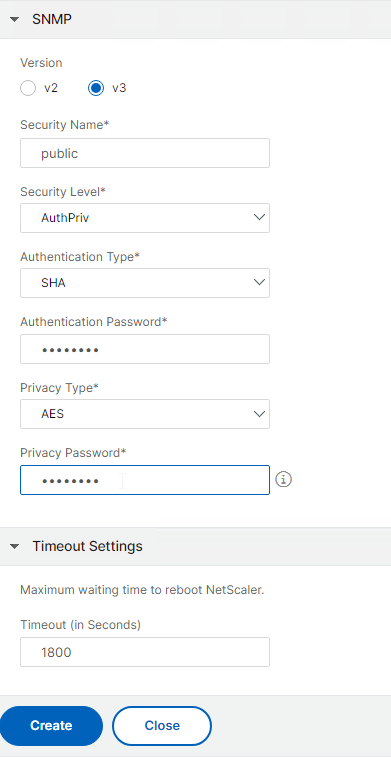
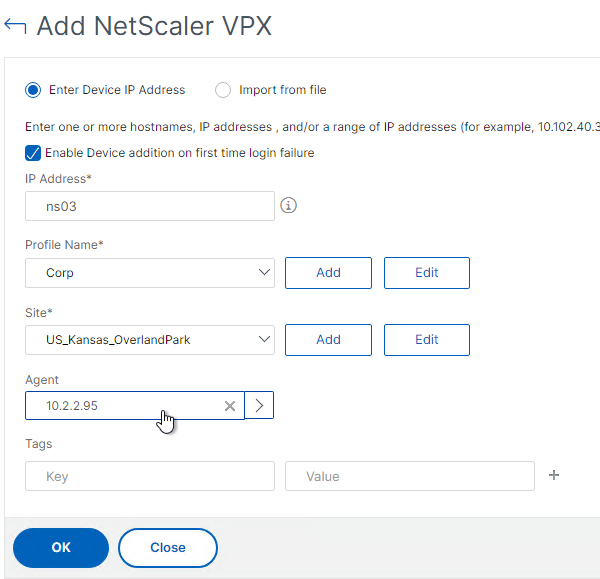
- In the top half, give the Profile a name and enter the password for the instance’s nsroot account. Create a separate Admin Profile for each unique nsroot password.
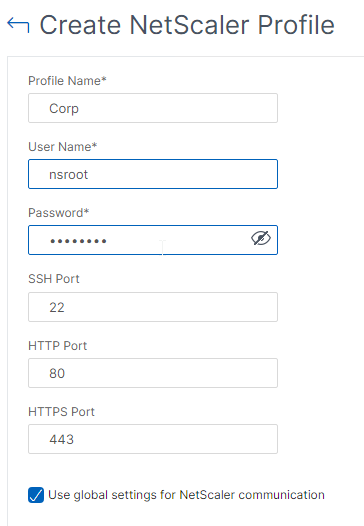
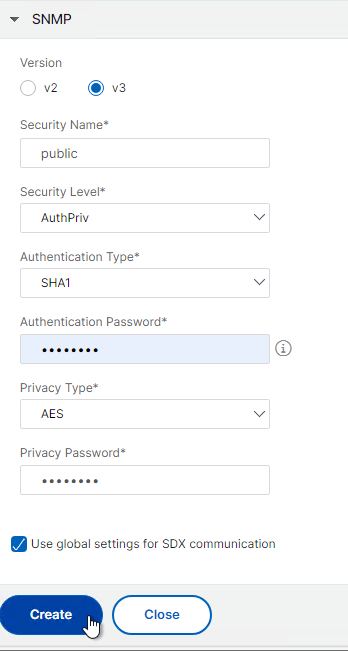
- In the bottom, make up some SNMP settings. You can do SNMP v3. Change the Authentication Type and Privacy Type to stronger options.
- Click Create when done.
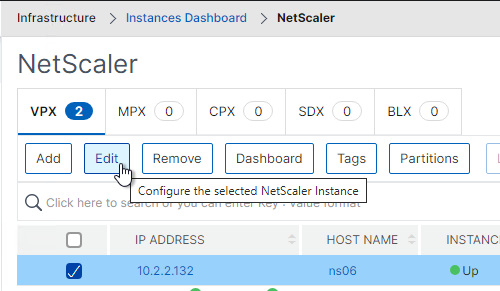
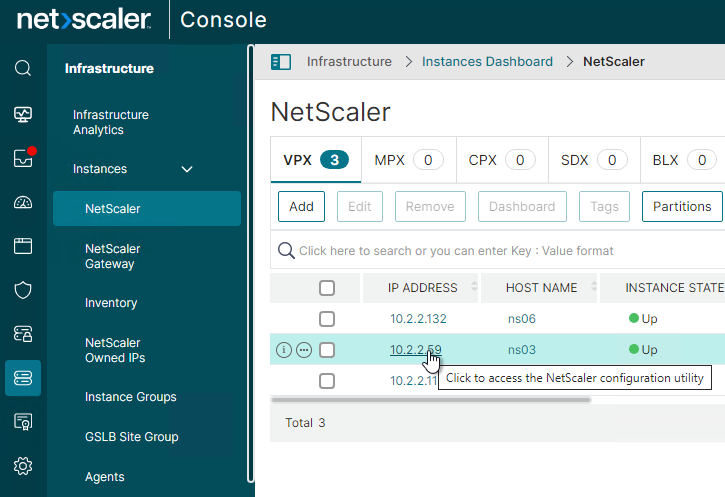
To add instances:
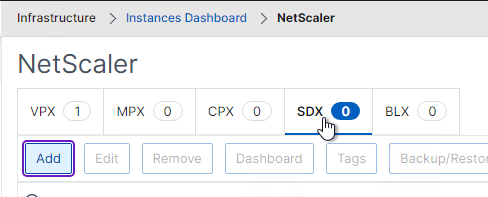
- Move your mouse to the left, expand Infrastructure, expand Instances, and click NetScaler.
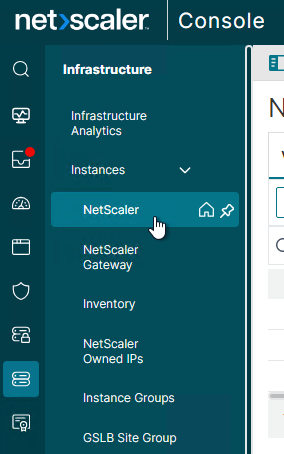
- On the right, select a tab (e.g. MPX), and then click Add.
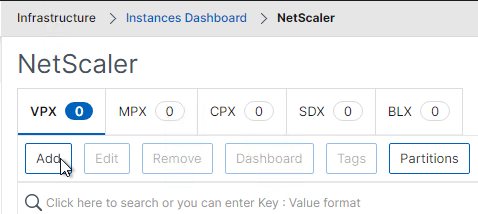
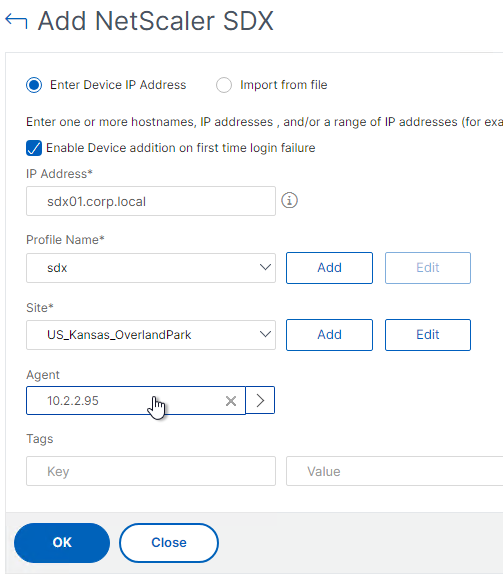
- The Add instance screen is the same as shown during the getting started wizard. To authenticate to the NetScaler ADC using nsroot, select an existing Profile or create a new one. If you have Sites or Agents, you can select one. Select a Site so it’s shown correctly on the world map. Click OK when done.
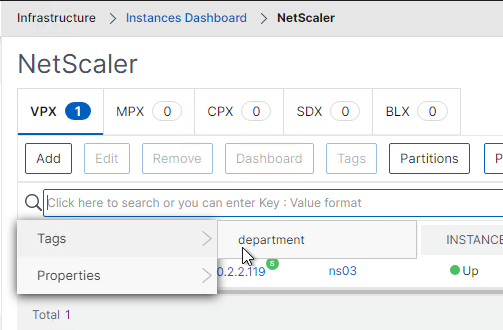
Tags:
- You can assign Tags to instances. See How to create tags and assign to instances at NetScaler Docs.
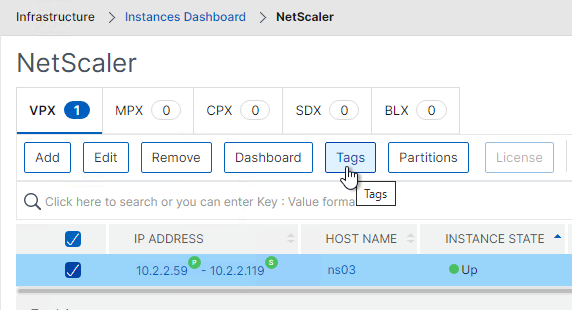
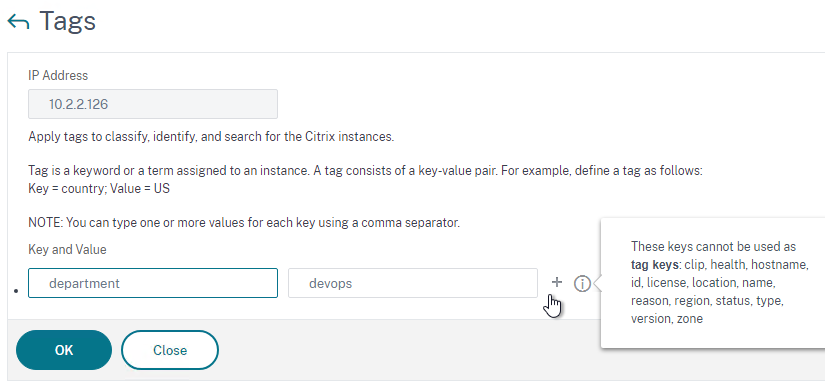
- You can then search instances based on the Tags.
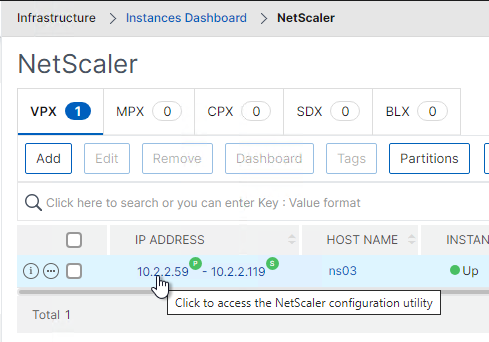
Instance Authentication from NetScaler Console
By default, when you click the blue link for one of the instances, NetScaler Console will do single sign-on to the instance using nsroot credentials. This is probably a security risk, or certainly an auditing risk.
To prevent NetScaler Console from doing single sign-on to instances:
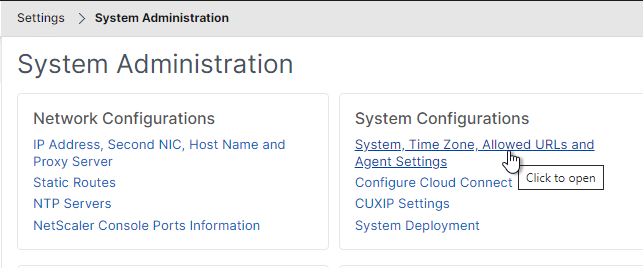
- In NetScaler Console, go to Settings > Administration.
- On the right, click System, Time zone, Allowed URLs and Agent Settings.
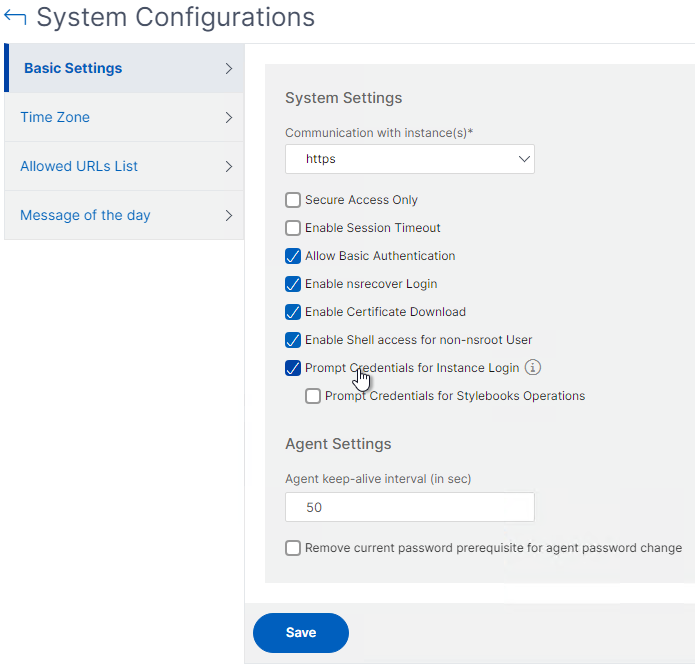
- In the Basic Settings page, check the box next to Prompt Credentials for Instance Login and click Save.
NetScaler SDX
- At Infrastructure > Instances > NetScaler, on the SDX tab, you can click Add to discover a SDX appliance plus all VPXs on that SDX appliance. You don’t have to discover the VPXs separately.
- In the Add NetScaler SDX page, click the Add button next to the Profile Name drop-down to create an SDX profile. Note: SDX profiles are different than VPX profiles.
- Enter the credentials for the SDX SVM Management Service.
- For NetScaler Profile, select an admin profile that has nsroot credentials for the VPX instances. After the SDX’s VPX instances are discovered, NetScaler Console uses this NetScaler Profile to login to each VPX. If you don’t have a VPX Admin Profile in your drop-down list, click the Add button. Note: You can only select one NetScaler Profile. If each VPX instance has different nsroot credentials, you can fix it after SDX discovery has been performed. The NetScaler Profile is different than the SDX Profile.
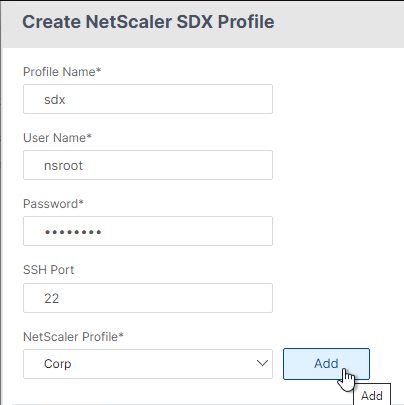
- Back in the Configure NetScaler Profile page, enter new SNMP settings that SDX will use to communicate with NetScaler Console.
- Click Create when done.
- Back in the Add NetScaler SDX page, select a Site, and optionally an Agent.
- Click OK to start discovery.
- After discovery is complete, switch to the VPX tab. You should automatically see the VPX instances.
- To specify the nsroot credentials for a VPX, right-click the VPX, and click Edit.
- In the Modify NetScaler VPX page, either select an existing Profile Name, or click the Add button to create a new one. Click OK when done. It should start rediscovery automatically.
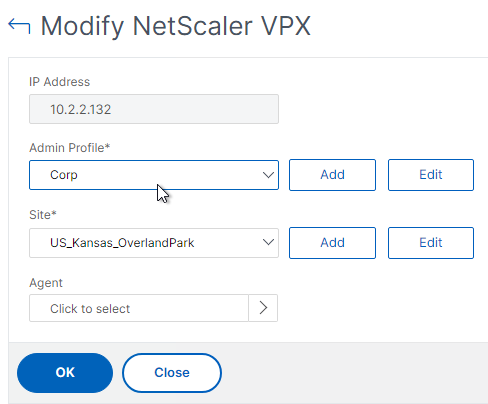
- In the Modify NetScaler VPX page, either select an existing Profile Name, or click the Add button to create a new one. Click OK when done. It should start rediscovery automatically.
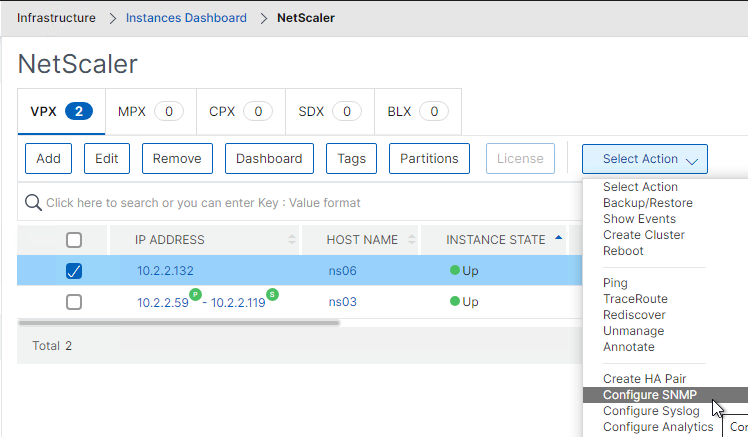
- After fixing the nsroot credentials, right-click the VPX instance and click Configure SNMP. NetScaler Console will configure the VPX to send SNMP Traps to NetScaler Console.
Instance management
- REST API proxy – NetScaler Console can function as a REST API proxy server for its managed instances. Instead of sending API requests directly to the managed instances, REST API clients can send the API requests to NetScaler Console. See NetScaler Console as an API Proxy Server
- Citrix Application Delivery Management PowerShell Module by Kenny Baldwin provides a Invoke-ADMNitro cmdlet to send Nitro commands to instances through NetScaler Console.
- NetScaler Flexed Licensing – Your Flexed license includes software instance licenses (VPX/CPX/BLX, SDX, MPX, and VPX FIPS) and bandwidth capacity licenses. You must apply the Flexed license on NetScaler Console. You must also apply the MPX Z-Cap and SDX Z-Cap license on NetScaler MPX and NetScaler SDX hardware respectively. A Flexed license also offers analytics for unlimited virtual servers. See Flexed capacity license at NetScaler Docs.
Enable AppFlow / Insight / Analytics
NetScaler Console build 21 and newer remove the VIP licensing requirement for Analytics.
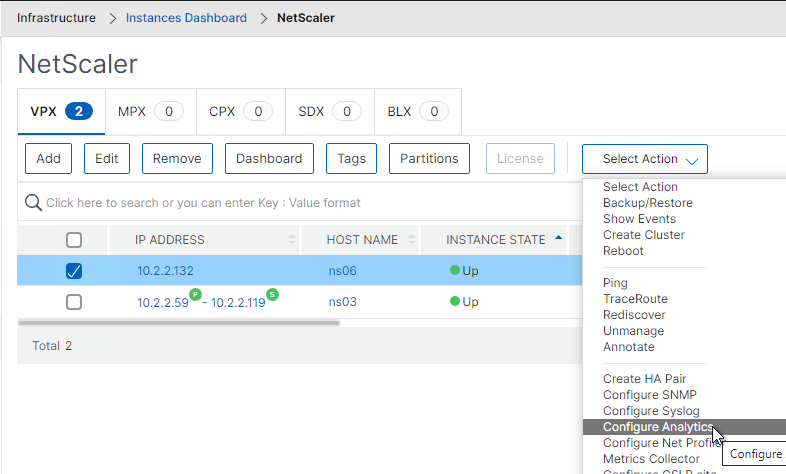
- Go to Infrastructure > Instances > NetScaler.
- On the right, switch to one of the instance type tabs (e.g. VPX).
- Select an instance, open the Select Action menu, and click Configure Analytics.
- Select one or more Virtual Servers and then click the button labelled Enable Analytics.
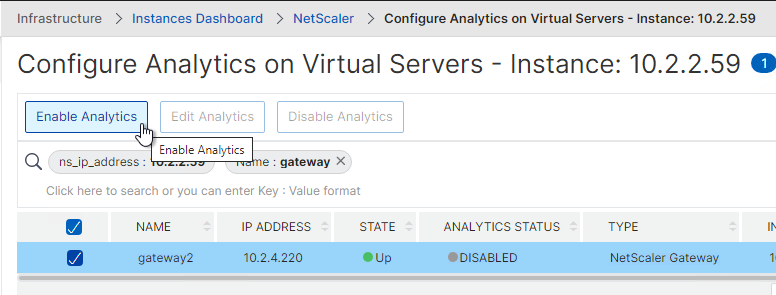
- Different options are available for different types of Virtual Servers.
- For NetScaler Gateways, you want HDX Insight. Gateway Insight provides AAA and EPA info for the Gateway. Enable WAF Security Violations if you enabled WAF on your Citrix Gateway.
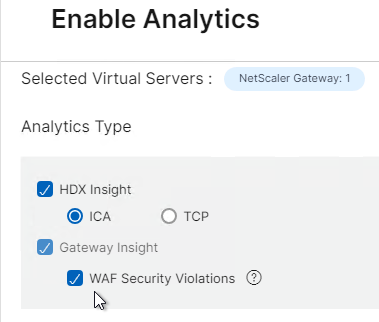
- Expand Advanced Settings and select NetScaler Gateway.
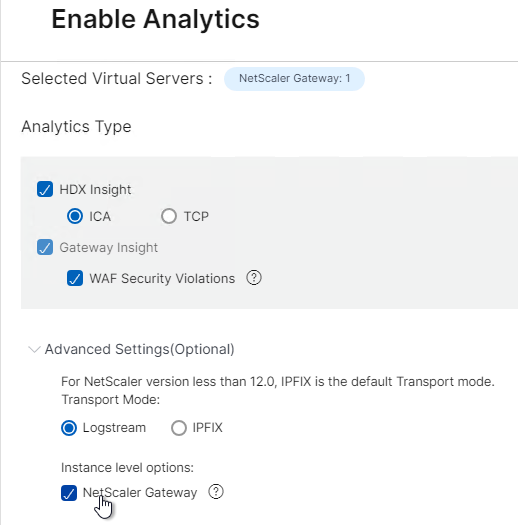
- Expand Advanced Settings and select NetScaler Gateway.
- For HTTP Load Balancing Virtual Servers, you want Web Insight. If you are licensed for NetScaler ADC Premium Edition, then you can also enable WAF Security Violations for Web App Firewall and Bot Protection monitoring.
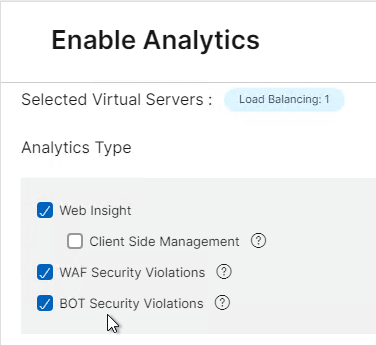
- For analytics on HTTP Virtual Servers, expand Advanced and click Enable X-Forwarded-For.
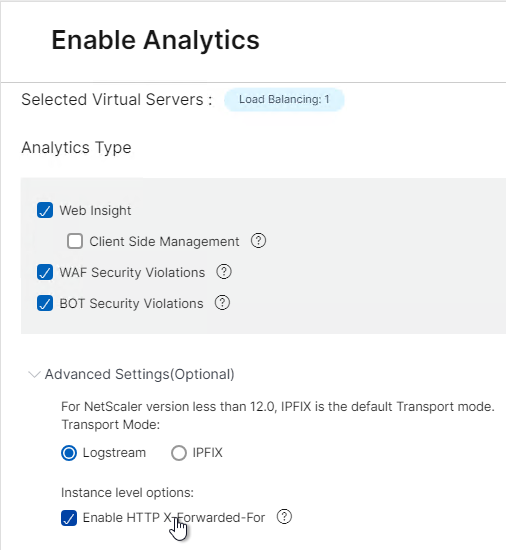
- For analytics on HTTP Virtual Servers, expand Advanced and click Enable X-Forwarded-For.
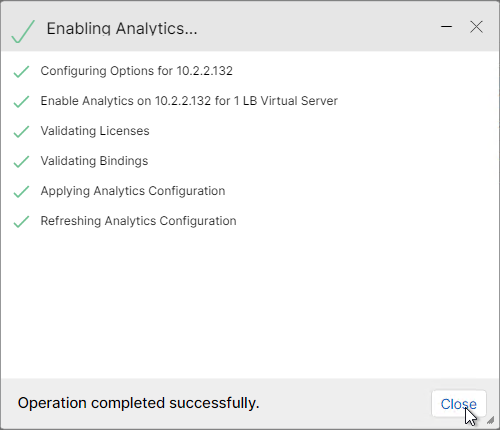
- Click OK to enable AppFlow on the Virtual Servers.
- Click Close when configuration is complete.
- Enable Analytics on more Virtual Servers.
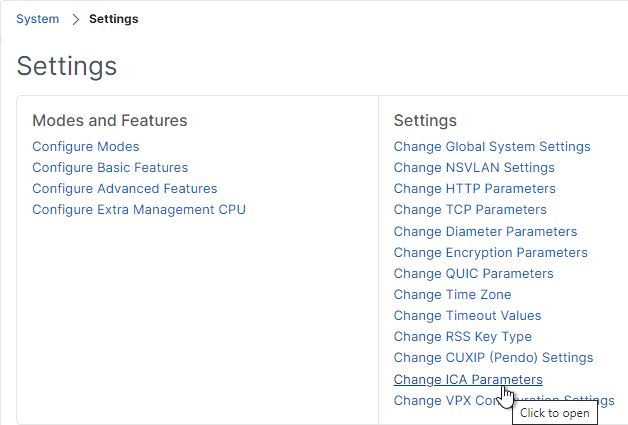
- Login to the NetScaler ADC (not NetScaler Console) and go to System > Settings.
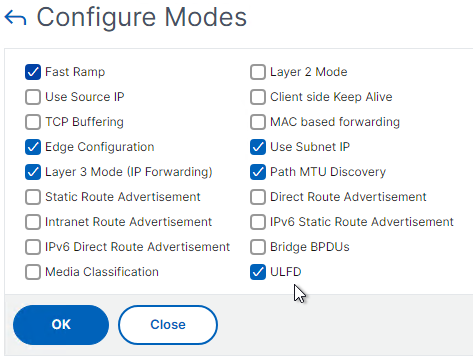
- On the right, click Configure Modes.
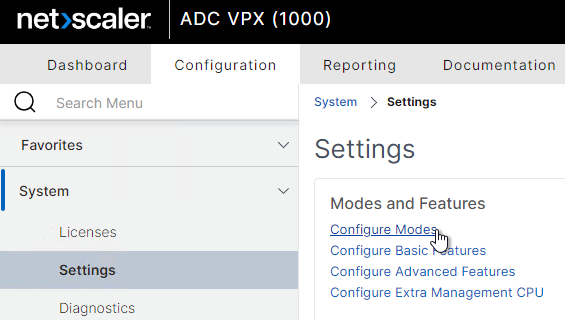
- If you are using LogStream, then make sure ULFD is checked. Click OK.
enable mode ulfd
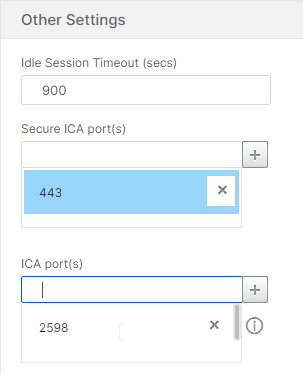
- On the right, click Change Global System Settings.
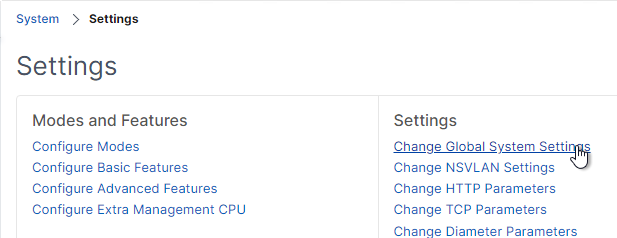
- Scroll down to ICA port(s) and add 1494 and 2598 to the list. Click OK. (Source = Citrix Discussions)
set ns param -icaPort 1494 2598
- On the right, click Change HTTP Parameters.
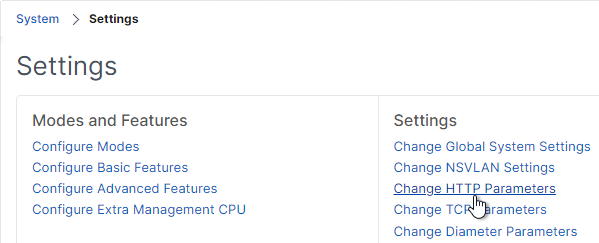
- At the top, add 80 and 443 to the Http Ports list. Click OK. (Source = Citrix Discussions)
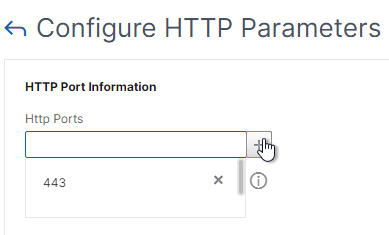
set ns param -httpPort 80 443
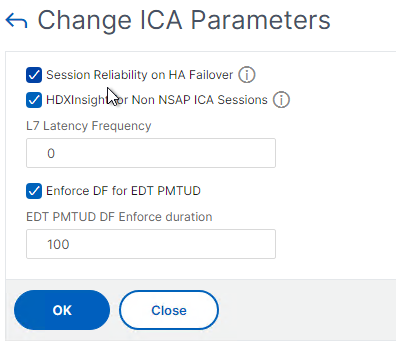
- By default, with AppFlow enabled, if a NetScaler ADC High Availability pair fails over, then all Citrix connections will drop, and users must reconnect manually. NetScaler ADC has a feature to replicate Session Reliability state between both HA nodes.
- From Session Reliability on NetScaler High Availability Pair at NetScaler Docs: Enabling this feature will result in increased bandwidth consumption, which is due to ICA compression being turned off by the feature, and the extra traffic between the primary and secondary nodes to keep them in sync.
- On NetScaler ADC, go to System > Settings.
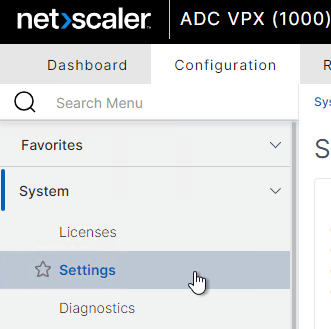
- On the right, in the Settings section, click Change ICA Parameters.
- Check the box next to Session Reliability on HA Failover and click OK.
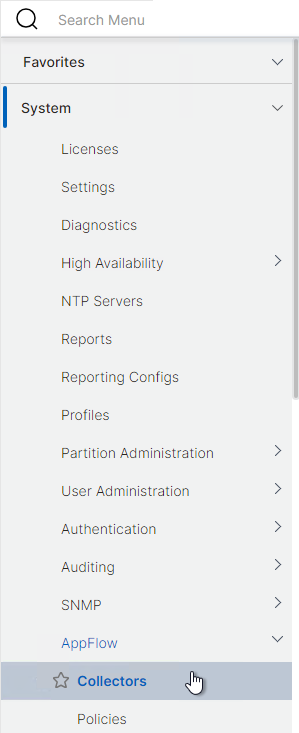
- On NetScaler ADC at System > AppFlow > Collectors, you can see if the AppFlow Collector (NetScaler Console) is up or not.
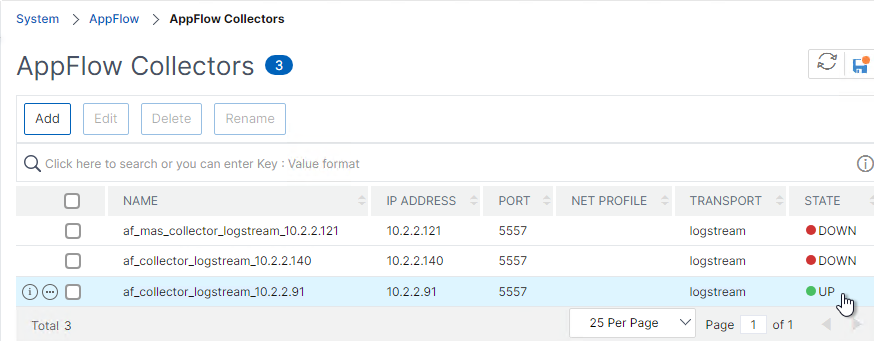
- Go to Traffic Management > Load Balancing > Services and find the adm_metric_collector_svc. If it’s not UP, then you can change it to use NSIP instead of SNIP.
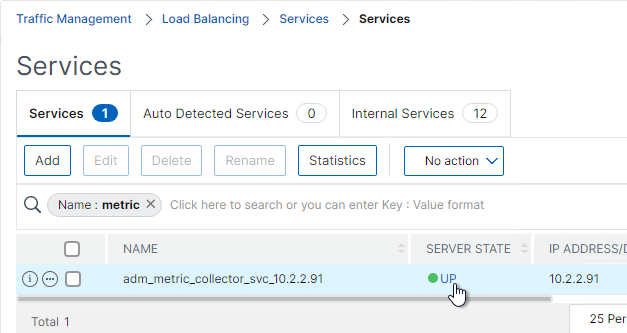
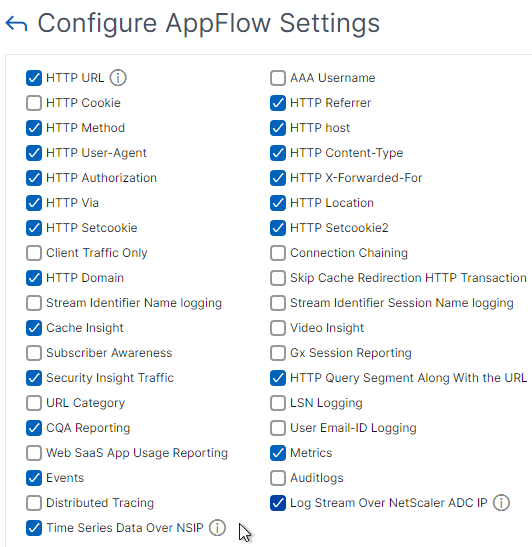
- Go to System > AppFlow. On the right, click Change AppFlow Settings.
- Check the box next to Time Series Data Over NSIP and click OK.
- Go to System > AppFlow. On the right, click Change AppFlow Settings.
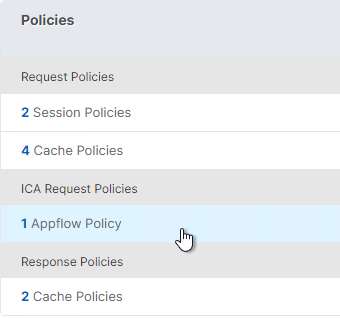
- When AppFlow is enabled on a Gateway Virtual Server, an AppFlow policy is bound to twice to the Gateway: once for Request Policies (i.e., HTTP), and once for ICA Request Policies. You might want to verify that these bindings are actually configured.
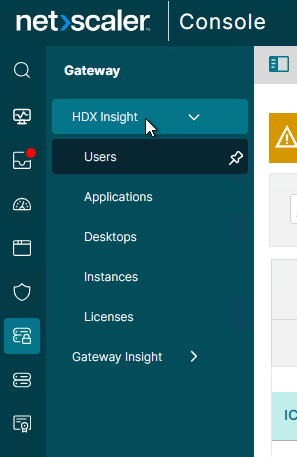
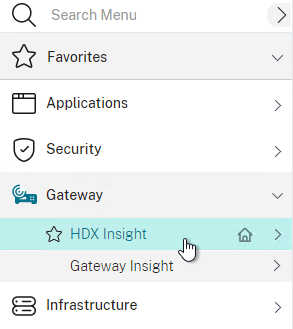
- On the NetScaler Console appliance, AppFlow for ICA (HDX Insight) information can be viewed under the Gateway > HDX Insight node.
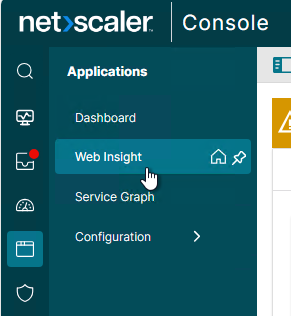
- Web Insight for HTTP Virtual Servers is under Applications > Web Insight. WAF Violations is under Security.
NetScaler Console nsroot Password
Changing NetScaler Console’s nsroot password also changes NetScaler Console’s nsrecover password.
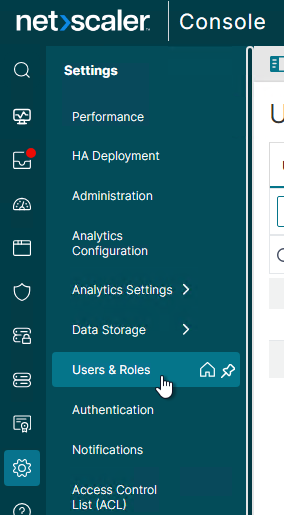
- In NetScaler Console, go to Settings > Users & Roles.
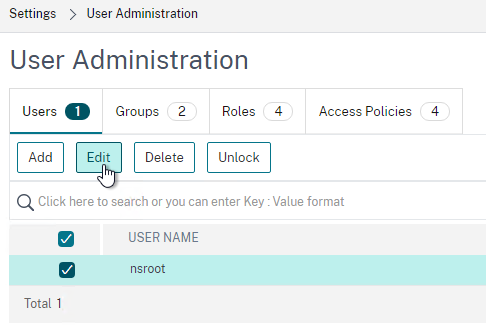
- On the right, on the tab named Users, select the nsroot account, and click Edit.
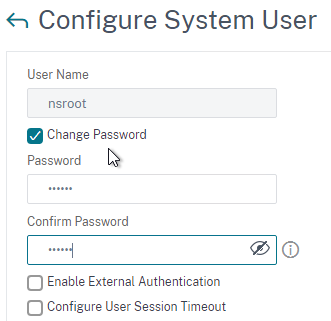
- Check the box next to Change Password and enter a new password.
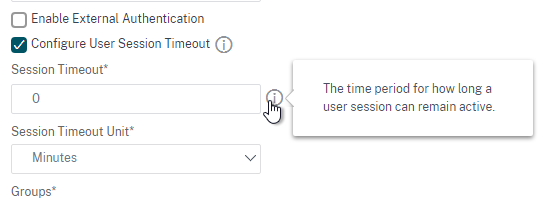
- You can also specify a session timeout by checking the box next to Configure Session Timeout.
- Click OK.

NetScaler Console Management Certificate
- The certificate to upload must already be in PEM format. If you have a .pfx, you must first convert it to PEM (Base64 certificate and key files). You can use a NetScaler ADC’s Import PKCS#12 feature to convert the .pfx to PEM and then download the converted certificate from the NetScaler ADC appliance.
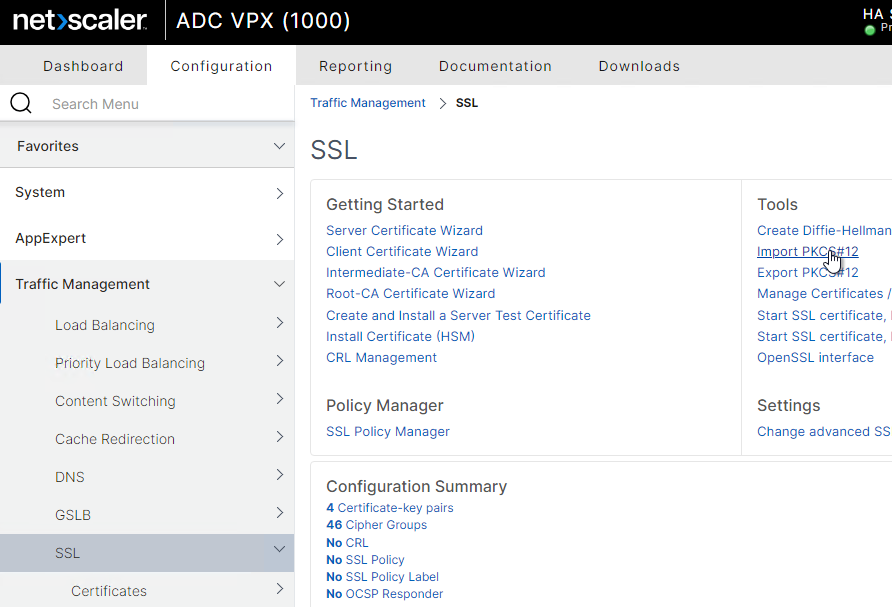
- On any NetScaler ADC, go to Traffic Management > SSL.
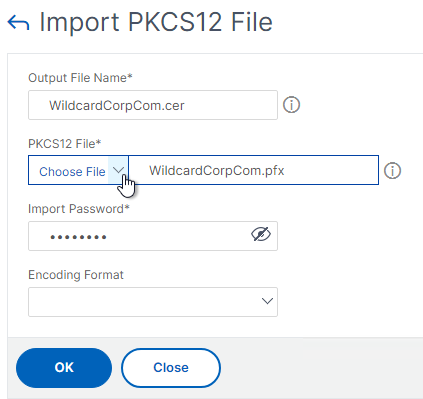
- On the right, click Import PKCS#12.
- Enter a name for a new file that will contain the PEM certificate and PEM key.
- Browse to the .pfx file and enter the password.
- You can optionally encrypt the PEM key by selecting an Encoding Format and entering an encryption key.
- Click OK.
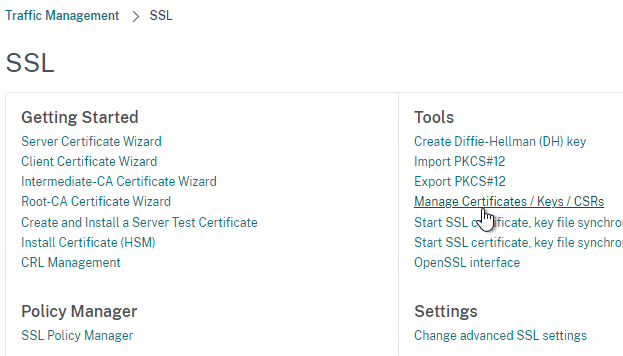
- To download the PEM file, go to Manage Certificates / Keys / CSRs.
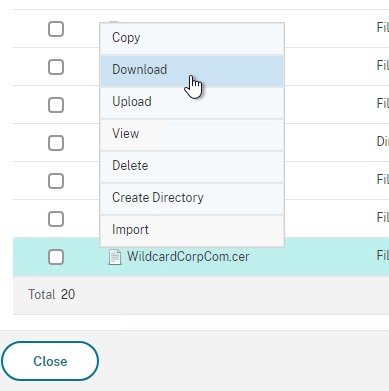
- Scroll to the bottom of the list, right-click the new file, and click Download.
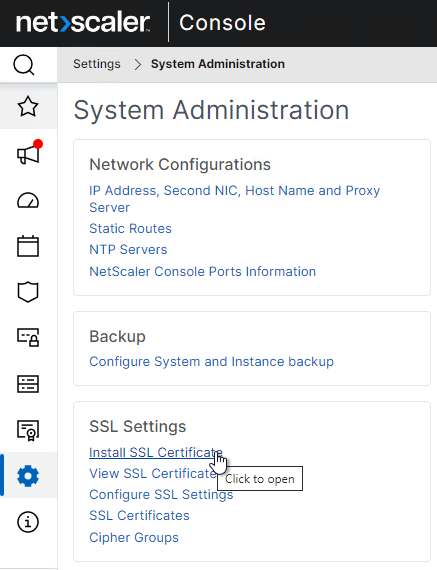
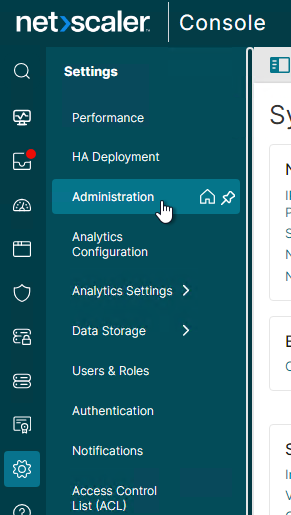
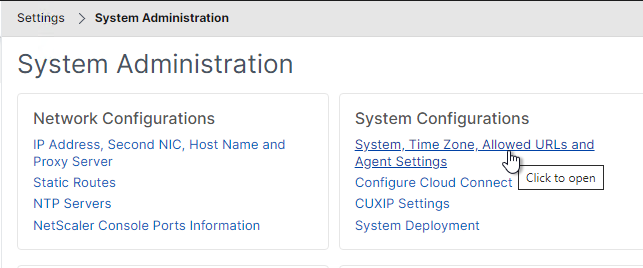
- Back in NetScaler Console, go to Settings > Administration.
- On the right, in the SSL Settings section, click Install SSL Certificate.
- Click Choose File to browse to the PEM format certificate and key files. If the PEM certificate and PEM key are in the same file, then browse to the same file for both fields.
- If the keyfile is encrypted, enter the password.
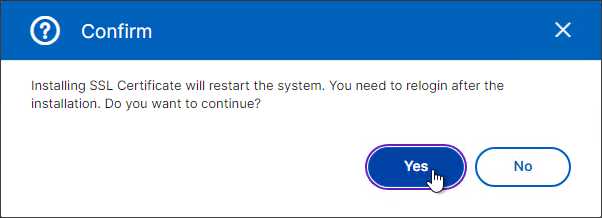
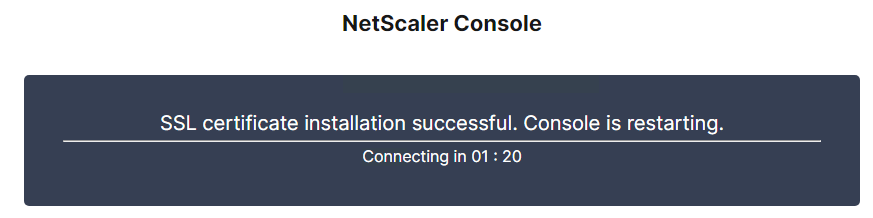
- Click OK.
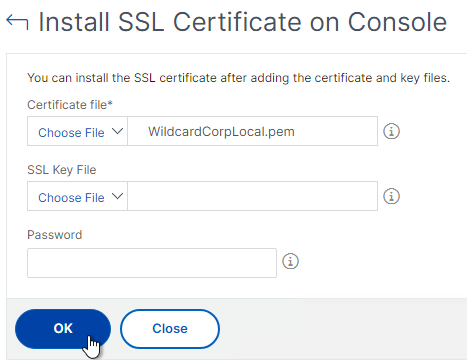
- Click Yes to reboot the system.
- To force users to use https when accessing the NetScaler Console management page, go to Settings > Administration.
- On the right, click System, Time zone, Allowed URLs and Agent Settings.
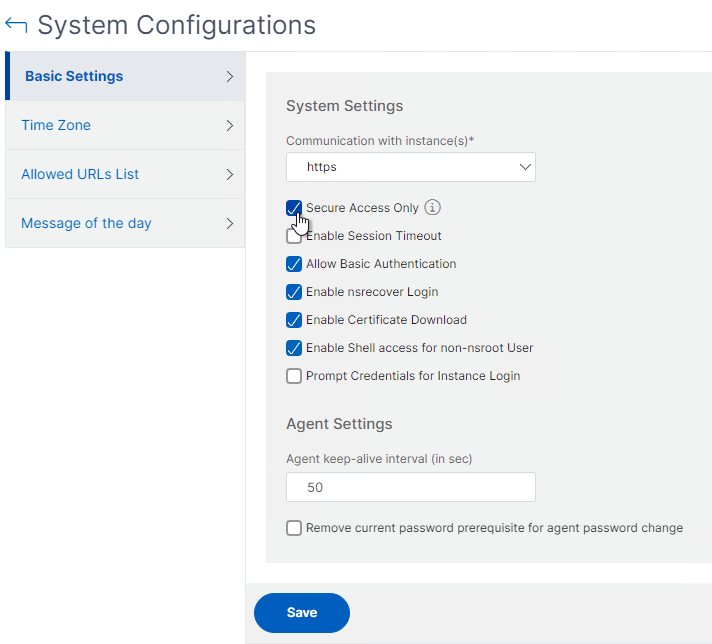
- On the Basic Settings page, check the box next to Secure Access Only and click Save.
System Configuration
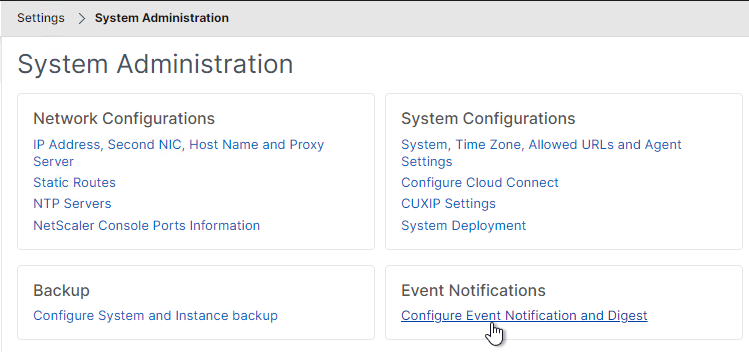
- Go to Settings > Administration.
- On the right, click System, Time zone, Allowed URLs and Agent Settings.
- Check the box next to Enable Session Timeout and specify a value.
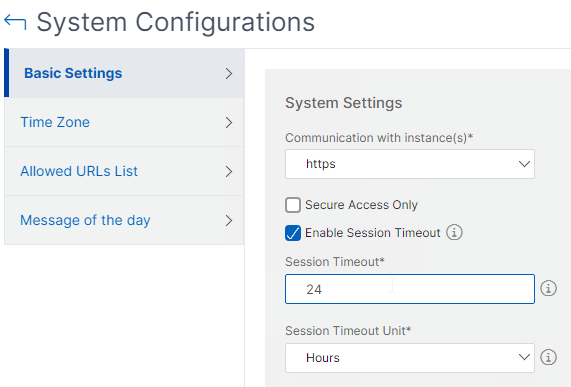
- By default, at Infrastructure > Instances > NetScaler , if you click a blue IP address link, NetScaler Console does single sign on to the instance using the nsroot credentials. If you want to force NetScaler Console users to login using non-nsroot credentials, then check the bottom box for Prompt Credentials for Instance Login.
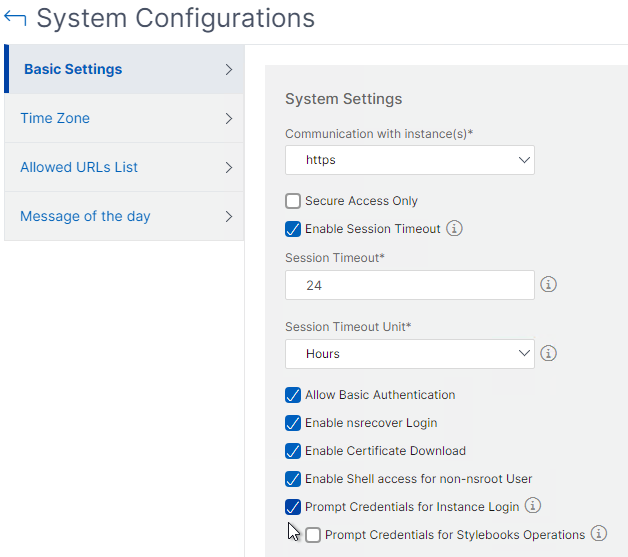
- Click Save.
- On the left, click the Message of the day tab.
- On the right, check the box next to Enable Message.
- Enter a message, and then click Save.
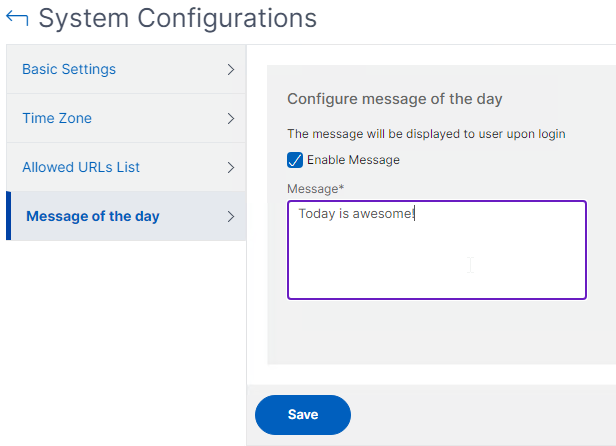
- Click the back arrow when done.
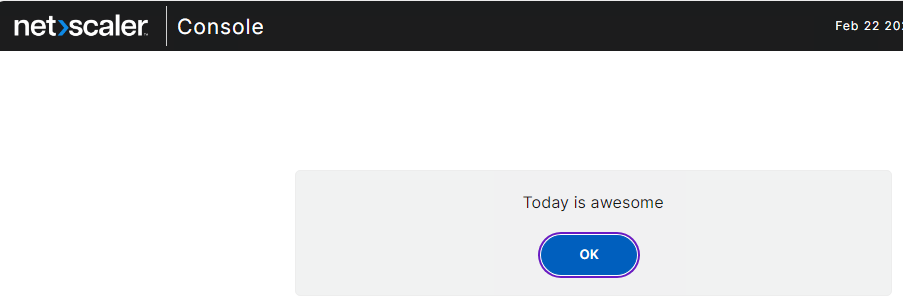
- When you login to NetScaler Console, you’ll be shown the message.
- Check the box next to Enable Session Timeout and specify a value.
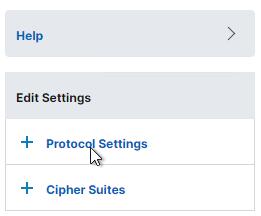
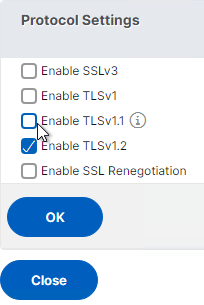
- Settings > Administration > Configure SSL Settings lets you disable TLS 1 and TLS 1.1.
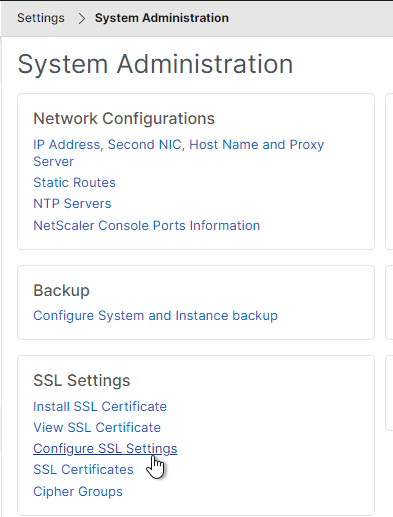
- On the right, click the Protocol Settings section in the Edit Settings section on the right side of the screen.
- On the left, uncheck TLSv1 and TLSv1.1. Then click OK.
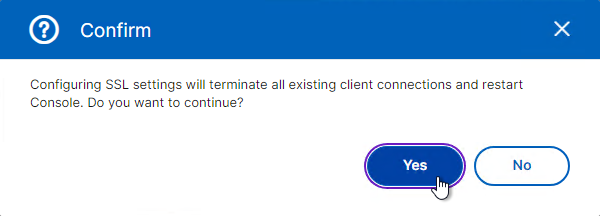
- Click Yes when asked to confirm the restart.
- On the right, click the Protocol Settings section in the Edit Settings section on the right side of the screen.
Prune Settings
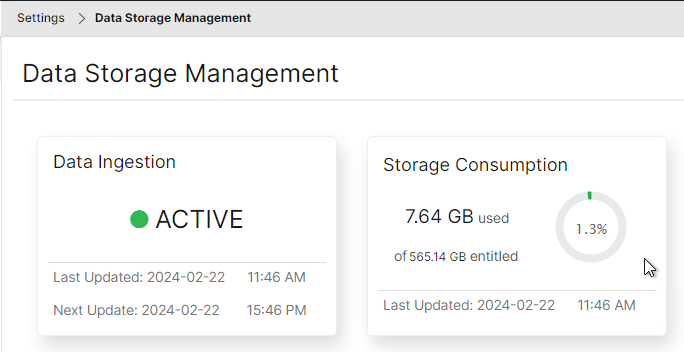
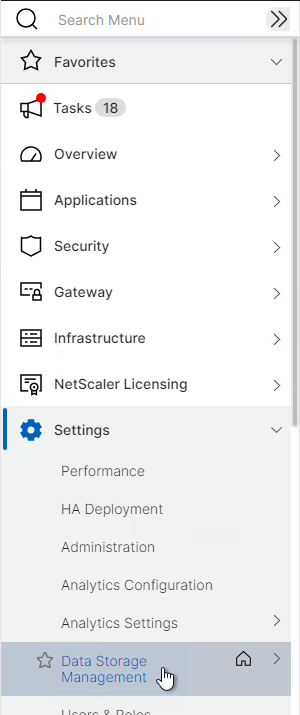
- To see the current database disk usage, go to Settings > Data Storage Management. You can manually initiate pruning from this page.
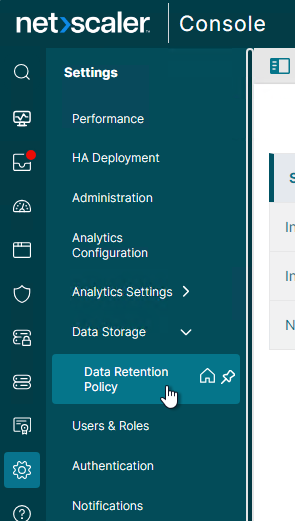
- Go to Settings > Data Storage Management > Data Retention Policy.
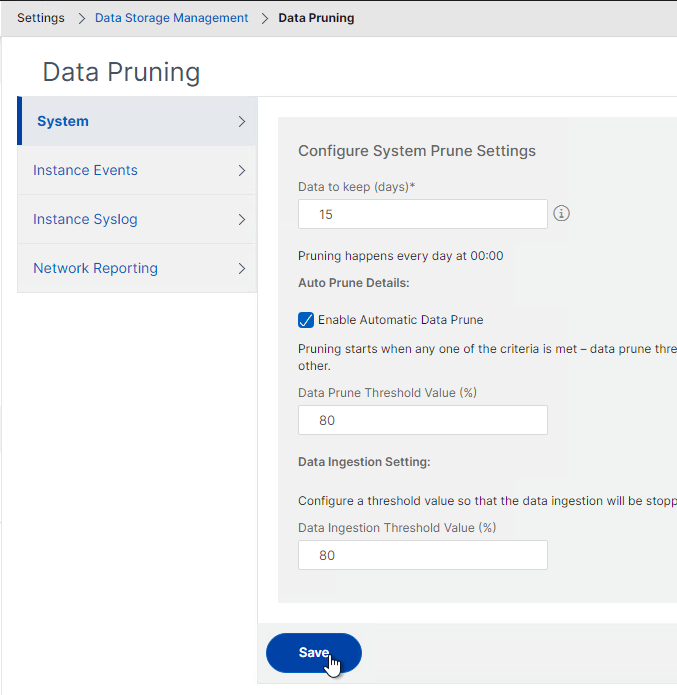
- System Pruning defaults to deleting System Events, Audit Logs, and Task Logs after 15 days. System events are generated by the NetScaler Console appliance, which is different than Instance events (SNMP traps) that are generated by NetScaler ADC appliances.
- If you change anything on these pages, click the Save button before switching to a different tab/node/page.
- NetScaler Console can initiate a purge automatically as the database starts to get full.
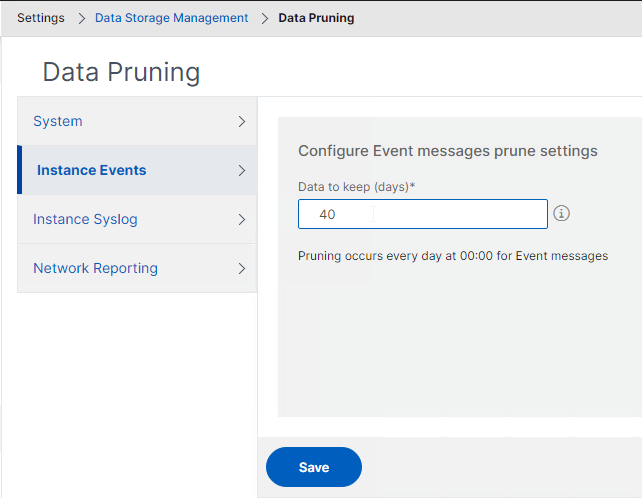
- Instance Events page controls when instance SNMP traps are pruned, which defaults to 40 days.
Backup Settings
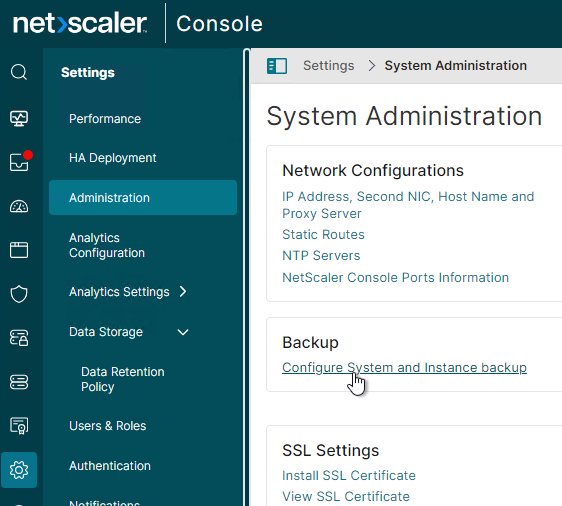
- In Settings > Administration, in the middle column, under Backup, click Configure System and Instance backup.
- System Backup Settings defines how many NetScaler Console backups you want to keep. These are NetScaler Console backups, not NetScaler ADC backups.
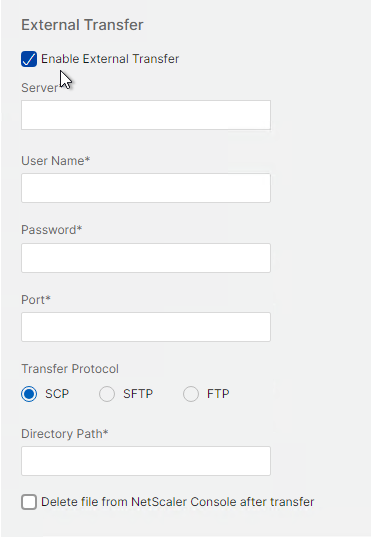
- There’s an option for External Transfer.
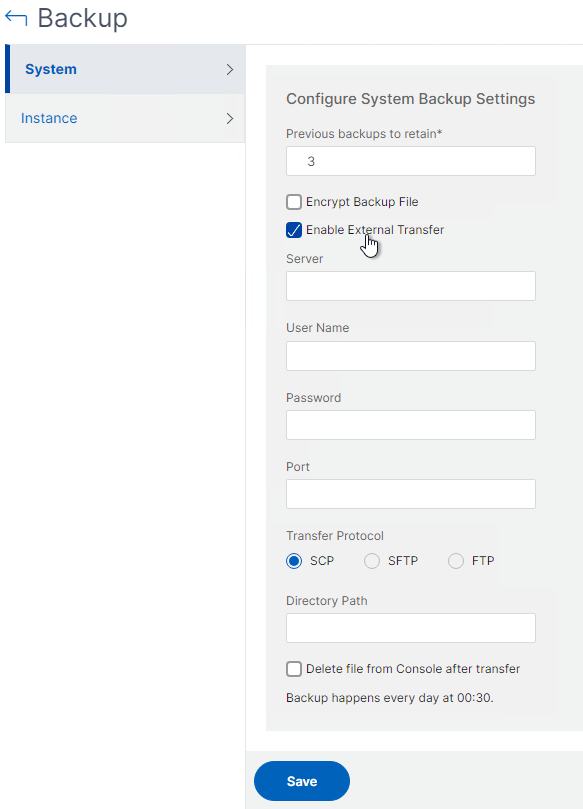
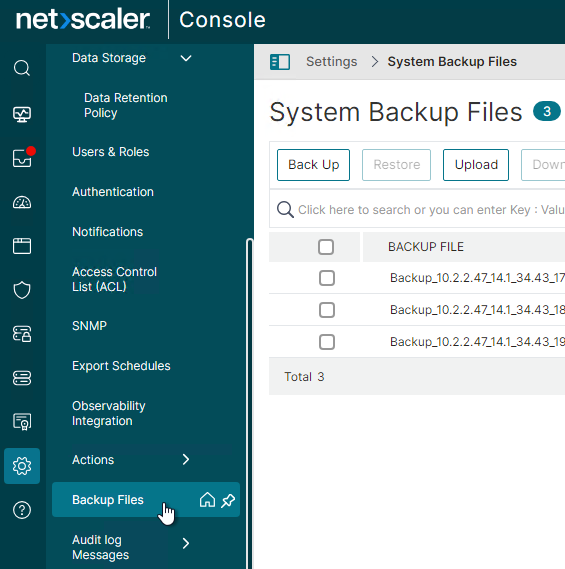
- NetScaler Console System backups (not Instance Backups) are at Settings > Backup Files.
- There’s an option for External Transfer.
- The Instance page lets you configure how often the instances are backed up.
- You probably want to increase the number of instance backups or decrease the backup interval. The backups are quite small (e.g. 700 KB).
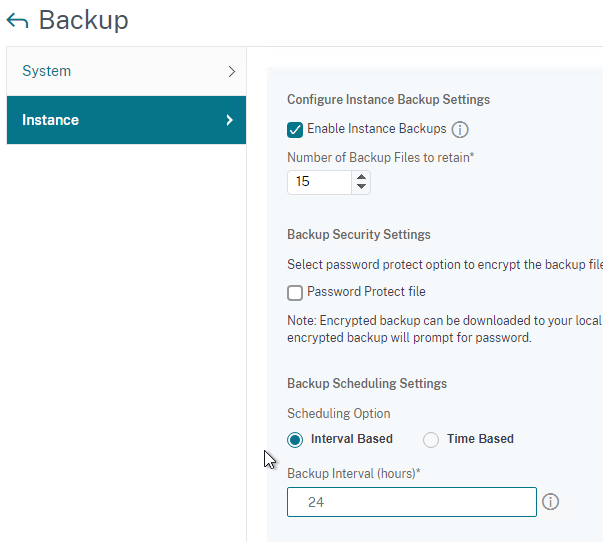
- There is an option to perform a backup whenever the NetScaler ADC configuration is saved.
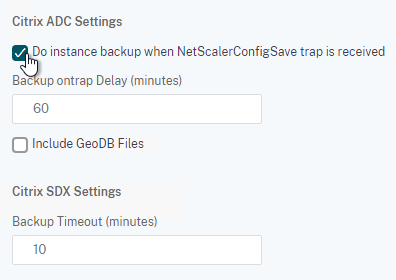
- The Enable External Transfer checkbox lets you transfer the backups to an external system so it can be backed up by your backup tool.
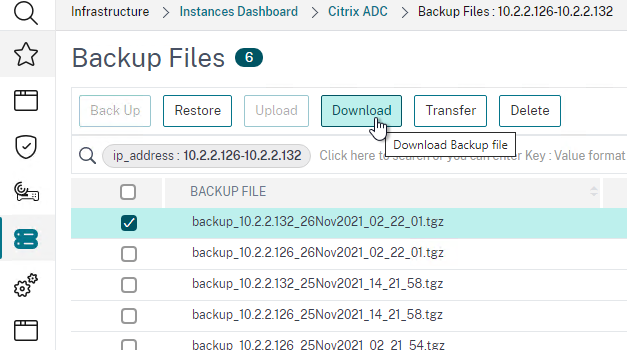
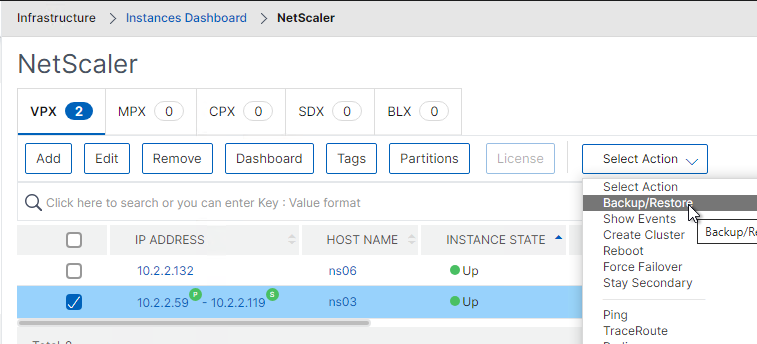
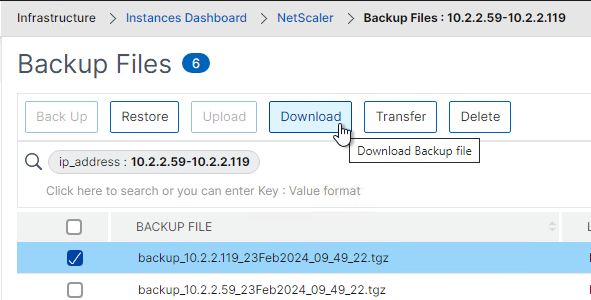
- Instance backups can be found at Infrastructure > Instances > NetScaler. Right-click an instance and click Backup/Restore.
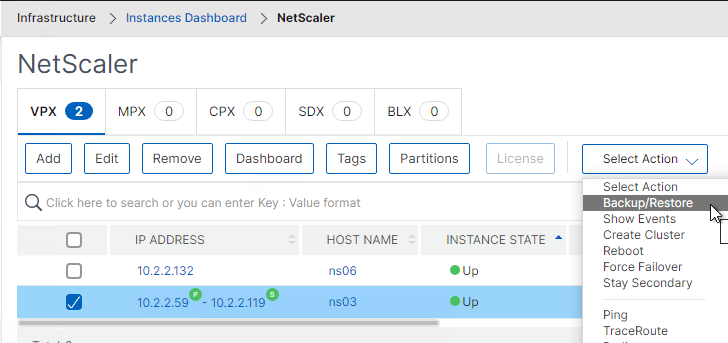
- You can Restore a backup, Download the backup, or Transfer it to an external system.
- You probably want to increase the number of instance backups or decrease the backup interval. The backups are quite small (e.g. 700 KB).
Analytics Settings
- There are more settings at Settings > Analytics Settings.
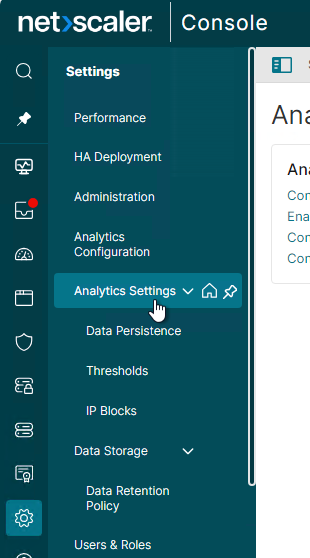
- ICA/Gateway Session Timeout can be configured by clicking the link.
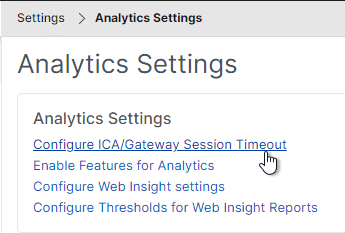
- If NetScaler Console doesn’t receive AppFlow records for a session, it will consider that session has got terminated in NetScaler ADC and stops monitoring that session further. The time for which NetScaler Console needs to wait before considering a session terminated is ICA session timeout. This is configurable in NetScaler Console, by default it is set to 15 minutes. (source = Citrix Discussions)
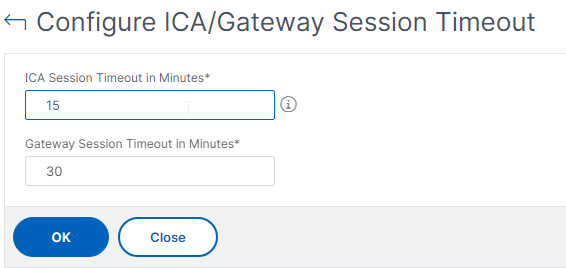
- If NetScaler Console doesn’t receive AppFlow records for a session, it will consider that session has got terminated in NetScaler ADC and stops monitoring that session further. The time for which NetScaler Console needs to wait before considering a session terminated is ICA session timeout. This is configurable in NetScaler Console, by default it is set to 15 minutes. (source = Citrix Discussions)
- Go to Applications > Dashboard.
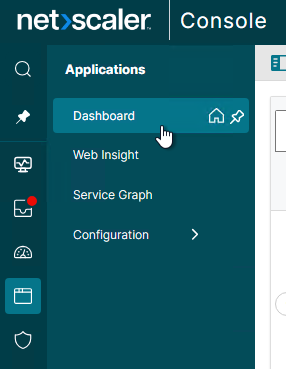
- On the top right, click the gear icon.
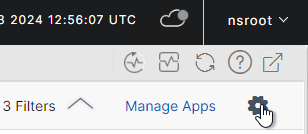
- Configure App Score factors and thresholds.
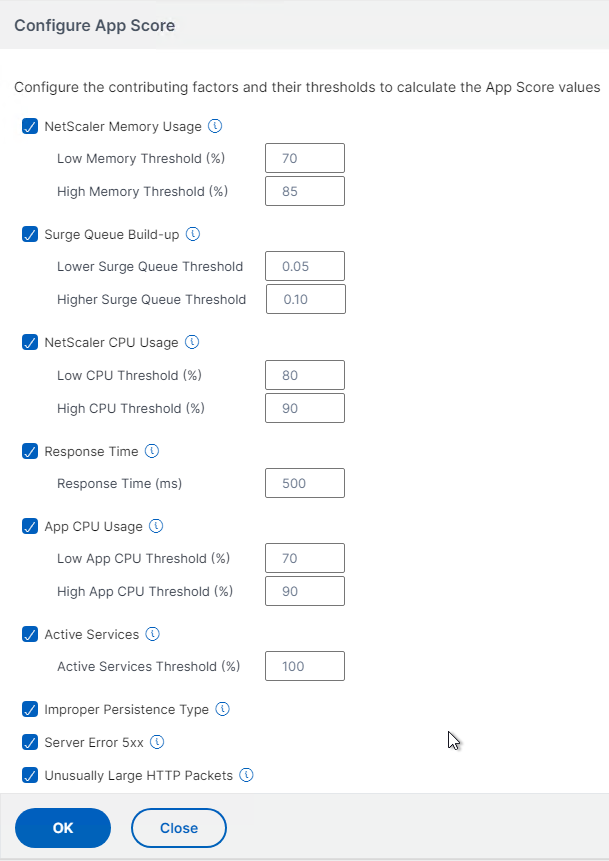
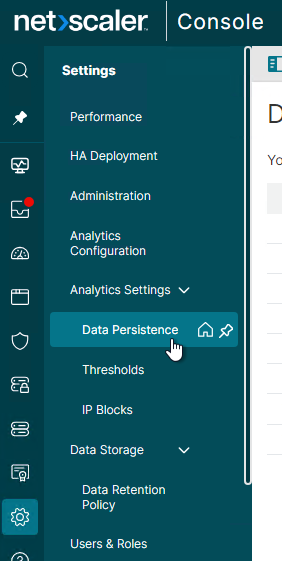
- Settings > Analytics Settings > Data Persistence lets you configure how long Analytics data is retained. Adjusting these values could dramatically increase disk space consumption.
- To see the current database disk usage, go to Settings > Data Storage.
- To see the current database disk usage, go to Settings > Data Storage.
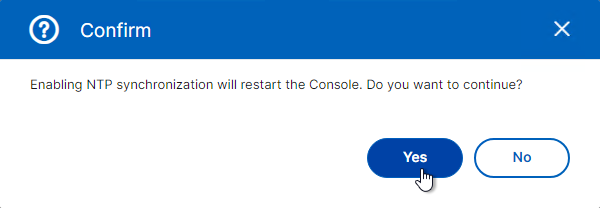
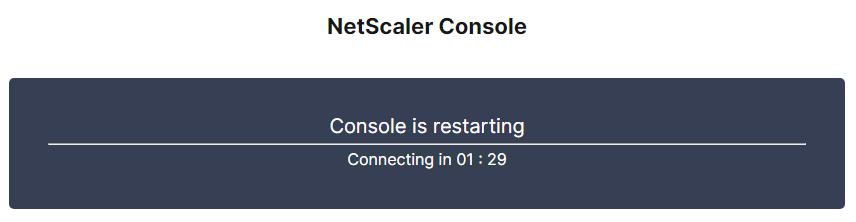
NTP Servers
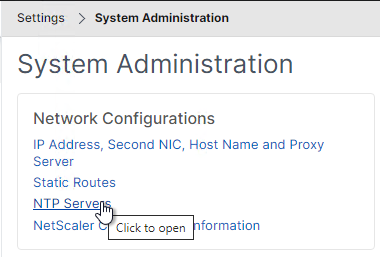
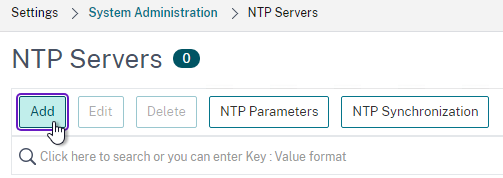
- On the left, click Settings > Administration.
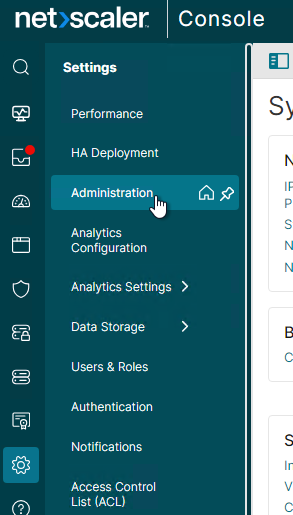
- On the right, click NTP Servers.
- Click Add.
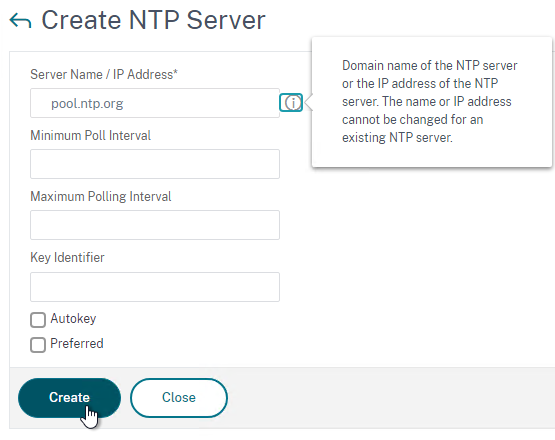
- Enter an NTP server and click Create.
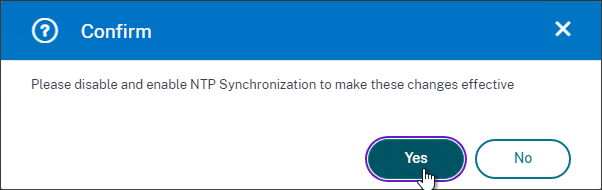
- After adding NTP servers, click the NTP Synchronization button.
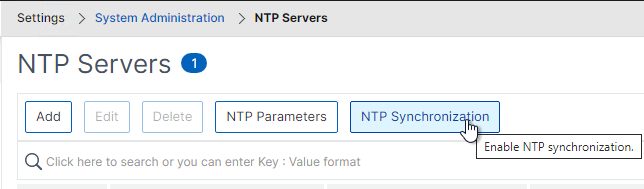
- Check the box next to Enable NTP Synchronization and click OK.
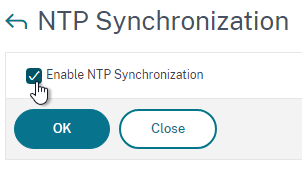
- Click Yes to restart.
Syslog
This is for syslog entries generated by NetScaler Console server, and not for syslog entries generated by the instances.
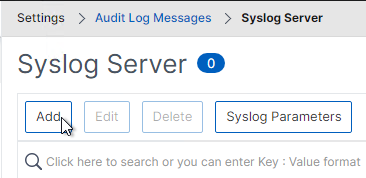
- Go to Settings > NetScaler Console Audit Log Messages > Syslog Servers.
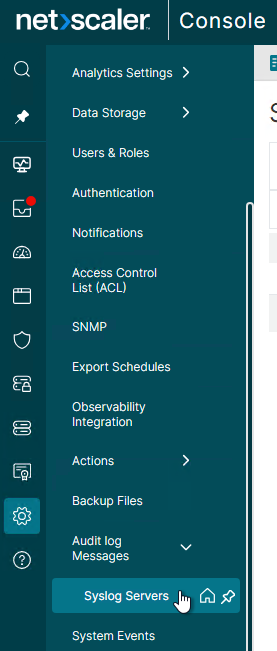
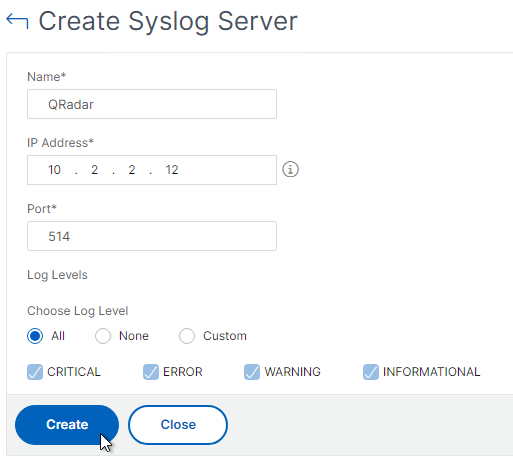
- On the right, click Add.
- Enter the syslog server IP address and select Log Levels. Click Create.
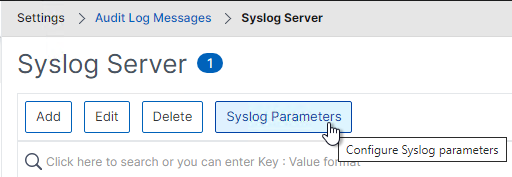
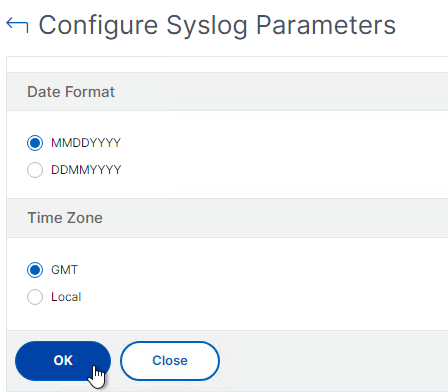
- You can click Syslog Parameters to change the timezone and date format.
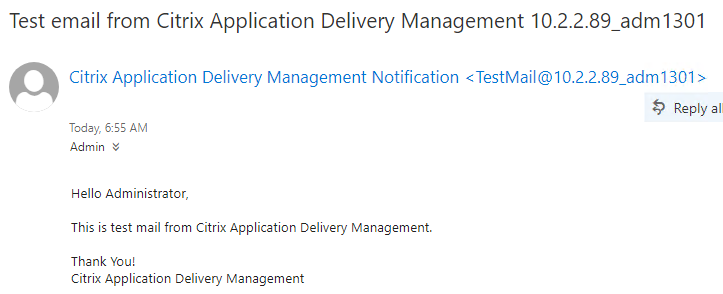
Email Notification Server
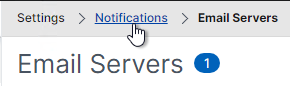
- Go to Settings > Notifications.
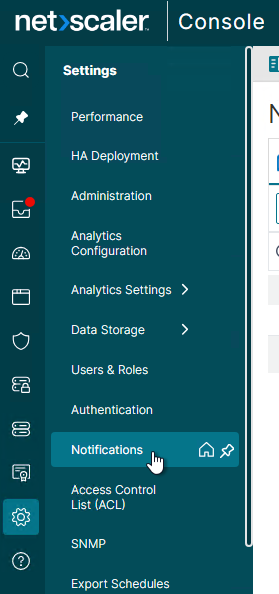
- On the right, on the Email tab, click the button named Email Servers.
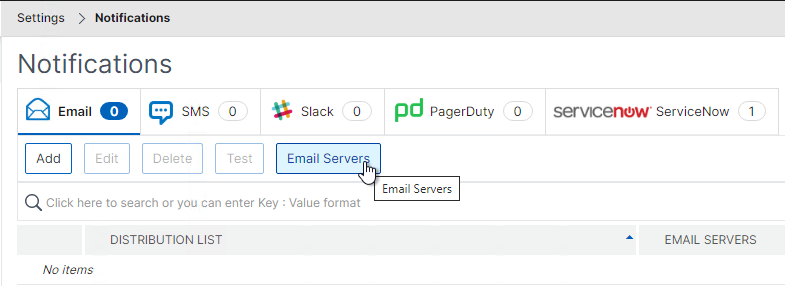
- Click Add.
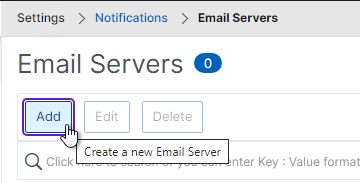
- Enter the SMTP Email server address and click Create.
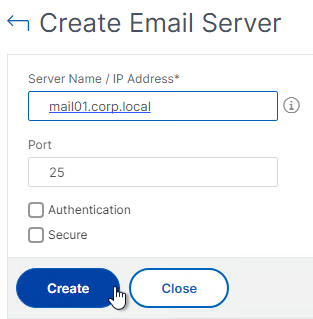
- Click Add.
- In the breadcrumb, click Notifications.
- On the right, on the Email tab, and click Add.
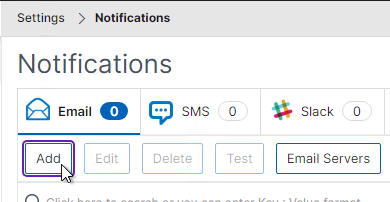
- Enter information for a destination distribution list and click Create.
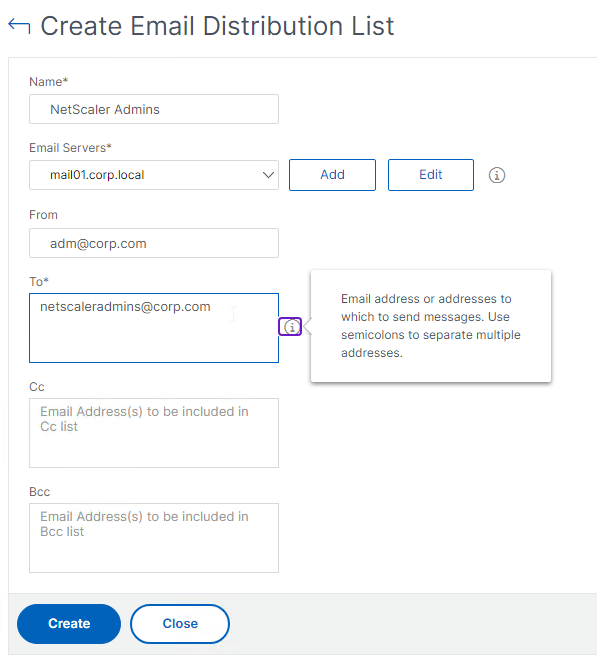
- Enter information for a destination distribution list and click Create.
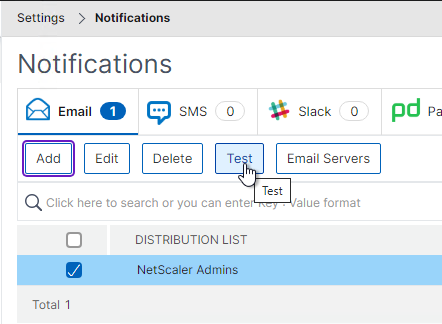
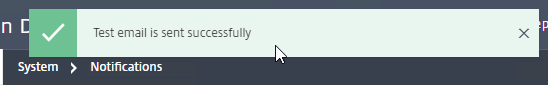
- You can highlight a Distribution List and click the Test button.
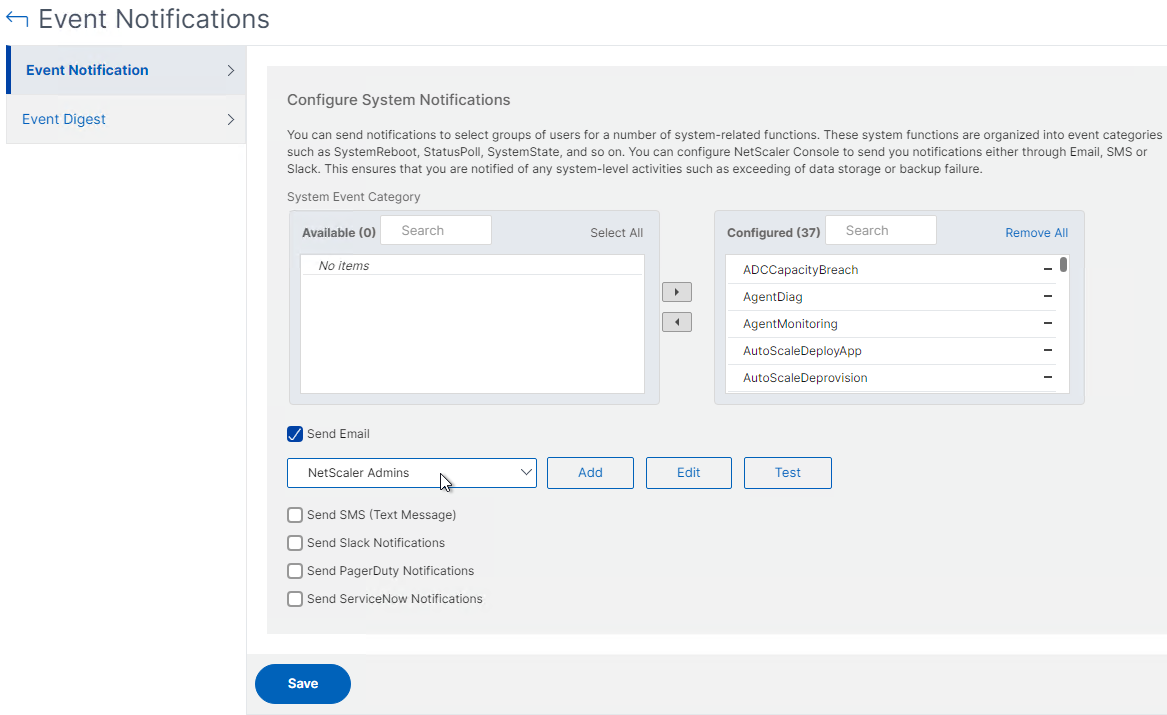
- On the left, click Settings > Administration.
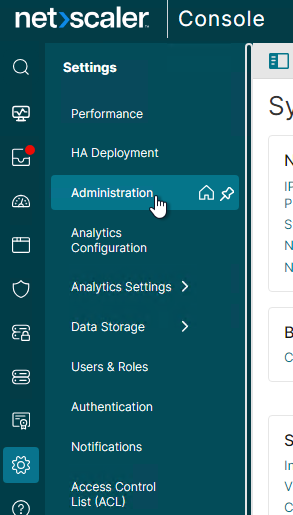
- On the right, click Change Event Notification and Digest.
- Move notification categories (e.g. UserLogin) to the right.
- Check the box next to Send Email. Select a notification distribution list. Then click Save.
Authentication
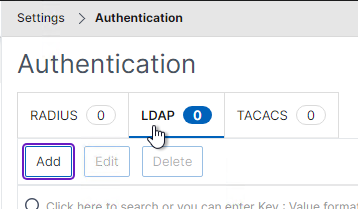
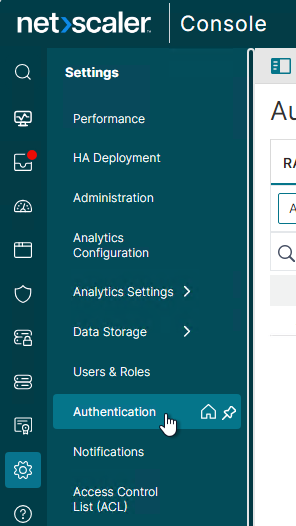
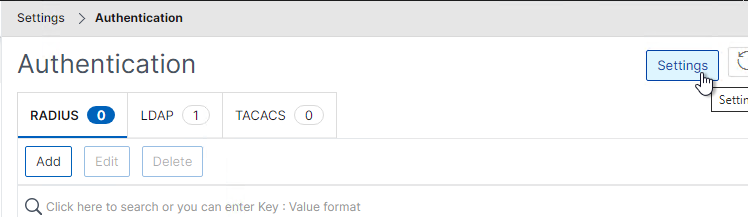
- Go to Settings > Authentication.
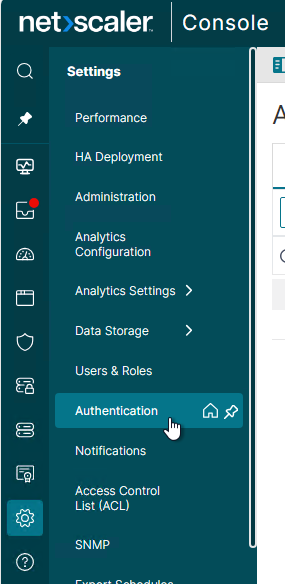
- On the right, switch to the tab named LDAP.
- Click Add.
- This is configured identically to NetScaler ADC.
- Enter a Load Balancing VIP for LDAP.
- Change the Security Type to SSL, and Port to 636. Scroll down.
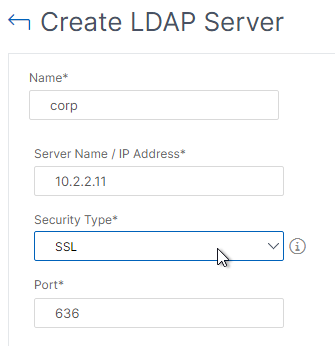
- Enter the Base DN in LDAP format.
- Enter the bind account credentials.
- Check the box for Enable Change Password.
- Click Retrieve Attributes and scroll down.
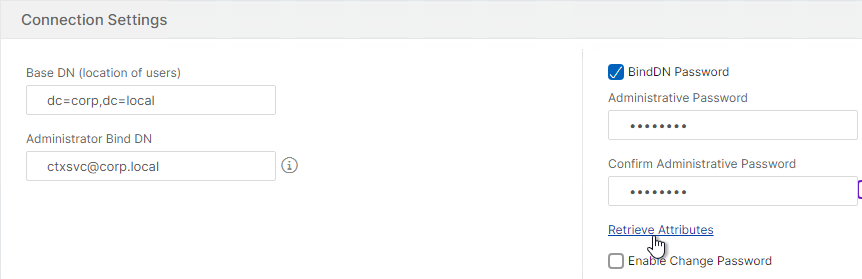
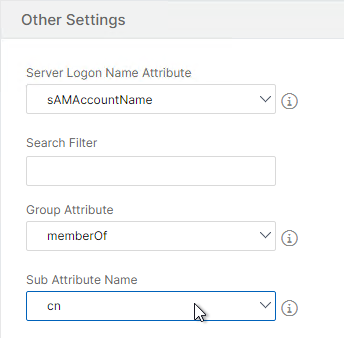
- For Server Logon Attribute, select sAMAccountName.
- For Group Attribute, select memberOf.
- For Sub Attribute Name, select cn.
- To prevent unauthorized users from logging in, configure a Search Filter. Scroll down.
- If desired, configure Nested Group Extraction.
- Click Create.

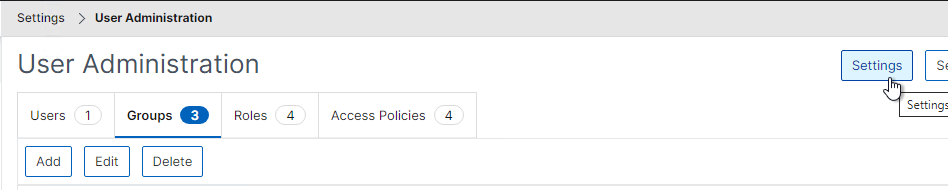
- On the left, go to Settings > Users & Roles.
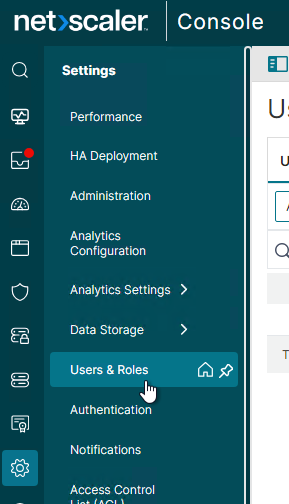
- On the right, click the tab named Groups.
- On the right, click Add.
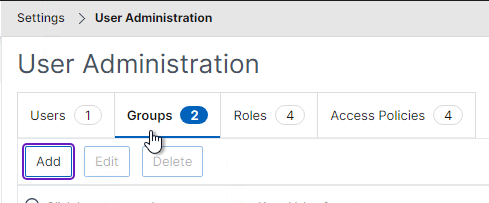
- Enter the case sensitive name of your NetScaler Console Admins AD group.
- Move the admin Role to the right.
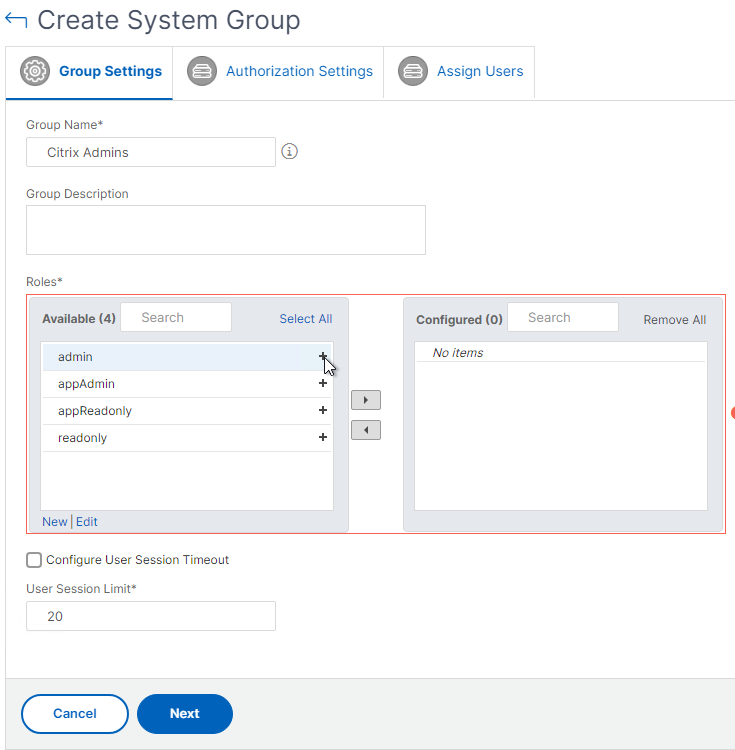
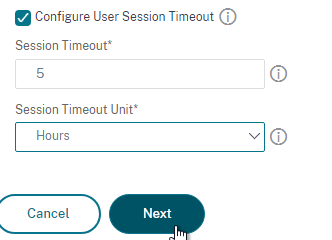
- The Configure User Session Timeout checkbox lets you configure a session timeout.
- Click Next.
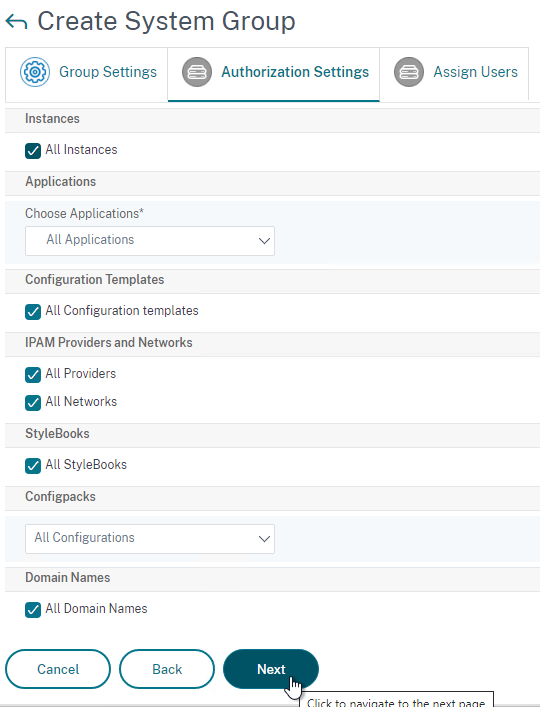
- On the Authorization Settings page, if you are delegating limited permissions, you can uncheck these boxes and delegate specific entities.
- All DNS Domain Names (GSLB) is an option for Stylebooks in ADM 12.1 build 49 and newer.
- Click Next.
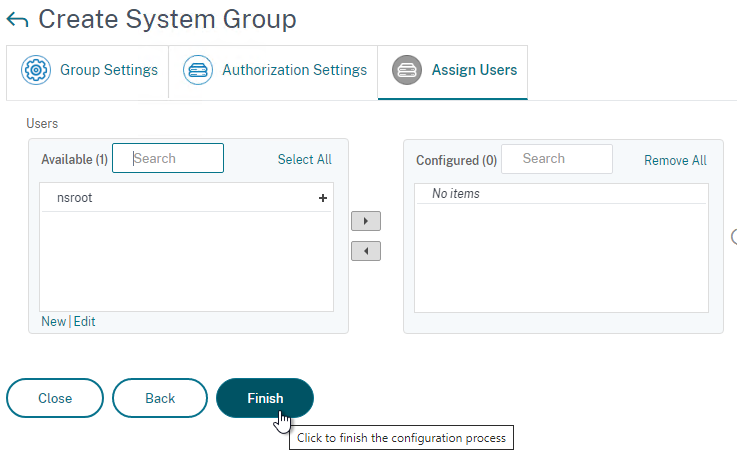
- In the Assign Users page, click Finish. Group membership comes from LDAP, so there’s no need to add local users.
- On the top right, click the button named Settings.
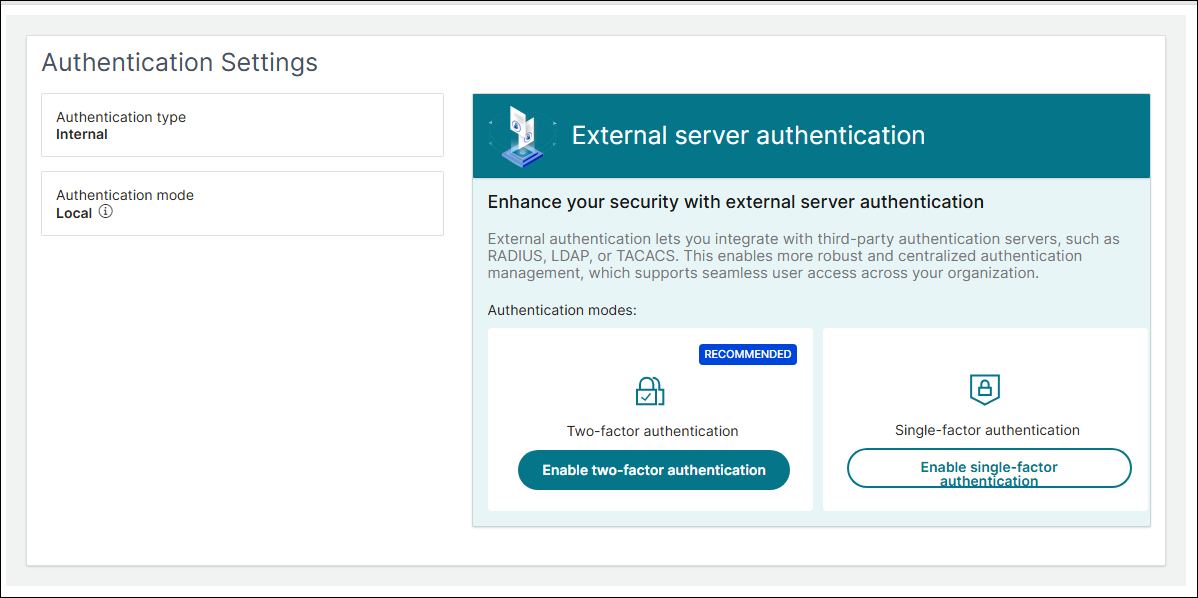
- NetScaler Console 14.1 build 43.50 and newer lets you configure two-factor authentication. NetScaler Docs.
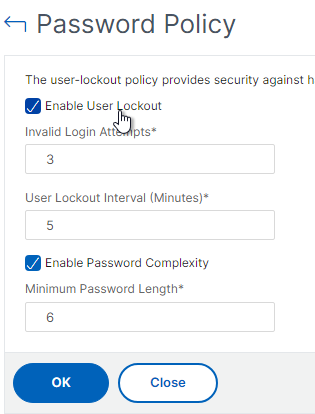
- If desired, check the box next to Enable User Lockout, and configure the maximum logon attempts. Click OK.
- NetScaler Console 14.1 build 43.50 and newer lets you configure two-factor authentication. NetScaler Docs.
- On the left, go to Settings > Authentication.
- On the top right, click the button named Settings.
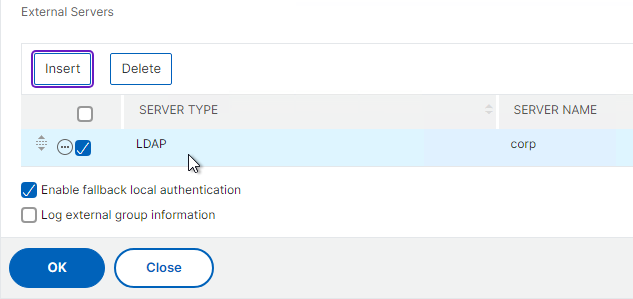
- Change the Server Type to EXTERNAL and click Insert.
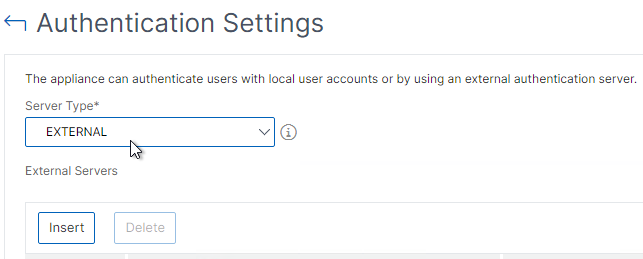
- Select the LDAP server you created and click OK.
- Make sure Enable fallback local authentication is checked and click OK.
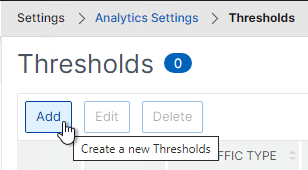
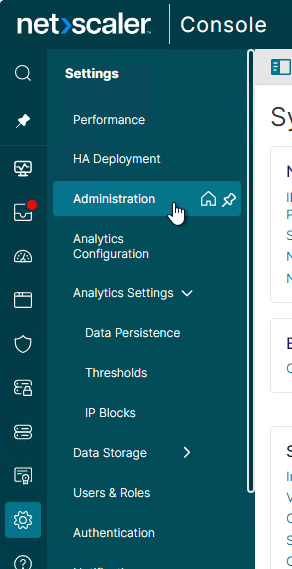
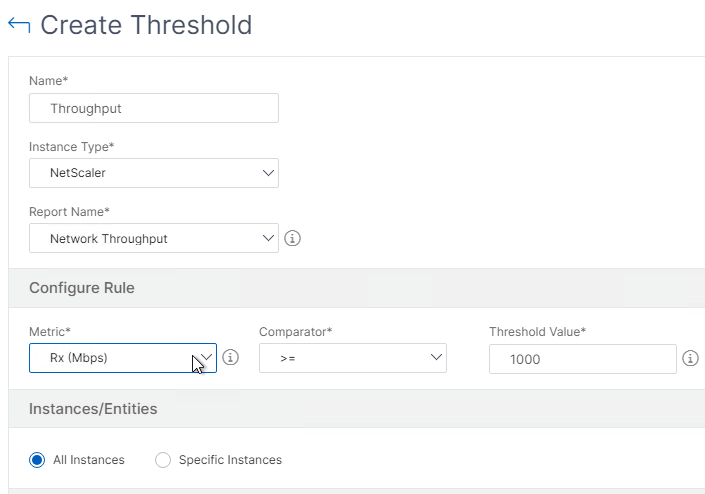
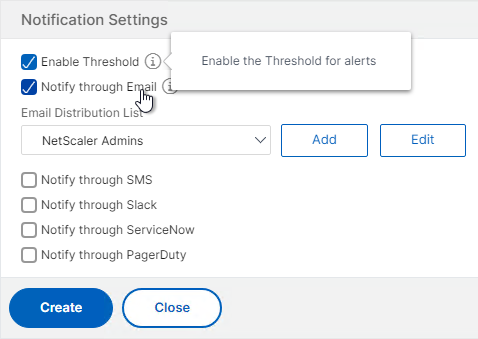
Analytics Thresholds
- Go to Settings > Analytics Settings > Thresholds.
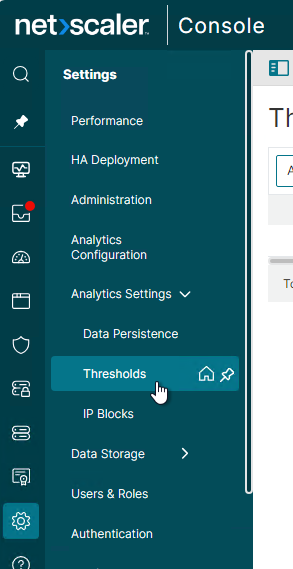
- On the right, click Add.
- Enter a name.
- Use the Traffic Type drop-down to select HDX, WEB, SECURITY, or APPANALYTICS.
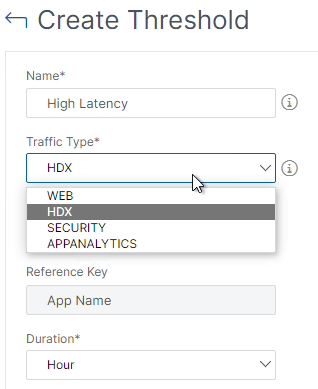
- Use the Entity drop-down to select a category of alerts. What you choose here determines what’s available as Metrics when you click Add Rule.
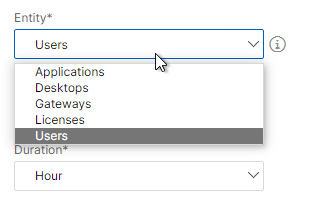
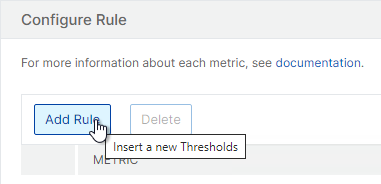
- Click Add Rule to select a metric and threshold.
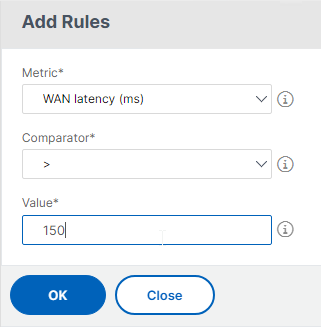
- To add multiple rules for multiple Entity types, simply change the Entity drop-down before adding a new rule.
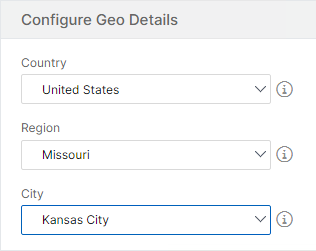
- If the Traffic Type is HDX, and the Entity drop-down is set to Users, on the bottom in the Configure Geo Details section, you can restrict the rule so it only fires for users for a specific geographical location.
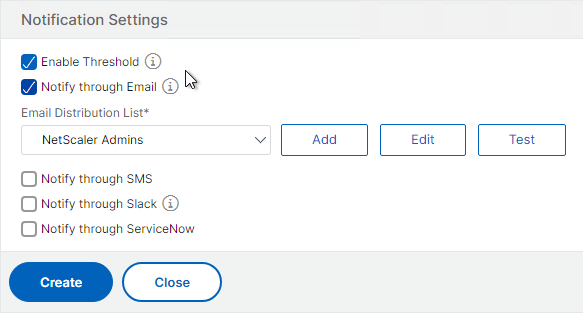
- In the Notification Settings section, check the box to Enable Threshold.
- Check the box to Notify through Email, and select an existing Email Distribution List.
- Click Create.
Private IP Blocks
You can define Geo locations for internal subnets.
- Go to Settings > Analytics Settings > IP Blocks.
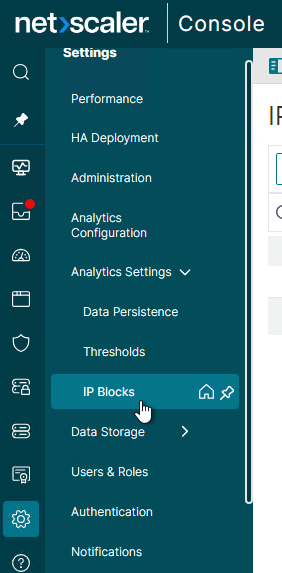
- On the right, click Add.
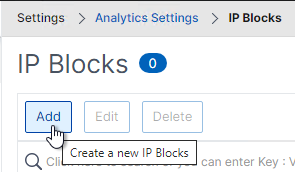
- In the Create IP Blocks page:
- Enter a name for the subnet.
- Enter the starting and ending IP address.
- Select a Geo Location (Country, Region, City). As you change the fields, the coordinates are automatically filled in.
- Click Create.
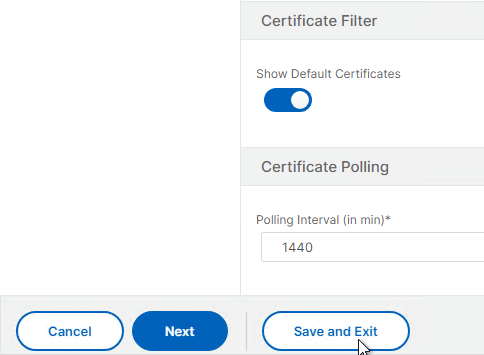
SSL Certificate Expiration Notification
SSL Dashboard can notify you when certificates will expire soon.
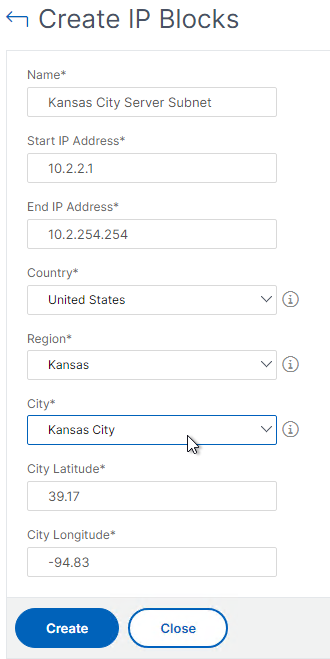
- In the NetScaler Console menu, expand Infrastructure and click SSL Dashboard.
- On the top right, click the button named Settings.
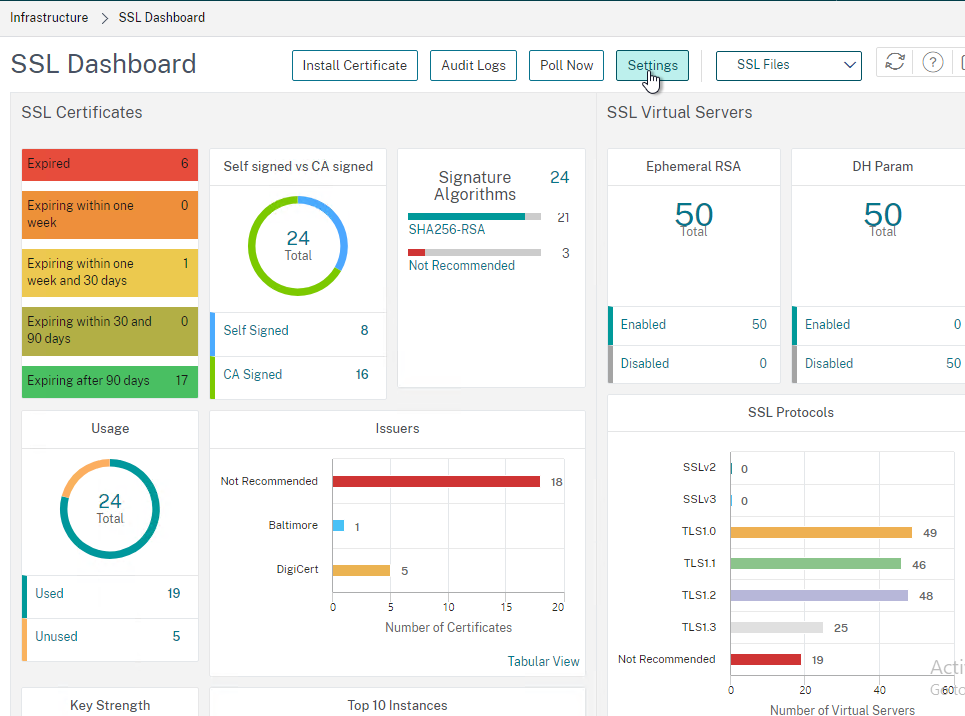
- In the Certificate is expiring in (days) field, enter the number of days before expiration that you want to receive a notification. The default is 30 days.
- Check one of the boxes (e.g. Email) below How would you like to be notified.
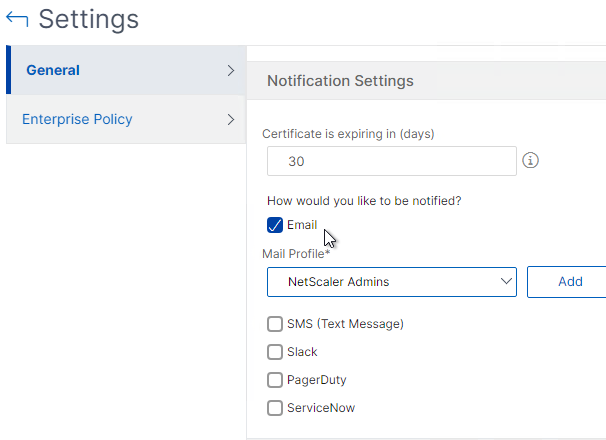
- Select a notification profile (e.g. Mail Profile) or Add one.
- Click Save and Exit or click Next to see more SSL Dashboard settings.
Instance Email Alerts (SNMP Traps)
You can receive email alerts whenever a NetScaler ADC appliance sends a critical SNMP trap.
- On the left, go to Infrastructure > Events > Rules.
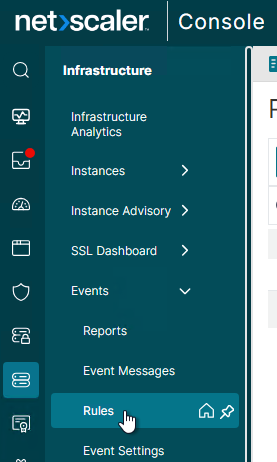
- On the right, click Add.
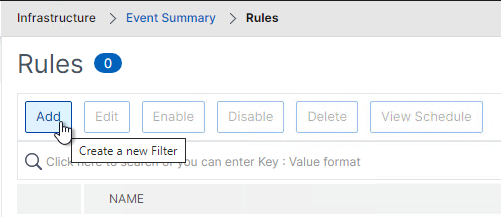
- Give the rule a name.
- Move Severity filters (e.g. Major, Critical) to the right by clicking the plus icon next to each Severity.
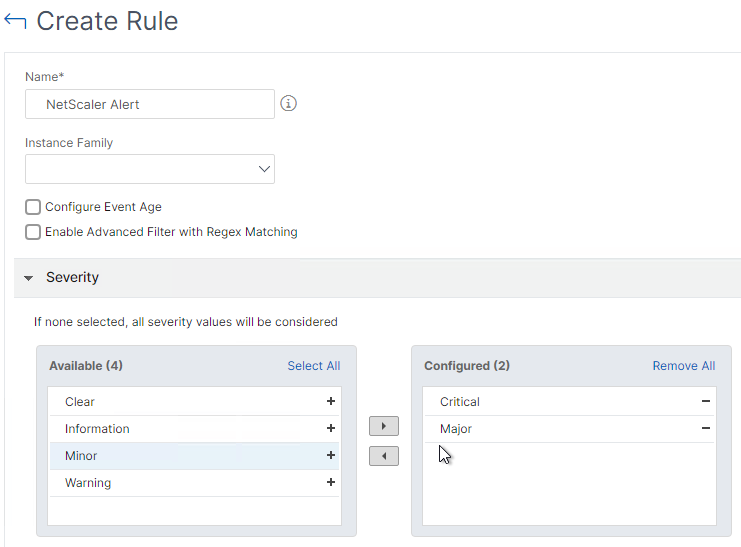
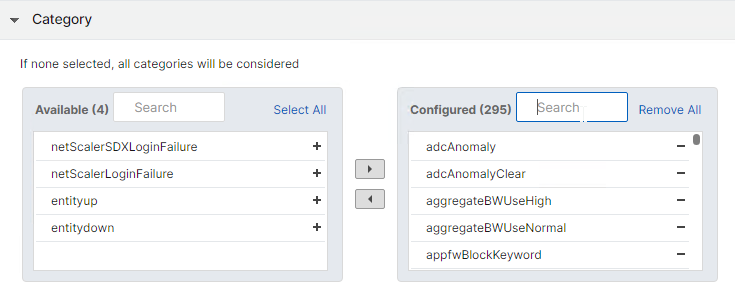
- While scrolling down, you can configure additional alert filters. Leaving them blank will alert you for all categories, objects, and instances. If you want to exclude some Categories (e.g., entitydown), then move all Categories to the right and move the excluded categories back to the left.
- On the bottom of the page, in the Event Rule Actions section, click Add Action.
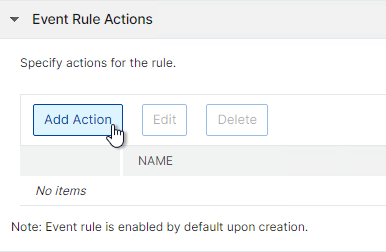
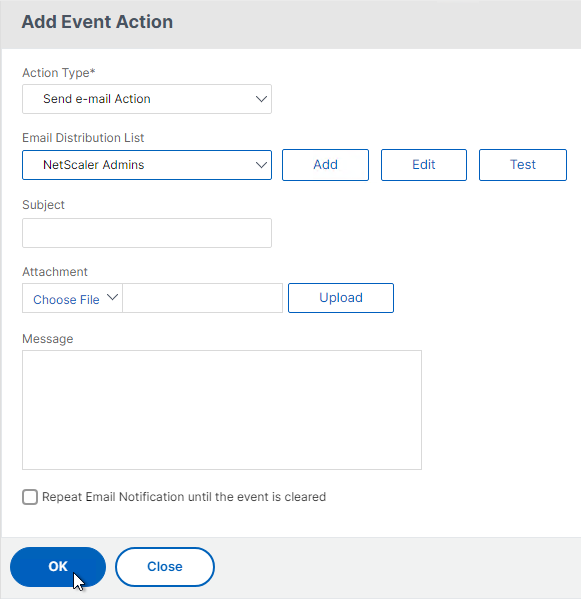
- In the Add Event Action page:
- Select an Action Type (e.g. Send e-mail Action).
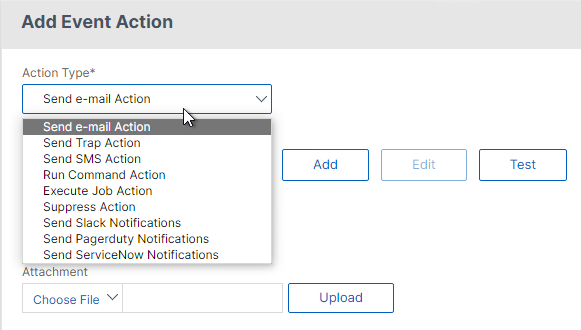
- Select the recipients (or click the Add button to add recipients).
- Optionally, enter a Subject and/or Message.
- If you enter a Subject, you can check Prefix severity, category, and failure object information to the custom email subject.
- Emails can be repeated by selecting Repeat Email Notification until the event is cleared.
- Select an Action Type (e.g. Send e-mail Action).
- Click OK.
- Then click Create to finish creating the event rule.

- See the Event Management section at All how to articles at NetScaler Docs.
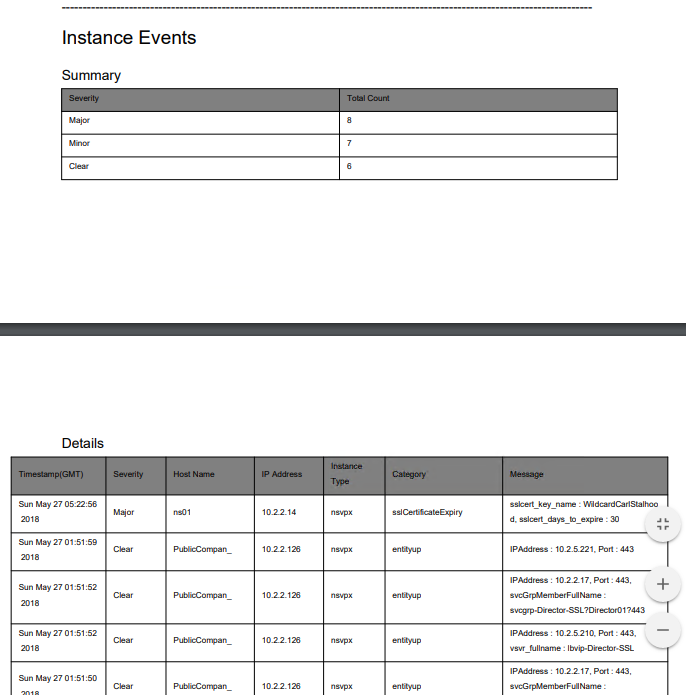
Events Digest
NetScaler Console can email you a daily digest (PDF format) of system and instance events.
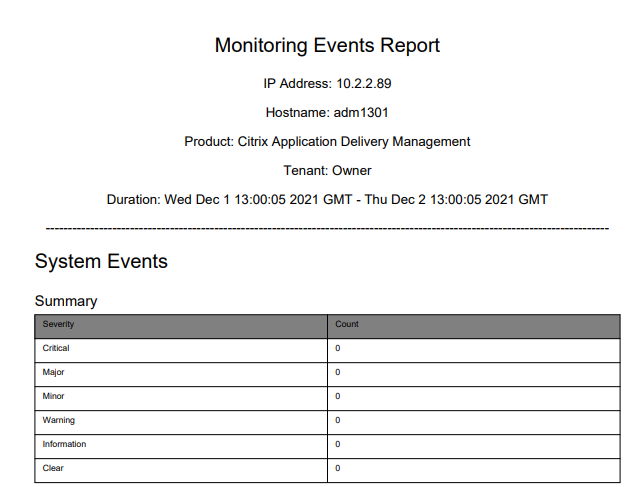
To enable the daily digest:
- Go to Settings > Administration.
- On the right, click Configure Event Notification and Digest.
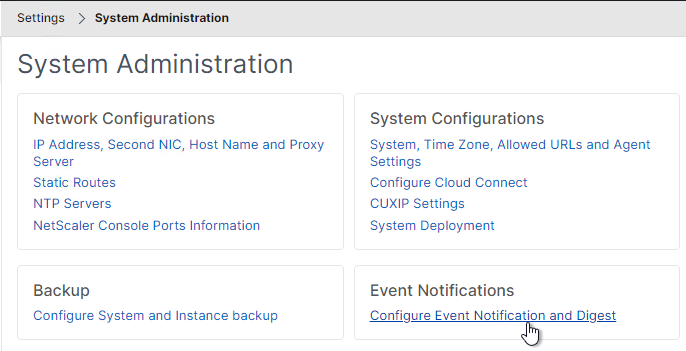
- Switch to the Event Digest page.
- Uncheck the box next to Disable Event Digest.
- Configure the other settings as desired and click OK.
Director Integration
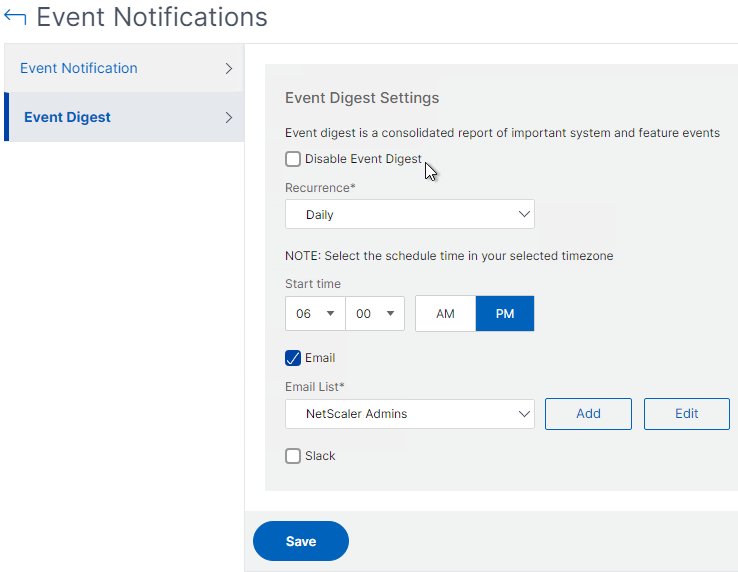
Integrating NetScaler Console with Director adds Network tabs to Director’s Trends and Session Details views. Citrix Blog Post Configure Director with Netscaler Management & Analytics System (MAS)
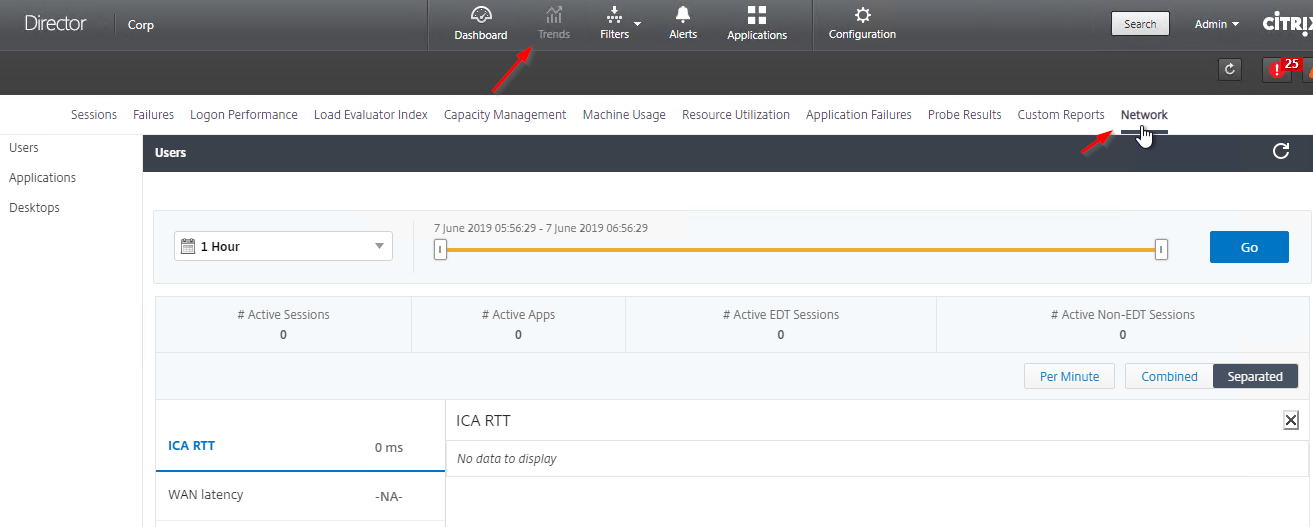
Requirements:
- Citrix Virtual Apps and Desktops (CVAD) must be licensed for Premium Edition (formerly known as Platinum Edition). This is only required for the Director integration. Without Premium, you can still access the HDX Insight data by visiting the NetScaler Console web site instead of from Director.
- Director must be 7.11 or newer for NetScaler Console support.
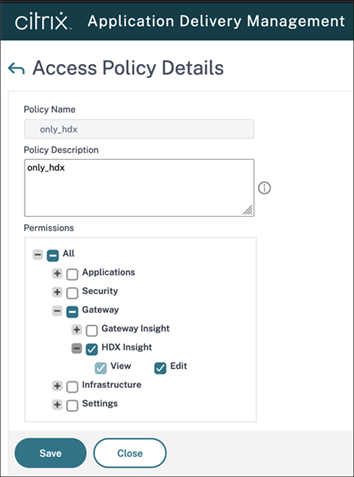
To link Citrix Director with NetScaler Console:
- On the Director server, run C:\inetpub\wwwroot\Director\tools\DirectorConfig.exe /confignetscaler.
- Enter credentials for a user that only has HDX Insight permissions.
- If HTTPS Connection (recommended), the NetScaler Console certificate must be valid and trusted by both the Director Server and the Director user’s browser.
- Enter 1 for NetScaler Console (formerly Insight).
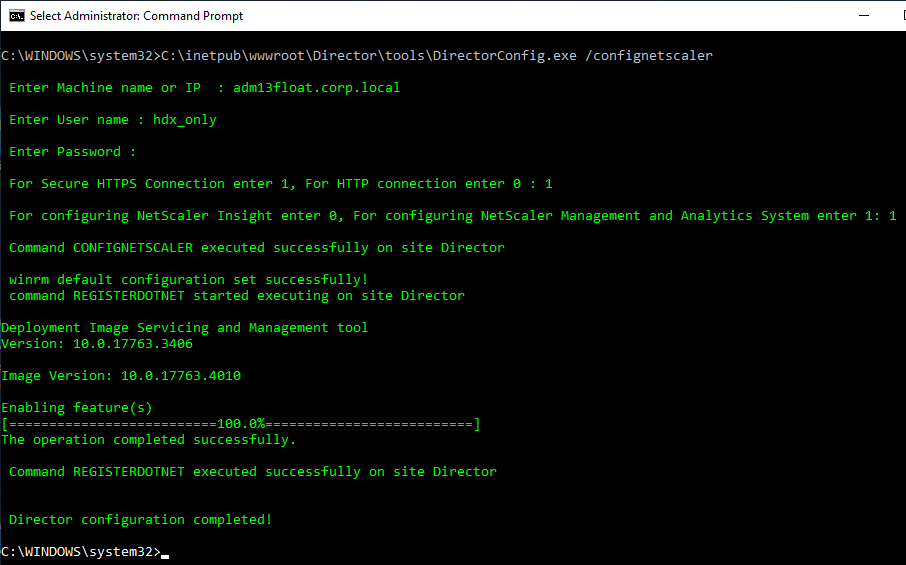
- Do this on both Director servers.
Use NetScaler Console
Infrastructure
Everything under the Infrastructure node is free.
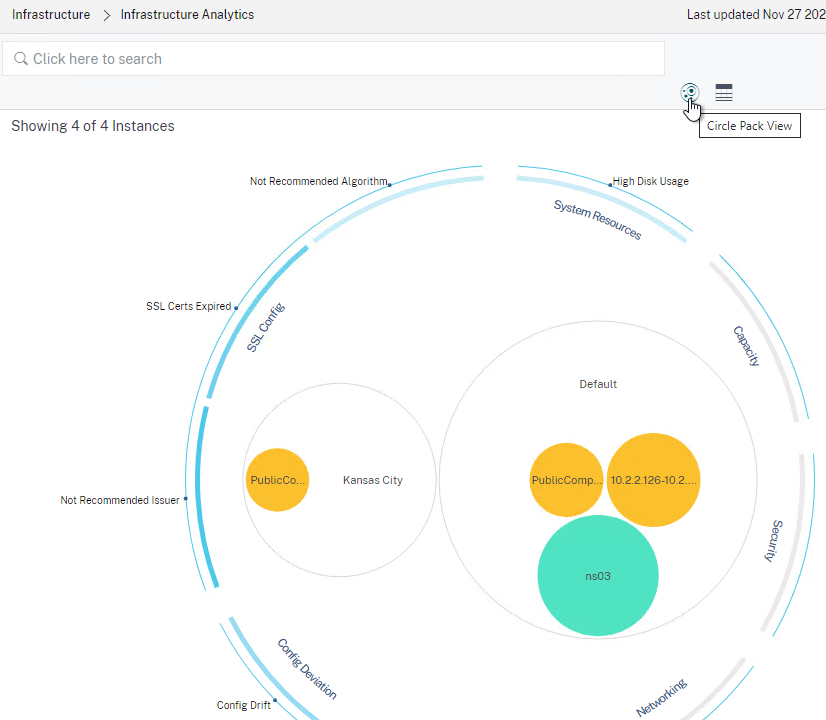
Infrastructure Analytics – there’s an Infrastructure Analytics node under the Infrastructure node. For details, see Infrastructure Analytics at NetScaler Docs.
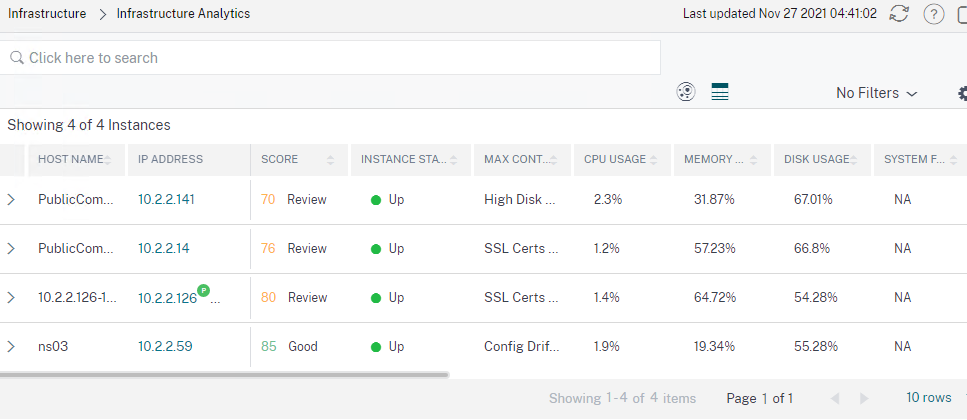
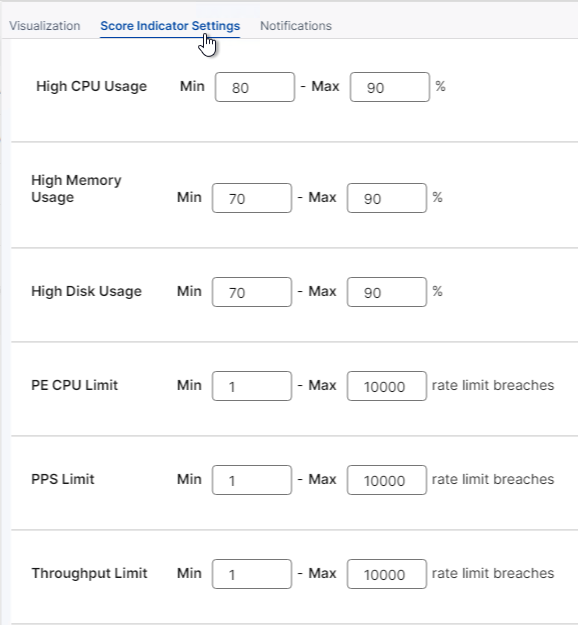
- On the top right, the gear icon above the table shows the Settings Panel.
- The tab named Score Indicator Settings lets you adjust how Infrastructure Analytics scores instance CPU, Memory, Disk, etc.
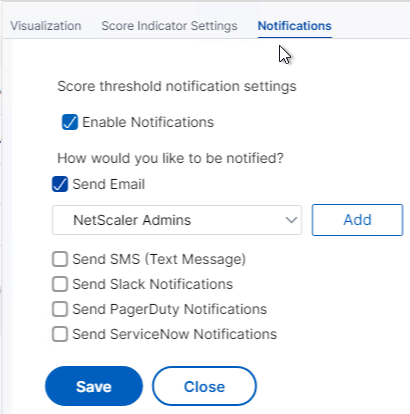
- The Notifications tab lets you be notified when score thresholds are crossed.
- You can click the Circle Pack button to change to the Circle Pack view.
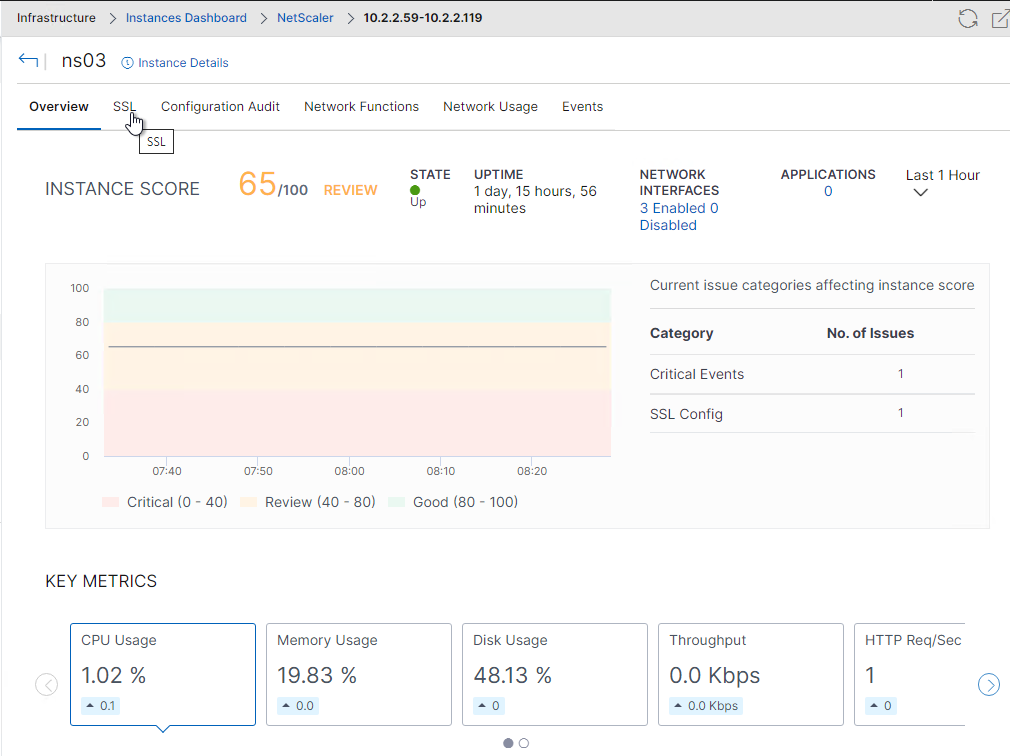
At Infrastructure > Instances > NetScaler, select an instance and view its Dashboard.
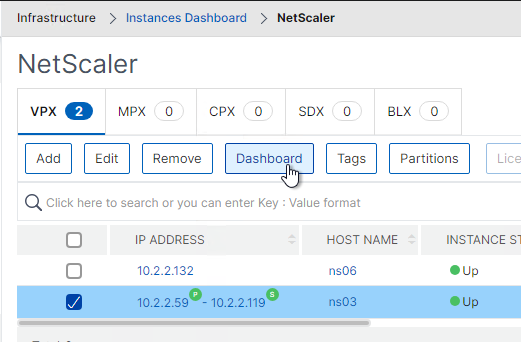
- The Instance Dashboard has tabs.
Backups are available by selecting an instance and clicking Backup/Restore.
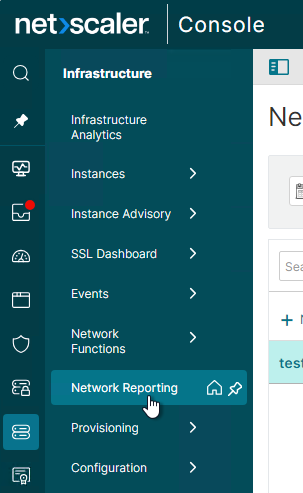
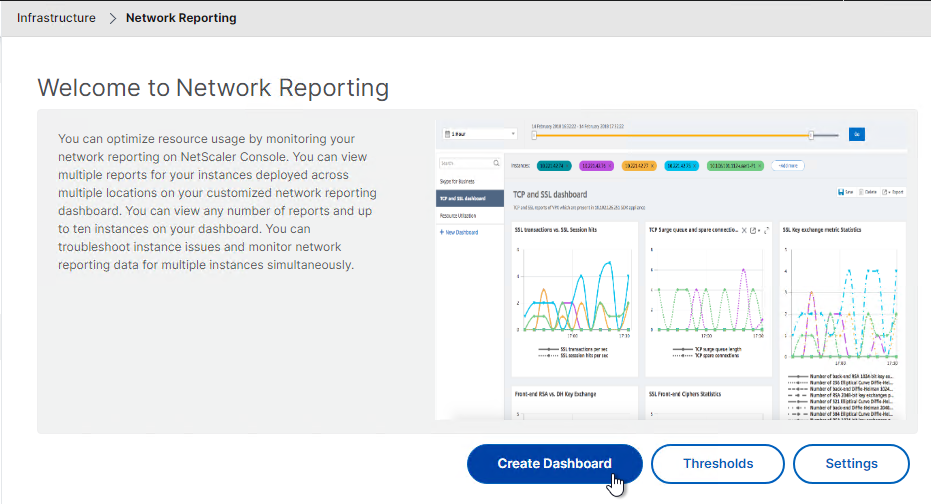
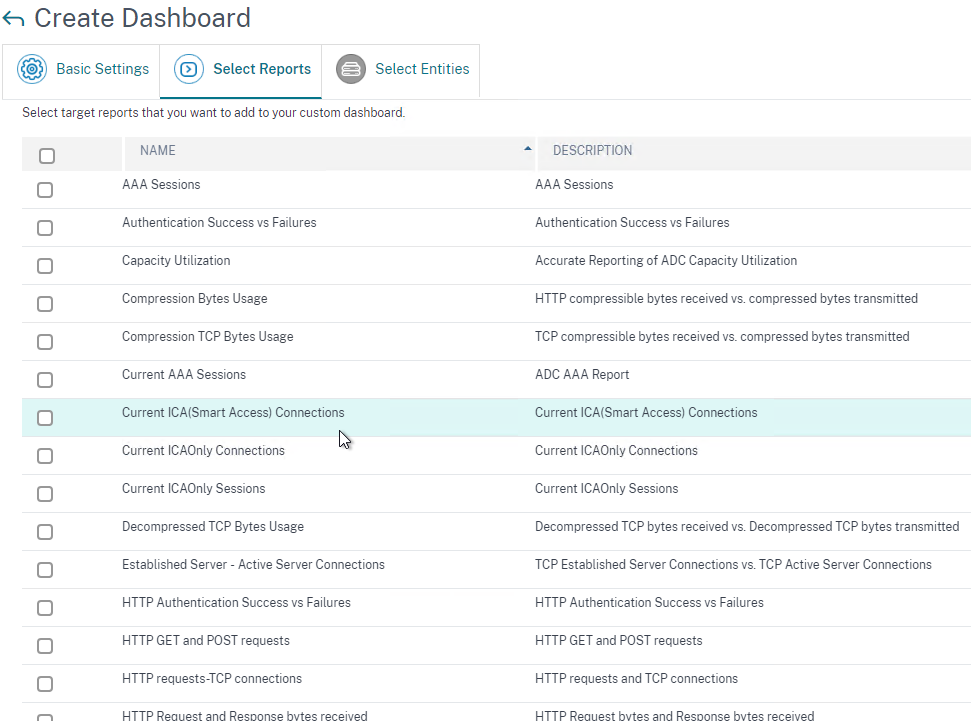
Infrastructure > Network Reporting lets you create Dashboards where you can view Instance performance data.
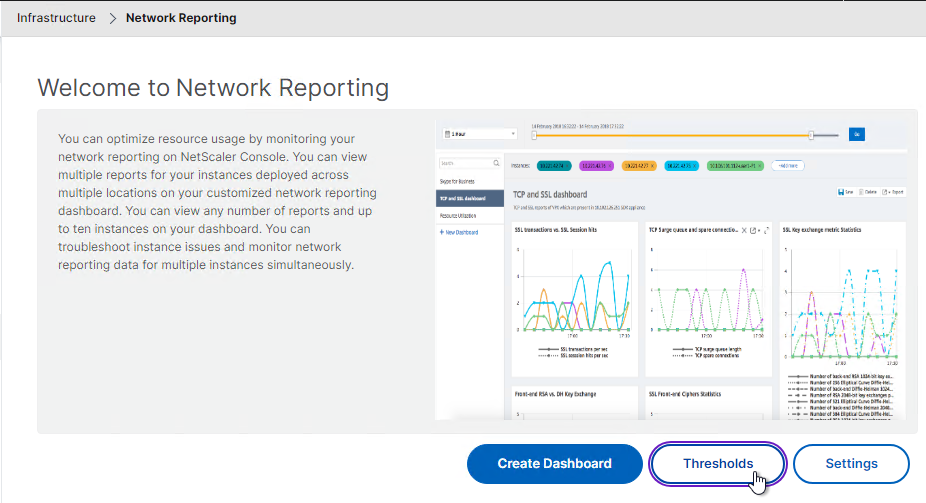
Infrastructure > Network Reporting has a Thresholds button that lets you create thresholds when counters cross a threshold. For example, you might want a notification when Throughput gets close to the licensed limit.
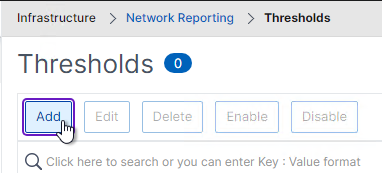
At the bottom of the threshold are Notification Settings.
Configuration Record and Play
Use NetScaler Console to record a configuration change on one instance and push the change to other instances.
- Go to Infrastructure > Configuration > Configuration Jobs.
- On the right, click Create Job.
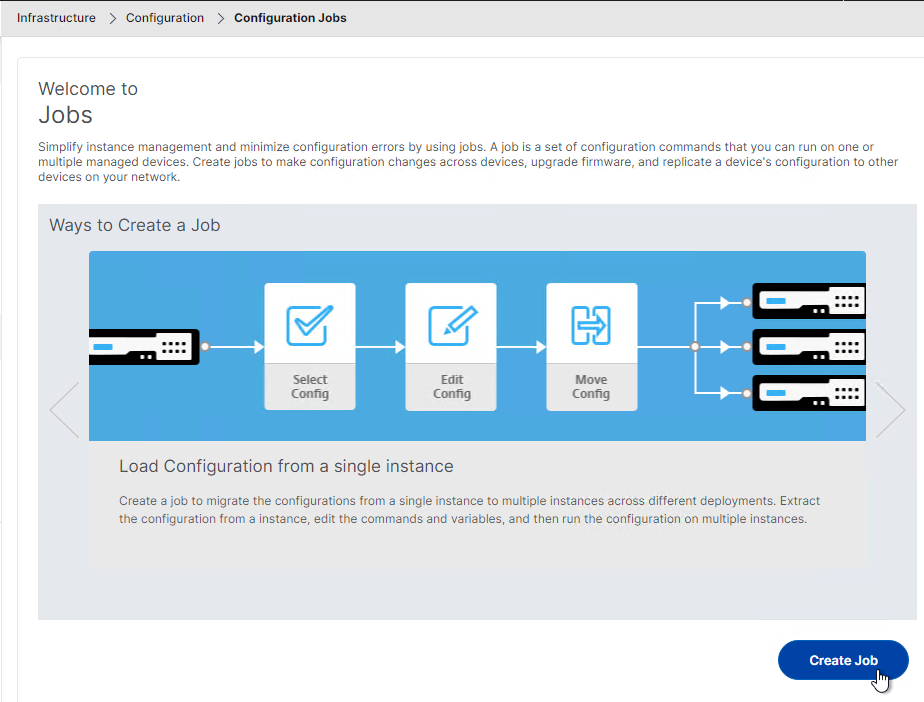
- Give the job a name.
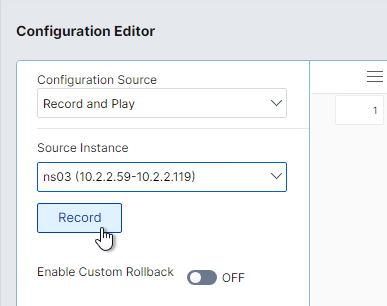
- Change the Configuration Source drop-down to Record and Play.
- Change the Source Instance drop-down to the instance you want to record.
- Click Record.
- You might have to allow pop-ups in your browser.
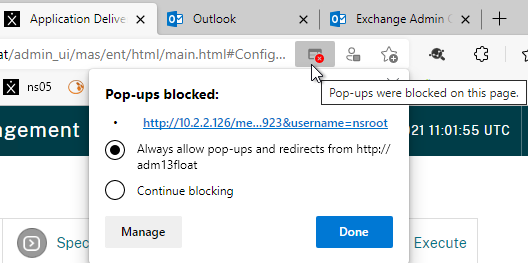
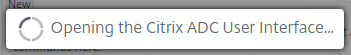
- NetScaler Console opens the instance GUI. Make changes as desired.
- When done, go back to NetScaler Console and click Stop.
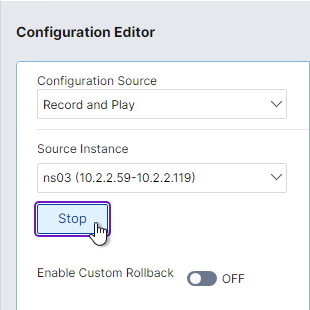
- NetScaler Console retrieves the changed config.
- On the left, you’ll see the changed commands. Drag them to the right.
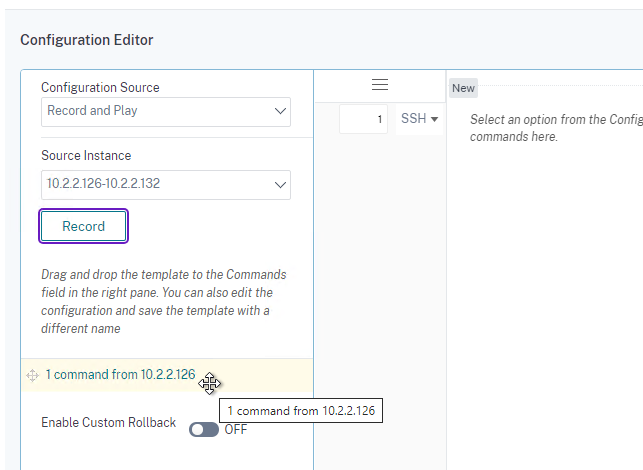
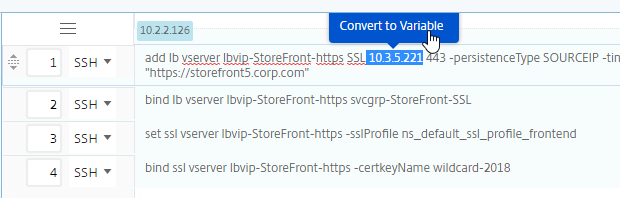
- On the right, you can change instance-specific values to variables by simply highlighting the values. This allows you to change the values for each instance you push this config to.
- Proceed through the rest of the Configuration Job wizard like normal. You’ll select instances, specify variable values for each instance, and schedule the job.
Analytics and Applications
The AppFlow Analysis tools (e.g., HDX Insight) are located under the Applications, Security, and Gateway nodes. See Viewing HDX Insight Reports and Metrics at NetScaler Docs.
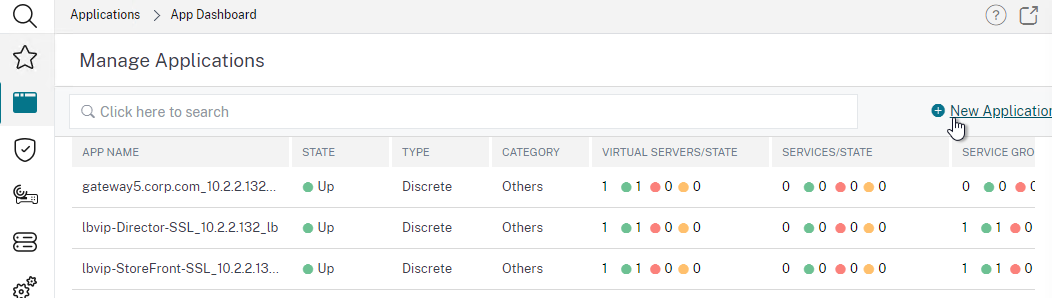
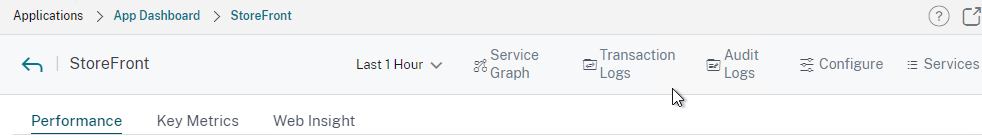
Applications > Dashboard automatically includes all Virtual Servers.
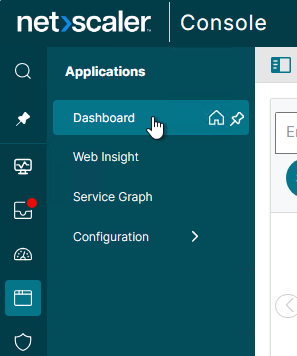
- On the top right, click Manage Apps to add a custom group of Virtual Servers together into an application. The grouped Virtual Servers are removed from the Others list.
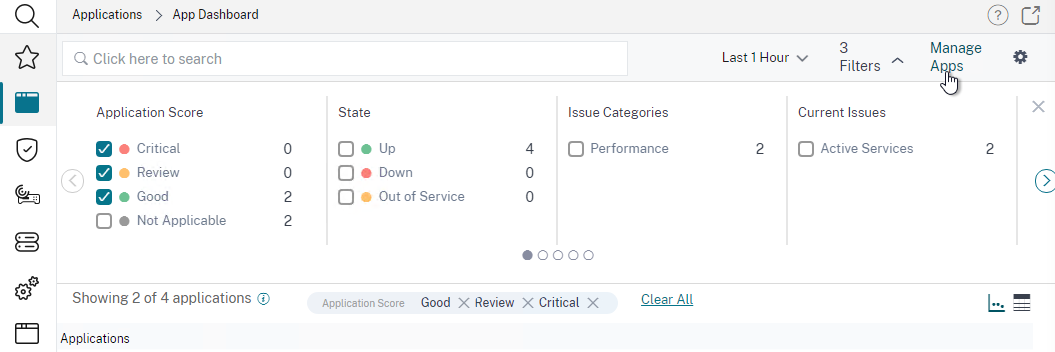
- Click New Application.
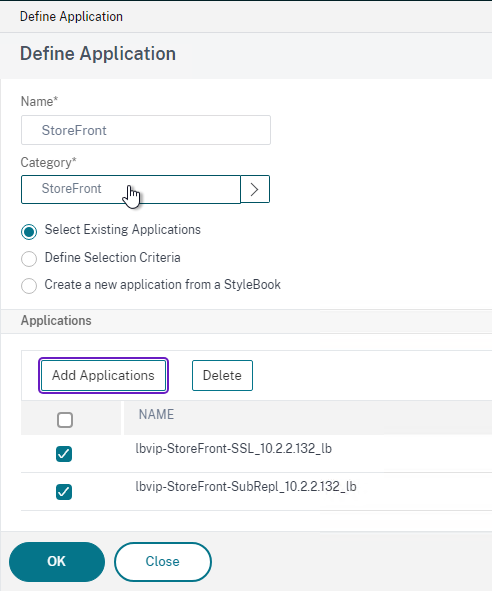
- Back in the App Dashboard, you can then click any Application’s box to view stats.
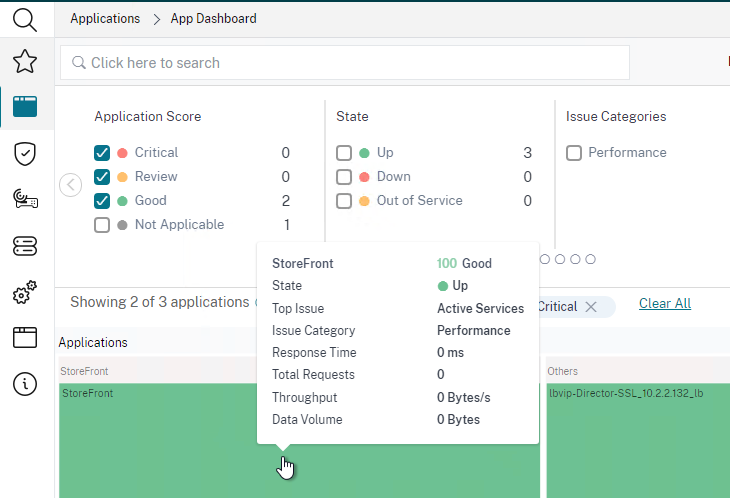
- For Custom Applications, it combines stats about all of the vServers in that Custom Application.
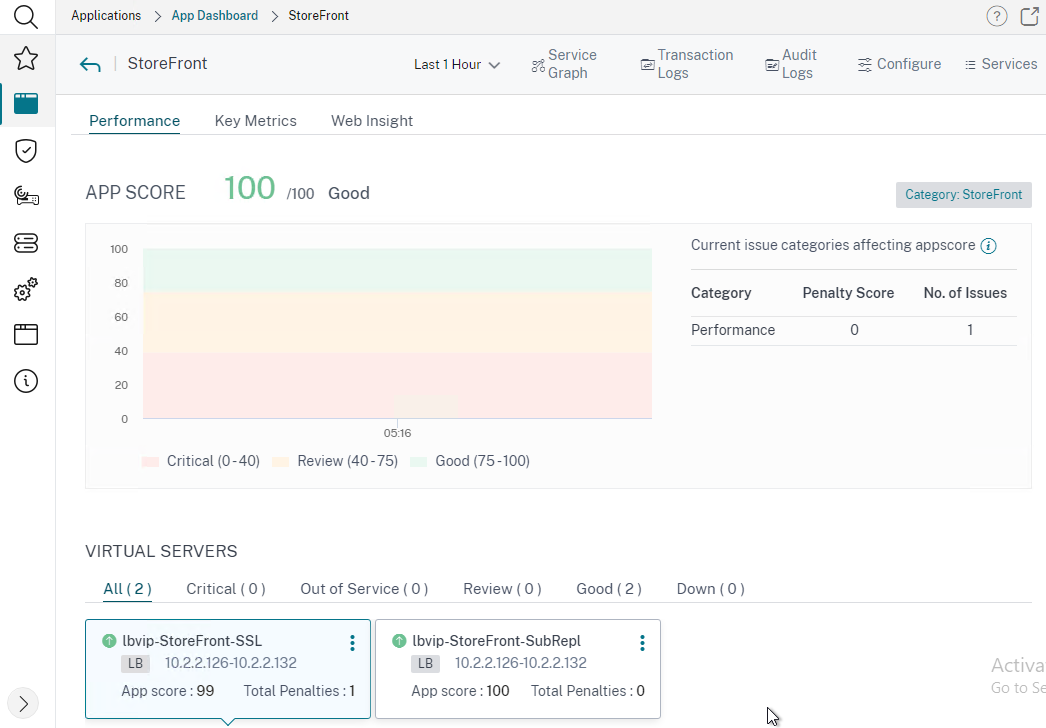
- There are buttons at the top the page to view more info about the application.
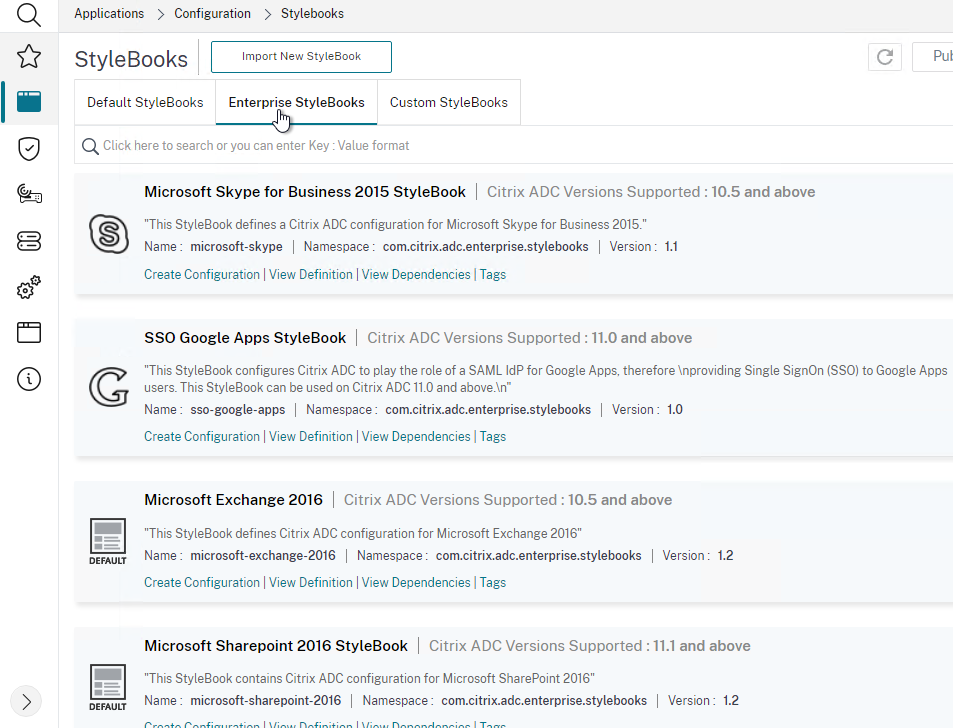
Applications > Configurations > StyleBooks lets you use StyleBooks to create new NetScaler ADC configurations.
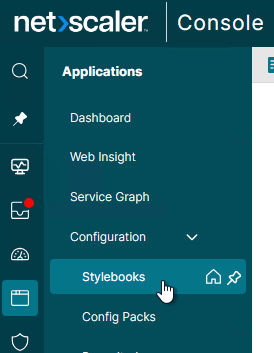
There are built-in Enterprise StyleBooks for Exchange, SharePoint, Oracle, ADFS, etc. Or you can create your own StyleBook and use it to create NetScaler ADC configurations. For details, see StyleBooks at NetScaler Docs.
The Applications Node has quite a bit of functionality. See Application Analytics and Management at NetScaler Docs for details.
Link:
- NetScaler Console How-to Articles at NetScaler Docs.
HDX Insight
HDX Insight Dashboard displays ICA session details including the following:
- WAN Latency
- DC Latency
- RTT (round trip time)
- Retransmits
- Application Launch Duration
- Client Type/Version
- Bandwidth
- Licenses in use
Citrix CTX215130 HDX Insight Diagnostics and Troubleshooting Guide contains the following contents:
- Introduction
- Prerequisites for Configuring HDX Insight
- Troubleshooting
- Issues Related to ICA parsing
- Error Counter details
- Checklist before Contacting Citrix Technical Support
- Information to collect before Contacting Citrix Technical support
- Known Issues
Gateway Insight
In the Gateway node is Gateway Insight.
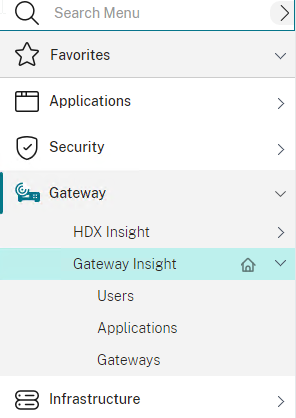
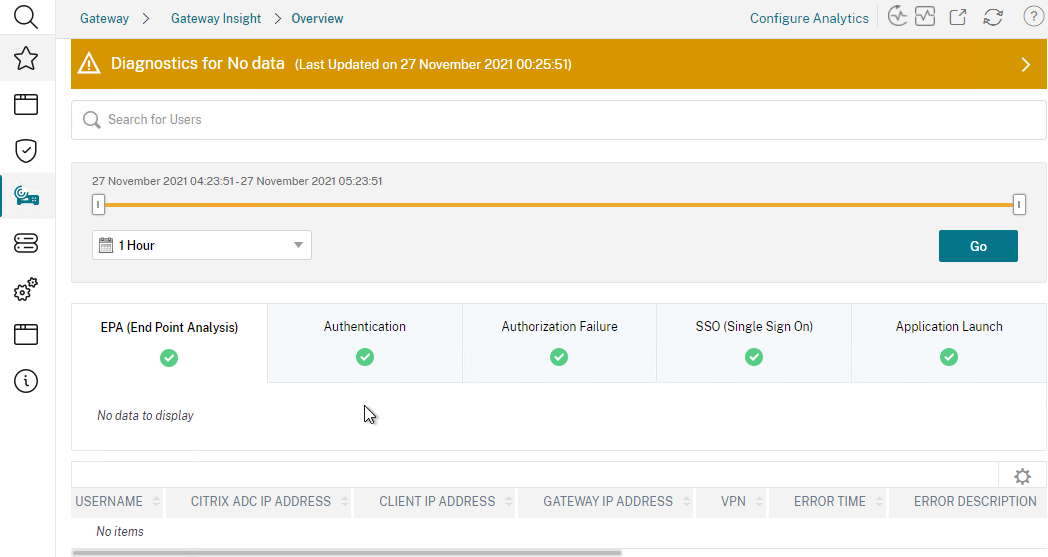
This feature displays the following details:
- Gateway connection failures due to failed EPA scans, failed authentication, failed SSON, or failed application launches.
- Bandwidth and Bytes Consumed for ICA and other applications accessed through Gateway.
- Number of users
- Session Modes (clientless, VPN, ICA)
- Client Operating Systems
- Client Browsers
More details at Gateway Insight at NetScaler Docs.
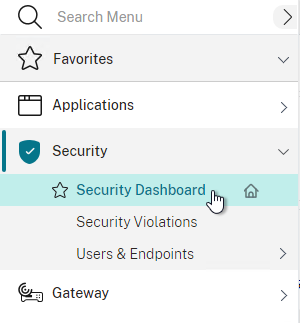
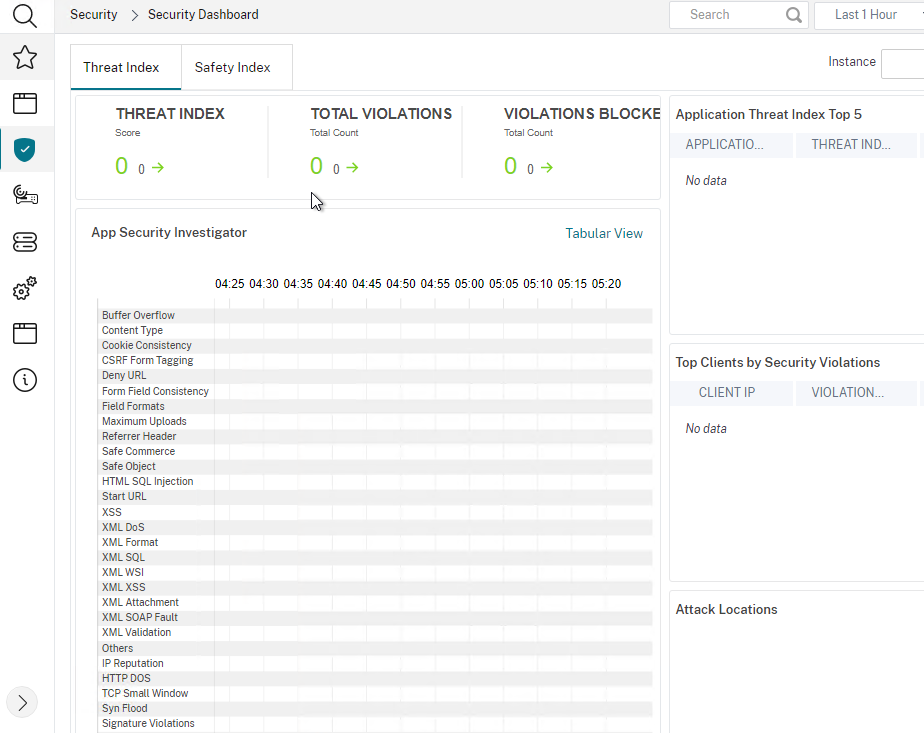
Security Dashboard
The Security Dashboard uses data from Application Firewall to display Threat Index (criticality of attack), Safety Index (how securely NetScaler ADC is configured), and Actionable Information. More info at Application Security Dashboard at NetScaler Docs.
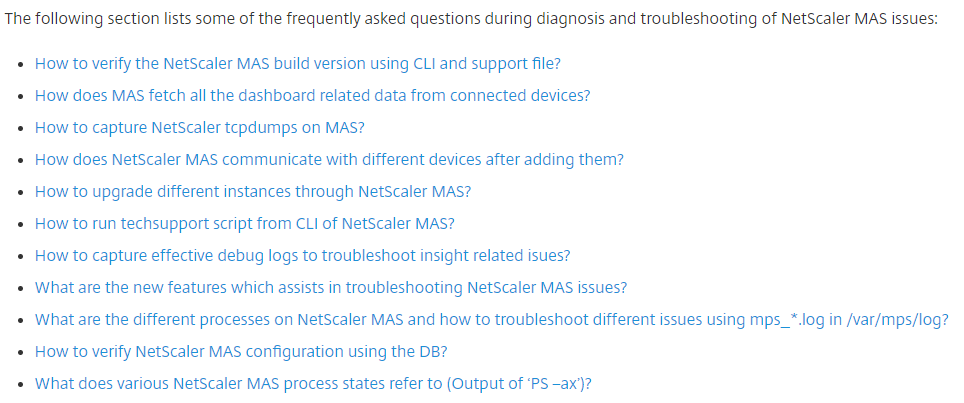
Troubleshooting
Citrix CTX215130 HDX Insight Diagnostics and Troubleshooting Guide: Syslog messages; Error counters; Troubleshooting checklist, Logs
Citrix CTX224502 Frequently Asked Questions During NetScaler MAS Troubleshooting
Upgrade NetScaler Console
Licensing – NetScaler Console build 21 and newer remove Analytics licenses thus enabling unlimited Analytics VIPs.
- Upgrade paths from Before you upgrade at NetScaler Docs.
- If you upgrade from 12.0 build 57.24 and higher, first upgrade to 12.1, then to 13.1, and then to 14.1.
- If you upgrade from 12.1, you must first upgrade to 13.0 64.xx, and then directly to 14.1.
- If you upgrade from versions lower than 13.0 64.xx, for better user experience, first upgrade to 13.0 64.xx and then to 14.1.
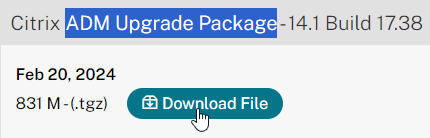
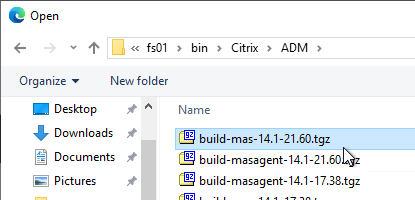
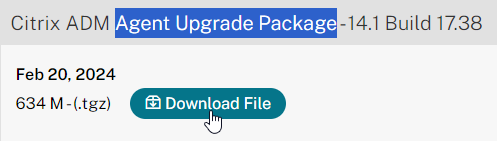
- Download the latest Citrix Application Delivery Management (ADM) Upgrade Package. You want the ADM Upgrade Package, not the ADM image. It’s around halfway down the page.
- Login to NetScaler Console Floating IP or Active Node. Upgrading the Active Node automatically upgrades the Passive Node.
- Go to Settings > HA Deployment and make sure both nodes are online and replicating.
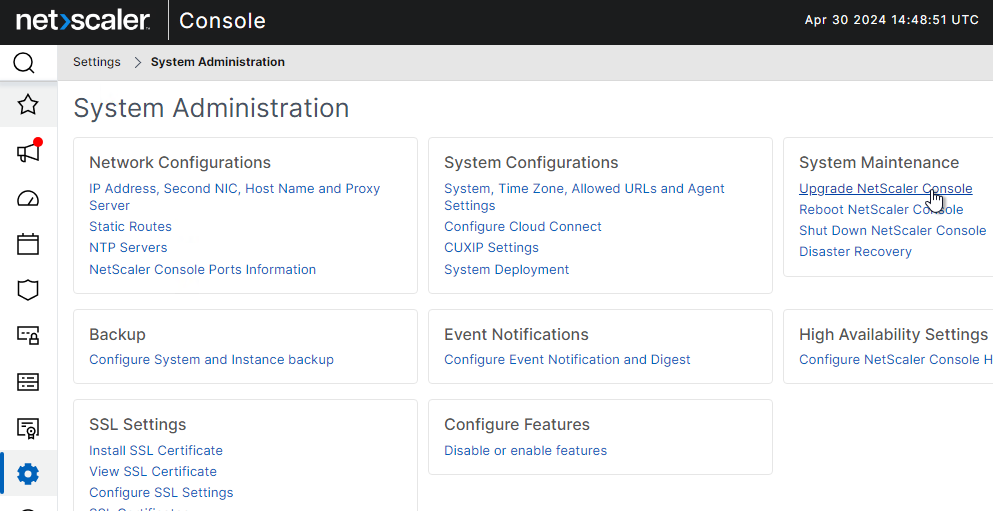
- Go to Settings > Administration.
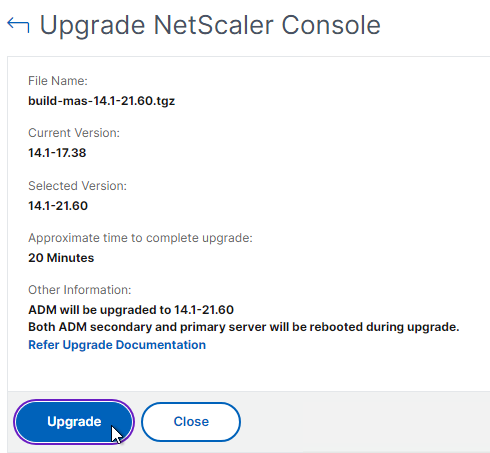
- On the right, in the far-right column, click Upgrade NetScaler Console.
- Browse to the build-mas-14.1…tgz Upgrade Package and click OK. The file name starts with build-mas-14.1 or build-mas-13.1 (not masagent).
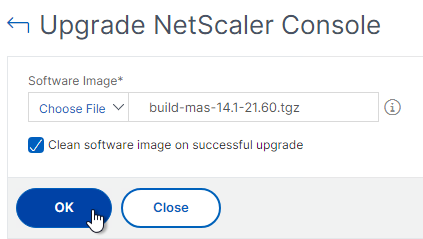
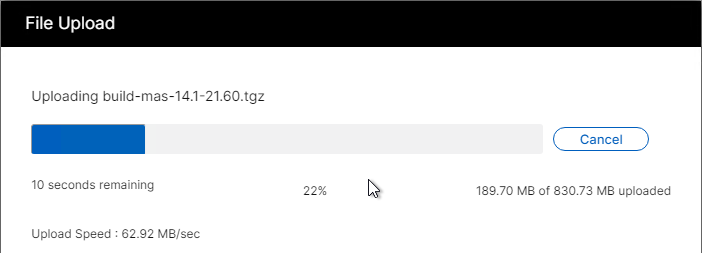
- Click Upgrade.
- Click Yes to continue with the upgrade.
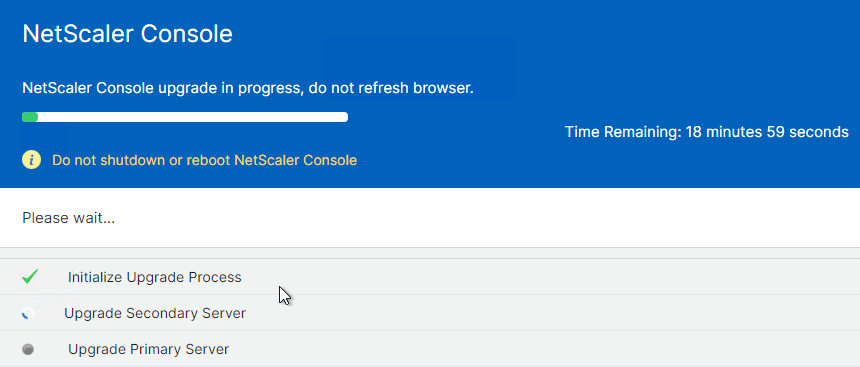
- After it says that NetScaler Console upgrade completed, click Login again.
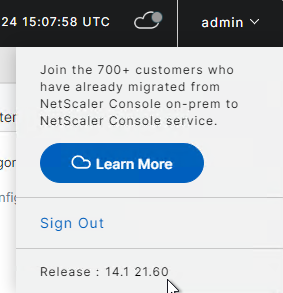
- The new firmware version can be seen by clicking your username in the top right corner.
Upgrade Disaster Recovery Node
After you upgrade the HA pair in the primary datacenter, you can upgrade the DR node.
- Use WinSCP or similar to connect to the DR node using the nsrecover credentials.
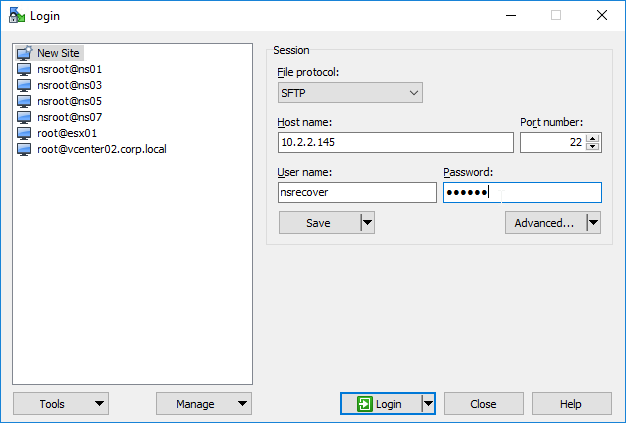
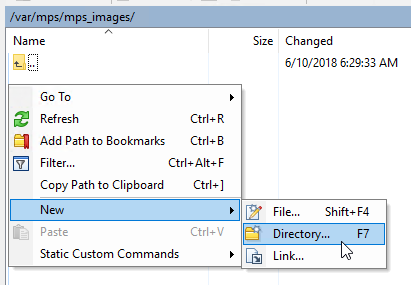
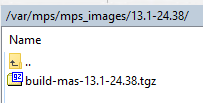
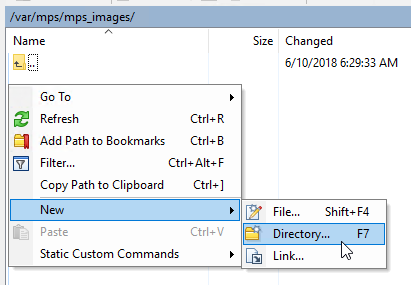
- On the NetScaler Console DR node, navigate to /var/mps/mps_images.
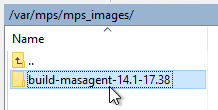
- Create a new Directory with the same name as the 13.1 build number. Then double-click the new directory to open it.
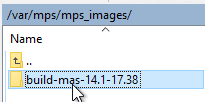
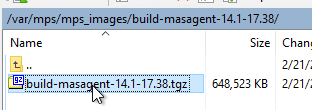
- Double-click the new directory to open it and then upload the file named build-mas-14.1-##.##.tgz or build-mas-13.1-##.##.tgz to the version-specific directory. This is the regular NetScaler Console upgrade file with a name starting with build-mas-14.1 or build-mas-13.1. It’s not the Agent upgrade file.
- SSH (Putty) to the DR node and login as nsrecover.
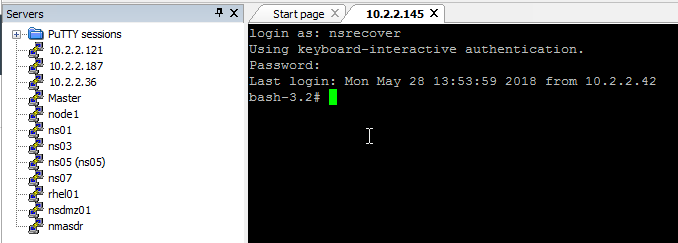
- Enter the following. Replace the # with the version number.
cd /var/mps/mps_images/14.1-##.## tar xvzf build-mas-14.1-##.##.tgz
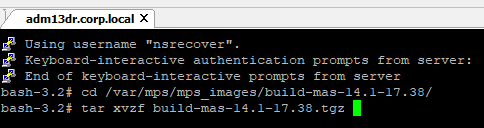
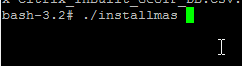
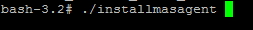
- Then enter the following. The appliance will reboot automatically.
./installmas
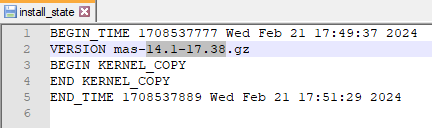
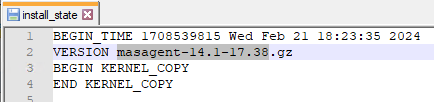
- After the reboot, the file /var/mps/log/install_state…
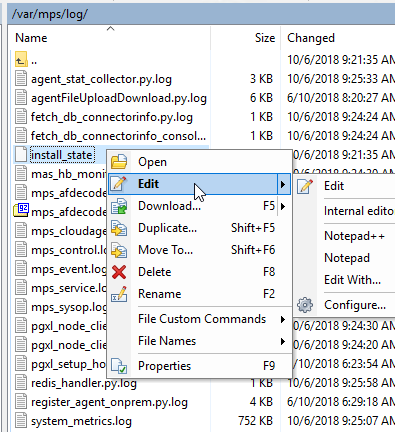
- …shows you the installed version.
Upgrade NetScaler Console Agents
After you upgrade the NetScaler HA pair in the primary datacenter, and after you upgrade the DR node, you can then upgrade the NetScaler Console Agents.
- From the NetScaler Console download page, at the bottom of the page, download the ADM Agent Upgrade Package. This Agent Upgrade file is different than the regular NetScaler Console upgrade file. And it is different than the files to deploy a new Agent. Find it at the bottom of the downloads page.
- In NetScaler Console 14.1 build 43.50 and newer, you can use the GUI to upgrade the Agents. NetScaler Docs.
- For older NetScaler Console, use WinSCP or similar to connect to the NetScaler Console Agent using the nsrecover credentials.
- On the NetScaler Console Agent, navigate to /var/mps/mps_images.
- Create a new Directory with the same name as the agent build number. Then double-click the new directory to open it.
- Upload the file named build-masagent-14.1-##.##.tgz or build-masagent-13.1-##.##.tgz to the version-specific directory. This is the NetScaler Console Agent upgrade file, and not the regular NetScaler Console upgrade file.
- SSH (Putty) to the NetScaler Console Agent and login as nsrecover.
- Enter the following. Replace the # with the version number.
cd /var/mps/mps_images/14.1-##.## tar xvzf build-masagent-14.1-##.##.tgz
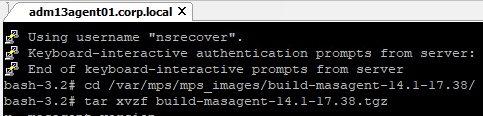
- Then enter the following. The appliance will reboot automatically.
./installmasagent
- After the reboot, the file /var/mps/log/install_state…
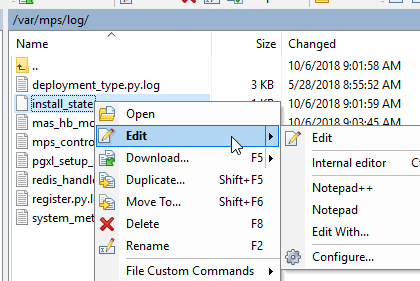
- …shows you the installed version.
- Repeat for any additional NetScaler Console Agents.
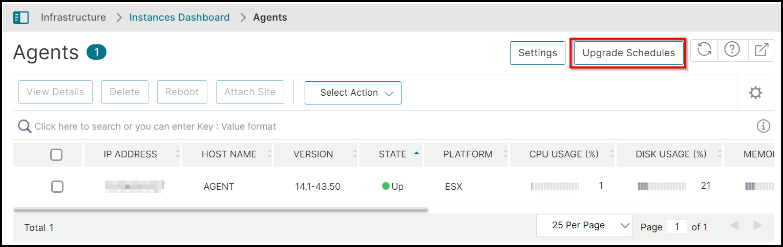
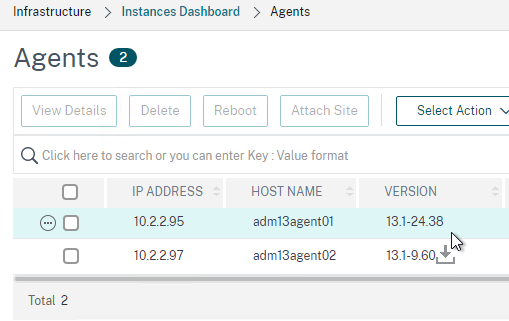
- If you login to NetScaler Console and go to Infrastructure > Instances > Agents…
- …you should see the new Version. It will take several minutes for the version number to update.
Hello, I’m having a problem migrating my console from version 14.1 43.50 to 14.1 56.71. The process is stuck at the configuration migration stage, and after a reboot, I no longer have access to the GUI. A self-signed NetScaler certificate has replaced my SSL certificates and is preventing the connection. For your information, it’s a console behind a Nutanix. Any idea?
Hi Carl, Something I am struggling to find any useful info on for NetScaler Console 🙁
I am seeing critical secuirty reports against several NetScalers for File Integrity Monitoring. I have checked the files flagged and not at all worried about them. But, I cant find a way to reset to accept these new files as the new baseline/generate new hashes?
thanks
Hi Carl, if deploying an on-prem NS Console do you still need the agents? Or can the VPX talk directly to the NS Console appliance?
Agents are not needed for on-prem Console.
Hi,
Can NetScaler Console On-Prem have the API Security Module?
I see this only on the NetScaler Console Service that has the API definition and all the API Agent that can be added.
But on the NetScaler Console On-Prem its only API Analytic and discovery
Hi Carl,
fairly easy question, I guess. We are currently looking into using Netscaler Console, but are not sure if we should use the OnPrem or Cloud Version. I’m looking into the differences between the two versions and was not able to find any sources that answer my questions. Are there any differences in terms of features and pricing?
I recommend the cloud version, so you don’t have to do updates or worry about database synchronization. Cloud version has different features as compared to on-prem.
Hi, Carl.
I recently upgraded from 14.1-12.35 to 14.1-25.56 in order to remediate some vulnerabilities. However, that ended up wiping my license files and as a result, nobody could connect to the ADC’s. I have a hybrid setup, with my ADC’s being on-prem VM’s. According to Citrix support, I have to enable the NetScaler Console within Citrix Cloud in order to upgrade, due to a licensing model change. Here were the follow up questions to Citrix and I have not received a response:
1) My ADC’s are currently on-prem and running 14.1-12.35. In order for me to jump to 14.1-25.56, I would first need to setup the NetScaler Console in Citrix Cloud.
2) Apparently, the licensing model has changed and by me moving the ADC’s to NetScaler Console, this will allow me to perform the upgrade to the latest build?
3) By moving them to the NetScaler Console, does this alter my configuration at all?
4) Will users be impacted, or will they still connect and access resources like they typically do?
5) How much downtime should I expect? Would the NetScaler’s just need to be rebooted after adding them to the NetScaler Console?
Would you happen to know if this is pretty straightforward?
If NetScaler Console is the cloud version, login to NetScaler Console and deploy the NetScaler Agent to your on-prem datacenter.
Then in NetScaler Console, allocate your Flex licenses to NetScaler Console.
If your NetScaler appliance is physical, then allocate a NetScaler zero-capacity license to the physical appliance to enable flex licensing. Not needed on VPX.
If VPX, add a license but choose remote licensing. Physical appliances will automatically ask for the license server. Enter the IP address of the agent. It will ask you to allocate licenses to the VPX, MPX, or SDX.
Changing licensing usually requires a reboot.
Awesome! I really appreciate it, Carl.
Greetings,
Changed adm aelf signed to an internal cert cert but it is not trusted by browser.
Anyway to upload the CA cert ?
In your browser, open Developer Tools and click the Security tab. There should be more info on the issue.
Hi Carl,
We’re experiencing a peculiar issue. We’ve deployed Citrix Secure Access version 23.1.1.11 (Always On – Split tunnel mode), but occasionally, some users receive downgrade notifications to version 22.10.1.9 or other versions. Unfortunately, I don’t have access to the NetScaler (Model: MPX 5901, version 13.0.190.7), but I’ve checked the client and found nothing unusual.
Do you have any ideas about this issue ?
Thanks.
Tom
Are you doing GSLB across multiple NetScalers? Maybe they have different versions of the Secure Access client.
We actually have two load-balanced NetScalers. I will need to check with our NetScaler specialist regarding this issue. However, is it possible that this issue is originating from the NetScaler side ? (in order to exclude investigation on Client)
By default, NetScalers try to push down the Secure Access client that is installed on the NetScalers.
Thank you Carl !
Hello, Im setting up new ADM agents(virtual appliances). They are currently configured to use a proxy for outbound connections. Proxy presents a cert that ADM agents need to trust. Is there also a way to add CA cert for outbound trusts??
I suspect there’s a Linux location but I’m not certain where that is.
Great article Carl. One thing I noticed is after the upgrade. In the “Customer Identity page” for release 13.0.85.15 there is no “Skip” button.
Maybe obvious but for a fresh install with NetScaler and all V-Servers in the DMZ would the ADM also be deployed in the DMZ? What ports need to be available from the LAN?
ADM talks to the NSIP. You should be able to open firewall between NSIP and ADM.
However, ADM on-premises is no longer receiving feature updates so you should consider the cloud version instead.
ADM might talk to the NSIP, but appflow is sent from the SNIP according to my FW logs
Hey Carl,
Have you noticed that a fresh deployment of Citrix ADC VPX 13.1 Build 9.60 is missing all the Login Schemas available in other versions? The LoginSchema folder is non existant
I’ve seen that in some builds.